Managed Detection and Response (MDR)
From MTTD to MTTR: How MDR Services Drive Real Security Outcomes
Managed Detection and Response (MDR) is a cybersecurity service that combines advanced threat detection technology with human expertise to continuously monitor an organization’s IT environment, hunt for threats and respond to incidents in real time.
MDR provides organizations with a 24/7 “managed SOC” (Security Operations Center) as a service – experts watch over your networks and endpoints around the clock, using sophisticated tools to identify malicious activity and quickly contain attacks on your behalf.
This proactive, turnkey approach to threat monitoring and incident response has become increasingly important in today’s evolving threat landscape, where businesses face an onslaught of advanced cyberattacks and often lack the in-house resources to keep up.
In fact, one industry survey found 94% of organizations are evaluating MDR services and 79% plan to adopt MDR, underscoring its growing role in modern security strategy.
What is Managed Detection and Response (MDR)?
Managed Detection and Response (MDR) is an outsourced security service designed to detect and respond to threats in real-time. Unlike traditional alerting tools, MDR goes further identifying, investigating, and actively responding to security incidents.
These services rely on a blend of advanced technology (like EDR agents, log analytics and network sensors) and expert human analysts to stop threats quickly.
Why MDR Matters: Speed is Everything
One of the key goals of MDR is to reduce two critical cybersecurity metrics:
- Mean Time to Detect (MTTD): How long it takes to identify a threat.
- Mean Time to Respond (MTTR): How quickly an incident is resolved after detection.
Organizations without MDR often take months to detect and contain breaches. IBM found the average dwell time for a breach was over 277 days. In contrast, MDR services can slash this to minutes, significantly reducing risk and impact.
Some key performance improvements from MDR adoption include:
- Detection in minutes rather than months
- MTTR reductions of 25–49%, with many organizations reporting even faster resolution times
- Reduced manual remediation effort, from hours to minutes per incident
Understanding How MDR Works
MDR acts as a remote extension of your security team, offering round-the-clock monitoring and fast response. Here’s how the process typically unfolds:
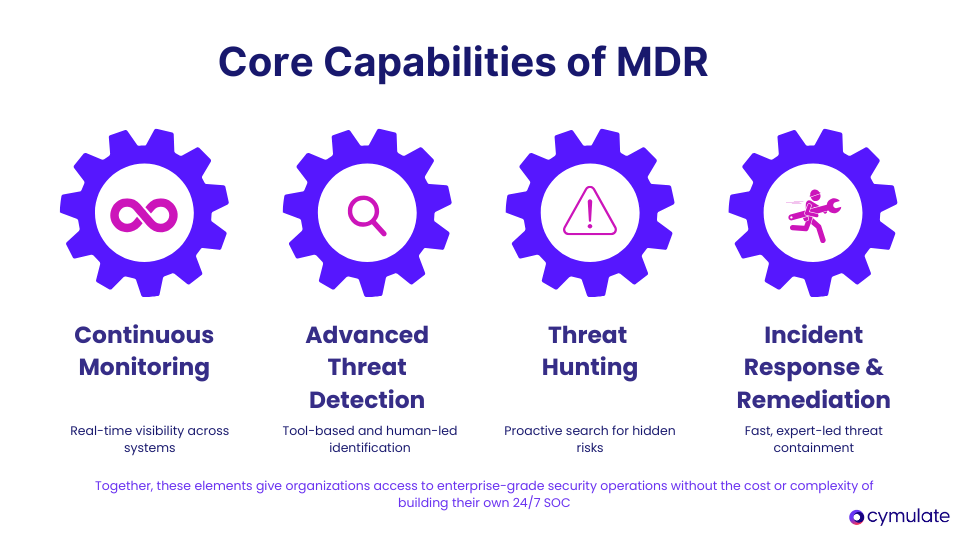
Continuous Monitoring: MDR providers continuously track endpoints, networks, cloud workloads, and more using tools like EDR and SIEM. This 24/7 monitoring ensures threats are caught - even during off-hours, weekends or holidays.
Advanced Threat Detection: MDR uses behavioral analytics, machine learning, threat intelligence and tailored detection rules to spot both known and novel threats. Crucially, human analysts play a hands-on role, reviewing alerts, filtering out false positives and recognizing sophisticated attacks that might bypass automation.
Investigation and Threat Hunting: When a threat is detected, MDR analysts conduct a deep forensic investigation to uncover the full scope of the incident. They examine how the attacker entered the environment, identify which accounts or systems were compromised, and assess the attacker’s movements across the network. By correlating activity and anomalies across multiple systems, they piece together a complete picture of the threat.
Threat hunting adds an extra layer of defense by proactively searching for stealthy or dormant threats that automated tools may overlook. This human-led analysis, powered by experience and intuition, increases the chances of catching sophisticated attackers using evasive tactics.
Response and Remediation: Once a threat is confirmed, MDR services act quickly to mitigate it. They immediately notify your team with a detailed incident report and either recommend or directly execute specific response actions, such as isolating compromised endpoints or terminating malicious processes.
Depending on the service model, they may also guide your internal team through the remediation steps or take direct action to remove persistence mechanisms and restore systems to a secure state.
Some MDR providers offer full remote remediation, handling these technical tasks on your behalf to reduce pressure on internal teams and speed up recovery.
MDR vs. Traditional Security Monitoring
MDR has emerged to address gaps left by more traditional security monitoring solutions such as Managed Security Service Providers (MSSPs) and in-house SIEM deployments. It’s helpful to compare MDR with these approaches to understand its advantages:
Addressing the Gaps in Legacy Solutions
Managed Detection and Response (MDR) emerged to overcome the limitations of traditional security models like Managed Security Service Providers (MSSPs) and standalone SIEM deployments.
While MSSPs monitor logs and manage security infrastructure, they usually stop at alert generation, leaving incident investigation and response up to internal teams.
In contrast, MDR is an outcomes-driven service. It not only monitors and detects threats but also investigates and actively responds to them in real-time. This significantly reduces the detection-to-response timeline and lowers the operational burden on internal security teams.
SIEM vs. MDR: Tool vs. Service
A SIEM aggregates security data and generates alerts, but it’s still just a tool. Organizations often struggle to make sense of SIEM alerts without a dedicated team to investigate and respond.
MDR wraps a managed service around such tools providing people, processes, and expertise to deliver real detection and response outcomes. SIEM requires time, tuning and staffing, while MDR offers faster deployment and a lighter footprint.
How XDR Complements MDR
Extended Detection and Response (XDR) is a platform that unifies detection across multiple domains like endpoints, networks, and cloud.
While XDR enhances visibility, it still needs human intervention for incident response. MDR services often integrate XDR to enrich their capabilities, and Managed XDR (MXDR) blends both for broader coverage and round-the-clock threat response.
MSSP vs. MDR
| Aspect | Traditional MSSP | Managed Detection & Response (MDR) |
| Primary Focus | Broad security monitoring and device management. Focused on alerts and compliance. | Specialized threat detection and real-time response. Focused on stopping threats quickly. |
| Detection Approach | Perimeter- or log-based, rule-driven, mostly reactive. | Multi-domain telemetry, advanced analytics and proactive threat hunting. |
| Incident Investigation | Limited triage. Often pushes alerts to the client to investigate. | Often siloed, may require using a vendor stack-limited workflow integration. |
| Response Actions | Broad but shallow – includes device configs, scanning, and reporting. | Actively contains threats and guides or performs remediation. May offer remote response. |
| Scope of Services | Often siloed, may require using a vendor stack - limited workflow integration. | Narrow but deep – focused on advanced detection, fast. containment, and expert-led investigation. |
| Integration | In-depth analysis, alert validation, and context-rich threat reports by analysts. | Integrates with client tools or provides minimal-footprint agents. Transparent and quick to deploy. |
MDR: Benefits That Drive Results
Adopting a Managed Detection and Response solution can provide numerous benefits for organizations, especially those who lack a large in-house security operations team. Here are some of the key benefits of MDR:
24/7 Monitoring and Faster Detection
MDR ensures around-the-clock threat monitoring, providing expert oversight even during weekends and holidays. This continuous vigilance improves detection speed and reduces alert fatigue for internal teams. Instead of being overwhelmed with false alarms, organizations are only notified when a verified threat emerges.
This significantly reduces dwell time, the period attackers remain undetected limiting their ability to cause damage.
Advanced Threat Detection
MDR services provide access to cutting-edge detection tools and expert analysts that many organizations cannot afford in-house. These include behavioral analytics, machine learning, and global threat intelligence feeds.
Together, they detect advanced attacks such as ransomware, zero-days, and stealthy intrusions. MDR teams also perform ongoing threat hunting, increasing the chances of uncovering even signature-less attacks.
Rapid and Guided Incident Response
Speed is crucial during a cyberattack. MDR services initiate response actions within minutes of detecting a threat. They isolate affected devices, block attacker activity and guide your team through containment steps.
This quick action helps prevent a small incident from becoming a large-scale breach. Many MDR providers also support recovery and post-incident cleanup.
Access to Security Expertise
MDR gives organizations immediate access to skilled professionals including threat hunters, forensic analysts, and incident responders without the burden of building a team internally.
These experts bring wide-ranging experience and specialized skills, significantly boosting your security operations. MDR also reduces strain on internal staff and mitigates the risks of burnout, turnover, or coverage gaps.
Lower MTTD and MTTR
MDR significantly reduces Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR). Instead of days or weeks, threats can be identified and addressed in minutes or hours.
This reduction in response time limits the scope of breaches, lowers potential damage and helps meet regulatory or compliance requirements more easily.
Cost Efficiency and ROI
Building an equivalent in-house SOC is resource-intensive and expensive. MDR provides similar capabilities at a predictable subscription cost, avoiding upfront investments in tools and personnel.
Studies show MDR can deliver strong ROI up to 5.5x over three years by minimizing breach costs, reducing downtime, and streamlining operations. It’s a scalable, cost-effective way to elevate security without exceeding budget constraints.
MDR Limitations and Challenges
While MDR brings significant advantages, it’s not a complete solution. Understanding its limitations is essential to setting realistic expectations and building a more resilient security posture.
1. MDR Is Reactive, Not Preventive
MDR is designed to detect and respond to threats, not to prevent them entirely. If an attacker bypasses preventive controls like firewalls or antivirus, MDR only engages once suspicious activity is detected.
This means some damage might already be done before MDR intervenes. Organizations should treat MDR as a safety net, not a substitute for foundational preventive practices like patching, segmentation and hardening.
2. Coverage Varies by Provider
The scope and quality of detection depend heavily on the MDR provider’s technology stack and focus areas. Many MDRs are endpoint-centric and may lack full visibility into cloud environments, identity systems, or network layers.
Some require clients to adopt specific tools, which may lead to vendor lock-in or force technology replacements. Detection quality also varies, some providers rely on generic threat intel with minimal tuning, increasing the risk of missed threats.
3. No Built-In Exposure Validation
Most MDR services don’t test whether your existing security controls are working effectively. They detect real attacks but don’t proactively simulate threats to identify detection gaps.
Without regular validation, organizations risk having blind spots that only get exposed during actual incidents. This highlights the need to pair MDR with security validation platforms that continuously assess detection and response readiness.
4. Vendor Dependency and Shared Responsibility
Outsourcing security operations introduces reliance on the MDR provider’s processes, analysts, and infrastructure. While MDR teams handle detection and initial response, your organization is still responsible for broader remediation and policy enforcement.
Lack of transparency or poorly defined roles can lead to miscommunication or missed actions. MDR should not be treated as a “set-and-forget” solution, it works best when paired with internal engagement and clearly coordinated processes.
Complementing MDR with Continuous Security Validation
MDR excels at detecting and responding to threats in real time, but it doesn’t validate whether your controls are ready to detect those threats in the first place.
MDR bridges the gap between assumed and actual security effectiveness, ensuring that your defenses, and your MDR can perform under real-world attack conditions.
Why Validation Is Critical
Over time, detection rules become outdated, misconfigurations creep in, and new techniques evade existing defenses. Continuous validation solves this by simulating real attack techniques and confirming whether your controls and MDR can detect and block them.
It helps answer practical questions: Are endpoint agents catching ransomware behavior? Will the MDR detect a brute-force login attempt? Are firewall policies functioning as intended?
According to Gartner and other sources, integrating continuous exposure management into your strategy significantly reduces the risk of breaches. While MDR manages the reactive response, validation handles proactive assurance.
How Cymulate Supports MDR Programs
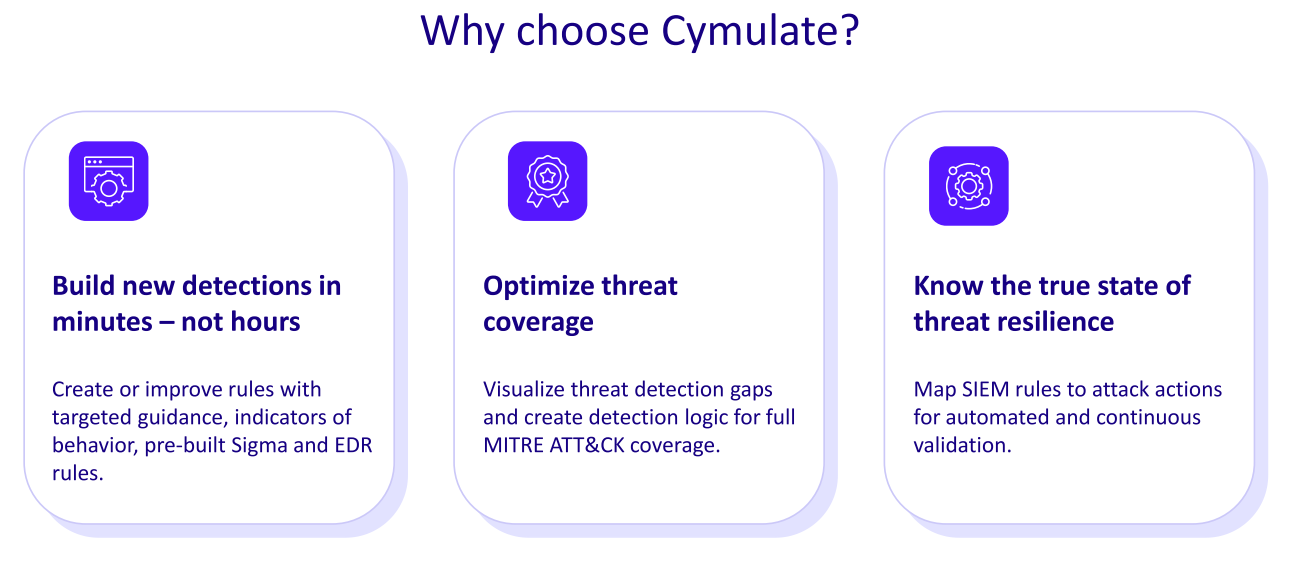
The Cymulate Exposure Validation Platform is purpose-built to complement MDR services. It enables security teams to:
- Validate Control Effectiveness: Cymulate continuously tests tools like SIEM, EDR and firewalls against evolving threats. Organizations can safely simulate attacks, such as data exfiltration or malware delivery and verify whether alerts are triggered and responses executed. This process transforms assumptions into evidence and helps security teams quickly address any failures or misconfigurations.
- Test Detection and Response Processes: Beyond tools, Cymulate evaluates the human and process elements of detection. Through Continuous Automated Red Teaming (CART), Cymulate emulates full kill-chain attacks to assess how well MDR teams and internal responders react. It highlights gaps in response speed or visibility, allowing for preemptive improvement before real-world consequences arise.
- Identify Blind Spots: Simulations help reveal which attack vectors or techniques evade detection. Cymulate maps detection coverage across the MITRE ATT&CK framework and pinpoints gaps. With this data, teams can adjust SIEM/EDR rules or work with the MDR provider to improve detection. Cymulate’s Detection Engineering module even suggests custom rule improvements, ensuring threat coverage stays current and contextual.
- Strengthen Detection and Response Over Time: This ongoing cycle, test, find gaps, fix, re-test drives measurable improvements in detection performance. Cymulate supports purple teaming, scenario-based drills and automated reporting. The result: optimized correlation rules, reduced response times and better preparedness during real incidents.
Get the Critical MDR Support You Need
MDR must be paired with continuous security validation. While MDR responds to live threats, validation ensures your defenses are always tuned and effective, even when attackers aren’t active.
This layer identifies detection gaps, tests control effectiveness and reinforces trust in your MDR’s capabilities.
Platforms like the Cymulate Exposure Validation Platform make this synergy possible. Cymulate helps organizations verify that their detection tools, and MDR providers can identify and react to emerging threats. It ensures your MDR service stays sharp, relevant and aligned with your unique risk environment.