Frequently Asked Questions
EDR Detection Rules & Endpoint Security
What is the purpose of Cymulate's EDR mitigation rules?
Cymulate's EDR mitigation rules are designed to help security administrators quickly identify and address weaknesses in endpoint security controls. These rules provide actionable guidance for creating new detection rules in EDR systems, enabling organizations to detect and prevent advanced attack tactics and techniques used by threat actors. By offering generic, adaptable rules, Cymulate accelerates defensive actions and improves overall endpoint resilience.
How does Cymulate assess endpoint security controls?
The Cymulate platform conducts comprehensive assessments of endpoint security controls by simulating thousands of signature-based and behavior-based attack scenarios. These simulations cover a wide range of threats, including malware, ransomware, worms, trojans, rootkits, DLL side-loading, and malicious code injection. The results help security teams identify which attack scenarios were not detected or prevented by their EDR solution, highlighting areas for improvement.
What types of attacks does Cymulate simulate for endpoint security?
Cymulate simulates a broad spectrum of attack types, including the latest malware, ransomware, worms, trojans, rootkits, DLL side-loading, and malicious code injection. These simulations are designed to test the effectiveness of endpoint security controls against real-world threats and uncover potential detection gaps.
How do Cymulate's EDR mitigation rules help accelerate defensive actions?
Cymulate's EDR mitigation rules provide security administrators with ready-to-use, generic detection rules that can be adapted to any EDR platform. By offering guidance on which fields and values to use, these rules enable rapid configuration of new detection rules, reducing the time needed to respond to emerging threats and minimizing the window of exposure.
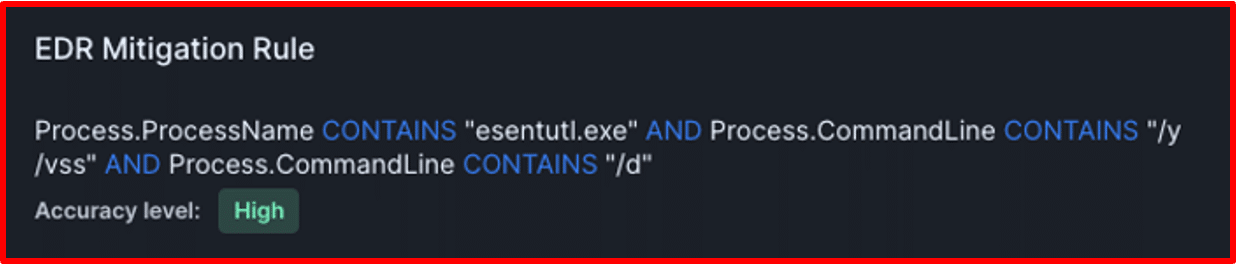
What is Cymulate's generic security detection query language?
Cymulate has developed a generic security detection query language to write EDR mitigation rules. This language standardizes the fields and values needed to codify new detection rules, making it easier for security admins to translate and implement these rules across different EDR platforms, despite variations in terminology and syntax.
How can security administrators translate Cymulate's mitigation rules to their EDR system?
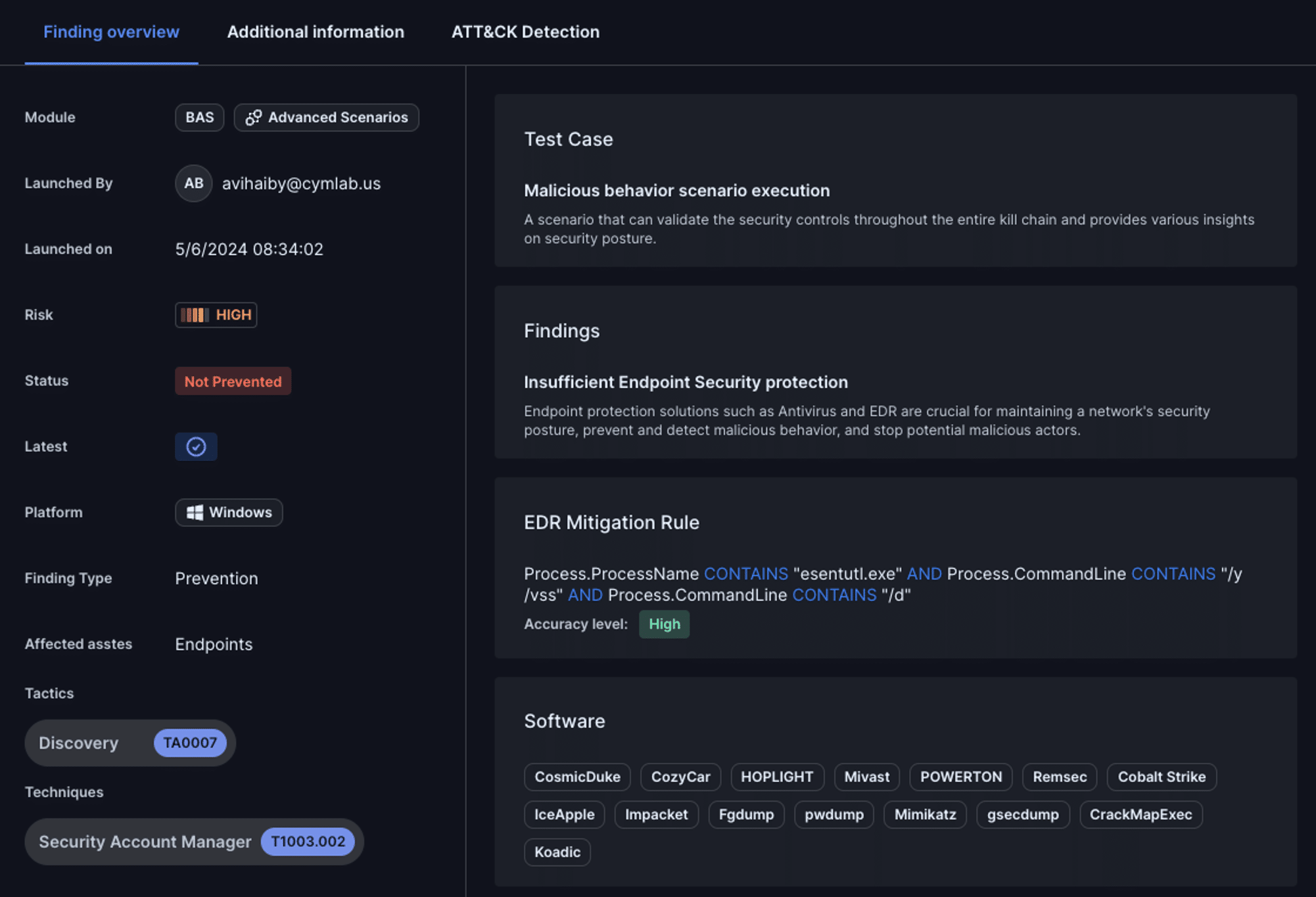
Security administrators can take the generic EDR mitigation rules provided by Cymulate and adapt them to the specific syntax required by their EDR system. Each rule includes an accuracy level to guide customization and minimize false positives. Admins are encouraged to start with detection rules, monitor for false positives, and then consider creating prevention rules if appropriate.
What is the significance of the accuracy level in Cymulate's EDR mitigation rules?
Each EDR mitigation rule from Cymulate is assigned an accuracy level (very low, low, medium, high, very high), indicating the likelihood of generating false positives. Security admins use this as a guide to determine if further customization is needed before deploying the rule in production environments, ensuring effective detection without overwhelming the system with alerts.
Can Cymulate's EDR mitigation rules be used for prevention as well as detection?
Yes, while Cymulate's EDR mitigation rules are primarily designed for detection, security admins with the appropriate expertise may use them as a basis for creating prevention rules. However, it is recommended to start with detection, monitor for false positives, and only then consider prevention to avoid unintended disruptions.
How does Cymulate validate the effectiveness of newly implemented EDR detection rules?
After configuring a new detection rule based on Cymulate's mitigation guidance, security teams can rerun the endpoint security assessment within Cymulate. This process validates whether the EDR solution now successfully detects the simulated attack, confirming the rule's effectiveness.
Why is time critical when implementing new EDR detection rules?
According to the CrowdStrike 2024 Global Threat Report, adversaries can achieve lateral movement within a network in just over an hour (average 62 minutes for eCrime actors). Rapid implementation of new detection rules is essential to minimize the risk of a successful breach and reduce the window of exposure to emerging threats.
What is an example of using Cymulate's EDR mitigation rule with CrowdStrike Falcon?
After running a Cymulate endpoint security assessment, if a malicious behavior is not detected by CrowdStrike Falcon, the findings overview provides a generic EDR mitigation rule. The Falcon administrator can copy this rule, adapt it to Falcon's syntax, and implement it as a detection rule. The effectiveness is then validated by rerunning the assessment to ensure the attack is now detected.
How do Cymulate's EDR mitigation rules help reduce false positives?
Each mitigation rule includes an accuracy level, guiding security admins to adjust the rule as needed before deployment. By starting with detection and monitoring results, organizations can fine-tune rules to balance detection efficacy and minimize false positives, ensuring operational stability.
Why are Cymulate's EDR mitigation rules considered strategic assets?
Cymulate's EDR mitigation rules are strategic assets because they enable organizations to accelerate the implementation of risk mitigation actions, improve cyber resilience, and stay ahead of evolving threats by continuously validating and updating endpoint security controls.
How can I see Cymulate's endpoint security assessment in action?
You can schedule a personalized demo with Cymulate to see how endpoint security assessments validate the efficacy of your endpoint security controls and how EDR mitigation rules can help you configure new detection rules in your EDR system. Visit the demo page to book a session.
What is the process for identifying endpoint security weaknesses with Cymulate?
After running an endpoint security assessment, Cymulate provides findings that highlight simulated attack scenarios not detected or prevented by your EDR solution. These findings help security teams pinpoint weaknesses and prioritize the configuration of new detection rules to address them.
How does Cymulate help with lateral movement attack detection?
Cymulate's attack simulations include scenarios for lateral movement, such as DLL side-loading and malicious code injection. By identifying gaps in detection for these tactics, Cymulate helps organizations configure EDR rules to detect and prevent lateral movement attacks more effectively.
What resources are available to learn more about Cymulate's EDR detection rule capabilities?
You can explore Cymulate's technical documentation, whitepapers, guides, and data sheets in the Resource Hub. These resources provide in-depth insights into exposure management, detection engineering, and endpoint security validation.
How does Cymulate's approach differ from traditional EDR rule management?
Traditional EDR rule management often relies on manual tuning and reactive updates. Cymulate automates the identification of detection gaps and provides generic, adaptable mitigation rules, enabling faster and more proactive defensive actions across diverse EDR platforms.
What are the benefits of using Cymulate for endpoint security validation?
Cymulate enables organizations to proactively identify detection gaps, accelerate the implementation of new EDR rules, reduce the risk of breaches, and improve overall cyber resilience. The platform's automation and actionable guidance help security teams respond faster to emerging threats and continuously optimize endpoint defenses.
How does Cymulate support different EDR platforms?
Cymulate's generic mitigation rules are designed to be adaptable to any EDR platform. Security administrators can translate these rules into the specific syntax required by their chosen EDR solution, ensuring broad compatibility and flexibility.
Features & Capabilities
What features does Cymulate offer for endpoint security validation?
Cymulate offers comprehensive endpoint security validation through automated attack simulations, generic EDR mitigation rules, and a standardized query language for rule creation. The platform also provides actionable findings, accuracy levels for rules, and guidance for adapting rules to any EDR system.
Does Cymulate integrate with other security tools?
Yes, Cymulate integrates with a wide range of technology partners across network, cloud, endpoint, and SIEM domains. Examples include Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, CrowdStrike Falcon, and more. For a full list, visit the Partnerships and Integrations page.
How easy is Cymulate to implement and use?
Cymulate is designed for quick, agentless deployment with minimal resources required. Customers report that the platform is intuitive and user-friendly, allowing security teams to start running simulations and receiving actionable insights within minutes. Comprehensive support and educational resources are also available.
What technical documentation is available for Cymulate?
Cymulate provides whitepapers, guides, data sheets, solution briefs, and e-books covering topics such as exposure management, detection engineering, and vulnerability validation. Access these resources in the Resource Hub.
What security and compliance certifications does Cymulate have?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, ensuring robust security, privacy, and compliance with global standards. For more details, visit the Security at Cymulate page.
How does Cymulate help prioritize exposures and remediation?
Cymulate ranks vulnerabilities based on exploitability, business context, and threat intelligence, enabling security teams to focus remediation efforts on the most critical exposures. This evidence-based prioritization improves operational efficiency and risk reduction.
What is Cymulate's approach to continuous threat validation?
Cymulate offers 24/7 automated attack simulations, continuously validating security posture and providing real-time insights to proactively defend against emerging threats. The platform's extensive threat library is updated daily to ensure coverage of the latest attack techniques.
How does Cymulate support detection engineering for SIEM, EDR, and XDR?
Cymulate validates detection responses and helps build custom detection rules for SIEM, EDR, and XDR platforms. The platform provides guidance for tuning and optimizing detection rules, improving mean time to detect and respond to threats.
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and selected scenarios. For a customized quote, schedule a demo with the Cymulate team via the demo page.
Use Cases & Benefits
Who can benefit from Cymulate's endpoint security validation?
Cymulate is ideal for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams across industries such as finance, healthcare, retail, media, transportation, and manufacturing. The platform supports organizations of all sizes seeking to enhance their endpoint security and overall cyber resilience.
What business impact can customers expect from using Cymulate?
Customers have reported an 81% reduction in cyber risk within four months, a 60% increase in team efficiency, 40X faster threat validation, a 30% improvement in threat prevention, and a 52% reduction in critical exposures. These outcomes demonstrate measurable improvements in security posture and operational efficiency. Read the Hertz Israel case study.
What pain points does Cymulate address for security teams?
Cymulate addresses pain points such as overwhelming threat volumes, lack of visibility, unclear prioritization, operational inefficiencies, fragmented tools, cloud complexity, and communication barriers. The platform provides continuous validation, evidence-based prioritization, and automation to help teams stay ahead of emerging risks.
How does Cymulate help different security personas?
Cymulate tailors its solutions to CISOs (providing metrics for investment justification), SecOps teams (automating validation and improving efficiency), red teams (scaling offensive testing), and vulnerability management teams (prioritizing exposures). Each persona benefits from features aligned to their specific challenges and goals.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its user-friendly and intuitive platform. Security professionals highlight its ease of deployment, actionable insights, and accessible support, making it a preferred choice for organizations seeking immediate value and improved communication of risks. Read customer quotes.
Where can I find Cymulate's latest news, events, and research?
Stay up-to-date with Cymulate through the blog, newsroom, and events & webinars pages. These resources cover the latest threats, research, company news, and upcoming events.
Where can I find a central hub for Cymulate's resources?
All of Cymulate's insights, thought leadership, and product information are available in the Resource Hub.
Competition & Comparison
How does Cymulate compare to other security validation platforms?
Cymulate stands out by offering a unified, AI-driven platform with continuous innovation, the largest attack simulation library, and features like automated mitigation and exposure prioritization. It is recognized for ease of use, measurable outcomes, and comprehensive coverage compared to competitors such as AttackIQ, Mandiant Security Validation, Pentera, Picus Security, SafeBreach, and Scythe. For detailed comparisons, visit the Why Cymulate page.
What makes Cymulate different from AttackIQ?
While AttackIQ focuses on automated security validation through attack simulation, Cymulate differentiates itself with a larger threat scenario library, AI-powered capabilities, and a focus on ease of use and workflow acceleration. Read more.
How does Cymulate compare to Mandiant Security Validation?
Mandiant Security Validation is one of the original BAS platforms but has seen less innovation in recent years. Cymulate is recognized for continuous innovation, AI and automation, and leadership in exposure management. Read more.
What are the differences between Cymulate and Pentera?
Pentera focuses on attack path validation, while Cymulate provides comprehensive exposure validation, covering the full kill chain and including cloud control validation. Read more.
How does Cymulate compare to Picus Security?
Picus Security is suitable for on-premise BAS needs but lacks the complete exposure validation platform Cymulate offers, including full kill chain coverage and cloud control validation. Read more.
What sets Cymulate apart from SafeBreach?
SafeBreach offers breach and attack simulation but lacks Cymulate's innovation, precision, and automation. Cymulate leads with AI-powered BAS, the largest attack library, and a full Continuous Threat Exposure Management (CTEM) solution. Read more.
How does Cymulate differ from Scythe?
Scythe is suitable for advanced red teams but lacks Cymulate's focus on actionable remediation and automated mitigation. Cymulate provides a more complete exposure validation platform with daily threat updates, no-code workflows, and vendor-specific remediation guidance. Read more.