Frequently Asked Questions
MITRE Engenuity Evaluation & Attack Scenarios
What is the MITRE Engenuity evaluation and how does it relate to Cymulate?
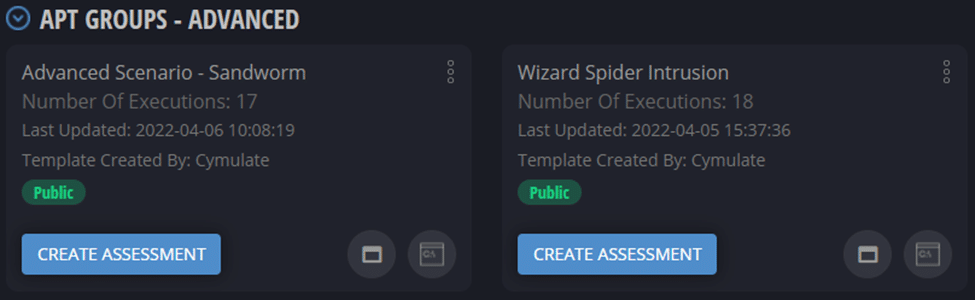
The MITRE Engenuity evaluation is an independent assessment that tests how security vendors' solutions detect, prevent, or mitigate real-life cyberattacks. Cymulate participates in these evaluations by emulating advanced persistent threat (APT) scenarios, such as Sandworm and Wizard Spider, to demonstrate its platform's ability to provide defenders with actionable information and automation for threat detection and response. Learn more.
How does Cymulate's evaluation approach differ from MITRE's methodology?
While MITRE Engenuity evaluates each attack step individually, Cymulate's platform connects all steps in a continuous, end-to-end attack chain, providing a holistic view of your organization's resilience across the full kill chain. This approach helps identify potential attack paths that step-by-step assessments might miss, offering more comprehensive security validation.
What are the key steps in the Sandworm scenario as emulated by Cymulate?
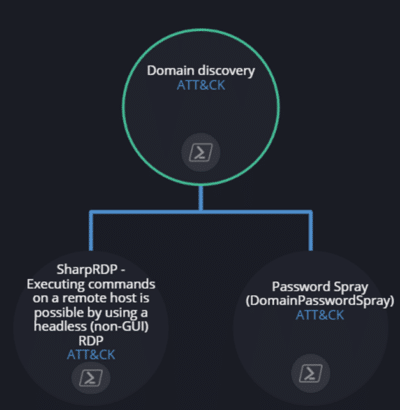
The Sandworm scenario includes 17 steps, starting with a phishing attachment and VBS script execution, followed by actions such as downloading files via WMI, creating admin users, SMB share creation, domain discovery, password spraying, RDP connections, keylogger installation, data exfiltration, file encryption, and log deletion. Cymulate visually displays the connections between these steps for in-depth analysis.
What does the Wizard Spider scenario simulate in Cymulate?
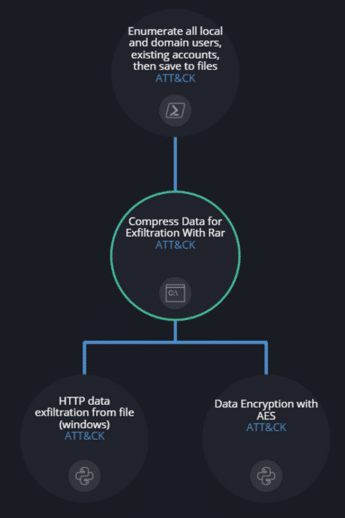
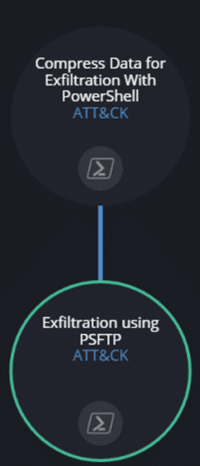
The Wizard Spider scenario simulates 18 steps, including internal discovery, lateral movement using AnyDesk and RDP, credential dumping, data compression and exfiltration, and deployment of domain-wide ransomware. Cymulate's dashboard shows the full attack chain, helping organizations assess their defenses against sophisticated ransomware campaigns.
How can organizations use Cymulate's MITRE-based scenarios to improve security?
Organizations can run Cymulate's Sandworm and Wizard Spider scenarios to assess their resilience against these advanced threats. After applying recommended fixes, rerunning the assessments helps verify improvements. Continuous validation is recommended to keep pace with evolving threats and frequent environment changes.
What is the benefit of using Cymulate's full kill chain emulation?
Cymulate's full kill chain emulation provides a realistic, end-to-end simulation of advanced attacks, revealing security gaps that might be missed by step-by-step assessments. This enables organizations to optimize their defenses and receive actionable recommendations for improvement.
How does Cymulate display attack chain connections in its dashboard?
Cymulate's dashboard visually displays the connections between different attack steps, allowing users to see how each action leads to the next. This visualization helps teams understand attack progression and identify where defenses may fail.
Why is continuous security validation recommended?
Continuous security validation is recommended because threats evolve rapidly and IT environments change frequently. Regular testing with Cymulate ensures that defenses remain effective and that new vulnerabilities are identified and addressed promptly.
How do Cymulate's results differ from MITRE Engenuity's published results?
Cymulate's results may differ from MITRE Engenuity's because Cymulate evaluates resilience across the entire attack chain, while MITRE assesses each step individually. This means Cymulate can uncover additional attack paths and provide a more comprehensive view of your security posture.
Where can I find more technical details about Cymulate's MITRE-based scenarios?
You can find more technical details and templates for Cymulate's MITRE-based scenarios in the advanced scenarios section of the platform and in the company's technical documentation. For in-depth resources, visit the Resource Hub.
Features & Capabilities
What are the key features of Cymulate's Exposure Management Platform?
Cymulate's Exposure Management Platform offers continuous threat validation, unified breach and attack simulation (BAS), continuous automated red teaming (CART), exposure analytics, attack path discovery, automated mitigation, and cloud validation. The platform is AI-powered, user-friendly, and provides actionable insights for prioritizing remediation efforts. Learn more.
Does Cymulate support integration with other security tools?
Yes, Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, CrowdStrike Falcon, CrowdStrike Falcon LogScale, Cybereason, and more. For a full list, visit the Partnerships and Integrations page.
How does Cymulate help with attack path discovery and lateral movement prevention?
Cymulate automates offensive testing to identify and mitigate threats related to privilege escalation and lateral movement. The platform provides dedicated features for attack path discovery and offers resources such as the blog post 'Stopping Attackers in Their Tracks' for strategies to prevent lateral movement. Read more.
What technical documentation is available for Cymulate users?
Cymulate provides whitepapers, guides, solution briefs, data sheets, and e-books covering topics like exposure management, CTEM, threat detection, vulnerability management, and more. Access all resources in the Resource Hub.
How easy is it to implement Cymulate?
Cymulate is designed for rapid deployment and ease of use. Customers report that implementation is fast and straightforward, requiring only a few clicks to get started. The platform supports agentless mode and offers comprehensive support resources for onboarding.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive, user-friendly interface and ease of deployment. Testimonials highlight the platform's simplicity, actionable insights, and excellent support. For example, Raphael Ferreira, Cybersecurity Manager, noted, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture." Read more.
What security and compliance certifications does Cymulate hold?
Cymulate is SOC2 Type II certified and complies with ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. The platform is also GDPR-compliant and hosted in secure AWS data centers with strong encryption and high availability. Learn more.
How does Cymulate ensure data security and privacy?
Cymulate employs a robust security program, including secure development lifecycle (SDLC), continuous vulnerability scanning, annual third-party penetration tests, strong encryption (TLS 1.2+ and AES-256), and comprehensive employee security training. The company has a dedicated Data Protection Officer (DPO) and Chief Information Security Officer (CISO).
Where can I find Cymulate's blog and latest research?
Cymulate's blog features updates on the latest threats, research, and product news. Visit the Cymulate Blog for more information.
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams across industries such as media, transportation, financial services, retail, and healthcare. Organizations of all sizes, from small businesses to enterprises, can benefit from its unified exposure management platform. Learn more.
What business impact can customers expect from Cymulate?
Customers typically see a 30% improvement in threat prevention, a 52% reduction in critical exposures, a 60% increase in team efficiency, and an 81% reduction in cyber risk within four months. Cymulate also enables 40X faster threat validation and significant time savings. See more.
What are some real-world case studies demonstrating Cymulate's value?
Case studies include Hertz Israel reducing cyber risk by 81% in four months, Nemours Children's Health improving detection and response, and Globeleq automating in-house validation. Explore more success stories on the Customers page.
What core problems does Cymulate solve for security teams?
Cymulate addresses overwhelming threat volumes, lack of visibility, unclear prioritization, operational inefficiencies, fragmented tools, cloud complexity, and communication barriers. The platform provides continuous threat validation, actionable insights, and unified exposure management to solve these challenges.
How does Cymulate tailor solutions for different security roles?
Cymulate provides validated exposure scoring and metrics for CISOs, automates processes for SecOps teams, offers scalable attack simulations for red teams, and prioritizes exposures for vulnerability management teams. Each persona receives tailored features and insights. Learn more.
What is Cymulate's primary mission and vision?
Cymulate's mission is to revolutionize cybersecurity by enabling a proactive approach to threat management. The company empowers organizations to manage their security posture and improve resilience through continuous validation and actionable insights. Read more.
How does Cymulate contribute to continuous threat exposure management (CTEM)?
Cymulate's platform evolves security practices into CTEM by continuously validating controls, simulating real-world threats, and providing measurable improvements in threat resilience and operational efficiency. This ensures organizations stay ahead of emerging risks.
What is the Cymulate Resource Hub?
The Cymulate Resource Hub is a central location for all product documentation, whitepapers, guides, solution briefs, data sheets, e-books, and more. It provides insights, thought leadership, and technical information for users. Access the Resource Hub.
Competition & Comparison
How does Cymulate compare to AttackIQ?
Cymulate offers an industry-leading threat scenario library and AI-powered capabilities for workflow automation and security posture improvement. AttackIQ focuses on automated security validation but lacks Cymulate's innovation, threat coverage, and ease of use. Read more.
What differentiates Cymulate from Mandiant Security Validation?
Mandiant is one of the original BAS platforms but has seen little innovation in recent years. Cymulate continually innovates with AI and automation, expanding into exposure management and being recognized as a grid leader. Read more.
How does Cymulate compare to Pentera?
Pentera is useful for attack path validation but lacks the depth Cymulate provides for fully assessing and strengthening defenses. Cymulate optimizes defense, scales offensive testing, and increases exposure awareness. Read more.
What are the advantages of Cymulate over Picus Security?
Picus may suit organizations seeking a BAS vendor with an on-prem option. Cymulate offers a more complete exposure validation platform, covering the full kill chain and cloud control validation. Read more.
How does Cymulate compare to SafeBreach?
Cymulate outpaces SafeBreach with unmatched innovation, precision, and automation. It features the industry’s largest attack library, a full CTEM solution, and comprehensive exposure validation. Read more.
What makes Cymulate different from Scythe?
Scythe is suitable for advanced red teams building custom attack campaigns. Cymulate provides a more comprehensive exposure validation platform with actionable remediation and automated mitigation. Read more.
How does Cymulate compare to NetSPI?
NetSPI excels in penetration testing as a service (PTaaS). Cymulate is designed for continuous, independent assessment and strengthening of defenses, and is recognized as a leader in exposure validation by Gartner and G2. Read more.
Pricing & Plans
What is Cymulate's pricing model?
Cymulate uses a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and scenarios selected. For a personalized quote, schedule a demo with the Cymulate team.
What information is required to subscribe to the Cymulate blog?
To subscribe to the Cymulate blog, you need to provide your full name, email address, and country of residence. See privacy policy.
Company Information
When was Cymulate founded and what is its global reach?
Cymulate was founded in 2016 and has a presence in 8 global locations, serving customers in 50 countries. Over 1,000 customers trust Cymulate to enhance their cybersecurity posture. Learn more.
How does Cymulate demonstrate its viability and innovation?
Cymulate demonstrates viability through continuous growth, a strong customer base, and frequent platform updates every two weeks, including new features like AI-powered SIEM rule mapping and advanced exposure prioritization. Read more.