Cymulate Expands WAF Validation with OAuth 2.0 Support
Avigayil Stein, Product Marketing Manager
Yoni Harris, Product Manager
Validating modern web applications just got easier
Cymulate now supports OAuth 2.0 authentication for web application firewall (WAF) assessments, enabling organizations to validate web applications secured with modern single sign-on (SSO) methods from identity providers such as Okta, Azure AD, Ping Identity, Google Workspace and Auth0.
This new capability significantly expands the platform’s ability to test modern web applications that use advanced authentication methods. With OAuth 2.0 support, enterprises can now validate up to 70% more web applications that were previously inaccessible. Early adopters have also reported up to 40% faster validation setup when testing authenticated environments.
Until now, WAF validation was limited to web applications using basic authentication. With OAuth 2.0, Cymulate customers can now assess authenticated, SSO-protected environments – a critical need for enterprises securing high-value applications behind modern identity systems.
Highlights
- Cymulate adds OAuth 2.0 support to WAF validation, enabling assessments of modern web applications using SSO authentication from providers like Okta, Azure AD and Auth0.
- Validate both public and authenticated web apps, expanding coverage to up to 70% more applications that were previously inaccessible to traditional WAF testing.
- OWASP-aligned attack simulations now extend to identity-protected endpoints, testing real-world exploits such as SQLi, XSS, RFI and command injection.
- Cymulate is one of the only exposure validation platforms that supports OAuth 2.0 for automated crawling of authenticated, SSO-protected web applications.
Why OAuth 2.0 support changes the game
By supporting OAuth 2.0, the Cymulate WAF validation can now test the security and effectiveness of protections within authenticated areas of web applications. This provides deeper, more accurate testing of protected assets that were previously inaccessible without advanced authentication capabilities.
Enterprises using secure SSO platforms can now seamlessly include their protected applications in Cymulate simulations. This expansion makes Cymulate compatible with a broader range of real-world environments, positioning it as one of the only exposure validation platforms that support OAuth for automated crawling.
OAuth 2.0 also aligns with how modern enterprises authenticate users and systems.
Instead of passing around credentials, authentication flows through secure token exchange, enabling fully automated and secure simulations without manual logins or redirects. Security teams can now continuously test WAF defenses in production-like environments without disrupting users or triggering anti-bot mechanisms on platforms like Cloudflare or Zscaler.
Breaking through authentication barriers with automated OAuth validation
With OAuth 2.0, Cymulate WAF simulations can now test authenticated web applications; the areas attackers are most likely to target once past login controls. Using secure token exchange, the platform accesses OAuth-protected endpoints and launches OWASP-aligned exploit payloads, such as SQLi, XSS, RFI and command injection, to measure how effectively web application firewalls and application-layer defenses respond.
Cymulate automatically handles the full OAuth token exchange, eliminating manual authentication steps and reducing setup time by up to 60% compared to manual testing. Because Cymulate WAF assessments remain fully agentless and external, there’s no need for manual logins or internal access points. The result is a realistic, continuous simulation that evaluates whether your WAF detects, blocks, or allows malicious activity on both public and authenticated routes.
These insights reveal which threats are prevented, which slip through and where fine-tuning is needed to harden protections. It’s the same continuous exposure validation approach Cymulate customers already rely on across email, endpoint and cloud environments, now extended to the web applications that power their business.
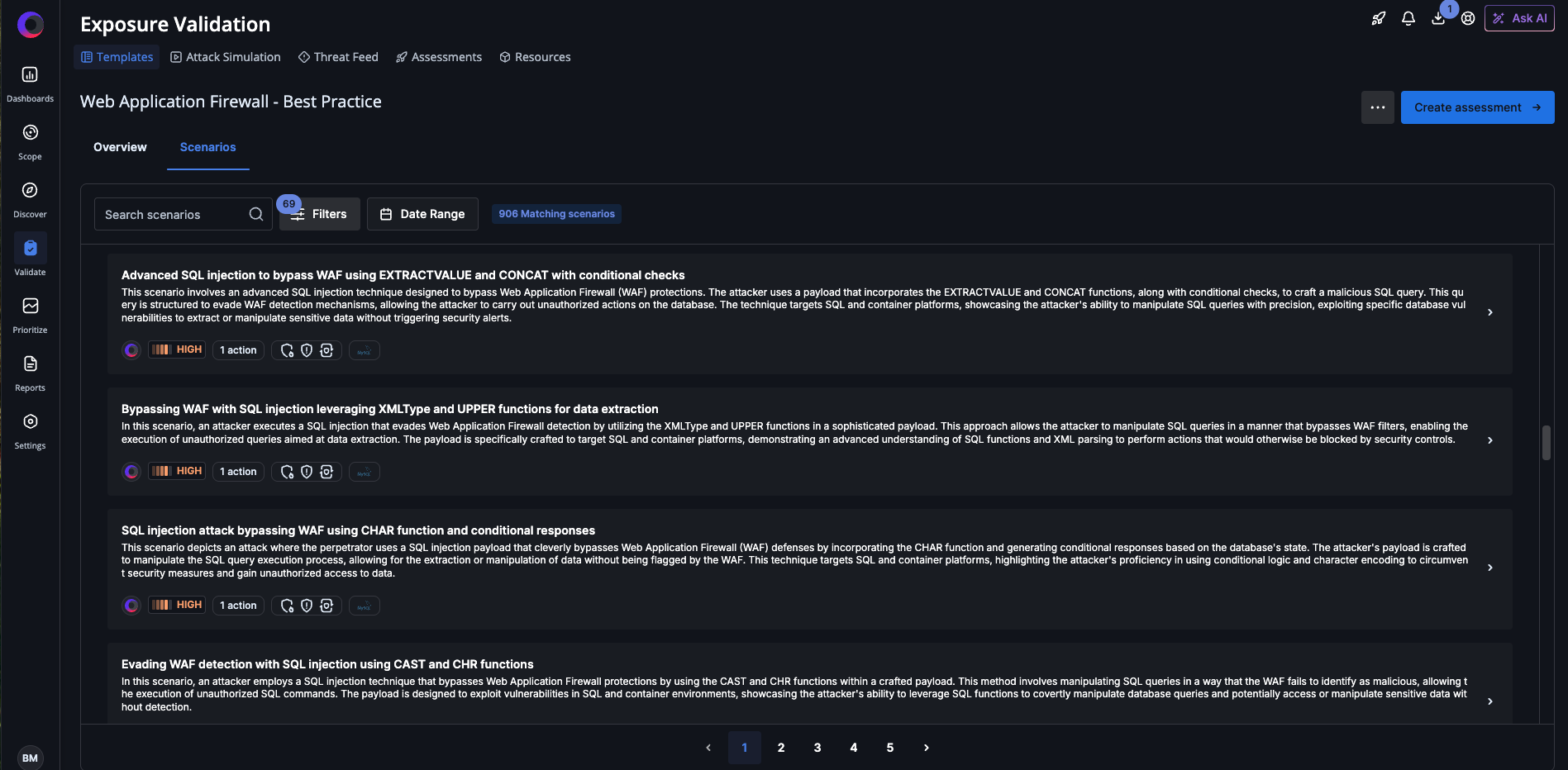
Cymulate WAF best practice template contains scenarios that test and optimize WAF configurations against a wide range of attack patterns.
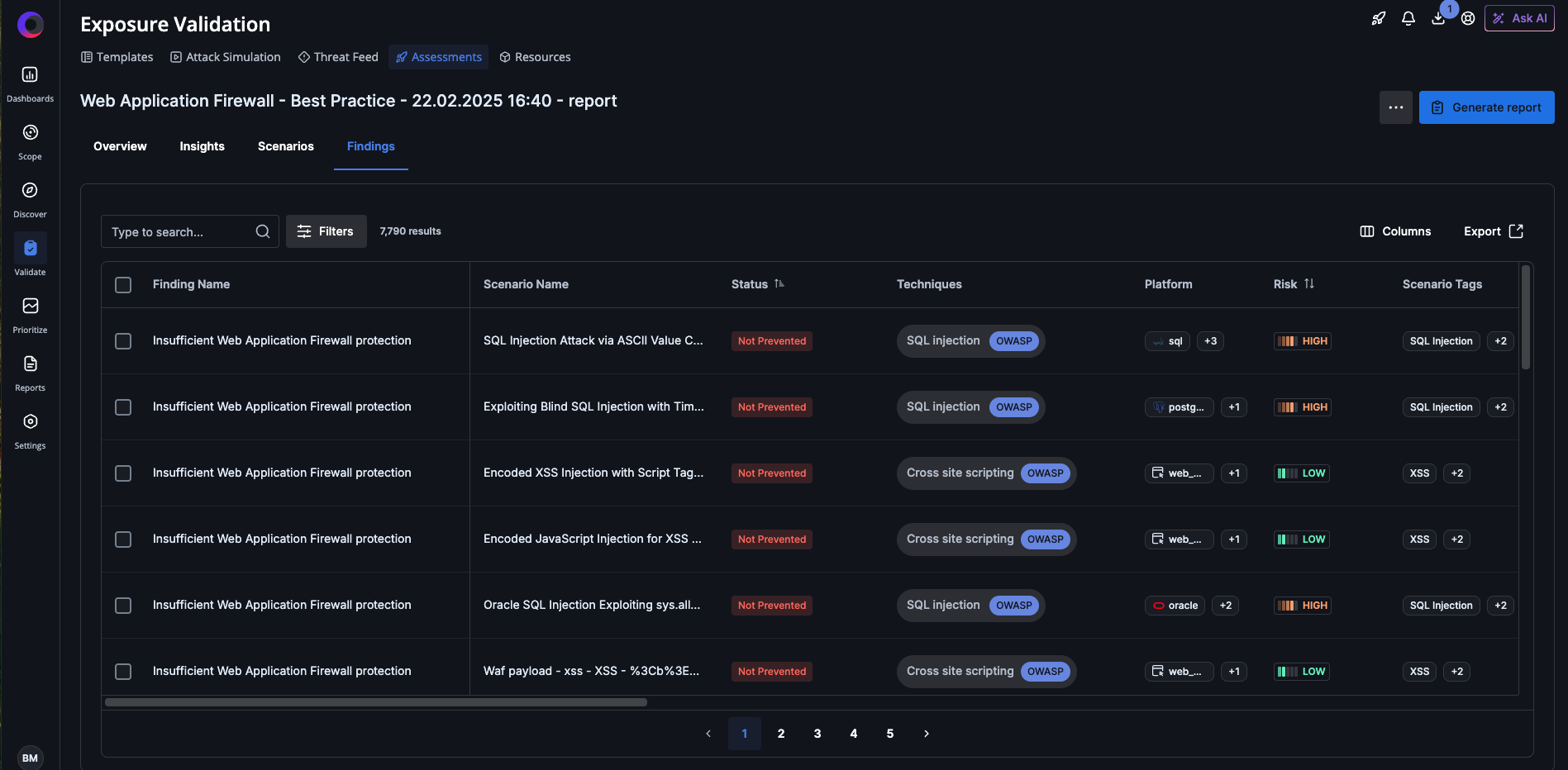
WAF findings enable you to identify gaps in prevention mechanisms, take remediation steps and optimize your organization's WAF.
Customer spotlight: Execs wanted speed, security demanded a WAF
A large retail enterprise learned the hard way that speed without security can be costly. After suffering a major cyberattack that took a revenue-critical server offline, the executive team wanted the system back in production immediately. However, the security team knew it needed to strengthen its WAF defenses before reestablishing the server that was affected.
The team conducted a Cymulate assessment, which revealed that 96% of web-based attacks successfully bypassed the organization’s defenses. Armed with this data, the security team quickly gained executive buy-in to deploy and tune a proper WAF.
Cymulate guided the customer in configuring the WAF, fine-tuned the rules and redeployed the server within two days. Since then, the organization has made Cymulate WAF assessments a mandatory step before every production release, ensuring every public-facing web service is protected before it goes live.
The bigger picture: Continuous, realistic validation for modern apps
With OAuth 2.0 support, Cymulate can now simulate how attacks behave in identity-driven environments, providing a more accurate view of real-world risk across authenticated web assets. Enterprises using OAuth or SSO authentication can now ensure their WAFs are equipped to withstand real-world attack techniques without compromising security or workflow.
For Cymulate customers already leveraging Exposure Validation across email gateways, endpoints, or cloud environments, this is the perfect time to expand into WAF testing. Modern web applications are often the most exposed, and now, validating them is simpler, safer and more comprehensive than ever.
Ready to test your WAF in real-world conditions?
See how the Cymulate WAF Assessments with OAuth 2.0 deliver continuous validation for modern, SSO-secured web applications. Contact your Cymulate representative or schedule a demo to get started.