Understanding Zero-Day Vulnerabilities & Attacks in Cybersecurity
Zero-day vulnerabilities and attacks represent one of the most significant cyber threats to corporations and private individuals. They exploit previously unknown software or hardware vulnerabilities, exposing systems to harmful activities.
Attacker groups tend to seek out these types of vulnerabilities due to the lack of available solutions to fix them and the increased probability of success. Until there is an available fix, attackers can continue their exploit and profit from the vulnerability.
In this guide, you will learn to distinguish among the core pillars of zero-day threats, identify the different types of vulnerabilities and explore the best practices and proactive strategies required to protect your organization from unknown exploits.
Key takeaways:
- Zero-day vulnerabilities and attacks are cybersecurity threats that exploit previously unknown software or hardware flaws.
- Defending against zero-day security threats requires proactive strategies, such as behavioral analysis and rigorous patch management.
- The Cymulate Exposure Management platform identifies which vulnerabilities are actually exploitable in a specific environment to prioritize the risks that matter most.
What is zero-day in cybersecurity?
Zero-day in cybersecurity refers to a security flaw in software or hardware that is unknown to the party responsible for fixing it. This security designation comes from the fact that the developer has had "zero days" to create a patch or fix for the issue because they have only just discovered it, often only after an attacker has already begun using it.
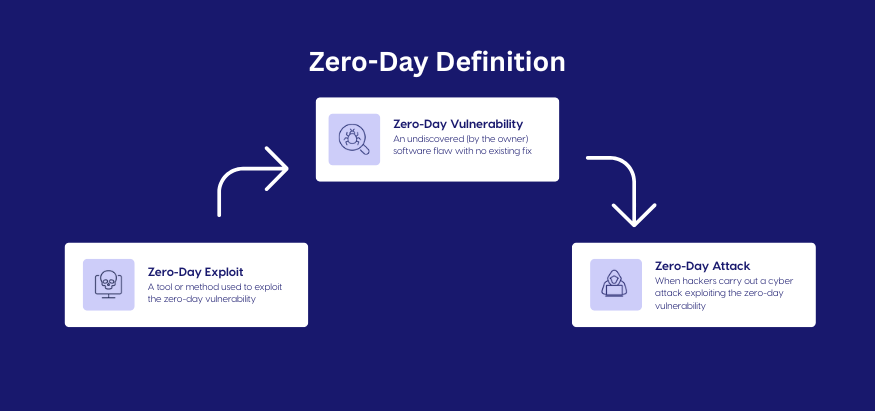
While zero-day terms are often used interchangeably, we must differentiate between these three pillars:
- Zero-day vulnerability: A physical or digital flaw in a system.
- Zero-day exploit: The specific code or method used by an attacker to take advantage of a system flaw.
Zero-day attack: The actual event where the exploit is used to cause a data breach or system failure.
What are zero-day vulnerabilities?
Zero-day vulnerabilities are unintentional security flaws in software, hardware, or firmware that are unknown to the parties responsible for patching or fixing them (such as the developer or vendor). Because the vulnerability is undiscovered, it remains open, meaning there are no available patches, updates, or security signatures to defend against it.
Types of zero-day vulnerabilities
Zero-day vulnerabilities typically fall into two primary categories:
- Software flaws are weaknesses in a program's code, ranging from simple bugs to complex design errors. They can make the whole system susceptible to cyberattacks.
- Hardware vulnerabilities refer to weaknesses in physical devices, such as drivers, monitors, or the computer's motherboard. These vulnerabilities are a severe concern in cybersecurity as they can be challenging to detect and mitigate, especially if employees are using their own personal hardware for work.
What is a zero-day exploit?
A zero-day exploit is a technical means, such as a specialized script, a piece of malware, or a sequence of commands, engineered to exploit a specific zero-day vulnerability. The exploit acts as the functional bridge between an undiscovered flaw in a system’s architecture and a successful security breach.
Unlike generalized malware, cybersecurity zero-day exploits are precisely designed to target the unique properties of a newly discovered weakness. Because these exploits target vulnerabilities that lack a public record or patch, they are highly effective at bypassing standard security protocols.
What are zero-day attacks?
Zero-day attacks are the actual execution of an exploit against a previously unknown vulnerability. This security attack follows a precise technical timeline, progressing from the initial introduction of a flaw in the codebase through its discovery and exploitation by threat actors, and finally ending with the release of a vendor security patch.

How to combat zero-day attack vulnerabilities
Combating zero-day attack vulnerabilities is challenging, but these 11 best practices can help mitigate the risk and impact of these attacks:
- Behavioral analysis and anomaly detection: Implement security solutions that use machine learning and artificial intelligence to identify unusual patterns and behaviors that may indicate a zero-day attack.
- Endpoint protection: Deploy advanced endpoint protection platforms (EPP) and endpoint detection and response (EDR) tools that can detect and respond to suspicious activities on individual devices.
- Regular software updates and patch management: Although zero-day vulnerabilities are unknown, ensuring that all software is up to date with the latest patches can help protect against known vulnerabilities and reduce the attack surface.
- Network segmentation: Divide the network into smaller, isolated segments to limit the spread of an attack and contain potential damage.
- Intrusion detection and prevention systems (IDPS): Use IDPS to monitor network traffic and system activities for signs of malicious behavior and to block potential attacks.
- Threat intelligence: Subscribe to threat intelligence feeds and participate in information-sharing communities to stay informed about emerging threats and potential zero-day vulnerabilities.
- Application whitelisting: Implement whitelisting to ensure that only approved and known-safe applications can run on your systems, reducing the risk of malicious software execution.
- Regular security assessments and penetration testing: Conduct regular security assessments, vulnerability scans and penetration tests to identify and address potential weaknesses in your systems.
- Employee training and awareness: Educate employees about cybersecurity best practices, including recognizing phishing attempts and other common attack vectors used to exploit zero-day vulnerabilities.
- Incident response plan: Develop and maintain a robust incident response plan to quickly and effectively address security incidents and minimize the impact of an attack.
- Use of sandboxing: Implement sandboxing techniques to run potentially suspicious code in an isolated environment that can be analyzed without posing a risk to the central system.
By employing security approaches and staying proactive, organizations can improve their resilience against zero-day attacks and minimize the potential damage they will likely cause.
Detection techniques for zero-day threats
While the nature of zero-day threats makes them more challenging to discover, strategies can be implemented to detect these vulnerabilities before attackers do. Two primary methods used for this purpose are anomaly-based detection and signature-based detection:
Anomaly-based detection
An anomaly-based detection is a proactive approach in cybersecurity that focuses on identifying patterns of behavior or events that deviate from the norm. By establishing a baseline of typical activity, security systems can flag unusual occurrences that may indicate a zero-day threat.
This method effectively detects previously unseen attacks by analyzing real-time network traffic and user behavior for irregularities, enhancing the ability to respond swiftly to emerging cyber threats.
Signature-based detection
Signature-based detection involves identifying malicious activity by comparing it to preexisting patterns or signatures of known threats. By analyzing known malware signatures, security systems can detect and block similar attacks in real-time.
This method is effective in spotting familiar threats but can be bypassed by zero-day exploit attacks that have not been previously identified. Security teams often combine signature-based detection with other techniques to enhance their cybersecurity posture and stay ahead of evolving threats.
Strategic defense against zero-day threats
Defending against zero-day attack exploits requires a comprehensive and proactive approach. One key defensive strategy is to identify and address vulnerabilities in Internet of Things (IoT) devices. Flaws in IoT devices can provide a gateway for attackers to exploit zero-day vulnerabilities and gain unauthorized access to networks. Key strategies include:
Deploying WAF
A Web Application Firewall (WAF) can detect and block malicious inputs that target security vulnerabilities, providing an additional layer of defense against zero-day attack exploits.
By prioritizing vulnerability management, conducting regular security assessments and staying informed about the latest threats and mitigation techniques, organizations can enhance their defenses against zero-day threats and minimize the potential impact of these attacks.
Applying patch management
Software vendors regularly release patches and updates to address known vulnerabilities and protect against emerging threats.
Organizations must prioritize patch management and ensure that all systems and applications are promptly updated with the latest security patches. This includes maintaining a comprehensive inventory of software and hardware assets, monitoring new vulnerabilities and implementing a patch management process for testing, deployment and verification.
Failure to apply patches promptly can leave systems susceptible to cyberattacks. Attackers can exploit zero-day vulnerabilities to gain unauthorized access, compromise data and disrupt business operations. Organizations can significantly reduce their risk of falling victim to zero-day attacks by prioritizing patch management and maintaining a proactive and diligent approach.
Implementing proactive defense measures
Organizations can adopt various security strategies to mitigate the risks associated with zero-day attacks:
- Deploying Distributed Denial of Service (DDoS) mitigation: These solutions detect and block DDoS attacks, which threat actors frequently use as a tactical smokescreen to mask concurrent zero-day exploitation.
- Hardening Linux-based systems: Given that many zero-day vulnerabilities target these environments, organizations should prioritize consistent patching, stringent access controls and continuous activity monitoring.
- Enforcing HTTPS encryption: Utilizing robust encryption protocols secures data in transit and prevents unauthorized actors from intercepting sensitive information during a potential breach.
Streamline zero-day vulnerability protection with Cymulate
The discovery of zero-day vulnerability exploits triggers a race against time. While legacy tools leave you exposed while waiting for a vendor patch, the Cymulate Exposure Management platform closes this critical window of vulnerability by replacing reactive waiting with proactive validation.
By shifting the focus from the flaw itself to your actual security posture, our platform empowers you to neutralize attacks through every stage of the threat lifecycle:
- Within 24 hours of a discovery, Cymulate provides a production-safe simulation of the exploit. You can test your defenses against the attack's behavior before a patch is even available
- Since zero-day bypass signatures are included, Cymulate tests your behavioral detections (EDR, SIEM, WAF) and identifies exactly which layer of your security stack is blind to the new threat
- If a security gap is found, our platform provides actionable mitigation guidance. You can generate vendor-specific Sigma rules or push automated updates directly to your security controls, acting as a virtual patch
- Instead of drowning in a list of CVEs, Cymulate shows you which vulnerabilities are actually exploitable in your specific environment, allowing you to prioritize the risks that truly matter
Ready to see how your defenses hold up? Book a demo to see the Cymulate Exposure Management platform in action.


