External Attack Surface Management (EASM)
External Attack Surface Management (EASM) is a cybersecurity practice of continuously discovering, monitoring and securing an organization’s internet-facing assets to reduce exposure to external threats.
It provides an “outside-in” view of your digital footprint by identifying all publicly accessible systems (websites, cloud services, APIs, etc.) and assessing them for vulnerabilities.
As organizations increasingly rely on cloud services and remote networks beyond the traditional perimeter, EASM plays a critical role in illuminating external risk. Gartner reports that cloud adoption and hybrid work have “accelerated the expansion of enterprises’ external attack surfaces,” leading to more exposures that security teams must manage.
By giving security teams the same view an attacker has, EASM allows businesses to find and fix weaknesses before hackers can exploit them.
What is External Attack Surface Management (EASM)?
External Attack Surface Management (EASM) is a proactive cybersecurity approach focused on identifying, managing, and reducing risks tied to an organization’s public-facing assets—such as websites, cloud storage, APIs and SaaS apps.
Unlike traditional security tools that concentrate on internal networks, EASM views the organization from an attacker’s perspective, continuously mapping what’s visible and vulnerable on the internet.
EASM differs from general Attack Surface Management (ASM) by zeroing in solely on assets accessible from the public internet. While internal ASM protects systems within your network, EASM exposes blind spots outside the firewall that traditional tools might miss.
It also differs from Cyber Asset Attack Surface Management (CAASM), which aims to provide a complete view of all assets (both internal and external) by aggregating data across systems. In contrast, EASM focuses strictly on external-facing assets—making it a key component of broader exposure management strategies.
How External Attack Surface Management Identifies Risks
External Attack Surface Management (EASM) functions as a continuous, automated process that identifies and reduces risks tied to an organization’s internet-facing assets. It mimics an attacker’s view of your infrastructure, constantly scanning for exposures and enabling faster response.
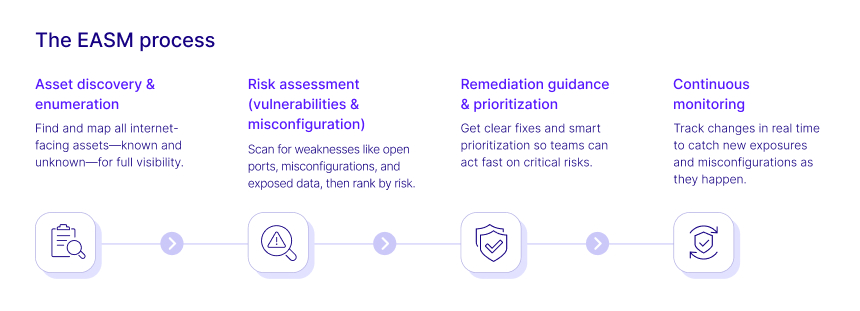
1. Asset discovery & enumeration
The first and foundational step of EASM is discovering all external-facing assets and enumerating their technical details. This includes domains, subdomains, IP addresses, cloud instances, APIs, web applications and other internet-exposed resources.
EASM platforms use a variety of techniques to uncover assets—DNS scanning, certificate transparency logs, cloud provider APIs, search engine indexing, and open-source intelligence (OSINT). These tools often detect assets created outside of IT’s purview (known as shadow IT), as well as forgotten systems that still pose a risk.
As Forrester describes, EASM tools continually scan for, identify, and fingerprint known and unknown assets, highlighting potential exposures. The result is a comprehensive, real-time inventory of public-facing systems that attackers could target.
2. Risk assessment (vulnerabilities & misconfigurations)
Once assets are discovered, EASM platforms evaluate them for weaknesses. They conduct non-intrusive scans and run configuration and vulnerability checks to uncover:
- Open ports and services
- Unpatched software or outdated libraries
- Misconfigured cloud storage (e.g., exposed S3 buckets)
- Expired SSL certificates
- Leaked credentials or sensitive data
- Exposed administrative panels or development tools
Importantly, modern EASM solutions enrich this raw data with threat intelligence—highlighting, for instance, whether a vulnerability is being actively exploited in the wild. Findings are then risk-ranked based on severity, exposure level, and exploitability.
This risk-based assessment model helps security teams cut through the noise and focus on what matters most, rather than being overwhelmed with raw scan results.
3. Remediation guidance & prioritization
After identifying risks, EASM platforms help teams prioritize and act. Each exposure is scored based on its severity and potential impact, with critical findings pushed to the top. For example, a misconfigured server hosting sensitive data would take precedence over a low-risk informational disclosure.
EASM tools often provide:
- Remediation guidance (e.g., patching instructions or config changes)
- Risk context (business impact, asset classification)
- Integration with ticketing tools like Jira or ServiceNow
- Workflow automation via SIEM or SOAR platforms
Some advanced solutions enable automated incident creation, firewall rule updates, or alert escalations when high-risk exposures are detected. While EASM platforms generally don’t remediate issues directly, they ensure the right people are alerted and supported with actionable data.
4. Continuous monitoring
A core advantage of EASM is its ongoing vigilance. The external attack surface is highly dynamic—new apps are deployed, cloud assets are spun up, and changes occur across domains and partner integrations. A one-time scan is insufficient.
EASM platforms conduct continuous or periodic scanning, tracking changes in real time and detecting:
- Newly exposed services
- Policy drift or misconfigurations
- Vulnerability re-emergence after updates
- Unauthorized changes to public-facing systems
This persistent monitoring acts like a digital watchtower—flagging security gaps as they emerge, not weeks or months later. For instance, if a developer accidentally exposes a staging database to the internet, EASM alerts security teams within hours.
The Lifecycle Approach
Together, these components form a closed-loop, proactive lifecycle:
- Discover assets
- Enumerate and assess exposures
- Prioritize and guide remediation
- Monitor continuously for changes
- Repeat
This loop enables organizations to reduce exposure windows, identify vulnerabilities before threat actors do, and continuously harden their external perimeter. When implemented effectively, EASM provides a scalable and strategic way to manage external risk and supports broader exposure management efforts.
Why External Attack Surface Management is Critical for Cybersecurity
As organizations increasingly operate in the cloud and rely on digital services, their attack surface extends far beyond the internal network.
EASM is essential because it provides visibility and control over these external-facing assets—those most visible and vulnerable to threat actors. Here’s why it matters:
Expanding digital footprint
Modern businesses deploy countless public-facing endpoints—from cloud services and SaaS apps to IoT devices and third-party integrations.
This expansion, fueled by remote work and cloud adoption, dramatically increases exposure to external threats. Without EASM, unknown or forgotten assets can go undetected until exploited. EASM ensures continuous discovery and tracking of these assets, helping teams stay ahead of their ever-growing digital footprint.
Blind spots in traditional security
Conventional tools like firewalls and vulnerability scanners are designed for internal environments. They often overlook assets deployed outside the network perimeter, such as an outdated subdomain or an unsecured cloud server.
EASM fills this gap by identifying shadow IT and unmanaged external infrastructure, giving security teams visibility into what attackers can already see online.
Preventing breaches and data leaks
External exposures are a common entry point for attackers. Misconfigured cloud storage, unpatched web servers, or compromised credentials can quickly lead to data breaches.
EASM minimizes this risk by detecting vulnerabilities early—before they can be exploited—making it a proactive line of defense that significantly reduces the likelihood of cyber incidents.
Compliance and trust
Regulations and cybersecurity frameworks increasingly demand up-to-date asset inventories and prompt vulnerability management.
EASM helps organizations meet these requirements by documenting external assets and demonstrating continuous risk monitoring. It also strengthens third-party risk oversight and shows due diligence in audits, improving customer and stakeholder trust.
EASM vs. Other Security Approaches
External Attack Surface Management (EASM) complements and enhances other cybersecurity practices by focusing on discovering and managing unknown, internet-facing assets. Here's how it compares to other common approaches:
EASM vs. vulnerability management (VM)
Vulnerability Management targets known internal systems, scanning them periodically for vulnerabilities and applying patches. In contrast, EASM begins with discovery, identifying unknown or unmanaged external assets before assessing their risks.
- VM = focuses on known assets within defined scopes.
- EASM = uncovers unknown, external assets outside traditional inventories.
Together, they create a comprehensive risk picture—EASM feeds findings into the VM process for deeper remediation.
EASM vs. attack surface reduction (ASR)
Attack Surface Reduction is about minimizing potential entry points by disabling or removing unnecessary assets, services, or permissions. EASM supports ASR by mapping the external environment and flagging misconfigured or unnecessary assets.
- EASM = discovers what’s exposed.
- ASR = reduces and hardens what’s exposed.
They work hand-in-hand—EASM finds vulnerabilities; ASR eliminates them.
EASM vs. exposure management
Exposure Management is a broader strategy that continuously identifies and prioritizes cyber risks across internal, external, and identity-based attack surfaces. EASM plays a critical role within Exposure Management by focusing on public-facing assets.
- Exposure Management = full-spectrum visibility and risk prioritization.
- EASM = focuses on external exposure, feeding critical data into the broader exposure landscape.
If Exposure Management is the whole chessboard, EASM is a key piece that monitors the external side.
Key Benefits of EASM
Implementing External Attack Surface Management (EASM) offers organizations significant advantages in proactively securing their internet-facing assets.

- Complete external visibility & early threat detection: EASM delivers a real-time, comprehensive map of all external-facing assets—known and unknown—giving security teams the same view as attackers. By uncovering shadow IT, outdated systems, and forgotten websites, it surfaces potential threat vectors often missed by traditional tools. This early warning capability allows for proactive mitigation before vulnerabilities are exploited.
- Continuous risk monitoring & prioritization: Unlike point-in-time assessments, EASM continuously monitors for changes across the external attack surface. It tracks new exposures, misconfigurations, and asset additions, updating dashboards and risk scores in real time. By enriching findings with context (e.g., asset criticality, active threats), EASM highlights the risks that truly matter, helping teams focus efforts and avoid alert fatigue.
- Faster remediation & reduced exposure time: EASM shortens the window between exposure and remediation by alerting teams quickly—sometimes within hours of a change. This enables faster patching and configuration fixes, reducing the time vulnerabilities remain exploitable. Risk-based prioritization ensures the most critical issues are addressed first, transforming emergency incidents into routine remediation workflows.
- Improved third-party risk management: An organization’s external attack surface often includes assets from subsidiaries, vendors, or partners. EASM sheds light on these third-party exposures, such as insecure vendor systems or inherited vulnerabilities from acquisitions. This visibility is vital as supply chain attacks continue to surge, allowing teams to evaluate and manage risks beyond their direct control.
- Enhanced compliance & reporting: While not its primary goal, EASM supports compliance efforts by providing audit-ready asset inventories and risk trend reports. Security leaders can demonstrate continuous risk management and measurable improvement over time—building trust with regulators, auditors, and stakeholders through clear, data-backed insights into their external security posture.
EASM Tools & Solutions
The growing importance of External Attack Surface Management (EASM) has led to the development of a wide range of tools, many of which share common capabilities designed to help organizations gain control over their internet-facing assets.
Automated, AI-powered discovery
Leading EASM platforms use automation and AI/ML to continuously scan the internet for exposed assets. They analyze data sources like DNS records, cloud metadata, and certificate logs to identify domains, IPs, and infrastructure associated with an organization.
AI improves attribution accuracy and reduces false positives by filtering out unrelated assets. These tools are typically agentless and scalable, operating externally without impacting internal systems—making deployment fast and non-intrusive.
Centralized asset inventory & classification
EASM solutions maintain a dynamic, categorized inventory of discovered assets—grouped by type (e.g., domains, web apps, IoT devices). This inventory is presented through interactive dashboards, often allowing tagging by business unit or asset criticality.
Some tools integrate with internal CMDBs to reconcile asset data and support IT governance. A comprehensive inventory forms the foundation for risk monitoring and strategic remediation.
Vulnerability & exposure analysis
Beyond discovery, EASM tools assess each asset’s risk posture using port scans, vulnerability databases, configuration checks, and SSL analysis. They often integrate threat intelligence to detect if specific vulnerabilities are actively being exploited. Some also offer web application scanning.
The result is a clear picture of which assets are risky—and why—allowing teams to prioritize based on real-world threats, not just raw findings.
Real-time alerting & reporting
EASM platforms deliver alerts when critical exposures or new assets are found, through email, Slack, or integrated dashboards.
They also provide scheduled reports, executive summaries, and trend charts to track changes in the external attack surface. Customizable alert thresholds help reduce noise and ensure high-priority risks are acted upon quickly.
Integration with existing security ecosystem
Top EASM tools integrate with SIEMs (like Splunk), XDR, SOAR platforms, and IT ticketing systems (e.g., Jira, ServiceNow). These integrations enable seamless incident handling, automated remediation workflows, and better correlation between external exposures and internal threat signals.
Integration ensures EASM fits into an organization's existing processes, enhancing operational efficiency.
Digital risk protection (DRP) capabilities
Some EASM solutions extend into brand and threat monitoring by detecting typosquatted domains, leaked credentials, and mentions in dark web forums.
These features enhance traditional EASM by flagging indicators of external abuse or impersonation. While not core to all EASM tools, this convergence with DRP strengthens overall threat awareness and defense.
How External Attack Surface Management Enhances Cymulate
Cymulate puts validation at the heart of exposure management with market-leading external attack surface management (EASM), breach and attack simulation (BAS) and automated red teaming (CART), so you can focus on what’s truly exploitable in your environment. By adding automated discovery of your external attack surface, you can see every asset from the attacker’s view to discover threat exposures and prioritize remediation.
Exposure validation through security testing
What sets Cymulate apart is its ability to validate whether exposures are truly exploitable. Using BAS and CART, Cymulate tests external vulnerabilities in real-world attack scenarios. This allows teams to prioritize risks based on actual exploitability, not just theoretical severity.
Closed-loop remediation and continuous improvement
Cymulate guides remediation with actionable fixes and can push custom detection rules or IoCs to tools like SIEMs and EDRs. After remediation, the platform re-tests exposures to confirm resolution. Its dashboards and analytics help track posture improvement over time—supporting a risk-based, iterative approach to security enhancement.
Unified external and internal visibility
Cymulate goes beyond EASM by also mapping internal assets and attack paths. This unified view—aligned with CAASM principles—shows how external exposures could lead to internal compromise, providing a holistic understanding of your security posture from both outside and inside perspectives.
Seamless integration and ease of use
Agentless and cloud-based, Cymulate is quick to deploy and integrates easily with third-party tools like SIEMs, ticketing systems, and vulnerability managers. This makes incorporating EASM into existing security workflows frictionless and scalable.
In short, Cymulate delivers both discovery and validation, enabling organizations to identify critical external exposures and test their impact—helping teams prioritize and remediate effectively.
Key Takeaways
EASM is the continuous discovery and monitoring of internet-facing assets (e.g., websites, APIs, cloud services) to detect vulnerabilities and reduce external risk. It provides an outside-in, attacker’s-eye view of an organization’s exposure, enabling proactive mitigation before issues are exploited.
Digital transformation and cloud adoption have expanded the attack surface, making EASM critical to uncover unknown, unmanaged, or shadow IT assets. EASM delivers comprehensive visibility, real-time risk scoring, prioritized remediation, and improves management of third-party and supply chain risks. It complements existing security tools—enhancing vulnerability management, supporting attack surface reduction, and contributing to broader exposure management programs.
Common challenges include handling alert noise, asset sprawl, and integration with workflows—but these can be addressed with proper implementation. Leading EASM solutions are automated, AI-powered, agentless, and integrate with SIEM, SOAR, and ticketing systems for seamless operations.