The Escalating Risk of Business Email Compromise
Attackers Are Launching Email Based Cyber Attacks As Never Before
Cyber criminals and malicious hackers keep targeting email inboxes. Corporate email accounts have always been a favorable target and according to security experts. In the United States alone, Business Email Compromise (BEC) attacks resulted in nearly $3 billion in reported losses in 2023, marking a 58% increase since 2020. The average loss per incident rose from approximately $74,723 in 2019 to $137,132 in 2023, indicating that while the number of incidents has slightly decreased, the financial severity per attack has intensified.
Why Email Is Still the Weakest Link
Roughly three quarters of all reported cyber incidents in 2024 started with phishing emails or malicious attachments sent to company employees. The main reasons why emails are easy pickings for cybercrooks is that because it is simple, does not require massive resources and focuses on the weakest link in the organization “people”. Furthermore, companies have a hard time detecting and mitigating security incidents quickly and accurately.
Last but not least, employees use their own devices for business and private use. The rise of BYOD (Bring Your Own Device) and, increasingly, BYOVD (Bring Your Own Vulnerable Device) has only amplified the risk, as personal devices used for both business and private tasks often lack proper security controls. When it comes to phishing, two simulations yielded a near 100% click rate: one that masqueraded as a database password reset alert, and another that claimed to include an updated building evacuation plan. It underpins how effective social engineering is.
Case Study: Yarrow Point Email Scam and Recent Ransomware Attacks
The Yarrow Point cyberattack shows how aging systems in, e.g., municipalities and governments combined with untrained staff, make easy targets for hackers. As part of an email scam, the Yarrow Point financial coordinator received an email that seemed to come from the town’s mayor asking to transfer money. He promptly wired $49,284 to an unidentified cybercrook. The email was sent by “Richard” although the mayor always used his nickname “Dicker”. A few months later, Yarrow Point fell victim to a ransomware attack, which locked down some of the town’s computer systems. Employees were denied access to files and in the end, nearly $10,000 in bitcoin was paid in ransom.
Email attacks are not going away anytime soon. Hackers will keep on using it to proliferate malware and ransomware, to trick users to browse to malicious websites with the purpose to steal sensitive data or fool employees to transfer money. Let’s take a look at some recent examples of email-based attacks that highlight just how persistent—and damaging—this threat vector remains.
- In March 2025, Google confirmed a surge of cyber-espionage attacks affecting Chrome users due to highly sophisticated malware triggered by phishing links in emails. Kaspersky researchers identified the malware exploiting a zero-day vulnerability, CVE-2025-2783, which allowed attackers to bypass Chrome's sandbox protections. Targeting media professionals, educational institutions, and government agencies, this attack was dubbed "Operation ForumTroll." Google announced a forthcoming security patch to address the vulnerability in the next browser update
- In February 2024, Change Healthcare, a subsidiary of UnitedHealth Group and one of the largest health data processors in the U.S., suffered a devastating ransomware attack by the ALPHV/BlackCat gang. The breach caused widespread outages across the healthcare sector, halting billing systems, delaying insurance claims, and affecting services at military pharmacies worldwide
- In the week of February 12, the City of Allentown, PA was hit by a cyberattack originating from a malicious email containing malware dubbed Emotet. The self-replicating malware stole credentials such as passwords of city employees. The municipality was forced to shut down some financial and public safety operations. The total costs will be around $1 million, including $800,000 to $900,000 for repairing the damage that the virus has done.
Especially BEC attacks use email to impersonate, spoof and spear-phish to trick employees into wiring millions of dollars to the hackers’ shell corporations and corresponding bank accounts.
Reducing BEC Risks
There are proven policies and safeguards organizations can put in place to make email attacks far less susceptible to Business Email Compromise:
- Educate employees about the risks to prevent social engineering.
- Make sure that systems and software are updated.
- Use an intrusion detection system that can flag e-mails with extensions that are (too) similar to the corporate e-mail extension.
- Flag e-mail conversations where the “reply” e-mail address is different from the “from” e-mail address.
- Color-code e-mails from employee/internal accounts in one color and e-mails from non-employee/external accounts in another color.
- Apply two-factor authentication requiring two different employees for all wire transfers.
- Use phone verification by dialing the telephone numbers registered in the system (and not the one in the email).
- Scrutinize all e-mail requests for suspicious transfer of funds.
- Implement the Domain Message Authentication Reporting & Conformance (DMARC) standard that verifies the domain of an email message.
Although these measures will help, they are not enough to prevent email attacks. The best approach is to conduct regular security assessments to expose the vulnerabilities within the organization by using a breach and attack simulation (BAS) platform.
How Cymulate Validates Email Security Readiness
To help organizations stay ahead of email-based threats, Cymulate offers an E-Mail module as part of its Breach and Attack Simulation (BAS) platform. This module tests how prepared organizations from all industries really are when it comes to handling these threats.
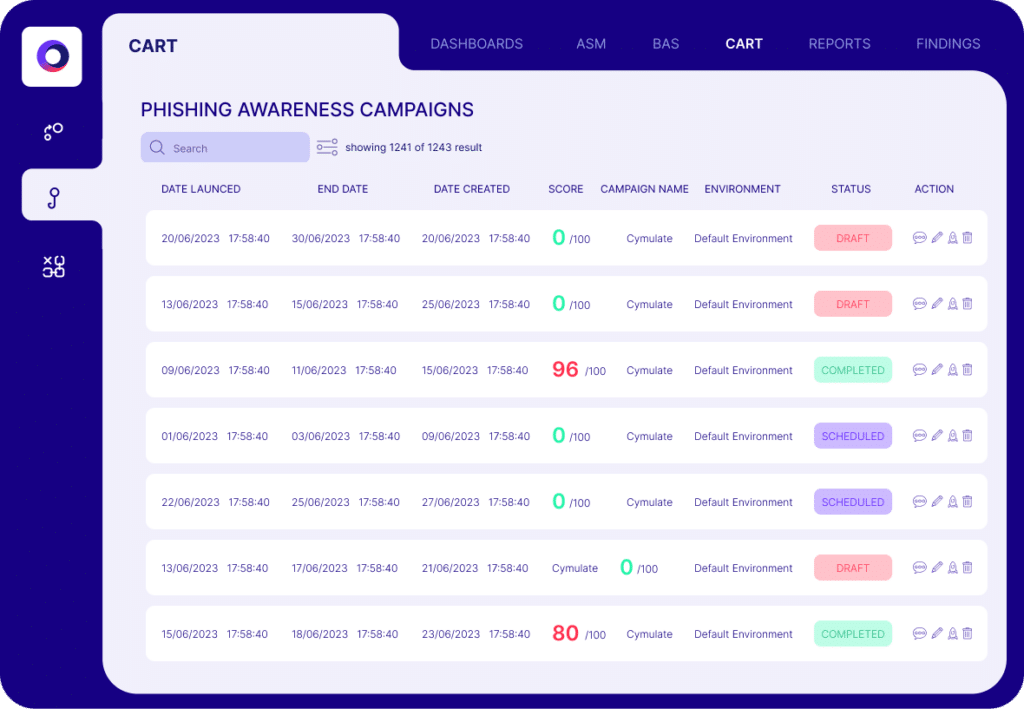
The simulation deploys offensive and defensive actions to expose critical vulnerabilities, such as sending emails containing ransomwares, worms, Trojans, links to malicious websites etc. to see if these emails would bypass the organizations’ first line of defense and reach their employees. During the next step, they can also test their security awareness regarding receiving such socially engineered emails that try to phish the employees into opening malicious attachments, disclosing their credentials or clicking on malicious links.
Ready to see how your defenses stack up? Book a demo with Cymulate to validate your organization’s resilience against email-based cyber threats.