Frequently Asked Questions
Mirai Variant Discovery & Technical Details
What new Mirai malware variant did Cymulate discover?
Cymulate's research team discovered a new in-the-wild variant of the notorious Mirai malware. This variant attempts to gain access to systems by guessing user passwords via SSH channels and then installs itself in various directories under the hidden folder “z”. It executes commands such as “cp” and “chmod” to carry out its malicious activities, making it harder to detect and remove.
How does the new Mirai variant attack systems?
The new Mirai variant uses SSH brute force attacks to guess user passwords and gain unauthorized access. Once inside, it installs itself in hidden directories and executes commands to evade detection, such as copying itself and changing file permissions. It also deletes log files and may delete itself at the end of the attack to cover its tracks.
What unique features does the new Mirai variant have?
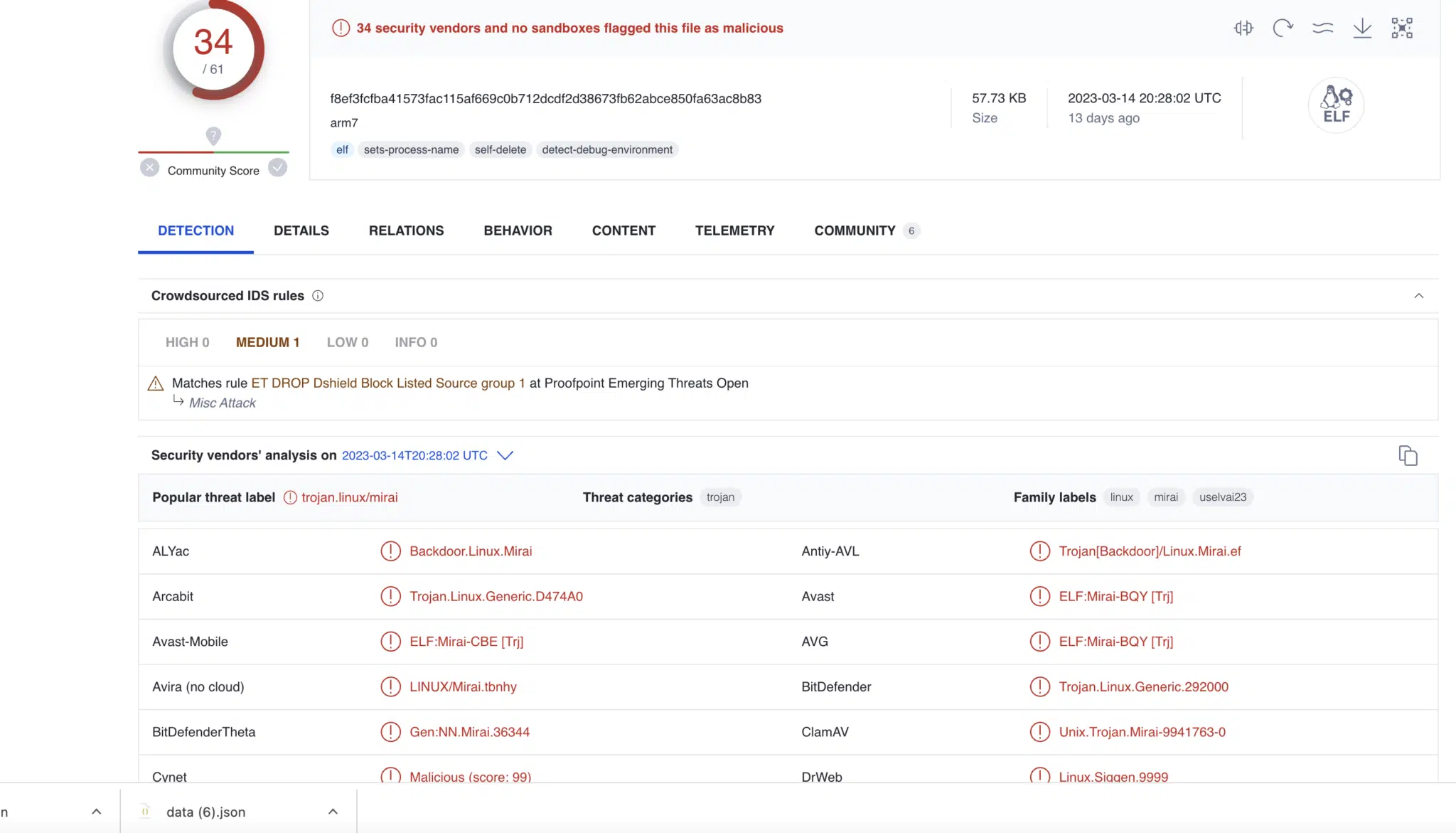
This Mirai variant uses the "uname" system call for DNS lookups and executes the "systemctl" command to control system services. It deletes log files and appears to delete itself after completing its attack, making forensic analysis more difficult. Three unique hashes have been identified for this variant, aiding in detection efforts.
How can organizations detect the new Mirai variant?
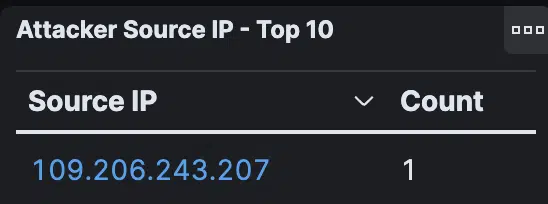
Detection can be aided by using Snort rules created by Proofpoint, which identify malicious activities such as Dshield blocklisted sources and DNS queries for .cc TLDs. Incorporating these rules into your cybersecurity defenses can help identify and prevent attacks from this Mirai variant. Organizations should also ensure their cybersecurity vendors and partners are up-to-date with these indicators of compromise (IoCs).
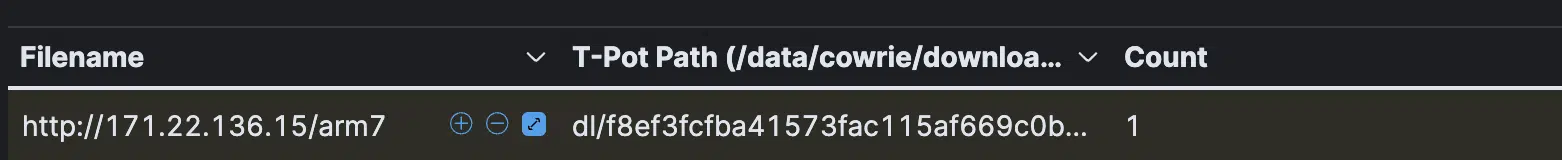
What are the identified hashes for the new Mirai variant?
The new Mirai variant discovered by Cymulate has three unique hashes:
f8ef3fcfba41573fac115af669c0b712dcdf2d38673fb62abce850fa63ac8b83
d5d15893674012d0caf1323f3dcaf5cba00079b33f4805bfa6283b1500612644
04c903b14210f7b38f2ae797755b27e80a37838ebb83976367ac48b258135ed8
What is the impact of the new Mirai variant on cybersecurity?
This variant poses a significant threat due to its ability to evade detection by hiding within legitimate files and directories, using SSH brute force attacks, and deleting evidence of its presence. It highlights the importance of strong passwords and robust system management practices to prevent unauthorized access and persistent threats.
How does Cymulate help organizations test their resilience against Mirai?
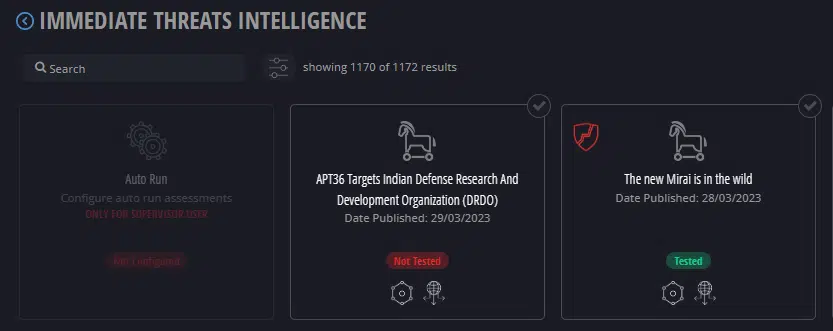
Cymulate's Immediate Threat Intelligence Module includes a ready-to-run test for the new Mirai variant. This allows organizations to validate their defenses against the latest threats and ensure their security controls are effective against real-world attack techniques.
What commands does the new Mirai variant use during its attack?
The malware executes commands such as "cp" (copy), "chmod" (change permissions), "uname" (system call), and "systemctl" (system and service manager). It also deletes log files and may delete itself to evade detection and hinder forensic analysis.
How can organizations stay protected from new Mirai variants?
Organizations should use up-to-date detection rules (such as Snort rules), enforce strong and unique passwords, and regularly validate their defenses with tools like Cymulate's Immediate Threat Intelligence Module. Regularly updating security controls and collaborating with cybersecurity vendors is essential to stay ahead of evolving threats.
Where can I find more technical details about the Mirai variant discovered by Cymulate?
For a deep dive into the technical analysis, attack methods, and detection strategies for the new Mirai variant, read the full blog post at Cymulate's blog.
Product Information & Features
What is Cymulate's Exposure Management Platform?
Cymulate's Exposure Management Platform helps organizations harden their defenses and optimize security controls by proactively validating controls, threats, and response capabilities. It enables organizations to focus on exploitable exposures and strengthen their overall security posture. Learn more.
What are the key features of Cymulate?
Cymulate offers continuous threat validation, a unified platform combining Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics, AI-powered optimization, complete kill chain coverage, attack path discovery, cloud validation, an Immediate Threats Module, and an extensive threat library with daily updates. See all features.
How does Cymulate's Immediate Threat Intelligence Module work?
The Immediate Threat Intelligence Module allows organizations to assess their environments against new attacks as they emerge. It provides ready-to-run tests for threats like the new Mirai variant, ensuring proactive defense and rapid validation of security controls.
What integrations does Cymulate support?
Cymulate integrates with numerous security technologies, including CrowdStrike Falcon, Cisco Secure Endpoint, BlackBerry Cylance PROTECT, AWS GuardDuty, Check Point CloudGuard, Akamai Guardicore, and CrowdStrike Falcon Spotlight. For a complete list, visit Cymulate's integrations page.
How does Cymulate help with exposure validation?
Cymulate automates real-world attack simulations to validate detection, prevention, and IOC coverage. Its Exposure Validation module makes advanced security testing fast and easy, enabling organizations to build custom attack chains and assess their resilience against the latest threats. Learn more.
What technical resources are available for Cymulate users?
Cymulate provides whitepapers, guides, solution briefs, data sheets, and industry reports covering exposure management, CTEM, vulnerability management, detection engineering, and more. Access these resources at Cymulate's Resource Hub.
How does Cymulate support detection engineering?
Cymulate enables organizations to build, tune, and test SIEM, EDR, and XDR rules to improve mean time to detect threats. The platform streamlines detection engineering and automation, helping teams optimize their detection capabilities. Learn more.
What is Cymulate's approach to continuous threat exposure management (CTEM)?
Cymulate's CTEM approach integrates validation into prioritization and mobilization, enabling collaboration across teams and ensuring measurable improvements in threat resilience and operational efficiency. Learn more.
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, Red Teams, and vulnerability management teams across industries such as media, transportation, financial services, and retail. It serves organizations of all sizes, from small teams to enterprises with over 10,000 employees.
What business impact can customers expect from Cymulate?
Customers have reported an 81% reduction in cyber risk within four months, a 60% increase in team efficiency, 40X faster threat validation, a 30% improvement in threat prevention, and a 52% reduction in critical exposures. These outcomes are supported by case studies such as Hertz Israel and others. Read the Hertz Israel case study.
How does Cymulate address the pain points of security teams?
Cymulate addresses overwhelming threats, lack of visibility, unclear prioritization, operational inefficiencies, fragmented tools, cloud complexity, and communication barriers by providing continuous threat validation, actionable insights, automation, and unified exposure management. Learn more.
Are there case studies showing Cymulate's effectiveness?
Yes, Cymulate features case studies across industries, including Hertz Israel (81% reduction in cyber risk), Nemours Children's Health (improved visibility), and a credit union (optimized SecOps). Explore all case studies at Cymulate's customer stories.
How does Cymulate's platform differ for different user roles?
CISOs benefit from quantifiable metrics and exposure scoring, SecOps teams gain operational efficiency and automation, Red Teams leverage automated offensive testing, and vulnerability management teams receive prioritized, validated exposures. Each persona's pain points are addressed with tailored solutions. Learn more.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive, user-friendly platform and actionable insights. For example, Raphael Ferreira, Cybersecurity Manager, said, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture." Read more testimonials.
How quickly can Cymulate be implemented?
Cymulate is known for its quick and straightforward implementation. It operates in agentless mode, requiring no additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment. See implementation stories.
Pricing & Plans
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs. Pricing depends on the package, number of assets, and scenarios selected. For a personalized quote, schedule a demo with Cymulate's team.
Security & Compliance
What security and compliance certifications does Cymulate have?
Cymulate is certified for SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. These certifications demonstrate Cymulate's commitment to security, privacy, and cloud compliance. Learn more.
How does Cymulate ensure data security and privacy?
Cymulate employs strong physical security, encryption for data in transit (TLS 1.2+) and at rest (AES-256), and hosts services in secure AWS data centers. The platform follows a strict Secure Development Lifecycle (SDLC), continuous vulnerability scanning, and annual third-party penetration tests. Read more.
Is Cymulate GDPR compliant?
Yes, Cymulate adopts a holistic approach to GDPR, incorporating data protection by design and maintaining a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO).
Competition & Comparison
How does Cymulate compare to AttackIQ?
AttackIQ provides automated security validation but lacks Cymulate's innovation, threat coverage, and ease of use. Cymulate offers a more comprehensive threat scenario library and advanced AI-powered features. Read more.
How does Cymulate compare to Mandiant Security Validation?
Mandiant is one of the original BAS platforms but has seen less innovation in recent years. Cymulate continually innovates with AI and automation and has expanded into exposure management as a grid leader. Read more.
How does Cymulate compare to Pentera?
Pentera focuses on attack path validation but lacks the depth of Cymulate's full exposure validation platform, which covers the entire kill chain and provides cloud control validation. Read more.
How does Cymulate compare to Picus Security?
Picus is suitable for those seeking a BAS vendor with an on-prem option but lacks Cymulate's comprehensive exposure validation platform, which covers the full kill chain and includes cloud control validation. Read more.
How does Cymulate compare to SafeBreach?
SafeBreach offers breach and attack simulation but lacks Cymulate's innovation, precision, and automation. Cymulate provides a full CTEM solution, comprehensive exposure validation, and advanced automation. Read more.
How does Cymulate compare to Scythe?
Scythe is built for advanced red teams to build custom attack campaigns but lacks Cymulate's ease of use, continuous validation, and actionable remediation guidance. Cymulate offers automated, no-code workflows, daily threat updates, and specific mitigation guidance. Read more.
Company & Resources
When was Cymulate founded and what is its global reach?
Cymulate was founded in 2016 and has a global footprint with offices in eight locations, serving customers in 50 countries. Over 1,000 customers trust Cymulate for their cybersecurity needs. Learn more about Cymulate.
What is Cymulate's mission and vision?
Cymulate's mission is to revolutionize how companies approach cybersecurity by fostering a proactive stance on managing security threats. The vision is to empower organizations to effectively manage their security posture and improve resilience against threats. Read more.
Where can I find Cymulate's blog, news, and events?
Stay updated with Cymulate's latest research, news, and events through the blog, newsroom, and events page.