White House Roundtable: AI Innovation Is Redefining Cyber Defense Across Government and Industry

AI is no longer a future capability in cybersecurity. It is already reshaping how organizations defend against modern threats. As attackers leverage AI and automation to scale faster than ever, the gap between traditional proactive defenses and today’s threat landscape continues to widen.
At last month’s White House AI Cyber Defense Roundtable, I was fortunate to have voice in the discussion for how both U.S. government and industry must leverage autonomous, AI-driven solutions that can operate continuously in real time, deliver predictive insight and respond at machine speed.
Throughout my career, I’ve conducted threat-based cybersecurity assessments across the DoD, Intelligence Community and federal agencies using the MITRE ATT&CK framework. This work supported major acquisition decisions and enterprise cyber strategies, which advanced capabilities and strengthened cyber defense. I had a front-row view into the operational challenges across legacy, cloud, hybrid and multi-cloud environments. The experience was invaluable, and I saw the cyber landscape transform, specifically seeing how adversaries continue to evolve, in ways I could not have even imagined.
I have brought that perspective and experience into the private sector, advancing and increasing adoption of automated, proactive cyber defense solutions. I continue to see the same persistent critical gaps that traditional security approaches fail to address, which I see I am not alone. This shift is now being reinforced at the highest levels of U.S. policy, with the White House, NIST and CISA accelerating the secure adoption of AI. At the same time, government and industry collaboration is unprecedented and growing to operationalize AI-driven solutions and strengthen cyber resilience.
Key takeaways:
- U.S. policy is accelerating AI adoption in cybersecurity and engaging the private sector more
- Presidential administration recognizes the shift and seeks to modernize U.S. government security practices, specifically antiquated acquisition processes
- Adversarial exposure validation is a critical defense capability for all industries
- Traditional approaches to security validation without AI fall short
- Cymulate is advancing AI-driven cyber defense
- Organizations must adopt AI-powered security validation to keep pace with attacks
U.S. Federal Government and NIST Promote Secure AI for Cyber Defense
AI solutions enable organizations to process massive amounts of data in real time, rapidly identify subtle patterns of malicious activity and respond faster than human-led operations alone.
Recently published U.S. policies and frameworks, highlighted in Table 1, send a clear and consistent message that secure, innovative AI must be adopted rapidly to strengthen cyber defense across prevention, detection and response. These initiatives aren’t just encouraging AI adoption; they are actively working to significantly strengthen cyber defense capabilities and shift the favor back to defenders.
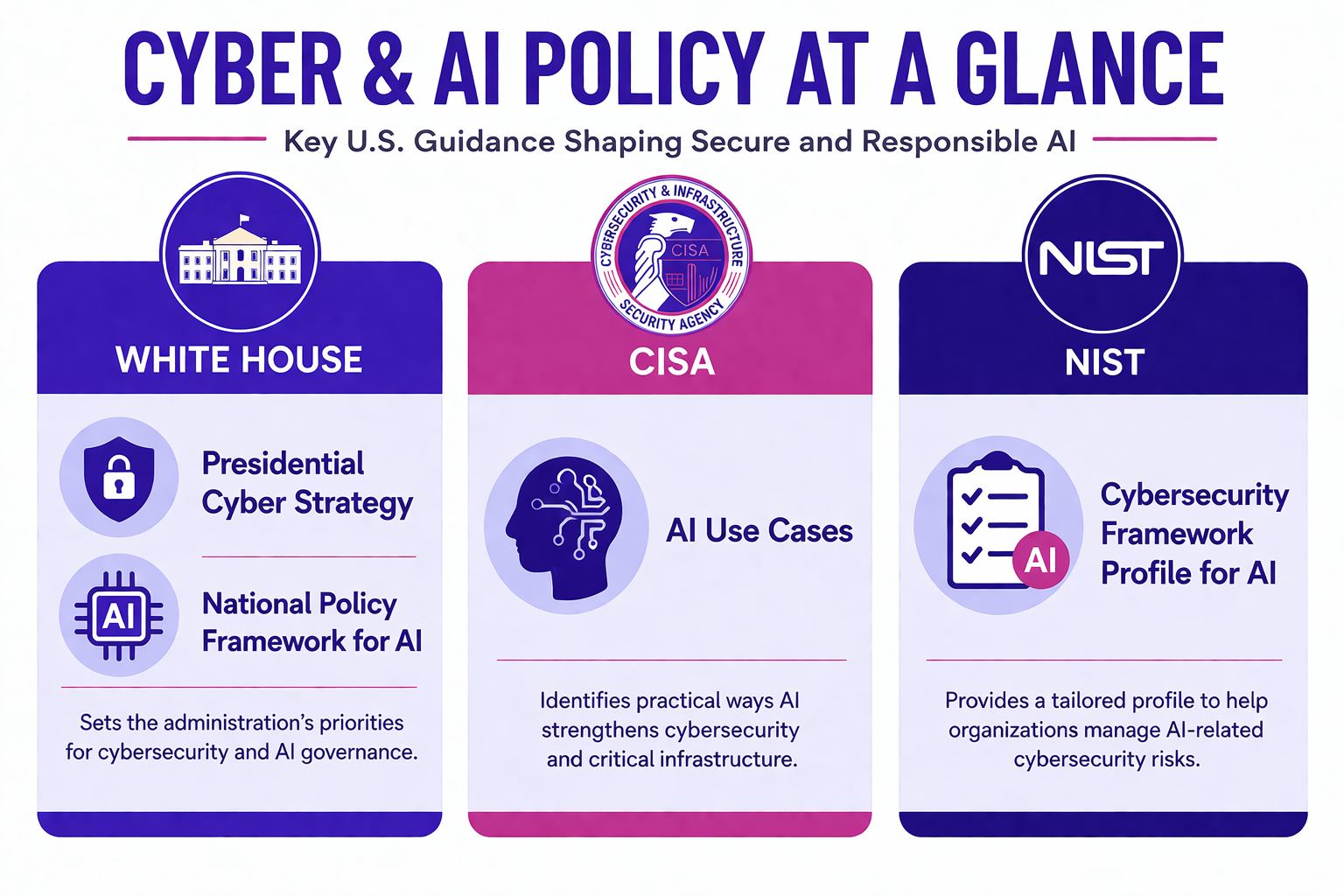
Given the volume of the policy memos coming out of D.C., it’s not always easy to stay on top of the most relevant points. To help, I’ve distilled the key insights that matter most for the purposes of this discussion in the table below.
| White House Presidential Cyber Strategy (March 2026) |
| • Implement AI-enabled cyber tools to detect, divert and deceive threat actors • Adopt and promote agentic AI in ways that securely scale network defense and disruption • Modernize procurement processes and remove barriers to entry so that the government can buy and use the best AI innovation technology to enhance cyber capabilities. |
| White House National Policy Framework for AI (March 2026) |
| • Communicated the importance on “removing barriers to innovation and accelerating deployment of AI applications” • Requested Congress establish regulatory sandboxes for AI applications that help “unleash American ingenuity and further American leadership in AI development and deployment” • Seeking to support development and deployment of sector-specific AI applications that follow existing regulations vs. creating a new federal rulemaking body to regulate AI |
| CISA Artificial Intelligence Use Cases |
| • Identified and evaluated innovative AI use cases to enhance cyber prevention and detection capabilities, such as: - Automated detection of PII - Confidence scoring in cybersecurity threat indicators - Malware reverse engineering - Critical infrastructure network anomaly detection - SOC anomaly detection |
| Cybersecurity Framework Profile for AI (NIST IR 8596) - Draft |
| • Provides an operational approach to both leverage AI in cyber defense and ensure AI is secure and reliable • Support organizations in their efforts to use AI to address cybersecurity challenges • Establishing a shared understanding of AI-related cybersecurity priorities and considerations organizations • Provides a set of common cybersecurity outcomes using AI for securing AI systems (secure), conducting AI-enabled cyber defense (defend) and thwarting AI-enabled attacks (thwart) |
Table 1: Summary of Recently Published U.S. Cybersecurity and AI Policies and Frameworks
AI-driven cyber defense solutions must be viewed as essential, not as just emerging capabilities, to restore the balance of power in favor of defenders.
White House AI Cyber Defense Roundtable
Cymulate participated in an invite-only, closed-door AI cyber defense roundtable at the White House, led by Michael Duffy, Federal Chief Information Officer. The session focused on how rapidly advancing AI capabilities can be leveraged to strengthen federal cybersecurity. Government and industry leaders came together to explore cyber challenges and practical, AI-driven use cases that enhance threat detection, deliver predictive insights and enable response at machine speed.
Along with Cymulate President Matt Handler, I represented Cymulate at the roundtable to provide industry perspectives to the discussion. It was refreshing to witness (and be a part of) senior government leaders on the panel directly asking the industry which cybersecurity solutions should be adopted as standard practice. In response, we highlighted our deep experience supporting the government’s use of breach and attack simulation, now evolved into adversarial exposure validation (AEV), to advance the cyber defense mission.
I was a part of federal programs that leveraged breach and attack simulation solutions to assess security capabilities and improve cyber defenses. I communicated to the panel that solutions like BAS/automated exposure validation with a threat-informed approach have been leveraged in the past; however, they have not been mandated and are still often treated as a “nice to have.” These proactive, threat-based solutions with advanced innovation and agentic AI must be mandated as a standard operational cyber defense solution to support the mission in shifting the balance in favor of the cyber defenders.
I also wanted to share additional important themes Matt and I identified throughout the discussion:
- Organizations are still grappling with persistent traditional cybersecurity challenge, which include limited visibility, siloed data, overwhelming alert volumes and reliance on manual processes, while attackers continue to innovate faster than defenders – the hope is AI will change the game.
- Data remains a central obstacle, highlighting that while centralized data lakes are ideal in theory, they are often impractical, leading to a growing need for federated, secure and accessible data approaches that can operate across modern, legacy and hybrid multi-cloud environments.
- It is critical that AI models and systems are secure and reliable; there were discussions on how to best apply identity and access management zero trust principles into AI solutions to ensure trust, attribution and integrity of data and actions.
- Private industry continues to face barriers to entering the market, limiting the federal government from achieving its cyber defense goals.
- The federal government is actively looking for ways to rapidly test, prototype and evaluate new solutions and modernize the procurement process.
This milestone event marks the first of many roundtables and collaborative engagements the government plans to hold with private industry to advance cyber defenses and achieve its broader cybersecurity strategy.
AEV solutions are critical, but traditional ones are not enough
Adversarial exposure validation (AEV), formerly known as breach and attack simulation (BAS), has evolved into a cornerstone capability in modern cybersecurity. What began as periodic, point-in-time testing has transformed into continuous, threat-informed validation aligned to real-world adversary behavior. Currently, over 60% of organizations have integrated BAS into their SOC operations, and nearly three-quarters report measurable improvements in incident response times. This rapid growth reflects a broader industry shift toward proactive, continuous security validation.
Adversarial exposure validation (AEV), recognized in Gartner® market guidance, is emerging as a critical capability for strengthening cyber resilience
However, despite this momentum, many aspects of these solutions still rely on human intervention, making it difficult to keep pace with increasingly advanced adversaries. As threats evolve at machine speed, traditional BAS and AEV approaches must advance and embrace agentic AI, advanced automation and autonomous capabilities to allow organizations to truly stay ahead.
How Cymulate is modernizing with advanced innovation and agentic AI and the value
Just like the federal government is recognizing the need to rapidly adopt AI and other advanced innovation to modernize cyber defenses, Cymulate also has recognized this and has invested heavily in incorporating innovation with AI and advanced automations into the platform.
The following Cymulate innovations with AI and advanced automation have significantly simplified automated offensive testing, lowered barriers to entry and makes continuous, threat-informed validation more accessible for organizations across all industries:
- AI-powered template creator: Within minutes, rapidly scope and run new threat attack simulations based on plain-text or threat intelligence URLs
- Auto-attack scenario mapping of existing detections: Automatically ingest existing detection rules and correlate to attacks to quickly validate detections are working for the latest threats
- Auto-generation of vendor-specific detection rules for gaps to quickly implement and re-test
- Auto mitigation pushes threat updates and recommended behavior rules to integrated security controls
As a sneak peek, Cymulate is investing heavily in the use of agentic AI to deliver autonomous execution of AEV across the end-to-end threat validation lifecycle – from maintaining context-aware organization environment and threat profiles, automatically running new attacks for the relevant threats, auto-pushing remediations for missed detections and prevention, continuously adapting and learning, and repeating this autonomous loop.
The risks and impacts of failing to adopt AI-driven and agentic AEV solutions
The consequences are clear if federal agencies and industry fail to adopt modern, agentic AI-driven cyber defense solutions. Adversaries will continue to outpace defenders, exploiting gaps faster than organizations can detect or respond. This imbalance will lead to more frequent and impactful breaches, loss of sensitive data, operational disruption and erosion of trust. Ultimately, mission success and business outcomes will be negatively impacted. Without evolving cyber defense capabilities (i.e., leveraging agentic AI and advanced innovation) to keep pace with the speed and sophistication of today’s threat landscape, organizations risk falling permanently behind in a fight that is only accelerating.
Don’t wait to connect with us
Reach out to us today to see how Cymulate is leveraging AI, automation and agentic innovation to modernize cyber defense. Learn how your organization can continuously validate security effectiveness and stay ahead of evolving threats.
Request a Live Demo
