New SEC Cybersecurity Rules: Reporting Requirements and How to Prepare
New SEC rules require public companies to report cyber incidents and detail cybersecurity governance. This blog explores how the rules change reporting, the need to involve leadership beyond just technology, and how Cymulate products can generate data to showcase strengthening defenses over time. A short read for executives on how to prepare for the upcoming requirements.
Understanding the New SEC Cybersecurity Disclosure Rules
In July 2023, the SEC adopted new cybersecurity reporting requirements for publicly traded companies. These rules mandate organizations to:
- Disclose cybersecurity incidents with a “material impact” within four business days via Form 8-K.
- Report annual cybersecurity governance and risk management practices in Form 10-K, even if no incidents occur.
Failure to comply with these requirements or submitting false or misleading information can result in regulatory penalties.
What Constitutes a “Material Impact” in Cybersecurity Reporting?
The SEC defines material impact as an event that would significantly influence an investor’s decision-making. According to Harvard Law School, materiality refers to:
“A substantial likelihood that a reasonable shareholder would consider it important in deciding how to vote” or “a substantial likelihood that the disclosure of the omitted fact would have been viewed by the reasonable investor as having significantly altered the ‘total mix’ of information made available.”
SEC Cybersecurity Rules: Key Reporting Requirements
1. Immediate Incident Reporting (Form 8-K)
Organizations experiencing a material cybersecurity incident must submit Form 8-K within four business days detailing:
- The nature of the incident
- The potential impact on business operations and investors
Companies may update reports as new information becomes available. A deferment is allowed only if the U.S. Government determines that disclosure would pose a national security or public safety risk.
2. Annual Cybersecurity Governance Disclosure (Form 10-K)
Publicly traded companies must also report their cybersecurity governance and risk management practices annually, including:
- Board oversight and leadership involvement
- Cyber risk management strategies
- Incident preparedness measures
How Organizations Can Prepare for the SEC Cybersecurity Rules
As the rules go (primarily) into effect on December 15, 2023, organizations do not have a lot of time to prepare for the changes to their annual reporting. They must also prepare to file Form 8-K should an incident occur and do so relatively quickly – having only four days to react. It is in the interest of all publicly traded organizations to prepare now for how they will meet the new reporting requirements later this year.
Defining Process and People, Not Just Technology
These new rules change how many organizations will think about cybersecurity. Requiring reporting on the process an organization takes to defend against cyber threats – including “… reasonably likely material effects of risks from cybersecurity threats and previous cybersecurity incidents” is vastly different from traditional cybersecurity operations which work in a reactive methodology to block threat activity as it is encountered.
Organizations must define how a potential threat activity that is reasonably known about would impact their organization if it were to be targeted at them, including reporting on processes that would be used to limit damage or define impact.
Additionally, the new rules require annual reporting to “… describe the board of directors’ oversight of risks from cybersecurity threats and management’s role and expertise in assessing and managing material risks from cybersecurity threats.” In essence, the SEC is now requiring that business leadership, not just technical leadership, is involved in handling cybersecurity.
Senior leadership teams and the board can no longer consider cybersecurity as the sole responsibility of the technology divisions of the organization but must detail how they are personally involved.
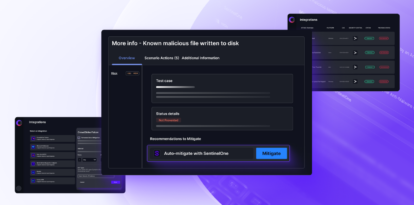
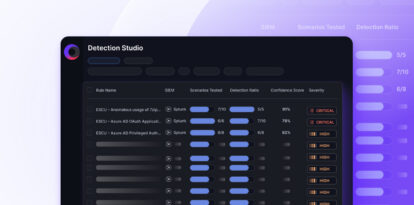
How Cymulate Helps Organizations Meet SEC Cybersecurity Requirements
Multiple products provided by Cymulate can aid in satisfying these new regulatory rules. Using Breach and Attack Simulation (BAS) and Continuous Automated Red Teaming (CART) all produce reporting that can be used to show how the organization is preparing for threat activity by testing their processes and technologies and remediating discovered weaknesses or gaps while also ensuring that any strengths are preserved and continue defending the organization. By using these tools over time, organizations can show the effectiveness of cyber resilience programs, and the growth in defensive operations as the threat landscape changes.
Exposure Analytics is a valuable asset in preparing for annual report filing.
By linking assets to business contexts, senior business leadership and the board (where required) can see the direct risk to business operations posed by cybersecurity operations, decisions, and actions against known threat activity.
Risk scoring provides the ability to view how budgetary and process decisions impact the ability of the business to defend itself and highlight where operations could be disrupted, or critical data lost if key assets remain at high levels of risk for significant periods of time.
Conversely, steps taken to strengthen key areas of defense, modernize or remove legacy platforms, and other operations that strengthen resilience and reduce risk will also be visible for inclusion in these reports, categorized by business context and significance to the organization and its operations.
Beyond the New Rules
Cymulate products can assist in meeting the reporting requirements created by these new rules, but they can also assist in mitigating the fallout of information that becomes public as a result of the rules. If an organization suffers a novel attack, having documentation and data that shows that the organization was preparing for and defending against an attack can be invaluable. Investor and customer confidence can be bolstered if the organization can prove that they were doing everything they could to avoid the attack being successful, and ongoing threat resilience with BAS and CART can provide that evidence.
Schedule a demo today and see how ongoing security validation can support your SEC compliance and boost stakeholder confidence