Living Off the Land (LOTL) Attacks
Living Off the Land (LOTL) Attacks Explained: Techniques, Detection & Mitigation
A Living off the Land (LOTL) attack is a stealthy cyberattack technique where adversaries exploit legitimate, native tools and processes already present in a target system or network to carry out malicious actions. Instead of installing custom malware or dropping files, the attacker leverages trusted operating system binaries, scripts and utilities—essentially using the victim’s own environment against itself.
This method is a type of fileless attack, as the malicious behavior runs in memory or via existing software without typical malware files being written to disk. By avoiding new executables, LOTL attacks reduce the likelihood of triggering antivirus signatures or traditional security alerts.
The term "living off the land" comes from the survival concept of using available resources instead of relying on new ones. In cybersecurity, this refers to the use of tools like PowerShell, Windows Management Instrumentation (WMI), command-line utilities and other built-in OS components to achieve an attacker’s goals while blending into normal activity.
Since these tools are regularly used by administrators and users, malicious behavior can hide in plain sight. There's often no obvious malware file for defenders to detect, making LOTL techniques among the stealthiest threats today.
Key characteristics of LOTL attacks include stealth, trust abuse and fileless execution. Attackers typically have some level of system access (e.g., stolen credentials or an initial phishing drop) and then pivot to using on-system tools for further exploitation. This lets them operate discreetly, often camouflaging actions as legitimate behavior.
What Sets LOTL Apart from Other Types of Attack
LOTL attacks are fundamentally different from traditional malware-based intrusions. While typical attacks involve introducing foreign malicious code—such as dropping a virus or injecting exploit-based payloads—LOTL attacks rely solely on existing trusted binaries and scripts, meaning no new code is added to the system.
This gives LOTL a significant stealth advantage over conventional malware. Another defining trait is the use of trusted, signed system binaries, often referred to as LOLBins (e.g., powershell.exe, wmi.exe). In malware attacks, the system treats the code as untrusted. But in LOTL attacks, the attacker abuses trusted tools that are already whitelisted within the system.
Stealth and evasion are core strengths of LOTL. Since no executables are dropped, these attacks often go undetected by signature-based antivirus tools. Traditional defenses look for known malicious files or behaviors, but LOTL provides very few indicators of compromise.
Instead of introducing malware, LOTL threats use native system tools to bypass security, making them difficult to detect or stop. The attacker’s activity often mimics legitimate administrative behavior—for instance, using PowerShell to extract passwords may appear identical to a system admin running routine scripts.
The table below summarizes key differences between a traditional malware attack and an LOTL attack:
| Aspect | Traditional Malware Attack | LOTL Attack |
| Execution Method | Deploys new malicious files or code onto the system and executes them (e.g. installing a virus or backdoor). | Leverages legitimate binaries and scripts already on the system (LOLBins) to execute the attack, often running in memory without writing new files. |
| Stealth | May be caught by antivirus signatures or flagged due to unfamiliar files on disk. Leaves clearer indicators of compromise (new processes, files). | Highly stealthy – malicious actions masquerade as normal OS or admin activity using trusted tools. Little or no malware on disk (fileless), making it hard to distinguish from benign behavior. |
| Tools Required | Requires delivering custom malware or exploit code to the target (external payload is introduced). | Requires no external payload beyond initial access. Attacker “lives off the land” by abusing built-in system tools and admin utilities. |
| Detection | Signature and IOC-based detection is effective if the malware is known. Unusual processes or files can trigger alerts. | Signature-based detection largely fails since no new malicious file is present. Detection relies on behavioral anomalies or patterns of misuse of legit tools. |
| Attacker Dwell Time | Often shorter if malware is caught by security scans or triggers obvious alerts. Incidents are typically contained faster once identified. | Tends to be much longer – adversaries can dwell for weeks or even months undetected. The longer they stay hidden, the more time they have to escalate privileges, steal data, or cause damage. |
As shown above, an LOTL attack’s reliance on trusted system components makes it a fundamentally different and more elusive threat than a standard malware infection. LOTL attackers take advantage of the assumptions and gaps in traditional security tools.
Most antivirus or endpoint solutions “focus on identifying external threats...or unauthorized executables,” whereas LOTL “bypass these defenses effortlessly” by not introducing anything obviously malicious.
Types of LOTL Attacks
LOTL is a broad tactic that spans multiple stages of an attacker’s kill chain. Below are common LOTL-based activities, each using native system tools or functions to avoid detection:
Credential dumping
Attackers may extract passwords and credentials without using external malware. A common method involves using Mimikatz (in-memory) or dumping memory from LSASS, which stores user credentials.
This approach helps obtain admin hashes and passwords while evading antivirus. For instance, during the NotPetya attack in 2017, attackers used stolen credentials (via Mimikatz) to spread across systems—demonstrating LOTL tactics in credential theft.
Lateral movement
LOTL techniques enable attackers to move across systems (pivoting) without deploying new malware. They often abuse tools like PsExec and WMI, which are typically used for legitimate remote administration.
These tools help execute commands remotely without raising alarms. A notable example is the 2015 Ukraine power grid attack, where PsExec and WinRM were used to move laterally and trigger a blackout—blending into legitimate processes while avoiding traditional detection.
System discovery
Before launching further actions, adversaries perform reconnaissance using built-in commands. Tools like systeminfo, whoami, ipconfig, tasklist, and net commands help gather insights into the environment.
These are all typical admin commands, but attackers use them to identify users, security tools, and potential pivot points—all without raising red flags due to their legitimate appearance.
Data exfiltration & abuse of native tools
LOTL methods also allow data exfiltration or downloading second-stage payloads using trusted tools. For example, Certutil can be misused to encode files, fetch remote data, or send stolen information disguised as regular traffic. Other tools like PowerShell, BITSAdmin, and scheduled tasks can quietly transfer data to attacker-controlled servers.
In one method, attackers compress and convert data to Base64 using Certutil, then exfiltrate it via DNS or HTTP requests—avoiding detection by blending into normal network activity. Since these tools are pre-approved in many systems, such exfiltration often bypasses Data Loss Prevention (DLP) tools.
These examples show how LOTL techniques span the full attack lifecycle—from credential harvesting and privilege escalation, to reconnaissance, lateral movement and data theft. Today, LOTL is used extensively in both state-sponsored espionage and ransomware campaigns.
Notably, in 2022, data showed that around 62% of attackers leveraged LOTL tools or techniques—highlighting its widespread use for stealth and operational success.
From Entry to Exploitation: The LOTL Kill Chain in Action
An LOTL attack unfolds in stages along the attacker’s kill chain, leveraging legitimate tools at each step. Below is an overview of how such an attack typically progresses:
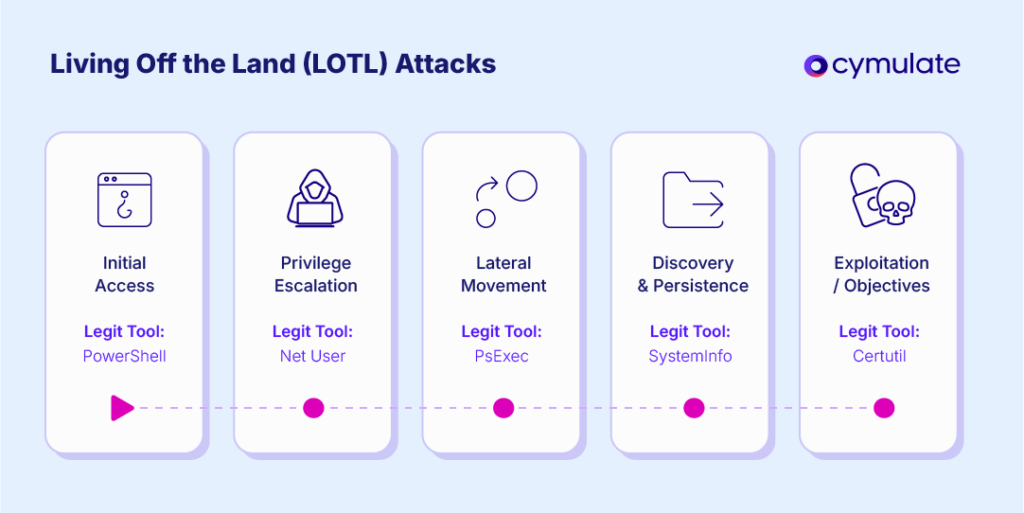
1. Initial access
The attacker first enters the target environment, often via phishing, exploiting vulnerabilities or using stolen credentials.
The initial access may involve a small script or malware, but LOTL tactics soon take over. For instance, after gaining a foothold, the attacker may spawn a PowerShell session or inject code into memory, establishing code execution on one machine using trusted tools.
2. Privilege escalation
Next, the attacker seeks to escalate privileges—gaining local admin or domain-level access. LOTL techniques help by dumping credentials from memory or abusing Windows binaries like schtasks.exe or fodhelper.exe for UAC bypass.
Actions like creating admin users or deleting backups can all be done with built-in tools like net user or vssadmin.exe, avoiding custom malware entirely.
3. Lateral movement
With elevated privileges, attackers expand across the network using tools like WMI, WinRM, or scheduled tasks.
These methods allow execution of code on remote systems using their own native tools—such as powershell.exe. For persistence or coordination, they may create hidden scheduled tasks on each target system, all using standard Windows features.
4. Discovery and persistence
Attackers continually perform environment reconnaissance with tools like tasklist, dir, net view, nltest and dsquery. For persistence, they avoid backdoor files and instead rely on mechanisms like registry run keys, WMI Event Subscriptions or even enabling RDP or creating a service via sc.exe. These techniques allow them to stay hidden and maintain access using only OS-level functionality.
5. Exploitation of objectives
Finally, the attacker executes their goal—whether data exfiltration, sabotage, or ransomware deployment—still using LOTL methods. For theft, they may transmit data with tools like Certutil or PowerShell’s Invoke-WebRequest.
For sabotage or ransomware, they may disable recovery using vssadmin.exe or wbadmin, often avoiding detection and sometimes even executing ransomware through scripts without ever dropping a file.
Tools Used in LOTL Attacks
LOTL attackers frequently exploit built-in tools, known as LOLBins (Living Off the Land Binaries), which are legitimate system utilities capable of powerful actions. Here are some of the most abused ones:
- PowerShell: A widely used command-line and scripting tool in Windows. Attackers abuse it to execute payloads in memory, download files and run encoded scripts (e.g., -EncodedCommand) — all using the trusted powershell.exe. It’s popular for its flexibility, stealth and system-level access.
- Windows Management Instrumentation (WMI): WMI allows local or remote code execution via wmic.exe. It’s often used to spawn processes on remote machines or gather system data. Since it’s frequently used by IT admins, malicious use often goes unnoticed.
- PsExec: A remote administration tool from Microsoft’s Sysinternals suite. Attackers use it to execute code on remote systems, often by copying a service executable. Because it’s common in enterprise environments, its use doesn’t typically trigger alarms.
- Rundll32: Used to run code from DLLs, rundll32.exe can also execute malicious scripts by acting as a proxy for code execution. It helps attackers disguise payloads as legitimate processes and is often used in macro-based attacks.
- CertUtil: A certificate management tool that can also download files and encode/decode data. Attackers use it to exfiltrate data or fetch malware, disguising these actions as routine certificate operations.
- MSHTA: Executes HTML applications (.hta) via mshta.exe. It allows attackers to run malicious scripts pulled from the web or attached to phishing emails, under the cover of a trusted binary.
- Scheduled Tasks (Schtasks.exe / Task Scheduler): Attackers create scheduled tasks to maintain persistence or execute scripts at intervals. It’s a native Windows feature often used in admin tasks, making it a stealthy method for continued access.
- Other Common LOLBins
Additional tools include:
- regsvr32.exe – executes DLLs and scripts
- bitsadmin.exe – transfers files in the background
- wscript/cscript – runs VBScript or JScript
- netsh, msconfig, excel.exe – misused for stealthy execution
On Linux/macOS: bash, curl, ssh, and osascript are common targets.
Detection of LOTL Attacks
Detecting LOTL attacks is difficult because they blend in with legitimate system activity.
Traditional security tools, focused on malware signatures or file-based indicators, often miss these attacks. However, with the right strategies, defenders can catch them. The main challenges with detecting lol attacks include:
- LOTL tactics don’t introduce new files or code, avoiding typical malware detection.
- Few indicators of compromise (IOCs): no strange hashes, ports or errors.
- Legitimate use of tools like PowerShell or PsExec generates logs similar to malicious usage.
- Many organizations lack behavioral baselines, making it hard to spot anomalies.
- Attackers may disable logging, clear event logs (e.g., via wevtutil.exe) or use older tools without audit features.
- Tools like CertUtil and PsExec produce minimal logs, aiding stealth.
LOTL Detection Strategies
Behavioral monitoring and anomaly detection
Focus on user behavior over known threats. If PowerShell is launched by a user who doesn’t typically use it—or if commands are obfuscated—that’s suspicious. Use UEBA tools to baseline normal behavior and flag deviations.
Detailed logging and telemetry
Enable:
- PowerShell Script Block Logging (event ID 4104)
- Command-line auditing (via Sysmon or Windows Audit Policy)
- Verbose logging for tools like WMI and Scheduled Tasks
Use a centralized SIEM to manage and secure logs (preferably write-once, read-many).
Suspicious event combinations
Look for dangerous process chains, like:
- winword.exe spawning cmd.exe or powershell.exe
- explorer.exe launching mshta.exe
- powershell.exe spawning rundll32.exe
These often signal malicious script execution or macro-based attacks. Customize your EDR rules to alert on such patterns.
Monitoring known LOLBins
Keep watchlists for usage of tools like certutil.exe, bitsadmin.exe, mshta.exe, wmic.exe, psexec.exe.
If not used regularly in your environment, any execution could warrant investigation. Consider restricting usage or limiting to specific systems and time windows.
Correlation and multi-level detection
Correlate across:
- Process level (e.g., unexpected use of schtasks.exe)
- Memory level (e.g., code injection or fileless payloads)
- Network level (e.g., odd command-and-control behavior)
XDR platforms help by connecting these signals. For example: a system downloads a file via PowerShell, then initiates RDP, then runs vssadmin.exe to delete backups—individually low-risk, together a clear threat pattern.
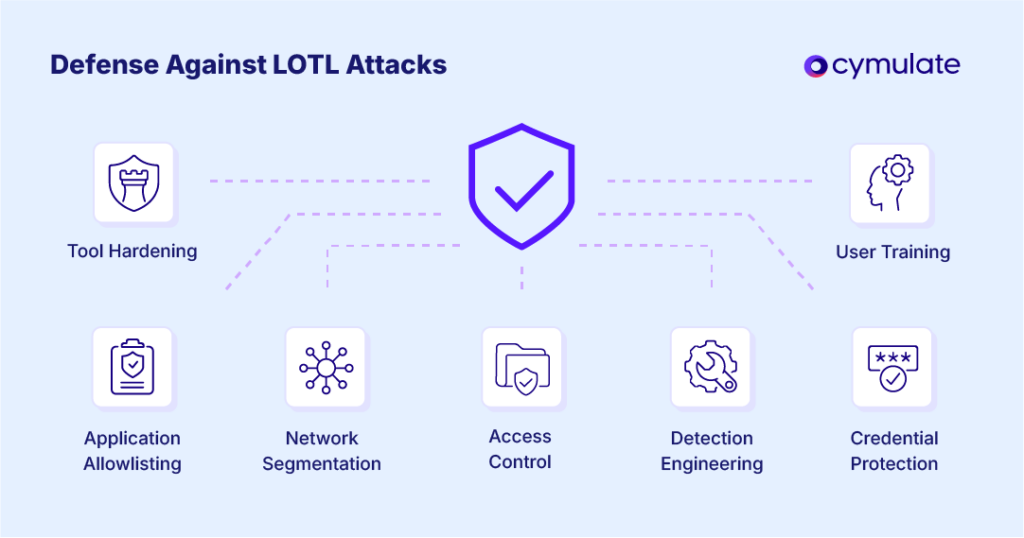
Mitigation of LOTL Attacks
Preventing LOTL attacks is difficult because they rely on legitimate system tools. However, a layered defense strategy—focused on least privilege, tool restriction and detection readiness—can greatly reduce their impact.
1. Apply least privilege and access control
Limit what users and processes can do. Many LOTL attacks succeed because compromised accounts have excessive privileges.
- Enforce User Account Control (UAC)
- Use MFA for remote access
- Prevent domain admins from logging into user machines
- Implement network segmentation to contain lateral movement
Even if attackers “live off the land,” these limits restrict their movement.
2. Application allowlisting (Safelisting)
Use tools like AppLocker or WDAC to control what binaries and scripts can run.
- Allow PowerShell only in Constrained Language Mode
- Block unused tools like mshta.exe, psexec.exe, or certutil.exe
- On Linux, apply SELinux or AppArmor profiles
These controls shrink the attack surface and prevent misuse of common LOLBins.
3. Disable or harden unused features
Turn off services you don’t need.
- Disable WMI, PowerShell, RDP or Remote Registry where not required
- Apply Constrained Language Mode, AMSI or restrict wscript/cscript
- Harden the tools you must use
The less "land" attackers can live off, the more visible their actions become.
4. Segmentation and network controls
Use firewalls and ACLs to block unnecessary access between systems.
- Limit communication to domain controllers
- Require jump-hosts for sensitive access
- Monitor and restrict lateral movement paths
Proper segmentation can contain attacks and prevent broad system access.
5. Protect and monitor credentials
LOTL attackers often use stolen credentials.
- Enforce strong passwords and credential rotation
- Use Credential Guard to protect secrets in memory
- Monitor for abnormal login behavior
Reducing credential exposure greatly limits attacker options.
6. Security tool hardening
Ensure attackers can’t tamper with defenses.
- Enable tamper protection in antivirus/EDR tools
- Secure logs so that log clearing triggers alerts
- Prevent tools like sc.exe from disabling services unnoticed
If attackers can’t hide, they’re more likely to be caught.
7. User training and IT process separation
Train users—especially IT staff—on LOTL threats.
- Encourage separate accounts for admin vs. regular tasks
- Use hardened admin workstations for privileged actions
- Promote awareness of unexpected scheduled tasks or tool misuse
Informed users help identify abnormal system behavior early.
8. Regular patching
Patch systems to reduce initial access and privilege escalation vectors.
- Some LOLBins are mitigated through updates
- Fix known exploits that could be used before LOTL techniques kick in
Even though LOTL abuses legit tools, patching closes many doors.
9. Validate and tune detection controls
Regularly test SIEM rules, EDR policies and AppLocker configurations.
- Simulate LOTL scenarios to ensure alerts trigger
- Fine-tune rules to avoid false positives
- Continuously improve through detection engineering
Detection is only effective if it’s accurate and actively maintained.
Recovery Time and Response Considerations
One of the most dangerous aspects of LOTL attacks is the extended dwell time attackers often enjoy. Since these intrusions are hard to detect, adversaries can remain inside a network for weeks or even months, during which they may steal sensitive data, establish persistence mechanisms or prepare for large-scale actions like ransomware deployment.
The longer an attacker stays hidden, the harder and longer the recovery becomes. Unlike cleaning up a single malware infection, recovering from a LOTL breach involves identifying all compromised systems, accounts and backdoors.
This might include hidden admin users, scheduled tasks or PowerShell scripts running in memory. In some cases, organizations have had to rebuild entire networks due to the depth of silent compromise. Because LOTL techniques often leave behind minimal logs, responders may need to rely on memory forensics and advanced threat hunting to fully understand the breach.
Once a suspicious LOTL activity is detected—like unusual PsExec usage—it’s critical to validate and respond quickly. Because attackers use legitimate tools, distinguishing between a malicious action and normal admin behavior requires careful context analysis.
Having incident response playbooks helps accelerate decisions, outlining steps such as isolating hosts, collecting forensic data, terminating processes and resetting credentials. Speed is essential—delays give attackers more time to escalate or move laterally.
In many LOTL cases, a coordinated response is required, especially when the attacker may have multiple footholds. Isolating systems, disabling compromised accounts and even temporarily taking segments of the network offline might be necessary. When ransomware actors are involved, timing becomes even more critical—delayed containment could allow them to deploy across the network.
How Cymulate Helps Mitigate LOTL Attacks
Cymulate helps organizations proactively defend against stealthy LOTL attacks by simulating real-world tactics using legitimate tools. As a platform that provides Breach-and-Attack Simulation (BAS) and Continuous Automated Red Teaming (CART), security teams can test their readiness, improve detection and fine-tune response capabilities—all in a controlled, risk-free environment.
- Simulating LOTL techniques safely: simulate LOTL tactics like PowerShell misuse, credential dumping and lateral movement through WMI or PsExec. These tests mimic real attacker behavior without causing damage, enabling teams to observe how their systems and analysts respond. This proactive approach helps identify blind spots before a real threat takes advantage of them.
- Testing and tuning detection rules: validate whether SIEM, EDR and detection rules are working effectively. Simulated attacks help teams see if alerts are triggered as expected. If not, they know where to adjust log sources or refine rules. This ensures that LOTL activity—often subtle and fileless—doesn’t go unnoticed.
- Improving response time and deducing false positives: By regularly running LOTL simulations, Cymulate familiarizes analysts with what malicious behavior looks like. This speeds up detection and response while helping teams fine-tune alerts to reduce noise. The result is a more confident, efficient SOC that can distinguish between true threats and normal admin activity.
- Supporting purple teaming and training: enables red and blue teams to test LOTL scenarios together, iterate quickly, and improve defenses. The simulations are also useful for training analysts, running response drills, and educating stakeholders on how LOTL attacks progress and are contained.
- Full Kill-Chain coverage and continuous validation: simulate full attack chains, from initial access to data exfiltration. This helps organizations assess their readiness across every phase of a LOTL-based attack. Over time, repeated simulations help track improvements and benchmark detection maturity.
- Immediate insight into security gaps: Each simulation provides detailed feedback on what was detected and what wasn’t. This helps teams focus remediation efforts precisely where they’re needed—whether tuning alerts, adjusting configurations, or reinforcing overlooked defenses. It also supports internal reporting and readiness assessments.
- Integration with security controls: Cymulate integrates with existing security tools to streamline improvements. It can suggest detection rules and push them directly to SIEMs, helping organizations evolve their defenses continuously rather than relying on static configurations.
A Proactive Partner in LOTL Defense
Cymulate acts as an ongoing testing and validation partner, helping organizations uncover weaknesses in their LOTL detection before real attackers can exploit them. By continuously simulating stealthy threats and refining defenses, Cymulate ensures teams are ready to act decisively when it matters most.