Frequently Asked Questions
Cybersecurity Talent Shortage & Industry Trends
Why is there a global shortage of cybersecurity professionals?
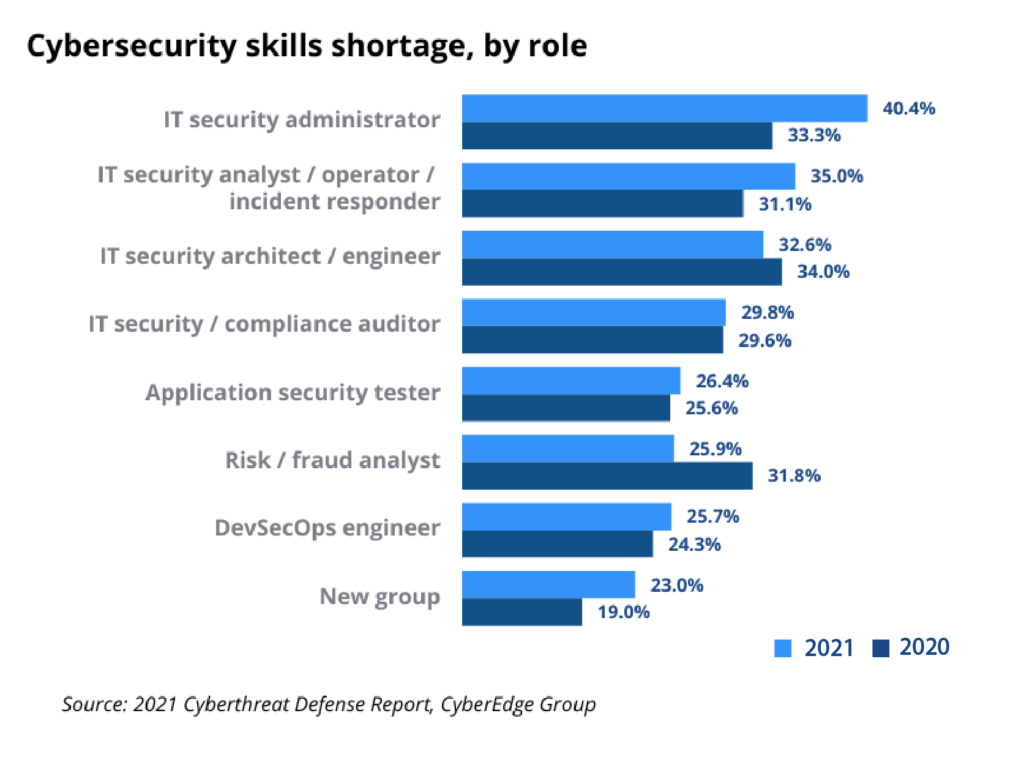
The global shortage of cybersecurity professionals is driven by the rapid increase in cyber threats and compliance demands, outpacing the supply of skilled workers. As of 2021, there were 3.5 million unfilled cybersecurity positions worldwide (source: New York Times, Cybersecurity Ventures). Organizations struggle to hire, develop, and retain talent, leaving them vulnerable to attacks and regulatory penalties.
How long do cybersecurity jobs typically remain unfilled?
Many cybersecurity jobs remain unfilled for six months or more due to the scarcity of candidates with the required skill sets and experience. This delay increases organizational risk and can lead to compromised security and compliance.
Can professionals from non-technical backgrounds succeed in cybersecurity?
Yes. According to (ISC)², 30% of cybersecurity professionals worldwide started their careers after holding non-technical roles such as business, accounting, or marketing. Organizations are increasingly hiring and training talent from diverse backgrounds to address the skills gap.
What strategies help organizations overcome the cybersecurity talent shortage?
Organizations can broaden their candidate pool beyond traditional tech backgrounds, partner with Managed Security Service Providers (MSSPs), and adopt security solutions that automate processes and educate users simultaneously. These strategies help fill gaps, upskill staff, and maintain compliance.
How do MSSPs help organizations with limited cybersecurity staff?
Managed Security Service Providers (MSSPs) offer advanced managed security services, including threat management, vulnerability management, anti-malware, scanning, and testing. They enable organizations of all sizes to access expert resources and automated tools, reducing the burden on internal teams and ensuring compliance.
What types of organizations benefit most from MSSPs?
Large enterprises, distributed organizations (like hotel and restaurant chains), and small to medium-sized businesses (SMBs) all benefit from MSSPs. Large organizations seek advanced managed services, while SMBs rely on MSSPs due to limited budgets and staff, ensuring protection and regulatory compliance.
How does automation help address the cybersecurity skills gap?
Automation enables less-experienced professionals to be effective while learning on the job. Solutions like Cymulate automate attack simulations and validation, allowing teams to focus on strategic tasks and upskill through hands-on experience with real-world threats.
What role does on-the-job training play in cybersecurity readiness?
On-the-job training, combined with practical tools and incident response exercises, helps teams develop and practice skills needed for effective breach response. This approach improves both individual and team performance during real incidents.
How does Cymulate support skill development for cybersecurity professionals?
Cymulate's platform enables users to launch attack simulations and run expert-created assessments, which are constantly updated with the latest attack techniques. Practitioners increase their adversarial knowledge and defensive skills through hands-on use, making them better defenders over time.
What is the impact of the cybersecurity talent shortage on compliance?
The shortage of skilled professionals makes it harder for organizations to maintain compliance with evolving standards. This increases the risk of breaches, fines, and other punitive measures. Automated solutions and MSSPs help bridge the gap and ensure ongoing compliance.
Features & Capabilities
What features does Cymulate offer to help organizations with limited cybersecurity resources?
Cymulate provides continuous threat validation, automated attack simulations, exposure prioritization, and a unified platform that combines Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics. These features help organizations of all sizes improve their security posture with minimal resources.
How does Cymulate automate security validation?
Cymulate automates security validation by running 24/7 attack simulations, validating defenses in real-time, and integrating with security controls to push updates for immediate threat prevention. The platform's AI-powered optimization prioritizes remediation efforts and provides actionable insights.
Does Cymulate support attack path discovery and lateral movement testing?
Yes, Cymulate includes attack path discovery capabilities, allowing organizations to identify potential attack paths, privilege escalation, and lateral movement risks. This helps teams proactively address vulnerabilities before attackers can exploit them.
How does Cymulate help prioritize vulnerabilities and exposures?
Cymulate validates exploitability and ranks exposures based on prevention and detection capabilities, business context, and threat intelligence. This enables organizations to focus on the most critical vulnerabilities and optimize remediation efforts.
What integrations does Cymulate support?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a complete list, visit our Partnerships and Integrations page.
How does Cymulate keep its threat simulation library up to date?
Cymulate provides an extensive library of over 100,000 attack actions aligned to MITRE ATT&CK, updated daily with the latest threat intelligence. This ensures organizations can test their defenses against emerging threats.
Is Cymulate easy to use for teams with varying skill levels?
Yes. Customers consistently praise Cymulate for its intuitive, user-friendly interface and ease of use. The platform is designed for quick implementation and provides actionable insights with minimal setup, making it accessible for users of all skill levels. Read customer testimonials.
How quickly can Cymulate be implemented?
Cymulate is designed for rapid deployment. It operates in agentless mode, requiring no additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment, with support available via email and chat. Schedule a demo to learn more.
What educational resources does Cymulate provide?
Cymulate offers a Resource Hub with insights, thought leadership, and product information, a blog covering the latest threats and research, webinars, e-books, and a glossary of cybersecurity terms. Access these resources at our Resource Hub.
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, Red Teams, and vulnerability management teams across organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. The platform addresses the unique needs of each role, improving threat resilience and operational efficiency.
How does Cymulate help organizations with fragmented security tools?
Cymulate integrates exposure data and automates validation, providing a unified view of the security posture. This helps organizations overcome gaps in visibility and control caused by disconnected tools. See the Hertz Israel case study.
What measurable outcomes have customers achieved with Cymulate?
Customers have reported an 81% reduction in cyber risk within four months (Hertz Israel), a 52% reduction in critical exposures, a 60% increase in team efficiency, and up to 60 hours saved per month in testing new threats. Explore more case studies.
How does Cymulate address resource constraints in security teams?
Cymulate automates manual tasks, improves operational efficiency, and enables teams to focus on strategic initiatives. This is especially valuable for organizations with limited staff or budgets. Read the sustainable energy case study.
How does Cymulate help with risk prioritization?
Cymulate provides validated data to prioritize exposures based on exploitability, business context, and threat intelligence, enabling teams to focus on the most urgent vulnerabilities. See the credit union case study.
Can Cymulate help organizations with cloud security validation?
Yes. Cymulate secures hybrid and cloud infrastructures through automated compliance and regulatory testing. For example, Nemours Children's Health improved detection and response in hybrid and cloud environments using Cymulate. Read the case study.
How does Cymulate support communication with executives and regulators?
Cymulate delivers quantifiable metrics and insights tailored to different roles, helping CISOs and security leaders justify investments and communicate risks effectively. Saffron Building Society used Cymulate to prove compliance and improve governance. Read the case study.
How does Cymulate help with post-breach recovery?
Cymulate enhances visibility and detection capabilities after a breach, ensuring faster recovery. For example, a bank improved protection and recovery by replacing manual processes with Cymulate. Read the case study.
What pain points does Cymulate solve for different personas?
Cymulate tailors solutions for CISOs (communication barriers, risk prioritization), SecOps teams (resource constraints, operational inefficiencies), Red Teams (threat simulation), and Vulnerability Management teams (validation and prioritization). Learn more on the CISO, SecOps, Red Teaming, and Vulnerability Management pages.
Security, Compliance & Implementation
What security and compliance certifications does Cymulate hold?
Cymulate is certified for SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. These certifications demonstrate adherence to industry-leading security and privacy standards. Learn more.
How does Cymulate ensure data security?
Cymulate uses encryption for data in transit (TLS 1.2+) and at rest (AES-256), hosts data in secure AWS data centers, and maintains a tested disaster recovery plan. Application security includes a secure development lifecycle, vulnerability scanning, and third-party penetration testing.
Is Cymulate GDPR compliant?
Yes. Cymulate incorporates data protection by design and has a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO), ensuring GDPR compliance.
What security features are built into the Cymulate platform?
The platform includes mandatory 2-Factor Authentication (2FA), Role-Based Access Controls (RBAC), IP address restrictions, and TLS encryption for its Help Center, ensuring robust access and data security.
How does Cymulate support implementation and onboarding?
Cymulate offers comprehensive support via email and chat, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers. Customers are responsible for providing necessary infrastructure, but the platform is designed for seamless integration and rapid adoption.
Where can I find Cymulate's latest news, research, and resources?
Stay updated with Cymulate's latest news, research, and resources through the blog, newsroom, events and webinars, and the Resource Hub.
Does Cymulate provide content on preventing lateral movement attacks?
Yes. Cymulate has a blog post titled 'Stopping Attackers in Their Tracks' that discusses common lateral movement attacks and prevention strategies. Read the blog post.
How does Cymulate's vision and mission relate to its product?
Cymulate's mission is to transform cybersecurity by enabling organizations to proactively validate defenses, identify vulnerabilities, and optimize their security posture. The platform supports this vision by providing continuous validation, actionable insights, and fostering collaboration across teams. Learn more about Cymulate's mission.
Where can I find a glossary of cybersecurity terms?
Cymulate provides an expanding glossary of cybersecurity terms, acronyms, and jargon. Access it at our glossary.
Pricing & Plans
What is Cymulate's pricing model?
Cymulate uses a subscription-based pricing model tailored to each organization's requirements. Pricing depends on the chosen package, number of assets, and scenarios selected. For a detailed quote, schedule a demo with the Cymulate team.