Protect Your Network from Unauthorized Access: 6 Security Controls Every CISO Needs in 2026
Unauthorized access to corporate networks is one of the most critical cybersecurity risks facing organizations. Knowing how to prevent unauthorized access is now a top priority for CISOs, SOC analysts, IT security managers and compliance officers.
From stolen credentials to disgruntled insiders, incidents of unauthorized access are steadily rising. In fact, IBM’s X-Force observed that the use of stolen or compromised credentials to access accounts surged 71% in one year.
Insider threats are growing as well – 83% of organizations reported at least one insider attack in the last year .
These trends highlight that unauthorized access from threat actors (whether external hackers or malicious insiders) is a growing menace. The fallout from such intrusions can be devastating, leading to costly data breaches and compliance penalties.
What Is Unauthorized Access? (Definition & Examples)
Unauthorized access is the act of gaining access to a system, network, application or data without proper permission or authority. In other words, it’s when someone (or some program) accesses resources they are not allowed to. This can refer to external hackers breaching a network, or even insiders (employees or contractors) exceeding their authorized privileges.
Examples of unauthorized access include:
- Phishing attacks: A threat actor tricks an employee into revealing their username/password or clicks a malicious login link, thereby stealing credentials. The hacker then uses those stolen credentials to log in and access internal systems without authorization.
- Brute force and credential stuffing: Attackers use automated scripts to guess passwords (brute force) or try leaked password combos (credential stuffing) to break into accounts. If successful, the attacker gains unauthorized entry into the account.
- Exploiting vulnerabilities: Hackers exploit unpatched software vulnerabilities to bypass authentication or invade a network. For instance, a SQL injection or software exploit might give an outsider administrative access – a form of unauthorized access.
- Insider threats: A legitimate user abuses their access. This could be a malicious insider (like a disgruntled employee downloading a customer database they’re not supposed to) or an accidental insider who unknowingly misuses credentials. Even well-intentioned employees can cause unauthorized access by sharing passwords or leaving sessions unlocked for others to piggyback.
- Third-party access misuse: Partners or vendors with network access might exceed their permitted access. (For example, the infamous Target breach occurred when attackers stole a HVAC vendor’s credentials, allowing them unauthorized access into Target’s network.)
Common Causes of Unauthorized Access
Understanding why unauthorized access happens is crucial to preventing it. Most incidents stem from a mix of security gaps and human error—weak spots that attackers are quick to exploit. Unauthorized access typically results from the following factors:
Weak or stolen passwords
Weak passwords, password reuse and single-factor authentication remain leading causes of unauthorized access. Attackers can easily guess or crack simple credentials, and stolen login data is widely available through phishing or data breaches.
Without multi-factor authentication (MFA), a single stolen or brute-forced password can give an attacker full access. This is why credential compromise is one of the most common methods used by threat actors—it’s often the path of least resistance.
Misconfigured access controls
Security misconfigurations often lead to unintended exposure. Examples include publicly accessible cloud storage buckets, open firewall ports or overly broad user permissions. If an attacker compromises such an account, they inherit those excessive privileges.
Proper configuration of identity and access management (IAM), cloud permissions, and firewall rules is critical. Many breaches trace back to misconfigured resources that were never meant to be exposed in the first place.
Lack of network segmentation
A flat network—one with little or no internal segmentation—makes lateral movement easy for attackers. Once inside, a threat actor can move from one compromised device to many others.
Without segmentation by department, data sensitivity, or function, a single foothold can become a full-blown breach. In contrast, proper segmentation contains intrusions, limiting what areas an attacker can reach and protecting high-value assets.
Human error and social engineering
Human mistakes are behind the majority of unauthorized access incidents. Users might fall for phishing emails, unknowingly share credentials or approve fraudulent login requests.
Admins may assign too much access or forget to disable accounts for departed employees, leaving behind vulnerable “ghost” accounts.
Poor habits—like password sharing or writing passwords on sticky notes—also make unauthorized access easier. With 74% of breaches involving human error or misuse, user education and vigilance are essential. Social engineering exploits people as the weakest link in your security chain.
Overprivileged accounts
Users or service accounts often have more privileges than necessary, violating the principle of least privilege. If an overprivileged account is compromised, attackers gain access to more systems and data than they otherwise could.
Shared admin accounts, poor Privileged Access Management (PAM) practices, and lack of credential rotation worsen the problem. Without regular access reviews, excess privileges accumulate over time, creating a goldmine for attackers waiting to exploit them.
6 Effective Security Controls to Prevent Unauthorized Access
To effectively block unauthorized access and mitigate associated risks, organizations must implement layered security controls. No single measure is foolproof; a combination of preventative and detective strategies offers the best defense. Below are six essential security controls:
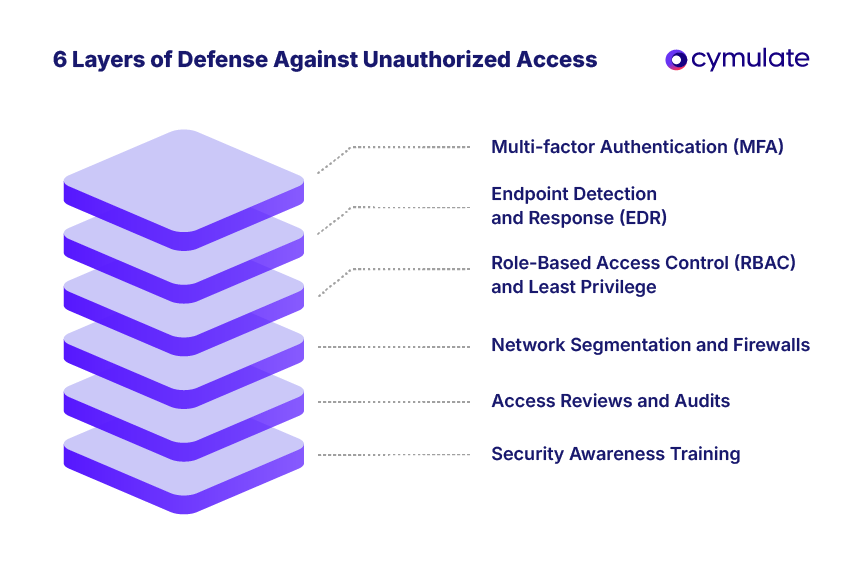
1. Multi-factor authentication (MFA)
MFA requires users to verify their identity with something beyond a password—like a mobile app approval or biometric. Even if an attacker obtains a password, they can’t log in without this second factor.
Microsoft reports MFA can prevent 99.9% of credential-based compromises. It’s crucial for sensitive systems, VPNs, and admin accounts. Use phishing-resistant MFA (like FIDO2 keys) where possible to strengthen defenses against stolen credentials.
2. Role-based access control (RBAC) & least privilege
RBAC assigns permissions based on job roles, reducing the risk of overprivileged accounts. Users should only have access necessary for their duties—nothing more.
This, combined with least privilege principles, limits damage if an account is compromised. Regular reviews of Identity and Access Management (IAM) roles and implementing Privileged Access Management (PAM) (such as just-in-time admin access and monitoring) are essential to minimize access abuse.
3. Network segmentation and internal firewalls
Dividing your network into isolated segments (e.g., separating servers, users, databases) limits lateral movement. An attacker who breaches one segment won’t easily reach others. Network segmentation aligns with Zero Trust, which assumes no internal access is automatically safe.
Enforce traffic restrictions between segments using firewalls and access controls. Tools like Network Access Control (NAC) can further limit which devices connect where. Regular firewall and penetration testing (e.g., Cymulate’s guide) helps validate your defenses and minimize breach impact.
4. Endpoint detection and response (EDR)
EDR tools monitor devices for suspicious activity, allowing rapid detection and response to threats. If attackers gain a foothold, EDR can flag behaviors like privilege escalation or unusual file access. These solutions are crucial for stopping attacks in progress and isolating compromised machines.
Pair EDR with Security Information and Event Management (SIEM) or Extended Detection and Response (XDR) tools for broader visibility. Strong endpoint security ensures threats that bypass perimeter defenses are still caught.
5. Regular access reviews and audits
Security isn't set-it-and-forget-it. Regular audits of user accounts and permissions help identify outdated access (e.g., ex-employees or role changes). Reviewing privileged access ensures only authorized personnel retain admin rights. Log audits can reveal failed logins, unusual access times, or other red flags.
Compliance frameworks like HIPAA, SOX, and PCI-DSS require these reviews as best practices. Auditing ensures that IAM and RBAC policies stay aligned with evolving roles and reduces opportunities for unauthorized access.
6. Security awareness and training
Human error is one of the top enablers of unauthorized access. Regular security awareness training helps employees recognize phishing attempts, social engineering tactics, and other threats. Simulated phishing exercises reinforce good habits.
Teach users not to share passwords or approve MFA prompts they didn’t initiate. A well-trained workforce adds a crucial human layer to your defense strategy, especially against tactics that bypass technical controls.
Consequences of Unauthorized Access
When unauthorized access occurs—whether from external attackers or insiders—the fallout can be severe and multifaceted, impacting everything from data integrity to business viability.
Unauthorized access often leads to the exposure or theft of sensitive data, including customer records, financial information, intellectual property, and employee details.
Such breaches may remain undetected for weeks, allowing attackers ample time to exfiltrate data. The consequences range from identity theft for individuals to competitive losses for businesses.
The average total cost of a breach reached $4.88 million in 2024, covering incident response, forensics, customer notifications, and service downtime. Costs escalate further if ransomware is involved, often requiring expensive remediation or ransom payments.
Regulatory fines and legal liabilities
Breaches resulting from unauthorized access frequently violate regulations like the GDPR and HIPAA. GDPR fines can reach up to €20 million or 4% of global turnover.
Organizations may also face class-action lawsuits and prolonged legal battles, as in the case of a company that paid $190 million in legal settlements post-breach. Healthcare-related breaches often incur HIPAA penalties of up to $1.5 million per category.
The public backlash following a breach can erode customer and investor trust. News coverage of compromised systems and mishandled incidents can lead to customer churn, diminished brand value, and long-term damage to loyalty. In some cases, it results in leadership changes and internal scrutiny.
How Cymulate Tests Your Defenses Against Unauthorized Access
Deploying controls like MFA, RBAC, and EDR is essential—but how can you be sure they actually work against real-world attacks? The Cymulate Exposure Validation Platform bridges that gap with continuous, automated testing that ensures your defenses are effective against unauthorized access attempts.
This helps verify whether existing controls (e.g., firewalls, MFA, EDR) detect and stop attacks. If a simulated breach succeeds undetected, security teams are alerted to address the gap before it’s exploited for real.
By scanning for misconfigurations, weak passwords, open ports and other vulnerabilities, Cymulate helps map your attack surface just like a hacker would. This proactive discovery lets teams remediate weaknesses before attackers can exploit them.
Breach and Attack Simulation (BAS)
The Cymulate BAS engine launches safe but realistic attack scenarios based on the MITRE ATT&CK® framework, testing how well your defenses respond to tactics like credential dumping, privilege escalation, or bypassing endpoint security. Regular simulations provide actionable insights, showing exactly where your security stands—and where it doesn’t.
Comprehensive Reporting and Guidance
After each simulation, Cymulate delivers clear reports highlighting which attacks succeeded, which were blocked, and how to fix any gaps. It offers remediation guidance, enabling continuous improvement and smarter prioritization of security efforts.
Cymulate acts as a real-time security coach, helping you answer vital questions like: “Are our defenses truly effective?” and “Where might an attacker still get through?” With Cymulate, you can continuously validate your security posture, mitigate the risk of unauthorized access, and stay prepared.