Lateral Movement
Lateral movement refers to the techniques attackers use to navigate through a compromised network in pursuit of high-value assets or sensitive data. This tactic gained prominence with the rise of Advanced Persistent Threats (APTs), where attackers shifted from immediate disruption to long-term espionage and data theft.
As security perimeters strengthened, attackers adapted, using stealthy methods to blend in with legitimate activity and remain undetected. Today, lateral movement is a critical concern due to the growing complexity and interconnectedness of networks, enabling attackers to exploit vulnerabilities and escalate their access.
What is Lateral Movement?
Lateral movement is a phase in cyberattacks where adversaries, after gaining initial access, move within the network to escalate privileges and locate critical information. This process involves reconnaissance, credential harvesting, and exploiting system vulnerabilities to traverse from one system to another.
As compared to direct attacks, lateral movement allows attackers to maintain persistence and avoid detection, making it a hallmark of advanced persistent threats (APTs). This phase often takes place over an extended period, allowing attackers to gather information and gain access to deeper layers of the network before launching their final payload.
Lateral movement techniques are particularly challenging to detect because they exploit legitimate tools and processes within the network. Attackers often use trusted credentials and authorized applications, blending in with normal activity to evade detection. Security professionals need to understand these methods in-depth to effectively identify and mitigate them before significant damage is done.
The Purpose of Lateral Movement
Attackers leverage lateral movement to achieve several objectives:
1. Persistence
By moving laterally, attackers can establish a foothold in various systems, ensuring continued access even if the initial entry point is discovered and remediated. This allows them to maintain control over compromised environments and launch further attacks at their discretion.
In the 2016 Democratic National Committee (DNC) cyberattack, attackers gained initial access through a phishing campaign and then moved laterally across multiple systems to ensure continued access, even after some entry points were remediated. They used this foothold to exfiltrate sensitive information over an extended period.
2. Privilege Escalation
Navigating through the network enables attackers to find and exploit accounts with higher privileges, granting them broader access to sensitive data and critical systems. Gaining elevated privileges is a key step that allows attackers to execute more sophisticated activities and compromise valuable assets.
In the 2020 SolarWinds attack, attackers moved laterally within the network to locate privileged accounts, allowing them to modify critical infrastructure and access sensitive systems. By exploiting SolarWinds Orion software, they were able to escalate privileges and gain access to highly sensitive information across multiple organizations.
3. Access to Critical Resources
Lateral movement facilitates the discovery and compromise of high-value assets, such as databases containing personally identifiable information (PII) or proprietary business data. By expanding their reach within the network, attackers can identify critical systems that hold valuable information and exploit them for financial gain, espionage, or sabotage.
In the Target data breach of 2013, attackers gained initial access through a third-party vendor and moved laterally to access payment systems. This allowed them to steal the credit card information of millions of customers, resulting in significant financial and reputational damage to Target.
In many cases, attackers spend weeks or even months exploring and mapping out the network, searching for the best opportunities to extract data or disrupt operations. The longer attackers can remain undetected, the greater the risks for the targeted organization.
Common Techniques of Lateral Movement
Attackers employ various methods to move laterally within a network:
Pass-the-Hash
- This technique involves using hashed credentials to authenticate across systems without knowing the actual plaintext password. By capturing and reusing these hashed values, attackers can bypass traditional authentication mechanisms and gain access to other systems within the network.
- In the 2017 NotPetya attack, attackers used tools like Mimikatz to extract hashed credentials from compromised systems and then used those hashes to authenticate to other machines within the network.
Pass-the-Ticket
- Attackers exploit Kerberos tickets to authenticate to other systems, bypassing the need for account passwords, known as Pass-the-Ticket attacks . By leveraging compromised Kerberos tickets, attackers can impersonate legitimate users and move undetected within the network.
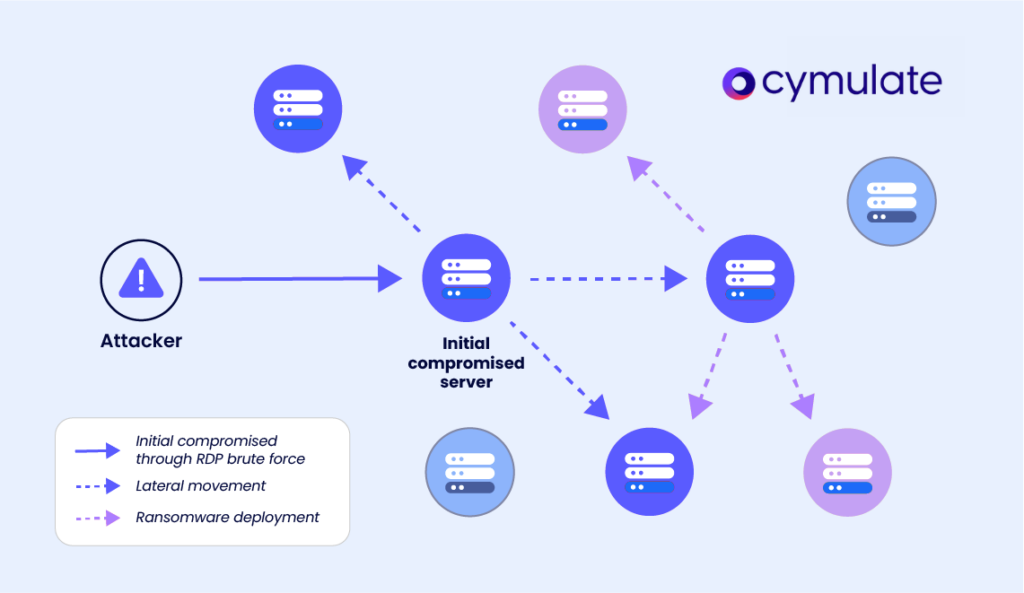
Remote Desktop Protocol (RDP) Abuse
- By compromising RDP services, attackers can remotely control systems within the network. This allows them to access sensitive systems, execute commands, and manipulate data as if they were legitimate users, making RDP abuse a powerful tool for lateral movement.
- In the 2018 SamSam ransomware attack, attackers used compromised RDP credentials to move laterally across the network and deploy ransomware to multiple systems, causing widespread disruption.
Windows Management Instrumentation (WMI)
- WMI can be misused to execute commands and scripts on remote systems, facilitating lateral movement. Attackers use WMI to interact with remote systems, run scripts, and execute malicious commands without needing direct access to the target machine.
- Attackers behind the APT33 campaign used WMI to execute malicious payloads on multiple systems within the targeted organization's network, allowing them to expand their access and escalate their attack.
Exploiting Weak or Misconfigured Permissions
- Attackers identify and exploit systems with inadequate permissions, allowing unauthorized access and movement. Misconfigurations, such as overly permissive file shares or weak access control lists (ACLs), provide attackers with opportunities to move laterally and gain further access.
- In the 2017 NotPetya attack, adversaries used tools like PsExec and WMI to propagate malware across networks, demonstrating the effectiveness of these techniques.
- These tools, which are often used by system administrators for legitimate purposes, can be repurposed by attackers to spread their malware and escalate their access within the network.
Understanding the Short-Term and Long-Term Risks of Lateral Movement
Lateral movement poses a severe threat, allowing attackers to traverse networks, escalate privileges, and amplify the damage of an attack. This tactic makes detection difficult, and increases the risk of operational, financial, and reputational damage. 44% of ransomware attacks are detected during lateral movement, and 25% of data breaches involve this tactic, often targeting sensitive information.
The compounding impacts of lateral movement extend beyond immediate breaches. Attackers often exfiltrate sensitive data, leading to compliance violations, financial penalties, and lasting reputational damage. Disrupted operations, caused by compromised systems, result in downtime that affects business continuity and critical services. Additionally, compromised systems expand the attack surface, serving as a base for further attacks and complicating containment and detection efforts.
Detection of Lateral Movement
Identifying lateral movement requires a multifaceted approach:
1. Network Traffic Analysis: Monitoring for unusual patterns or anomalies in network traffic can reveal unauthorized movements. Anomalies such as unexpected connections between systems, large data transfers, or unusual access times can indicate lateral movement activities.
2. User Behavior Analytics: Analyzing deviations from typical user behavior helps in detecting compromised accounts. For example, if a user's account starts accessing systems or data that are outside of their normal scope of work, this may indicate that the account has been compromised and is being used for lateral movement.
3. Endpoint Detection and Response (EDR): EDR solutions monitor endpoints for suspicious activities indicative of lateral movement. By tracking changes in system configurations, file access, and process execution, EDR tools can identify behaviors that suggest lateral movement and alert security teams to potential threats.
4. Security Information and Event Management (SIEM) Systems: SIEM platforms aggregate and analyze logs from various sources to identify potential threats. By correlating data from network devices, servers, endpoints, and applications, SIEM systems can provide a comprehensive view of activity within the network and help identify signs of lateral movement.
Attackers are increasingly using encrypted communication, legitimate credentials, and obfuscation techniques to evade detection, making it critical for security teams to stay updated on the latest threat tactics and improve their detection capabilities.
Prevention and Mitigation Strategies
Given its destructive potential, addressing lateral movement is critical for strengthening organizational resilience. Proactive steps, such as securing Active Directory, monitoring for abnormal network behaviors, and implementing robust detection mechanisms, can significantly reduce the risks associated with lateral movement and prevent attackers from achieving their objectives.
Network Segmentation
Dividing the network into isolated segments limits an attacker's ability to move freely. Proper network segmentation ensures that even if one part of the network is compromised, attackers cannot easily access other areas, reducing the overall impact of an attack.
Least Privilege Access Control
Ensuring users have only the access necessary for their roles minimizes potential exploitation. By limiting access rights, organizations can reduce the risk of attackers gaining elevated privileges and moving laterally through the network.
Regular Vulnerability Assessments
Conducting frequent assessments helps identify and remediate security weaknesses. Regular vulnerability scanning and penetration testing allow organizations to identify potential entry points and address them before attackers can exploit them.
Multi-Factor Authentication (MFA)
Implementing MFA adds an additional layer of security, making unauthorized access more difficult. By requiring multiple forms of verification, MFA can prevent attackers from using stolen credentials to move laterally within the network.
Security Validation Through Continuous Testing
Regularly testing security controls ensures they function as intended and can withstand evolving threats. Continuous security validation allows organizations to assess the effectiveness of their defenses and make necessary adjustments to stay ahead of emerging threats.
A proactive approach that includes regular testing, monitoring, and refinement of security controls is essential to preventing lateral movement and minimizing the impact of potential attacks.
Lateral Movement Mitigation Made Simple with Cymulate
Cymulate offers comprehensive solutions to detect and mitigate lateral movement within networks. Through continuous security validation, Cymulate enables security teams to simulate lateral movement tactics, identify vulnerabilities, and assess the effectiveness of existing controls.
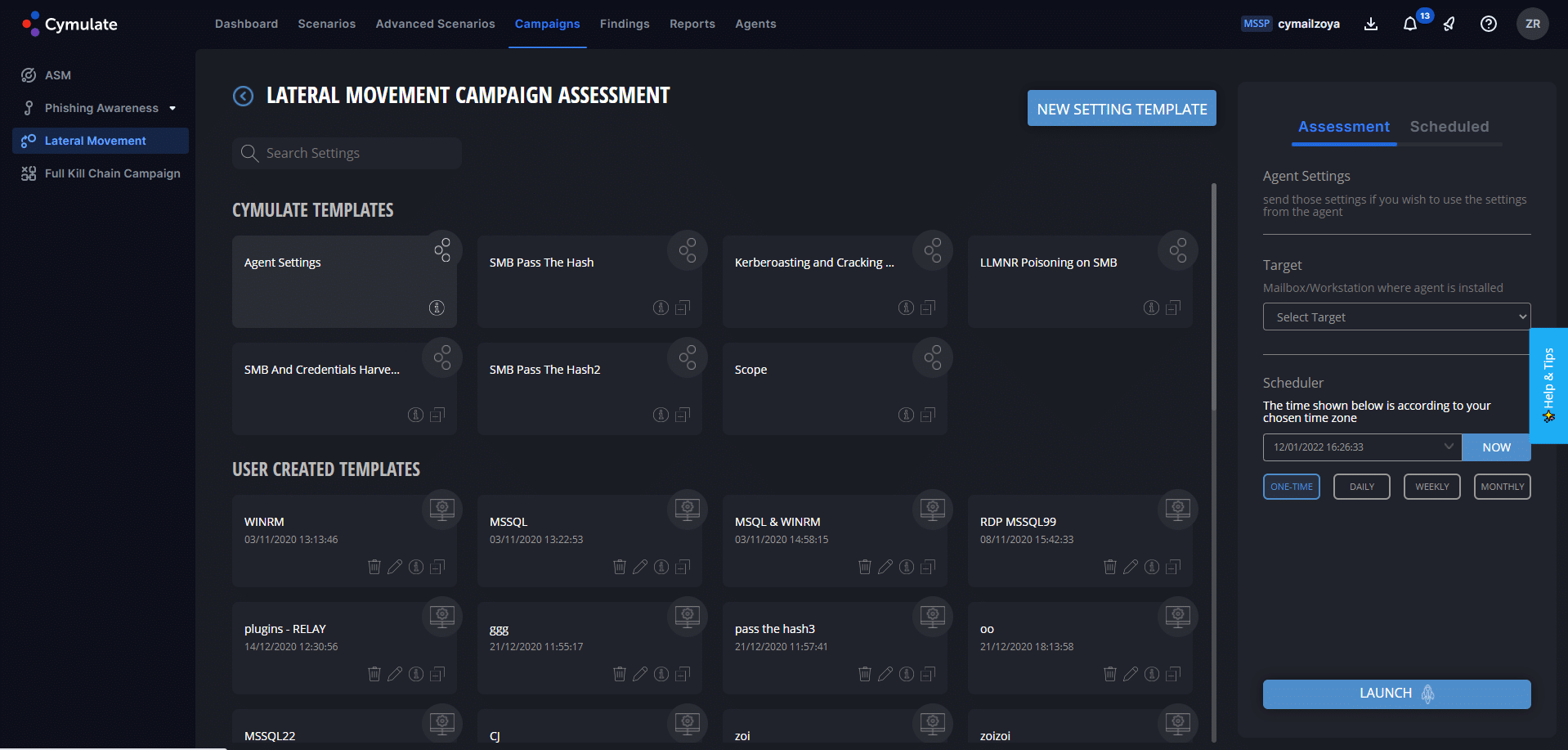
How it works:
Phase 1 - Discovery: The Cymulate Agent scans the system and internal network for potentially reachable systems and fingerprints them. In addition, relevant information is collected from the workstation itself, such as network shares, user accounts, and services. Once critical areas to access are identified, the next step is gathering login credentials that will allow entry.
Phase 2 - Credential Access: The Cymulate Agent will collect information from the workstation based on common credential dumping techniques, which will later be used for spreading purposes. Credential dumping techniques can include dumping tokens, hashes, and Kerberos tickets from memory, as well as the collection of cleartext passwords.
Phase 3 - Lateral Movement: Based on results from previous stages, the Cymulate Agent will try to spread laterally from the original workstation by leveraging one or more attack methods. If Crown Jewels have been defined in the template, the campaign will attempt to access these specifically.
Phase 4 - Test Results and Actionable Insights: The Lateral Movement results are presented in an interactive graphic diagram that shows the attacker’s lateral movement path and the methods used to achieve each hop, along with KPI metrics and actionable mitigation recommendations. By taking the appropriate countermeasures, IT and security teams can increase their internal network security. A technical and an executive report are also generated following each assessment, and a risk score is calculated.
This proactive approach allows organizations to prioritize and address weaknesses, reducing the risk of lateral movement and protecting critical assets.
Bottom Line
Lateral movement attack cases are being reported continuously, with attackers constantly evolving their methods to bypass security measures. The only way to effectively prevent such attacks is to simulate and mitigate these threats before they even occur.
A combination of proactive security measures, continuous monitoring, and regular validation can help organizations stay resilient in the face of increasingly sophisticated cyberattacks.
If companies focus on both prevention and detection, security teams can limit the impact of lateral movement and protect their most valuable assets.