Cymulate vs NetSPI
Recognize the value of a proven SaaS platform vs. a pen testing company that wants to sell you their tools.
Cymulate Named
a G2 Leader
Cymulate Recognized as Leader for Security and Exposure Validation
Cymulate Named a
Customer’s Choice
2024 Gartner® Peer Insights™ Voice of the Customer for BAS Tools Report
For Exposure Validation, Stick to the Market Leader
NetSPI is an excellent choice if you are looking for a penetration testing as a service (PTaaS) vendor. But if you want to independently assess and strengthen your organization’s defenses, NetSPI’s approach to automated exposure validation will limit you.
Cymulate is recognized by both Gartner and G2 as a leader in exposure validation, with a track record of continuous innovation. With Cymulate, our customers independently optimize their cyber defenses while proving the state of cyber resilience by validating controls, threats and response so they can focus on the exploitable.
Cymulate vs NetSPI Comparison Chart
Use Case | Capabilities | NetSPI |
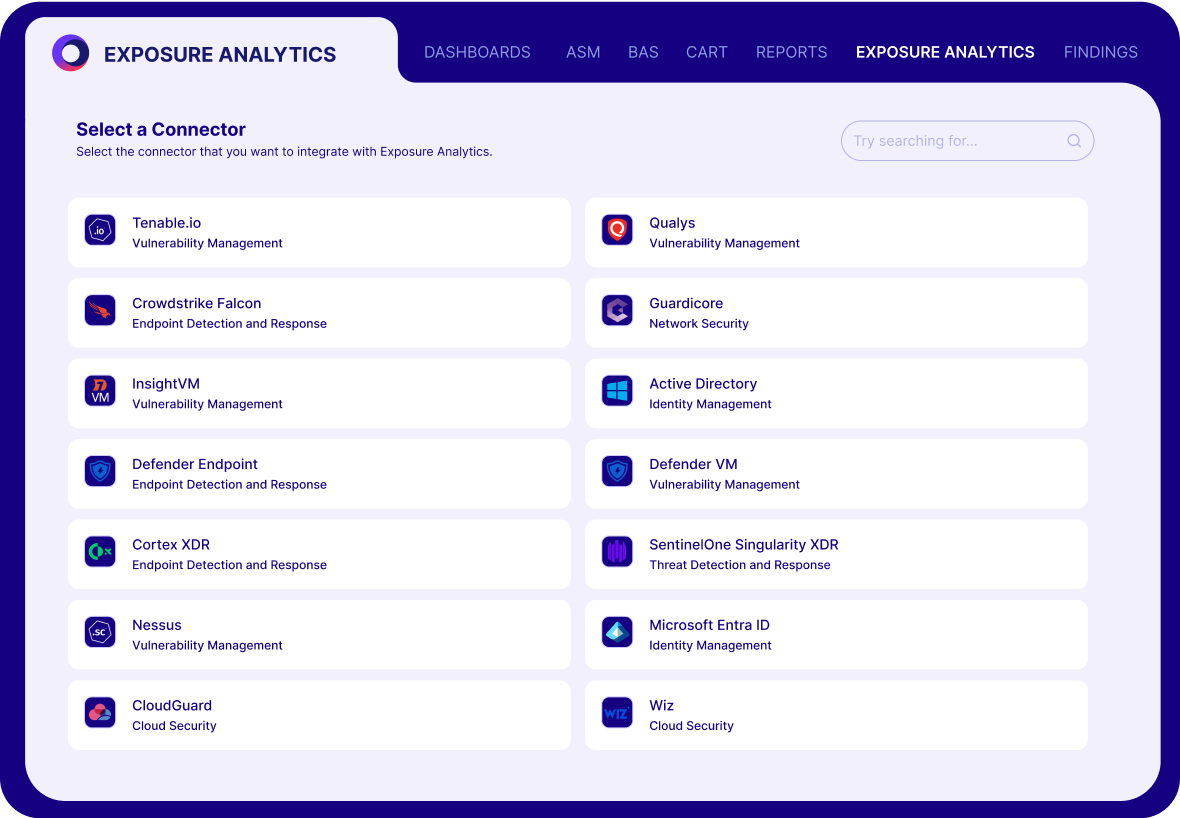
Defensive Posture Optimization | Security controls integrations | Endless control integrations to validate detection and prevention. | Limited and unpublished control integrations. | ||
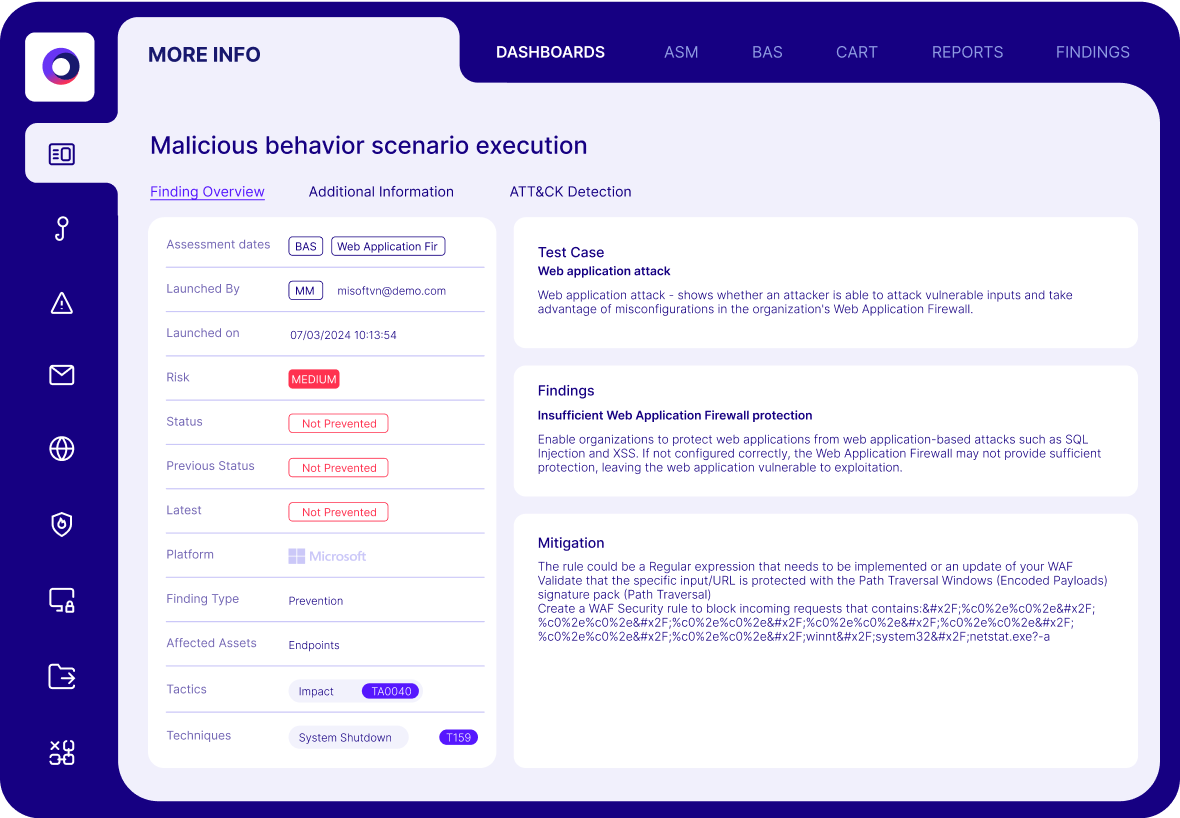
Threat-informed defenses | Automates IoC updates and provides custom detection rules and policy tuning to fine-tune security configurations. | Limited control tuning guidance. | |||
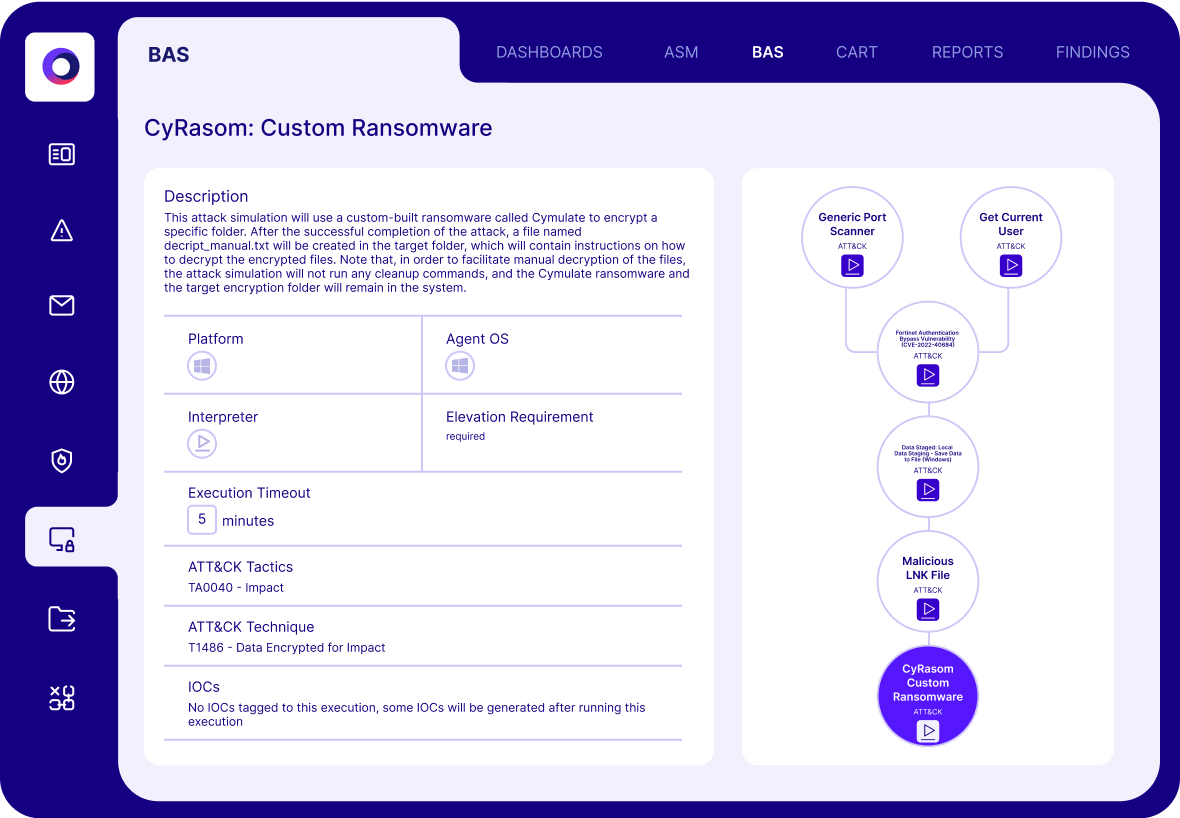
Scale Offensive Testing | Attack Scenario creation workbench | Provides both out-of-the-box assessments and AI-assisted custom attack scenarios. Visualizes each step of an assessment to improve remediation efforts. | No custom attack scenarios. | ||
Automation, extensible testing | Automates security validation using real-world attack scenarios, including cloud controls. | No testing of cloud controls. Delivered as part of service-led engagements. | |||
Attack paths | Tests lateral movement and validates security across the full kill-chain. | No testing for lateral movement or complex attacks across an environment. | |||
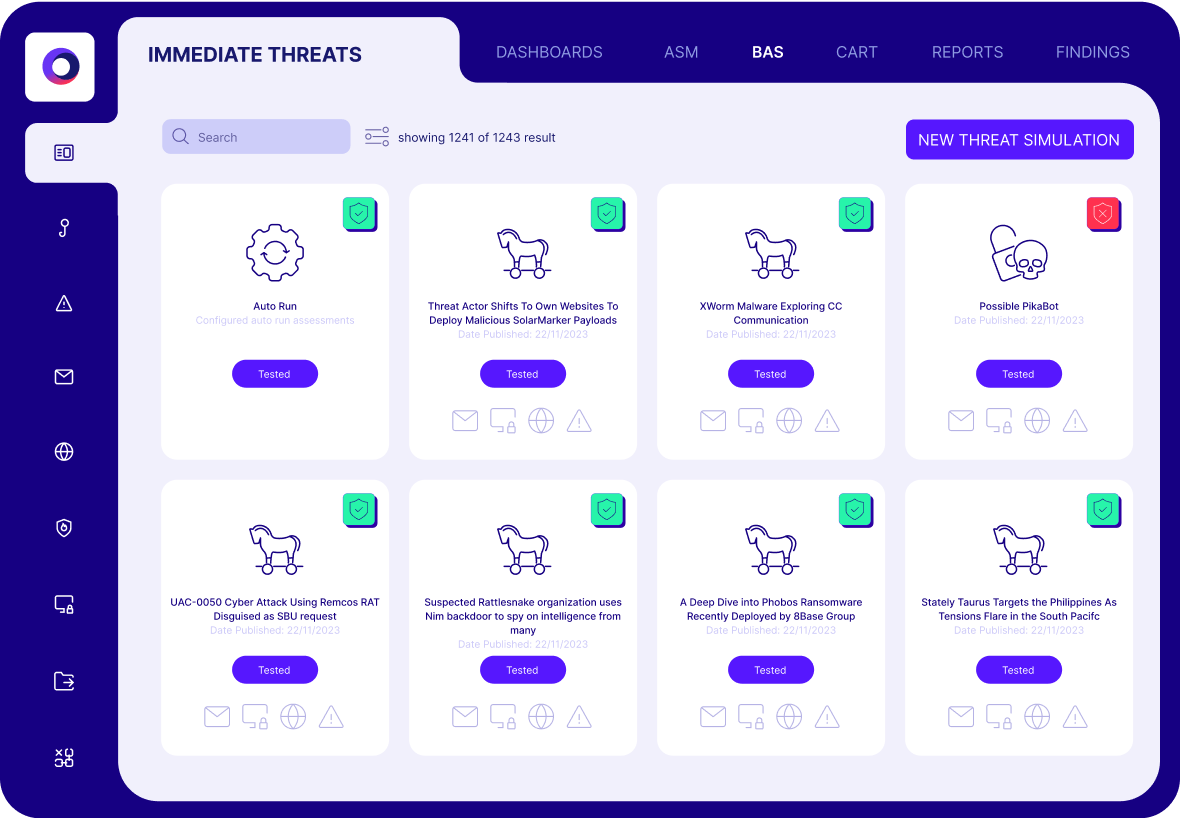
Exposure Awareness | Automated & continuous testing | Easy and automated testing for continuous validation of threats, security controls, threats and response capabilities. | Basic breach and attack simulation for controls testing. | ||
Always current attack scenario knowledge | Daily updates of the latest threats and continuously adding new assessments. | No daily update for the latest threats. Infrequent updates of attack techniques. |
Exposure validation that filters out the noise, so you can focus on the exploitable.
Validate Controls
Find and fix your gaps
Validate Threats
Know your risk
Validate Response
Battle test your SOC
Why Companies Choose Cymulate Over NetSPI
What our customers say about us
Organizations across all industries choose Cymulate for exposure validation, proactively confirming that defenses are robust and reliable-before an attack occurs.
Upgrading from NetSPI to Cymulate is easy.
We’ve helped numerous clients upgrade from NetSPI to Cymulate. We’ll help you build and customize production-safe assessments for all your environments, so you can independently optimize your controls and reduce exposure risk.