Data Security Posture Management (DSPM)
Data Security Posture Management (DSPM) is a proactive approach to protecting sensitive data. It helps organizations identify risks, enforce security policies, and maintain compliance.
With data spread across cloud, hybrid, and on-premises environments, cybersecurity is more complex than ever. Traditional tools struggle to track where data is stored, who has access, and how it's protected. DSPM solves this by providing real-time visibility and automated risk management.
Without DSPM, businesses risk data breaches, financial penalties, and reputational damage. As threats evolve and compliance requirements tighten, organizations need DSPM to stay secure and resilient.
The Importance of Having a Solid DSPM
A strong DSPM strategy helps organizations protect sensitive data and avoid security risks. Without it, businesses face data exposure, unauthorized access, and misconfigurations—leading to breaches and compliance failures.
DSPM helps by:
- Identifying where sensitive data is stored and who has access to it.
- Detecting misconfigurations that leave data vulnerable.
- Enforcing security policies to prevent unauthorized access.
Compliance automation is another critical factor. Regulations like the General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA), Health Insurance Portability and Accountability Act (HIPAA), and The PCI Security Standards Council (PCI SSC) require strict data protection measures. DSPM ensures businesses meet these mandates by continuously monitoring and securing sensitive data. This reduces the risk of non-compliance and hefty fines.
The consequences of poor data security posture are severe. Data breaches can lead to financial losses, reputational damage, and legal penalties. Companies may also lose customer trust, which is hard to rebuild.
With cloud data security challenges growing, DSPM is no longer optional—it’s essential. It provides visibility, control, and compliance, helping organizations stay secure in an evolving threat landscape
How DSPM Works
Data security posture management continuously monitors and assesses an organization’s data security. It helps identify risks, enforce security policies, and ensure compliance—all in real time.
DSPM solutions work by analyzing:
- Data repositories – scanning structured and unstructured data to detect sensitive information.
- Cloud environments – identifying misconfigurations, excessive permissions, and security gaps.
- Access controls – monitoring who has access to data and whether it aligns with security policies.
Beyond monitoring, DSPM prioritizes risks based on severity and impact. Instead of overwhelming security teams with endless alerts, it highlights the most critical threats. This allows organizations to focus on fixing the biggest vulnerabilities first.
DSPM also automates remediation, helping businesses quickly resolve security issues. It integrates with existing security tools to enforce policies, revoke risky permissions, and patch misconfigurations.
5 Key Components of DSPM
DSPM consists of several critical components that help organizations protect sensitive data and reduce risk exposure.
1. Data discovery and classification
DSPM continuously scans cloud, on-premises, and hybrid environments to locate sensitive data. It classifies information based on its type (e.g., personal data, financial records, intellectual property) to apply the right security measures.
2. Access management and permissions control
Unauthorized access is a major security risk. DSPM analyzes user permissions to ensure that only the right people can access sensitive data. It detects excessive or outdated permissions and helps enforce least privilege access policies.
3. Risk assessment and prioritization
Not all security risks are equal. DSPM evaluates vulnerabilities and ranks them based on severity, helping security teams focus on the most critical threats first.
4. Continuous monitoring and threat detection
DSPM provides real-time visibility into data security posture. It alerts teams to suspicious activity, misconfigurations, and policy violations, enabling quick response and remediation.
5. Compliance enforcement
Regulatory frameworks like GDPR, CCPA, and HIPAA require strict data protection. DSPM helps organizations meet compliance by continuously monitoring and enforcing security controls.
By integrating these components, DSPM ensures organizations maintain a strong security posture, prevent breaches, and stay compliant in an evolving threat landscape.
DSPM Best Practices
Implementing DSPM effectively requires a proactive approach. Here are key data security posture management best practices to strengthen your data security posture:
- Continuously discover and classify data: You can’t protect what you don’t know exists. Regularly scan and classify data across cloud, on-premises, and hybrid environments. Identify sensitive information like personal data, financial records, and intellectual property.
- Enforce least privilege access: Limit data access to only those who need it. Review user permissions frequently and remove unnecessary privileges. This reduces the risk of unauthorized access and insider threats.
- Monitor and detect threats in real time: Enable continuous security testing and monitoring to detect suspicious activity, unauthorized access, or misconfigurations. Set up automated alerts to quickly respond to security incidents.
- Prioritize and address security risks: Not all threats are equal. Focus on the most critical risks first, such as exposed sensitive data or weak access controls. Use DSPM insights to guide your security response.
- Automate compliance and security controls: Ensure compliance with regulations like GDPR, CCPA, HIPAA, and PCI DSS by automating security policies. Regular audits and real-time enforcement help avoid violations and penalties.
Integrate DSPM with existing security tools: Strengthen your security ecosystem by connecting DSPM with SIEM, IAM, and cloud security solutions. This improves visibility and streamlines security management.
DSPM Use Cases
Data security posture management helps organizations protect sensitive data and strengthen security. Here’s how it applies in real-world scenarios:
Cloud data protection
As businesses store more data in the cloud, security challenges grow. DSPM identifies where sensitive data is stored, who has access, and whether it’s properly protected.
It detects misconfigurations, excessive permissions, and potential risks—helping organizations prevent data leaks.
Insider threat mitigation
Employees, contractors, and third parties can pose security risks. DSPM monitors user access to detect unusual behavior, unauthorized data access, or privilege misuse. It helps organizations enforce least privilege access and reduce insider threats.
Compliance readiness
Regulations like GDPR, CCPA, HIPAA, and PCI DSS require strict data protection. DSPM automates security checks, ensures encryption policies are followed, and provides audit-ready reports.
This simplifies compliance and reduces the risk of fines.
Incident response enhancement
When a security incident occurs, speed matters. DSPM provides real-time insights into data exposure, risk levels, and potential threats. It helps security teams detect, contain, and respond to breaches faster, minimizing damage.
Data Loss Prevention (DLP) support
DSPM enhances traditional Data Loss Prevention (DLP) strategies by identifying at-risk data and preventing accidental exposure. It ensures that sensitive files are not stored in unsecured locations and that data-sharing policies are enforced.
Third-party risk management
Many organizations rely on third-party vendors and partners, increasing security risks. DSPM evaluates external access to sensitive data, ensuring vendors follow security best practices and do not introduce vulnerabilities.
Tools and Platforms for DSPM
Several leading cybersecurity companies offer data security posture management tools to help organizations protect their data. These platforms integrate seamlessly with existing security infrastructures, enhancing overall data protection.
- Palo Alto Networks provides comprehensive DSPM capabilities through its Prisma Cloud platform. It offers agentless, near real-time visibility across multicloud environments, identifying misconfigurations and vulnerabilities to safeguard sensitive data.
- Zscaler's Data Protection Management solution focuses on securing cloud data from leaks. It delivers granular visibility into cloud data, classifies sensitive information, and identifies access permissions and compliance status.
- IBM collaborates with other cybersecurity leaders to enhance DSPM offerings. Through partnerships, IBM aims to reduce cybersecurity complexity by consolidating multiple tools into unified platforms, thereby strengthening security postures and improving operational efficiencies.
How Cymulate Enhances DSPM
Cymulate plays a pivotal role in continuous security validation and exposure management by proactively assessing and enhancing an organization's data security posture. Its platform simulates real-world cyberattacks to identify exploitable weaknesses in data security controls, enabling businesses to address vulnerabilities before malicious actors can exploit them.
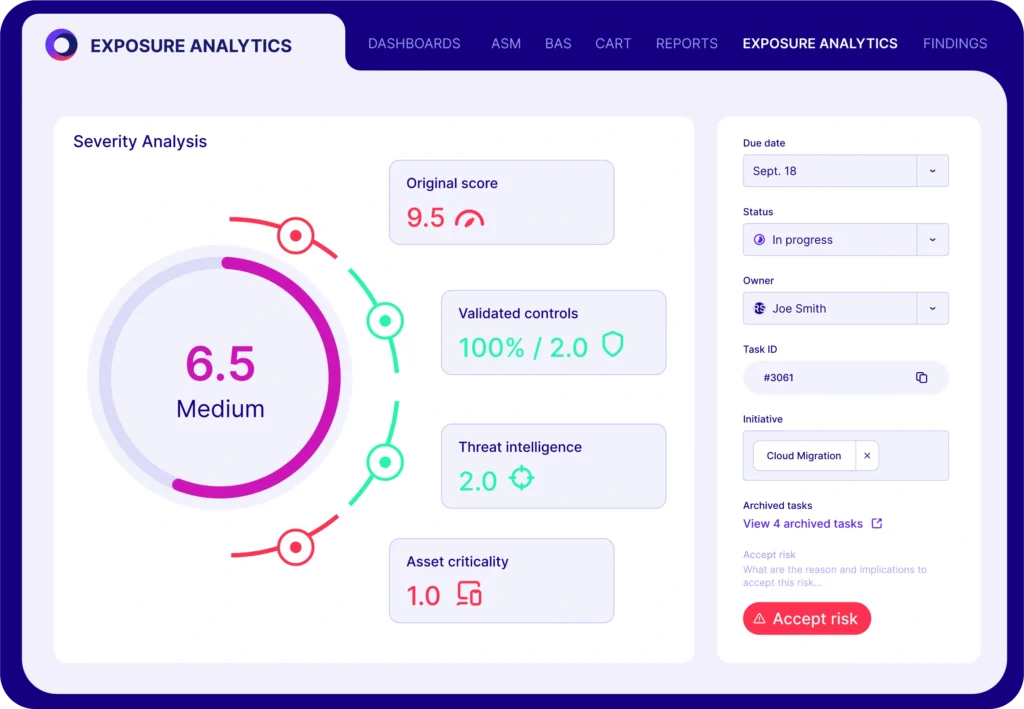
Key features of Cymulate include:
- Real-time risk assessment: The platform offers continuous monitoring, providing up-to-date insights into potential threats and vulnerabilities. This real-time assessment allows organizations to prioritize and remediate risks promptly, maintaining a robust security posture.
- Proactive remediation guidance: Upon identifying vulnerabilities, Cymulate delivers actionable recommendations to mitigate risks effectively. This guidance empowers security teams to implement targeted measures, enhancing overall data protection.
- Actionable insights for improvement: By continuously validating security controls against emerging threats, Cymulate provides organizations with clear, data-driven insights. These insights inform strategic decisions, ensuring that security measures evolve in line with the threat landscape.
Incorporating Cymulate into an organization's security framework enables a proactive approach to data security solutions, ensuring continuous validation and improvement of defenses against evolving cyber threats.