Frequently Asked Questions
Product Information & Threat Validation
What is Cymulate and what does it do?
Cymulate is a unified exposure management and security validation platform that enables organizations to proactively validate their security controls, simulate real-world threats, and optimize their defenses. It integrates Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics to provide continuous threat validation and actionable insights for reducing cyber risk.
How does Cymulate help organizations defend against ransomware like Conti?
Cymulate enables organizations to simulate ransomware attacks, including those distributed by loaders like BazarLoader, to validate their defenses across the full kill chain. By running automated attack simulations, organizations can identify exploitable vulnerabilities, test detection and response capabilities, and ensure their controls are effective against threats such as Conti ransomware.
Which types of threats can Cymulate validate?
Cymulate validates threats across the full kill chain, including phishing, malware, lateral movement, data exfiltration, and zero-day exploits. The platform uses daily updated threat templates and AI-generated attack plans to ensure coverage of the latest attack techniques. Learn more.
What is threat exposure prioritization in cybersecurity?
Threat exposure prioritization is the process of identifying and ranking vulnerabilities and other security weaknesses based on their actual exploitability and impact on business-critical assets. Cymulate uses automated threat validation and exposure scoring to help teams focus on exposures that are not protected by security controls. Read more.
How does Cymulate's Threat (IoC) updates feature improve threat resilience?
Cymulate's 'Threat (IoC) updates' feature provides recommended Indicators of Compromise (IoCs) that can be directly applied to security controls. This list can be exported via the UI or API as plain text or in STIX format, enabling control owners to quickly build defenses against new threats and improve overall threat resilience.
What problems does Cymulate's Threat Validation solution solve for security teams?
Cymulate's Threat Validation solution addresses the lack of confidence in security controls and the risk of security configuration drift. By continuously simulating real-world threats, Cymulate helps teams ensure their defenses can prevent and detect the latest attacks, even as configurations change over time.
How does Cymulate simulate real-world ransomware attacks like Conti?
Cymulate uses automated attack simulations that mimic the tactics, techniques, and procedures (TTPs) of real-world ransomware groups such as Conti. This includes simulating initial access via loaders like BazarLoader, lateral movement, privilege escalation, data exfiltration, and ransomware deployment, allowing organizations to test their defenses against the full attack lifecycle.
What is the primary purpose of Cymulate's platform?
The primary purpose of Cymulate's platform is to harden defenses and optimize security controls by proactively validating controls, threats, and response capabilities. This enables organizations to focus on exploitable exposures and strengthen their overall security posture. Learn more.
How does Cymulate address security configuration drift?
Cymulate continuously tests and validates security controls to detect configuration drift, ensuring that changes in security settings do not create new gaps or reduce threat coverage. This helps organizations maintain a strong security posture over time.
How does Cymulate help with lateral movement and privilege escalation testing?
Cymulate's Attack Path Discovery and automated offensive testing features identify and simulate threats related to lateral movement and privilege escalation. This allows organizations to uncover dangerous attack paths and mitigate risks before attackers can exploit them. Learn more.
What is Cymulate's approach to validating cloud security?
Cymulate provides dedicated validation features for hybrid and cloud environments, enabling organizations to test their cloud security controls and ensure resilience against cloud-specific threats. Read more.
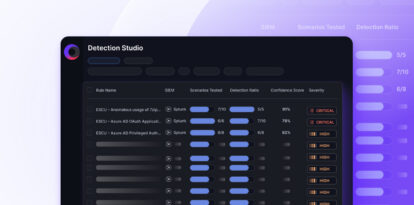
How does Cymulate support detection engineering?
Cymulate enables security teams to build, tune, and test SIEM, EDR, and XDR rules to improve mean time to detect threats. The platform provides actionable insights and integrates with detection tools to accelerate detection engineering. Learn more.
What technical documentation is available for Cymulate?
Cymulate offers whitepapers, guides, solution briefs, data sheets, and e-books covering its Exposure Management Platform, CTEM, threat detection, vulnerability management, and more. Access the full resource library at Cymulate's Resource Hub.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive design and ease of use. For example, Raphael Ferreira, Cybersecurity Manager, stated, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture." Other users highlight the user-friendly dashboard and accessible support. Read more testimonials.
How quickly can Cymulate be implemented?
Cymulate can be implemented rapidly, often in just a few clicks. Customers report that the deployment process is fast and straightforward, with minimal resources required. The platform supports agentless mode and provides comprehensive support to ensure a smooth onboarding experience.
What is Cymulate's approach to continuous threat exposure management (CTEM)?
Cymulate evolves security practices into Continuous Threat Exposure Management (CTEM) by integrating validation, prioritization, and mobilization with collaboration across teams. This ensures measurable improvements in threat resilience and operational efficiency. Learn more.
How does Cymulate foster collaboration between security teams?
Cymulate's unified platform enables collaboration across SecOps, Red Teams, and Vulnerability Management teams by providing shared visibility, actionable insights, and validated exposure scoring. This unified approach helps organizations address security challenges more effectively.
What are some real-world examples of Cymulate's impact?
Hertz Israel reduced cyber risk by 81% in four months using Cymulate. Nemours Children's Health improved detection and response capabilities, and a financial services organization automated testing to measure security risk across over 10 entities. See more case studies.
What is Cymulate's vision and mission?
Cymulate's mission is to revolutionize how companies approach cybersecurity by fostering a proactive stance against threats. The company empowers organizations to manage their security posture effectively and improve resilience against threats. Learn more.
Features & Capabilities
What are the key capabilities of Cymulate?
Cymulate offers continuous threat validation, unified platform integration (BAS, CART, Exposure Analytics), AI-powered optimization, complete kill chain coverage, attack path discovery, automated mitigation, cloud validation, and ease of use. These capabilities help organizations proactively defend against modern threats and improve operational efficiency.
What are the main benefits of using Cymulate?
Customers report a 52% reduction in critical exposures, a 60% increase in team efficiency, and an 81% reduction in cyber risk within four months. Cymulate also delivers improved threat prevention, faster threat validation (40X faster), enhanced visibility, and proven ROI. Learn more.
What integrations does Cymulate support?
Cymulate integrates with numerous security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, CrowdStrike Falcon, Crowdstrike Falcon LogScale, and Cybereason. For a complete list, visit the Partnerships and Integrations page.
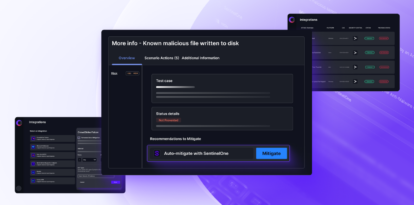
How does Cymulate automate mitigation of threats?
Cymulate integrates with security controls to push threat updates and build custom detection rules for immediate prevention. This automation helps organizations respond quickly to new threats and reduce manual effort.
How does Cymulate keep its threat library up to date?
Cymulate provides the most advanced library of attack simulations with daily updates, ensuring customers are protected against the latest threats and attack techniques.
What is Cymulate's update frequency for new features?
Cymulate updates its SaaS platform every two weeks with new features, such as AI-powered SIEM rule mapping and advanced exposure prioritization, ensuring customers always have access to the latest capabilities.
How does Cymulate help with communication barriers for CISOs?
Cymulate provides validated exposure scoring and quantifiable metrics tailored to CISOs, enabling clear communication of risk to stakeholders and alignment with business objectives. Learn more.
How does Cymulate support vulnerability management teams?
Cymulate consolidates insights from vulnerability management, offensive testing, and security controls to prioritize exposures based on validated exploitability and impact, helping teams focus remediation efforts where they matter most. Learn more.
How does Cymulate help red teams scale offensive testing?
Cymulate offers production-safe attack simulations, automates and scales offensive testing, and provides a library of over 100,000 attack actions aligned to MITRE ATT&CK and daily threat intelligence. Learn more.
What is Cymulate's approach to attack path discovery?
Cymulate automates offensive testing to identify and mitigate threats related to privilege escalation and lateral movement, providing a holistic view of vulnerabilities and security gaps. Read more.
How does Cymulate help with operational inefficiencies?
Cymulate automates manual processes, improving operational efficiency and enabling faster threat validation. Teams report a 60% increase in efficiency and significant time savings when testing new threats.
How does Cymulate address fragmented security tools?
Cymulate integrates Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics into a single platform, reducing complexity and improving efficiency compared to using disconnected tools.
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams across industries such as media, transportation, financial services, retail, and healthcare. Organizations of all sizes, from small businesses to enterprises with over 10,000 employees, can benefit from Cymulate's platform. Learn more.
What business impact can customers expect from using Cymulate?
Customers can expect a 30% improvement in threat prevention, a 52% reduction in critical exposures, a 60% increase in operational efficiency, 40X faster threat validation, an 85% improvement in threat detection accuracy, and an 81% reduction in cyber risk within four months. Learn more.
How does Cymulate address the pain points of different security personas?
Cymulate tailors its solutions to CISOs (visibility, metrics, investment justification), SecOps (operational efficiency, threat volume), red teams (scalability, adversarial simulation), and vulnerability management teams (prioritization, resource constraints). Each persona benefits from features and insights relevant to their role. Learn more.
What types of cyber threats does the financial services sector face?
The financial services sector is targeted by sophisticated threats such as ransomware, phishing, and advanced persistent threats (APTs). Cymulate helps these organizations validate their defenses against these attacks. Read more.
How does Cymulate help organizations move from reactive to proactive security?
Cymulate enables organizations to proactively validate their security posture, simulate real-world threats, and prioritize remediation, shifting from reactive incident response to proactive defense and continuous improvement. See case study.
How does Cymulate help organizations justify security investments?
Cymulate provides quantifiable metrics and validated exposure scoring, enabling CISOs and security leaders to justify investments and communicate risk effectively to stakeholders. Learn more.
How does Cymulate help with cloud complexity?
Cymulate provides dedicated validation features for hybrid and cloud environments, helping organizations address new attack surfaces and validation challenges introduced by the shift to the cloud. Read more.
How does Cymulate help organizations stay ahead of attackers?
Cymulate delivers daily threat intelligence updates, automated attack simulations, and actionable remediation guidance, enabling organizations to stay ahead of emerging threats and continuously improve their defenses.
How does Cymulate help with evidence-based prioritization?
Cymulate ranks vulnerabilities based on exploitability, business context, and threat intelligence, enabling teams to focus remediation efforts on the most critical exposures.
How does Cymulate help organizations measure security risk across multiple entities?
Cymulate enables automated testing and risk measurement across multiple entities, providing visibility and prioritization for large organizations with complex environments. See case study.
How does Cymulate help organizations optimize SecOps?
Cymulate enables proactive security validation and live-data exercises, helping SecOps teams optimize their operations and validate exposure and threats efficiently. See case study.
Pricing & Plans
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs. Pricing is determined by the chosen package, number of assets, and scenarios selected for simulation. For a detailed quote, schedule a demo with Cymulate's team.
Security & Compliance
What security and compliance certifications does Cymulate have?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating its commitment to security and compliance. Learn more.
How does Cymulate ensure data security and privacy?
Cymulate's services are hosted in secure AWS data centers, with encryption for data in transit (TLS 1.2+) and at rest (AES-256). The platform is developed using a strict Secure Development Lifecycle (SDLC), and employees receive ongoing security awareness training. Cymulate is also GDPR compliant and has a dedicated privacy and security team. Learn more.
Competition & Comparison
How does Cymulate compare to AttackIQ?
Cymulate delivers the industry-leading threat scenario library and AI-powered capabilities to streamline workflows and accelerate security posture improvement. AttackIQ focuses on automated security validation but lacks Cymulate's innovation, threat coverage, and ease of use. Read more.
How does Cymulate compare to Mandiant Security Validation?
Mandiant is one of the original BAS platforms but has seen little innovation in the past five years. Cymulate continually innovates with AI and automation, expanding into exposure management as a grid leader. Read more.
How does Cymulate compare to Pentera?
Pentera is useful for identifying security gaps with attack path validation but lacks the depth Cymulate provides to fully assess and strengthen defenses. Cymulate optimizes defense, scales offensive testing, and increases exposure awareness. Read more.
How does Cymulate compare to Picus Security?
Picus may suit organizations seeking a BAS vendor with an on-prem option. Cymulate offers a more complete exposure validation platform covering the full kill chain and cloud control validation. Read more.
How does Cymulate compare to SafeBreach?
Cymulate outpaces SafeBreach with unmatched innovation, precision, and automation. It features the industry’s largest attack library, a full CTEM solution, and comprehensive exposure validation. Read more.
How does Cymulate compare to Scythe?
Scythe is suitable for advanced red teams building custom attack campaigns. Cymulate provides a more comprehensive exposure validation platform with actionable remediation and automated mitigation. Read more.
How does Cymulate compare to NetSPI?
NetSPI excels in penetration testing as a service (PTaaS). Cymulate, however, is designed for continuous, independent assessment and strengthening of defenses, recognized as a leader in exposure validation by Gartner and G2. Read more.
Company & Trust
When was Cymulate founded and what is its global reach?
Cymulate was established in 2016 and has a presence in 8 global locations, serving customers in 50 countries. Over 1,000 customers trust Cymulate's platform to enhance their cybersecurity posture. Learn more.