Mean Time to Detect (MTTD)
Mean time to detect (MTTD) is the average time it takes for an organization to identify a security threat or incident. It measures how quickly a team can spot potential breaches, vulnerabilities, or attacks.
A lower MTTD means threats are detected faster, reducing the risk of damage. In cybersecurity, speed is everything. The longer a threat goes undetected, the more harm it can cause—data breaches, system downtime, or financial losses.
Organizations should aim to minimize MTTD to:
- Reduce damage – the sooner an issue is found, the less impact it has.
- Improve response time – early detection allows teams to act faster.
- Strengthen security – quick detection helps prevent future attacks.
Achieving a low MTTD requires strong monitoring tools, automated threat detection, and a well-trained security team. Companies that prioritize fast detection gain a major advantage—stopping threats before they escalate.
How to Measure MTTD
MTTD quantifies how long it takes an organization to detect security threats. It is calculated using the following formula:
MTTD = Total detection time / Number of incidents.
Each component in the formula matters:
- Total detection time: The sum of the time taken to detect all incidents over a specific period. This starts from the moment an attack begins until it is identified.
- Number of incidents: The total security breaches, attacks, or anomalies detected in that period.
For example, if a company experienced 5 cyberattacks in a month and took a total of 50 hours to detect them, MTTD would be: 50 hours / 5 incidents = 10 hours per incident. This means, on average, it takes 10 hours to detect each incident. The goal is to reduce this time as much as possible.
Let’s look at how MTTD varies across different security threats. The table below shows real-world security monitoring metrics of incident detection times for various incidents:
| Incident type | Total incident detection time (hours) | Number of incidents | MTTD (hours) |
| Phishing attack | 24 | 6 | 4 |
| Malware infection | 40 | 10 | 4 |
| Ransomware attack | 60 | 3 | 20 |
| Insider threat | 100 | 5 | 20 |
| DDoS attack | 12 | 4 | 3 |
This data highlights that some incidents, like phishing and malware infections, are detected relatively quickly. However, threats such as insider attacks and ransomware take longer to identify, making them more significant risks to an organization’s overall security posture.
What Does MTTD Actually Indicate?
MTTD is a direct reflection of an organization's security posture. A lower MTTD means threats are detected quickly, reducing potential damage. A higher MTTD suggests slow detection, giving attackers more time to exploit vulnerabilities.
Why mean time to detect KPIs matter:
- A low MTTD means security teams are proactive. They use strong monitoring, automated alerts, and well-trained analysts. This prevents attacks from spreading, minimizes downtime, prevents breaches, and strengthens overall defenses.
- A high MTTD indicates gaps in detection. Attackers have more time to steal data, install malware, or escalate privileges. The longer an attack goes unnoticed, the harder it is to contain. The consequences can be severe—financial loss, reputational damage, and operational disruptions.
Monitoring MTTD over time helps organizations measure progress. If MTTD improves, security is getting stronger. If it worsens, detection gaps need fixing. The goal is simple: keep MTTD low to stay ahead of evolving threats.
How to Reduce MTTD
Detecting threats faster is crucial for minimizing damage. The key is to streamline security processes and leverage the right tools. Here’s how to improve MTTD:
Implement security automation
Manual threat detection is slow and prone to errors. Automating key processes speeds up response times and improves accuracy.
SIEM and SOAR platforms analyze logs and trigger alerts instantly. Automated detection tools quickly spot anomalies, while AI-driven analytics identify patterns faster than humans, ensuring threats are caught before they escalate.
1. Continuous monitoring & threat intelligence
A proactive approach helps detect threats early. Keep an eye on all network activity:
- Deploy real-time monitoring for endpoints, cloud, and network traffic.
- Use threat intelligence feeds to stay ahead of emerging risks.
- Implement behavioral analytics to catch unusual activities before they escalate.
Reduce noise for faster triage
Too many false positives slow down detection. Optimize alerts by:
- Fine-tuning detection rules to filter out irrelevant alerts.
- Prioritizing alerts by risk level to focus on the biggest threats first.
- Using machine learning to reduce redundant notifications.
Optimizing tools and processes is crucial, but people play a key role in reducing MTTD. A well-trained, coordinated team detects threats faster. Regular training keeps analysts sharp and prepared for new threats.
Also, clear escalation procedures ensure quick, confident decision-making during incidents. Strong collaboration between IT and security teams improves visibility, making it easier to spot and respond to threats in real time.
Why Is It Important to Maintain a Low MTTD?
Both mean time to detect and mean time to respond are crucial for minimizing damage and maintaining strong security. The faster you detect a threat, the quicker you can contain it and prevent serious consequences.
Faster incident response
The longer a threat stays undetected, the greater the risk. A low MTTD gives security teams the advantage, limiting the time attackers have to move through systems. Fast breach detection time leads to quicker containment, stopping breaches before they spread. It minimizes downtime, keeping business operations running smoothly.
It also protects sensitive data, reducing the risk of theft or leaks.
Cost of delayed detection
The longer a threat lingers, the more damage it causes. Data loss can be costly, whether from theft or corruption, and may lead to legal consequences. Compliance risks increase, as failing to detect and report breaches on time can result in heavy fines.
Operational disruptions are another threat—attacks can shut down critical systems, impacting productivity and revenue.
Yet, every industry aims for rapid detection, but standards vary. On average:
- Top-performing security teams detect threats in minutes or hours.
- Most organizations take days or weeks to identify incidents.
- High-risk industries, like finance and healthcare, aim for MTTD under 24 hours.
Challenges in Reducing MTTD
Many organizations struggle with inefficient detection due to overwhelming alerts, limited visibility, and false positives. Addressing these challenges is key to improving security response times.
Alert fatigue
Security teams often deal with too many alerts, making it hard to focus on real threats. Important signals get buried under noise, leading to delayed responses or missed incidents. To combat this:
- Prioritize alerts based on severity and risk.
- Use automation to filter and group related alerts.
- Continuously refine detection rules to reduce unnecessary notifications.
Lack of visibility across environments
Threats can go unnoticed, especially in hybrid or multi-cloud environments. Without full visibility, security teams may miss critical signs of compromise. Strengthening visibility requires a centralized approach.
Logging and monitoring should cover all systems. Extended detection and response (XDR) tools provide broader coverage, while real-time threat detection and monitoring ensures all endpoints, cloud services, and networks remain under watch.
False positives slowing down response times
Too many false positives waste time and delay action on real threats. Investigating harmless alerts reduces security operations efficiency. To minimize false positives:
- Fine-tune detection rules to focus on real threats.
- Implement machine learning to recognize normal activity and reduce false alarms.
- Use threat intelligence to validate alerts before acting.
By tackling these challenges with smarter automation, better visibility, and refined detection strategies, organizations can significantly reduce MTTD and strengthen their security posture.
How Cymulate Helps Reduce MTTD
Reducing mean time to detect is crucial for maintaining a robust security posture. Cymulate platform offers practical solutions to achieve this by enabling organizations to:
Continuously validate security controls
Regular validation ensures that security measures function effectively against evolving threats. Cymulate facilitates this by:
- Automating security assessments: The platform conducts continuous, automated tests to evaluate the performance of security controls, ensuring they meet required standards.
- Providing actionable insights: After each assessment, Cymulate delivers detailed reports with remediation guidance, enabling security teams to address identified gaps promptly.
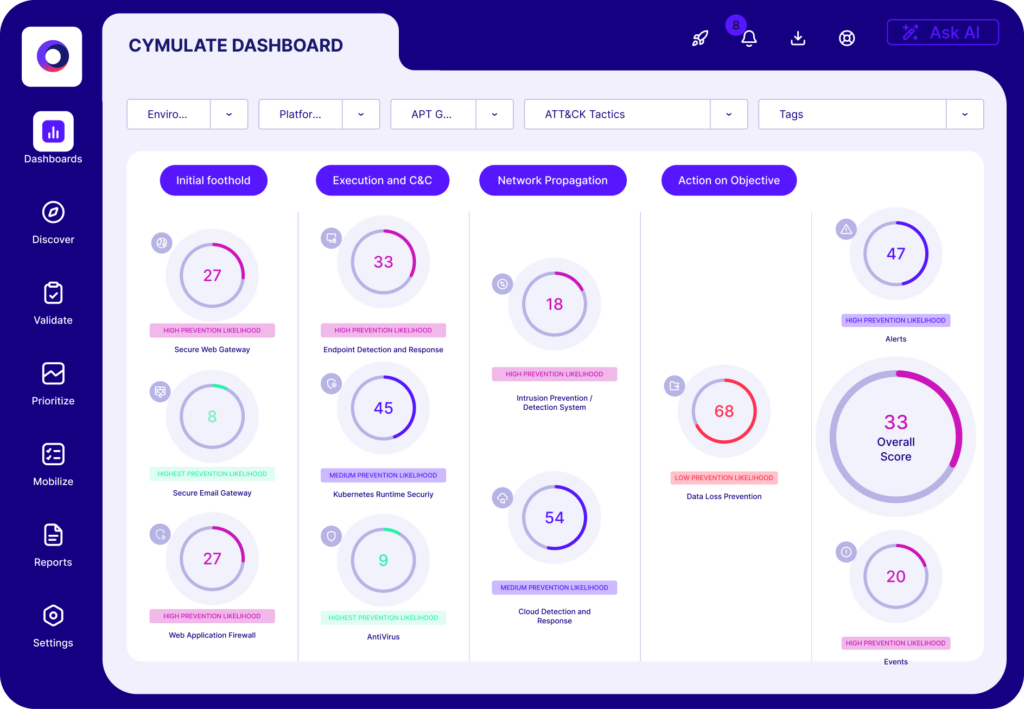
Identify gaps in detection capabilities
Undetected vulnerabilities can slow down threat detection. Cymulate helps close these gaps by simulating real-world attacks, testing how well an organization detects and responds to threats. It also highlights detection failures by analyzing simulation results, pinpointing weak spots in security defenses. This insight allows teams to strengthen their detection mechanisms and improve overall security.
Automate breach and attack simulations for faster insights
Timely insights into security weaknesses are essential for rapid response. Cymulate accelerates this process through:
- Automated breach and attack simulations: The platform continuously runs simulations that replicate the latest threats, providing immediate feedback on security posture.
- Enhancing security operations centers (SOCs) efficiency: By automating routine testing, Cymulate frees up SOCs to focus on addressing critical issues, thereby reducing MTTD.
Incorporating Cymulate into your security strategy ensures continuous threat validation, early detection of vulnerabilities, and swift insights through automation—all contributing to a reduced MTTD and a stronger security framework.

