Product Information & Email Gateway Validation
What is Cymulate's Email Gateway Validation?
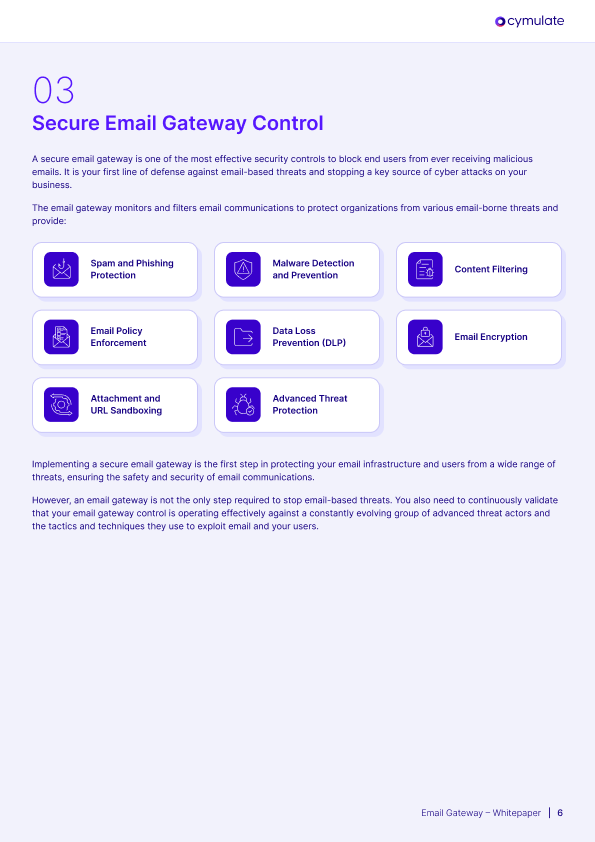
Cymulate's Email Gateway Validation is a production-safe, fully automated solution that continuously tests and validates your secure email gateway against the latest malicious links and payloads. It helps ensure your email security controls are operating as intended and capable of blocking modern email-borne threats. Source
What types of threats does Cymulate's Email Gateway Validation simulate?
The solution simulates a comprehensive suite of email-borne threats, including malicious links, malicious attachments, executable payloads, dummy code execution, true file type detection, and email attachment policies. Source
How often can I validate my email security controls with Cymulate?
Cymulate's breach and attack simulations are fully automated and production-safe, allowing you to validate your email security controls weekly using the latest malicious links and payloads. Source
Why is email gateway validation important for cybersecurity?
Email remains the #1 attack vector for cyber criminals, with 94% of organizations experiencing email-based security incidents and falling victim to phishing attacks. Continuous validation helps prevent cyber attacks by ensuring your email gateway is your first line of defense. Source
Is there a whitepaper available for email gateway validation best practices?
Yes, you can download the whitepaper 'Relieving the Stress from Email-based Threats' for practical guidance and best practices on testing and validating your secure email gateway. Download the Whitepaper
What featured resources are available to learn more about Cymulate's platform?
Featured resources include the Cymulate Exposure Management Platform data sheet, the Exposure Management Product Whitepaper, and the Omdia report highlighting validation and prioritization capabilities. Find more at our resources page.
Where can I find Cymulate's thought leadership content like whitepapers, reports, and e-books?
You can access Cymulate's thought leadership content, including whitepapers, reports, and e-books, through our Resource Hub.
How does Cymulate help organizations prevent email-based cyber attacks?
Cymulate helps organizations prevent email-based cyber attacks by continuously testing, validating, and optimizing email gateway controls against the latest threats, ensuring that malicious emails are blocked before reaching users. Source
What are the most common email-borne threats organizations face?
The most common email-borne threats include phishing attacks, malicious links, ransomware, and malicious attachments. According to Egress Software, 94% of organizations suffered email security incidents, and 69% of ransomware attacks began with an email. Source
How does Cymulate's Email Gateway Assessment work?
Cymulate's Email Gateway Assessment uses breach and attack simulations to validate the efficacy of email defenses. It tests for malicious links, attachments, executable payloads, dummy code execution, true file type detection, and email attachment policies. Source
Where can I find resources like whitepapers, reports, and product information?
You can find a combination of insights, thought leadership, and Cymulate product information in our Resource Hub.
Is there a whitepaper available about validating and optimizing email gateway controls against email-based threats?
Yes, we have a whitepaper titled 'The Stress from Email-based Threats' which serves as a practical guide for validating and optimizing email gateway controls. Learn More
What specific areas does Cymulate's Email Gateway Assessment cover?
Cymulate's Email Gateway Assessment covers malicious links and attachments, executable payloads, dummy code execution, true file type detection, and email attachment policies. Source
What resources are available to learn more about Email Gateway Validation?
Resources include the Email Gateway Validation Solution Brief, a blog post on validation best practices, and the 'Stress from Email-based Threats' whitepaper. Find more at our resources page.
Can you provide a customer success story about how Cymulate identified and helped remediate an email gateway flaw?
Yes. In the story 'Caught, But Not Contained: The Email Gateway Flaw,' Cymulate helped an insurance company reconfigure its email gateway to quarantine emails if even one antivirus detected ransomware, reducing the risk score from 30 to 5 in one hour. Source
What remediation guidance did Cymulate provide to the insurance customer to fix their email gateway?
Cymulate guided the customer's security team to reconfigure its email gateway to quarantine an email even if only one antivirus detects ransomware, ensuring any flagged email would be stopped. Source
What specific email gateway exposure did Cymulate identify for the insurance customer in the 'Caught, But Not Contained' story?
Cymulate assessments showed the gateway allowed emails to be delivered if only one of its seven antiviruses detected ransomware, blocking only if multiple antiviruses flagged it. Source
Can you provide an overview of the customer story 'The Nesting Trick That Bypassed the Gateway'?
In this story, Cymulate helped a banking client discover a critical exposure where the gateway blocked single attachments but failed to block emails containing a zip file with a nested executable. The team closed the gap in about 4 weeks with Cymulate's guidance. Source
How does Cymulate's platform integrate with other security tools?
Cymulate integrates with a wide range of technology partners across network, cloud, endpoint, and SIEM domains, including Akamai Guardicore, AWS GuardDuty, CrowdStrike Falcon, and more. See full list
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its user-friendly and intuitive platform. Testimonials highlight easy implementation, actionable insights, and accessible support. Read testimonials
How long does it take to implement Cymulate?
Cymulate is designed for quick, agentless deployment, requiring minimal resources. Customers can start running simulations almost immediately after deployment. Source
What support options are available for Cymulate customers?
Cymulate offers email support, real-time chat support, a knowledge base, webinars, e-books, and an AI chatbot for technical queries and best practices. Source
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs, determined by package, number of assets, and scenarios selected. For a quote, schedule a demo.
Features & Capabilities
What are the key capabilities of Cymulate?
Cymulate offers continuous threat validation, attack path discovery, automated mitigation, detection engineering, complete kill chain coverage, and an extensive threat library with daily updates. Source
What business impact can customers expect from using Cymulate?
Customers report an 81% reduction in cyber risk within four months, a 60% increase in operational efficiency, 40X faster threat validation, 30% improvement in threat prevention, and a 52% reduction in critical exposures. Read case study
What security and compliance certifications does Cymulate have?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, ensuring robust security and compliance. Source
How does Cymulate differ from similar products in the market?
Cymulate offers a unified, AI-driven platform integrating breach and attack simulation, continuous automated red teaming, and exposure prioritization. It provides measurable outcomes, continuous innovation, and ease of use, addressing pain points for CISOs, SecOps, Red Teams, and Vulnerability Management teams. See comparisons
Competition & Comparison
Who are Cymulate's main competitors?
Main competitors include AttackIQ, Mandiant Security Validation, Pentera, Picus Security, SafeBreach, and Scythe. See full comparison
How does Cymulate compare to AttackIQ?
AttackIQ delivers automated security validation but lacks Cymulate's innovation, threat coverage, and ease of use. Cymulate offers the industry's leading threat scenario library and AI-powered capabilities. Read more
How does Cymulate compare to Mandiant Security Validation?
Mandiant is one of the original BAS platforms but has become outdated with little innovation in the past 5 years. Cymulate continually innovates with AI and automation, expanding into exposure management. Read more
How does Cymulate compare to Pentera?
Pentera focuses on attack path validation but lacks the depth Cymulate provides to fully assess and strengthen defenses. Cymulate offers comprehensive exposure validation, covering the full kill chain and providing cloud control validation. Read more
Use Cases & Benefits
Who is the target audience for Cymulate's products?
Cymulate is designed for CISOs, Security Leaders, SecOps teams, Red Teams, and Vulnerability Management teams across industries such as finance, healthcare, retail, media, transportation, and manufacturing. Learn more
What pain points does Cymulate solve for customers?
Cymulate addresses overwhelming threat volumes, lack of visibility, unclear prioritization, operational inefficiencies, fragmented tools, cloud complexity, and communication barriers for CISOs. Source
How does Cymulate solve pain points for different personas?
Cymulate provides quantifiable metrics for CISOs, automates processes for SecOps, offers advanced threat simulation for Red Teams, and consolidates risk prioritization for Vulnerability Management teams. Source
What core problems does Cymulate solve?
Cymulate solves overwhelming threat volumes, lack of visibility, unclear prioritization, operational inefficiencies, fragmented tools, cloud complexity, and communication barriers. Source