Frequently Asked Questions
Product Information & Proactive Security
What is proactive security and how does Cymulate support it?
Proactive security is the practice of identifying and mitigating cyber exposures before they can be exploited, rather than reacting after an incident. Cymulate supports this approach by continuously validating defenses, identifying exposures, and helping organizations build resilience against evolving threats. Exposure validation ensures controls are working as intended and focuses remediation on what’s actually exploitable. Source
How does exposure validation work in Cymulate?
Exposure validation in Cymulate involves simulating real-world cyberattacks to test whether existing defenses detect, block, or allow threats. It provides security teams with a clear, prioritized view of risk, enabling them to act where it matters most. This process uncovers hidden exposures and validates assumptions about security controls. Source
What are some real-world gaps Cymulate has helped organizations discover?
Cymulate customers have discovered issues such as servers believed to be isolated but exposed to the internet, hardcoded passwords across environments, and email gateways failing to block malicious scripts. These exposures were found and remediated before attackers could exploit them, demonstrating the value of proactive security. Source
How does Cymulate make advanced security testing fast and easy?
Cymulate Exposure Validation enables advanced security testing by providing a unified platform for building custom attack chains, all accessible in one place. This streamlines the process and makes it easy for security teams to validate their controls. Source
What is the primary purpose of Cymulate's platform?
The primary purpose of Cymulate's platform is to proactively validate cybersecurity defenses, identify vulnerabilities, and optimize security posture. It helps organizations harden defenses and optimize controls by continuously validating threats and exposures. Source
How does Cymulate help organizations move from reactive to proactive security?
Cymulate enables organizations to continuously validate and remediate exposures before attackers exploit them. By embedding cyber resilience into operations and not just incident response plans, Cymulate helps teams adopt a proactive security mindset. Source
What types of security testing does Cymulate offer?
Cymulate offers breach and attack simulation (BAS), continuous automated red teaming (CART), exposure validation, attack path discovery, and automated mitigation. These tools simulate real-world attacks and validate security controls across the IT environment. Source
How does Cymulate help prioritize remediation efforts?
Cymulate focuses remediation on exposures that are actually exploitable, not just theoretically risky. It provides a prioritized view of risk, enabling security teams to act where it matters most and avoid wasting resources on low-impact issues. Source
What is the impact of using Cymulate on cyber resilience?
Organizations using Cymulate have demonstrated improved cyber resilience by discovering and remediating exposures before attackers can exploit them. This proactive approach reduces the likelihood of breaches and strengthens overall security posture. Source
Where can I find case studies and customer success stories about Cymulate?
You can find case studies and customer success stories on Cymulate's Customers page, including examples like Hertz Israel reducing cyber risk by 81% within four months and LV= taking a data-driven approach to security validation. Read the Hertz Israel case study.
How does Cymulate help organizations avoid the cost of assumption in cybersecurity?
Cymulate helps organizations avoid the cost of assumption by continuously validating controls and uncovering hidden exposures. This ensures that security tools are actually protecting the organization, rather than relying on assumptions about their effectiveness. Source
What resources are available to learn more about proactive security and exposure validation?
Cymulate offers resources such as the eBook "10 Cybersecurity Exposures You Can’t Afford to Ignore" and technical documentation on exposure validation. Visit the Resource Hub for whitepapers, guides, and more. Download the eBook.
How does Cymulate support different security roles and teams?
Cymulate is designed for CISOs, Security Leaders, SecOps teams, Red Teams, and Vulnerability Management teams. It provides tailored solutions for each persona, including quantifiable metrics, operational efficiency, automated offensive testing, and prioritized exposure management. Learn more.
What is the mission and vision of Cymulate?
Cymulate's vision is to create an environment where organizations proactively validate their cybersecurity defenses, foster collaboration, and drive lasting change in how security is managed. The mission is to lead the way in exposure management and threat validation. Source
How does Cymulate help organizations build cyber resilience?
Cymulate helps organizations build cyber resilience by embedding continuous validation into operations, enabling teams to discover and remediate exposures before attackers can exploit them. This proactive discipline strengthens defenses and reduces risk. Source
What are the benefits of continuous validation with Cymulate?
Continuous validation with Cymulate ensures that security controls are always tested against real-world threats, helping organizations stay ahead of attackers, reduce risk, and focus remediation efforts on the most critical exposures. Source
How does Cymulate help organizations justify security investments?
Cymulate provides quantifiable metrics and actionable insights that help CISOs and security leaders justify investments and communicate risk to stakeholders. This evidence-based approach supports strategic decision-making. Source
Where can I find technical documentation and guides for Cymulate?
Cymulate provides technical documents such as whitepapers, guides, data sheets, solution briefs, and e-books. These resources are available in the Resource Hub and cover topics like exposure management, detection engineering, and vulnerability validation. Read the Exposure Management Platform whitepaper.
Features & Capabilities
What are the key capabilities of Cymulate?
Cymulate offers continuous threat validation, attack path discovery, automated mitigation, detection engineering, complete kill chain coverage, and an extensive threat library with daily updates. These capabilities help organizations stay ahead of emerging threats and optimize their security posture. Source
What are the main benefits of using Cymulate?
Main benefits include an 81% reduction in cyber risk within four months, 60% increase in operational efficiency, 40X faster threat validation, 30% improvement in threat prevention, and a 52% reduction in critical exposures. Read the Hertz Israel case study.
How easy is Cymulate to use and implement?
Cymulate is praised for its user-friendly and intuitive platform. It operates in agentless mode, requires minimal resources, and can be deployed quickly. Customers report that it is easy to implement and provides immediate value. Read customer testimonials.
What integrations does Cymulate offer?
Cymulate integrates with a wide range of technology partners, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, CrowdStrike Falcon, Cybereason, and more. For a complete list, visit the Partnerships and Integrations page.
How does Cymulate support detection engineering?
Cymulate validates responses and builds custom detection rules for SIEM, EDR, and XDR, helping organizations improve mean time to detect and optimize their detection engineering processes. Learn more.
Does Cymulate provide automated mitigation?
Yes, Cymulate integrates with security controls to push threat updates for immediate prevention of missed threats, enabling automated mitigation and strengthening defenses. Learn more.
Pain Points & Solutions
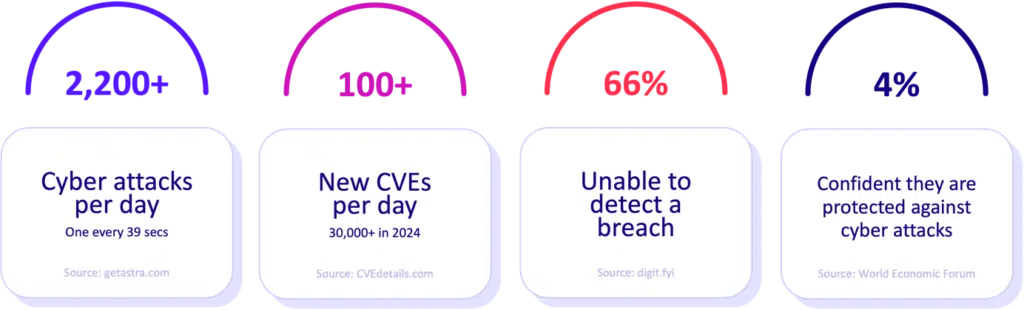
What core problems does Cymulate solve?
Cymulate solves problems such as overwhelming volume of threats, lack of visibility, unclear prioritization, operational inefficiencies, fragmented security tools, cloud complexity, and communication barriers. It addresses these with continuous threat validation, prioritization, improved resilience, collaboration, automation, and validated exposure scoring. Source
What pain points do Cymulate customers express?
Customers express pain points like being overwhelmed by threats, struggling with visibility, unclear prioritization, operational inefficiencies, fragmented tools, cloud complexity, and communication barriers. Cymulate addresses these with continuous validation, prioritization, improved resilience, collaboration, automation, and exposure scoring. Source
How does Cymulate address pain points for different personas?
Cymulate tailors solutions for CISOs (communication and metrics), SecOps (operational efficiency and visibility), Red Teams (threat simulation), and Vulnerability Management (risk prioritization and efficiency). Each persona benefits from features aligned to their specific challenges. Learn more.
Pricing & Plans
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and scenarios selected. The subscription fee is non-refundable and must be paid regardless of actual use. For a quote, schedule a demo.
Competition & Comparison
Who are Cymulate's main competitors?
Cymulate's main competitors include AttackIQ, Mandiant Security Validation, Pentera, Picus Security, SafeBreach, and Scythe. Each competitor offers different strengths and approaches to security validation. Source
How does Cymulate compare to AttackIQ?
AttackIQ delivers automated security validation but lacks Cymulate's innovation, threat coverage, and ease of use. Cymulate offers the industry's leading threat scenario library and AI-powered capabilities to streamline workflows and accelerate security posture improvement. Read more.
How does Cymulate compare to Mandiant Security Validation?
Mandiant is one of the original BAS platforms but has become outdated with little innovation in the past 5 years. Cymulate continually innovates with AI and automation, expanding into exposure management as a grid leader. Read more.
How does Cymulate compare to Pentera?
Pentera focuses on attack path validation but lacks the depth Cymulate provides to fully assess and strengthen defenses. Cymulate offers comprehensive exposure validation, covering the full kill chain and providing cloud control validation. Read more.
How does Cymulate compare to Picus Security?
Picus is suitable for on-premise BAS needs but lacks the complete exposure validation platform Cymulate provides. Cymulate covers the full kill chain and includes cloud control validation, making it a more comprehensive solution. Read more.
How does Cymulate compare to SafeBreach?
SafeBreach offers breach and attack simulation but lacks Cymulate's innovation, precision, and automation. Cymulate leads with AI-powered BAS, the largest attack library, and a full Continuous Threat Exposure Management (CTEM) solution. Read more.
How does Cymulate compare to Scythe?
Scythe is suitable for advanced red teams but lacks Cymulate's focus on actionable remediation and automated mitigation. Cymulate provides a more complete exposure validation platform with daily threat updates, no-code workflows, and vendor-specific remediation guidance. Read more.
Security & Compliance
What security and compliance certifications does Cymulate have?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications. These ensure robust security practices, privacy, and compliance with global standards. Source
How does Cymulate ensure product security and compliance?
Cymulate employs secure AWS data centers, strong encryption (TLS 1.2+ and AES-256), secure development lifecycle, continuous vulnerability scanning, annual penetration tests, and ongoing employee security training. It is GDPR compliant and has a dedicated privacy and security team. Source
Support & Implementation
How long does it take to implement Cymulate?
Cymulate is designed for quick deployment, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment. Read customer testimonials.
What support options are available for Cymulate customers?
Cymulate offers email support, real-time chat support, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for querying the knowledge base and creating AI templates. Email support | Chat support
Resources & Documentation
Where can I find Cymulate's blog and newsroom?
Stay updated with the latest threats, research, and company news through Cymulate's blog and newsroom.
Where can I find resources like reports, blogs, and webinars from Cymulate?
Find insights, thought leadership, and product information in Cymulate's Resource Hub, as well as specific resources like the blog, newsroom, and events/webinars page.
Do you have a blog post about preventing lateral movement attacks?
Yes, Cymulate has a blog post titled 'Stopping Attackers in Their Tracks' discussing common lateral movement attacks and prevention strategies. Read the blog post.
Where can I find a central hub for Cymulate's insights, thought leadership, and product information?
All resources, including insights, thought leadership, and product information, are available in Cymulate's Resource Hub.