Frequently Asked Questions
Collaboration & Organizational Impact
How does Continuous Security Validation improve collaboration between risk management teams?
Continuous Security Validation fosters collaboration by providing objective, data-driven insights that all lines of defense—first, second, and third—can use to align on risk language, identify measurable improvements, and avoid communication breakdowns. By offering trend data and early indicators of control deviations, it enables teams to proactively address issues, reducing escalation and improving overall risk management outcomes. (Source: Cymulate Blog)
What are the main communication challenges Continuous Security Validation helps solve?
It addresses challenges such as technical misunderstandings, overdue actions, and subjective opinions that can lead to ineffective controls and increased organizational risk. By shifting conversations to a data-driven, risk-assessment-scored approach, teams can focus on facts rather than opinions, reducing unnecessary escalations and ensuring more effective risk mitigation. (Source: Cymulate Blog)
How does Cymulate help organizations with limited audit and assurance resources?
Cymulate provides always-on assurance, reducing reliance on sample-based manual testing. This is especially valuable for organizations with fewer second and third line resources, as it automates oversight and provides continuous, fact-driven evidence for risk management. (Source: Cymulate Blog)
What are the benefits of using trend data in security validation?
Trend data allows organizations to pinpoint security control deviations and failures, monitor if controls are keeping pace with evolving threats, and identify measurable improvements over time. This enables proactive risk management and supports more accurate, accountable risk-return submissions. (Source: Cymulate Blog)
How does Cymulate support a culture of 'operate securely'?
Cymulate embeds automated oversight and continuous validation into daily operations, driving control maturity and accountability. This helps organizations maintain an 'operate securely' mindset, ensuring that security is an ongoing, measurable process rather than a one-time event. (Source: Cymulate Blog)
How does Continuous Security Validation help first-line teams?
First-line teams benefit by being empowered to self-identify changes that may impact security posture early, communicate risk in a consistent language, and reduce the burden of providing evidence to auditors. This leads to more efficient business-as-usual (BAU) operations and improved risk management. (Source: Cymulate Blog)
What value does Continuous Security Validation provide to second and third line teams?
Second and third line teams gain access to real-time data, reducing the need for manual assurance or audit activities. This minimizes resource overhead and enables more effective, ongoing oversight of security controls. (Source: Cymulate Blog)
How does Cymulate help avoid emotional or subjective risk discussions?
By providing fact-driven evidence and objective metrics, Cymulate helps teams focus on measurable outcomes rather than subjective opinions, reducing emotional debates and fostering constructive, data-based risk management conversations. (Source: Cymulate Blog)
How does Cymulate support perimeter-facing controls like Endpoint, Email, and Web gateways?
Cymulate enables BAU teams to identify and address issues in perimeter-facing controls early, reducing the risk of high-impact vulnerabilities and ensuring that controls are effective against the latest threats. (Source: Cymulate Blog)
What is the overall business impact of implementing Continuous Security Validation?
Organizations can expect improved control maturity, more accurate risk-return submissions, and a more accountable security culture. Continuous Security Validation helps keep risk management processes aligned with business objectives and regulatory requirements. (Source: Cymulate Blog)
Features & Capabilities
What features does Cymulate offer for security validation?
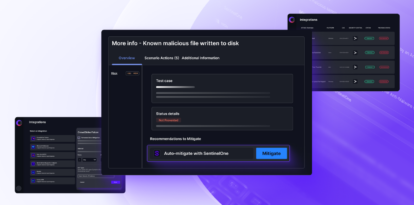
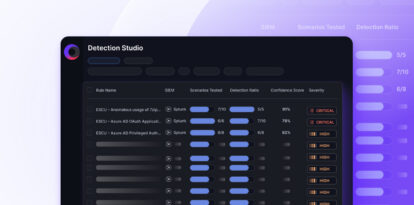
Cymulate offers a unified platform that integrates Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics. Key features include 24/7 automated attack simulations, AI-powered optimization, complete kill chain coverage, attack path discovery, automated mitigation, cloud validation, and an extensive threat library with daily updates. (Source: Cymulate)
Does Cymulate support integration with other security technologies?
Yes, Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, CrowdStrike Falcon, Crowdstrike Falcon LogScale, and Cybereason. For a full list, visit the Cymulate Partnerships and Integrations page.
What are the key benefits of Cymulate's Endpoint Security Validation?
Cymulate's Endpoint Security Validation automates continuous testing of endpoint controls, identifies gaps and weaknesses, provides mitigation guidance, and continuously measures and improves endpoint security posture to reduce cyber attack risk. (Source: Cymulate Endpoint Security Validation)
How does Cymulate automate security validation?
Cymulate automates security validation through continuous, agentless simulations that test security controls across the full attack lifecycle. The platform provides actionable insights, automated mitigation, and integrates with existing security tools to streamline workflows and accelerate improvement. (Source: Cymulate)
What is the Cymulate threat library?
The Cymulate threat library is an advanced collection of attack simulations, updated daily, that enables organizations to test their defenses against the latest threats and tactics. (Source: Cymulate)
How does Cymulate help with cloud security validation?
Cymulate provides dedicated validation features for hybrid and cloud environments, integrating with cloud-native security tools and simulating attacks to ensure cloud controls are effective against emerging threats. (Source: Cymulate)
How often is Cymulate updated with new features?
Cymulate updates its SaaS platform every two weeks, introducing new features such as AI-powered SIEM rule mapping and advanced exposure prioritization to keep customers ahead of evolving threats. (Source: Cymulate)
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams across industries such as media, transportation, financial services, retail, and healthcare. It is suitable for organizations of all sizes, from small businesses to enterprises with over 10,000 employees. (Source: Cymulate)
What business impact can customers expect from using Cymulate?
Customers typically see a 30% improvement in threat prevention, a 52% reduction in critical exposures, a 60% increase in team efficiency, and an 81% reduction in cyber risk within four months. These outcomes are supported by customer case studies such as Hertz Israel. (Source: Cymulate)
How does Cymulate help with operational efficiency?
Cymulate automates manual processes, enabling teams to validate threats 40 times faster and save an average of 60 hours when testing new threats. This allows security teams to focus on strategic initiatives rather than repetitive tasks. (Source: Cymulate)
How does Cymulate improve collaboration between SecOps, red teams, and vulnerability management?
Cymulate's validated exposure scoring consolidates insights from vulnerability management, offensive testing, and security controls, providing a unified view that fosters collaboration and more efficient prioritization across teams. (Source: Cymulate)
What measurable outcomes have customers reported after using Cymulate?
Customers have reported a 52% reduction in critical exposures, a 60% increase in team efficiency, and an 81% reduction in cyber risk within four months. These results are based on real-world deployments and case studies. (Source: Cymulate)
Pricing & Plans
What is Cymulate's pricing model?
Cymulate uses a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and scenarios selected for simulation. For a personalized quote, you can schedule a demo with Cymulate's team. (Source: Cymulate)
How can I start a Cymulate free trial?
You can start a 14-day free trial of Cymulate by visiting the Cymulate Free Trial page. This allows you to experience the platform's capabilities firsthand. (Source: Cymulate Blog)
Implementation & Ease of Use
How long does it take to implement Cymulate?
Cymulate is known for its fast and straightforward implementation. Customers report being able to deploy and integrate Cymulate quickly, often in just a few clicks, with minimal resources required. (Source: Cymulate)
How easy is Cymulate to use?
Cymulate is praised for its intuitive, user-friendly interface and dashboard. Customers highlight its ease of use, quick deployment, and the high functionality provided for assessing security posture. (Source: Cymulate)
What support resources does Cymulate provide for onboarding?
Cymulate offers comprehensive support, including email and chat support, webinars, e-books, and a knowledge base to ensure a smooth onboarding process. (Source: Cymulate)
Security & Compliance
What security and compliance certifications does Cymulate hold?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating its commitment to robust security and compliance practices. (Source: Cymulate Security)
How does Cymulate ensure data security and privacy?
Cymulate hosts its services in secure AWS data centers, uses strong encryption (TLS 1.2+ for data in transit, AES-256 for data at rest), and follows a strict Secure Development Lifecycle (SDLC) with regular audits and third-party penetration tests. It also complies with GDPR and employs a dedicated privacy and security team. (Source: Cymulate)
Competition & Comparison
How does Cymulate compare to AttackIQ?
Cymulate offers a larger threat scenario library, AI-powered capabilities, and greater ease of use compared to AttackIQ, which focuses on automated security validation but lacks Cymulate's innovation and coverage. (Source: Cymulate vs AttackIQ)
How does Cymulate differ from Mandiant Security Validation?
Mandiant is one of the original BAS platforms but has seen little innovation in recent years. Cymulate continually innovates with AI and automation, expanding into exposure management and recognized as a grid leader. (Source: Cymulate vs Mandiant)
What makes Cymulate different from Pentera?
Pentera is useful for attack path validation but lacks the depth Cymulate provides for fully assessing and strengthening defenses. Cymulate optimizes defense, scales offensive testing, and increases exposure awareness. (Source: Cymulate vs Pentera)
How does Cymulate compare to Picus Security?
Picus may suit organizations seeking a BAS vendor with an on-prem option. Cymulate offers a more complete exposure validation platform covering the full kill chain and cloud control validation. (Source: Cymulate vs Picus)
How does Cymulate differ from SafeBreach?
Cymulate outpaces SafeBreach with unmatched innovation, precision, and automation. It features the industry’s largest attack library, a full CTEM solution, and comprehensive exposure validation. (Source: Cymulate vs SafeBreach)
How does Cymulate compare to Scythe?
Scythe is suitable for advanced red teams building custom attack campaigns. Cymulate provides a more comprehensive exposure validation platform with actionable remediation and automated mitigation. (Source: Cymulate vs Scythe)
How does Cymulate differ from NetSPI?
NetSPI excels in penetration testing as a service (PTaaS). Cymulate is designed for continuous, independent assessment and strengthening of defenses, recognized as a leader in exposure validation by Gartner and G2. (Source: Cymulate vs NetSPI)