Command and Control (C2)
Command and Control (C2) Attack: How Threat Actors Maintain Access and Control
Key insights
- C2 is the attacker’s lifeline: It provides persistence and remote control, enabling data theft, lateral movement, ransomware deployment, and botnet activity.
- Stealthy communications: C2 traffic often hides in normal protocols (HTTP/HTTPS, DNS, SMTP) and uses encryption to evade detection.
- Flexible architectures: Centralized, peer-to-peer, and third-party C2 setups determine resilience and detection difficulty.
- Well-known tools & malware: Cobalt Strike, Emotet, TrickBot, and RATs all rely on C2 to scale attacks and adapt.
- Detection requires layered defenses: Network monitoring, DNS analysis, egress controls, and host-based detection are essential, supported by threat intelligence and user awareness.
- Continuous validation is critical: Regular BAS and purple-team simulations (e.g., via Cymulate) help identify detection gaps and adapt to evolving C2 tactics.
Detecting C2 Attacks: The Threat Behind Data Exfiltration and Lateral Movement
A Command and Control (C2) attack is a cyberattack where attackers establish a covert communication channel between a compromised system and an attacker-controlled server. This backdoor channel allows the attacker to send commands to the infected machine and receive data from it, effectively remotely controlling the victim system.
In the context of the cyber kill chain (the stages of a cyberattack laid out by Lockheed Martin’s model), command-and-control is typically one of the final stages before the attacker achieves their end goals.
By the time a C2 channel is established, the attacker has already bypassed initial defenses and gained a foothold. This stage is critical because it provides persistence, the attacker can continually communicate with the compromised host to maintain access.
Through this C2 link, a threat actor can download additional malware, exfiltrate data, move laterally, or launch destructive actions at will. In other words, a successful C2 attack often leads directly to the “actions on objectives” phase, such as stealing data, deploying ransomware, conducting espionage or even using the victim machine as part of a botnet for further attacks.
Why does C2 matter so much? Because it’s the attacker’s lifeline into your environment. With an active C2 channel, attackers can persist undetected, continuously issue remote commands and harvest information over an extended period.
It enables them to coordinate compromised machines across an enterprise (or across the globe in the case of botnets) and orchestrate complex attacks like Distributed Denial of Service (DDoS) or mass data theft.
How C2 Attacks Work
A C2 attack usually unfolds after an initial compromise. First, the attacker infects a target system (for example, through a phishing email, malicious attachment, drive-by download, or exploiting a software vulnerability).
The malware or backdoor installed on the victim then initiates a connection to the attacker’s command-and-control server, essentially “phoning home” to let the attacker know the coast is clear. This is often done stealthily via a beaconing mechanism: the infected host sends out periodic signals to the C2 server, asking for instructions.
Once the C2 communication channel is established, the attacker can issue commands to the malware. The compromised host will execute these commands and send results or stolen data back to the C2 server, all without the legitimate user’s knowledge.

Communication Methods
Threat actors design C2 channels to blend in with normal network traffic. Many C2 tools use common application-layer protocols like HTTP or HTTPS web traffic, DNS queries or SMTP email as the transport, since these are typically allowed out of an organization’s network and don’t raise immediate suspicion.
The malware may connect to what appears to be an innocent website or make DNS lookups that actually carry encoded commands. By piggybacking on standard protocols and ports (80/443 for web, 53 for DNS, etc.), the C2 traffic hides in plain sight among legitimate traffic.
For example, an infected computer might repeatedly make an HTTP GET request to a seemingly benign URL that actually contains encrypted instructions from the attacker. Similarly, C2 instructions can be embedded in DNS request/response payloads (known as DNS tunneling).
The goal is to avoid obvious red flags; C2 traffic is often camouflaged as normal web browsing, DNS lookups or other routine communication. Modern C2 frameworks also often employ encryption (e.g. HTTPS or custom encrypted protocols) so that defenders can’t easily inspect the contents of the traffic.
Centralized vs. Decentralized C2
Different architectures exist for command-and-control infrastructure, each influencing ease of detection and disruption:
Centralized C2 architecture
In this classic model, all infected hosts (bots) communicate with a central server or small set of servers controlled by the attacker. It resembles a client-server setup, where the botmaster issues commands from one central C2 server to all bots.
Historically, infamous botnets used IRC chat servers or web servers for central C2. Attackers benefit from simplicity and direct control, but this structure introduces a single point of failure. Defenders identifying and blocking the IP or domain can disrupt the botnet's communications.
Attackers counteract this with redundant C2 servers, fast-flux DNS, proxies or redirectors to complicate takedowns.
They might host infrastructure on reputable cloud providers or compromised legitimate servers to evade detection. Still, centralized C2 remains relatively straightforward to detect due to consistent source communication. Modern malware often includes fallback servers or rotations to enhance resilience.
Peer-to-Peer (P2P) C2 architecture
In this decentralized model, there’s no single central server; infected hosts communicate among themselves. Each bot acts both as client and server, forming a mesh network that propagates commands similarly to torrent networks.
P2P C2 is challenging to dismantle because removing one node doesn't stop the others from communicating. Detection is tougher as traffic spreads across many nodes, blending with regular peer traffic.
Malware like TrickBot or Conficker historically demonstrated high resilience through this method. Hybrid models are common, initially using a central C2 and, if disrupted, switching to P2P schemes for redundancy.
“Random” or third-party C2 channels
The most evasive setups utilize legitimate services or diverse infrastructure instead of attacker-controlled servers. Attackers have leveraged public forums, cloud storage, social media, and CDNs to conceal C2 communications.
Commands can be hidden in social media comments, Google Docs files, or quietly retrieved from email inboxes. Techniques like domain generation algorithms (DGA) create constantly changing endpoints, making tracking difficult.
Regardless of architecture, the C2 phase of an attack is where the attacker maintains persistence and control. The longer this channel remains active without detection, the more freedom the attacker has to accomplish their objectives.
They might use the C2 channel to escalate privileges, conduct internal reconnaissance, spread to high-value systems and eventually exfiltrate data or trigger impact actions (like launching ransomware). Breaking the C2 link, via detection and blocking effectively cuts off the attacker’s hands. But doing so requires knowing what to look for, as we’ll explore in the detection section.
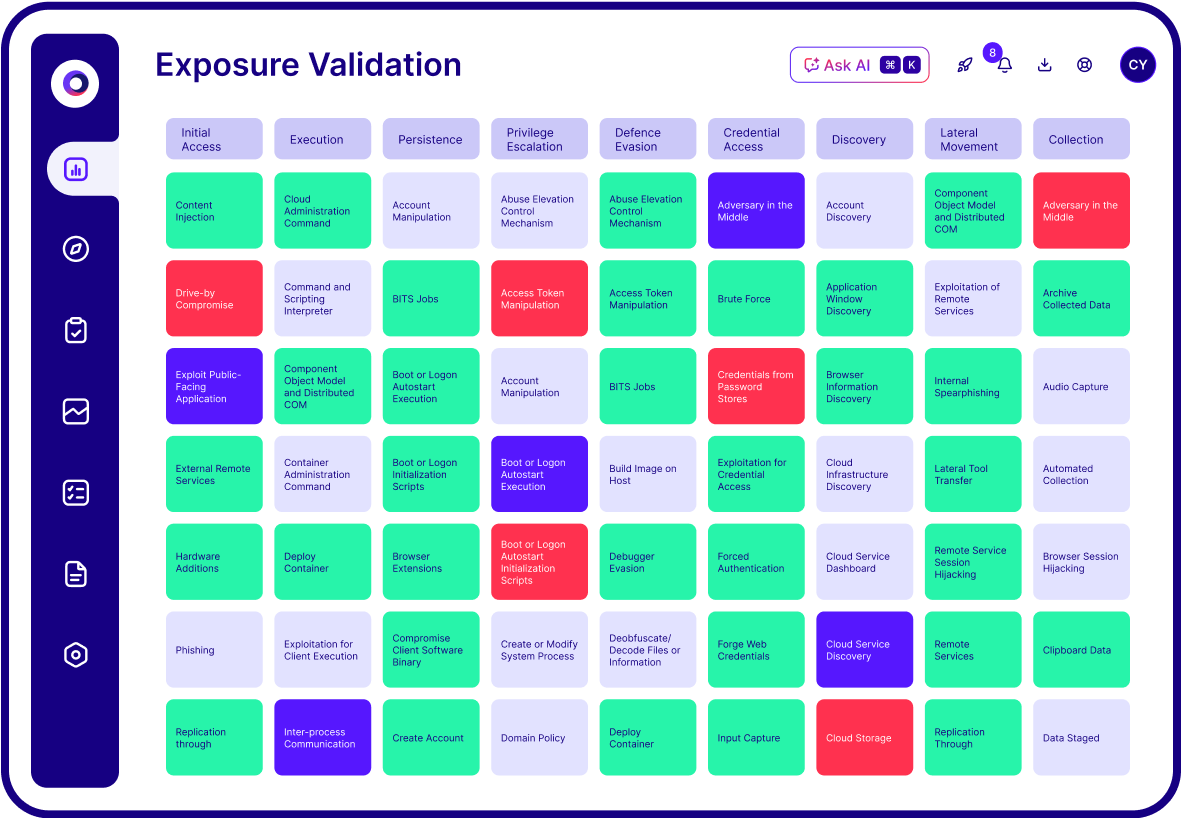
Common C2 Techniques (MITRE ATT&CK References)
The MITRE ATT&CK® framework categorizes the various techniques adversaries use for Command and Control. Here are a few of the common C2 techniques, along with their ATT&CK tactic IDs, that threat actors employ:
T1071 – Application Layer Protocol
Using standard application-layer protocols for C2 communications. Adversaries may craft their C2 traffic to use protocols like HTTP/S (web browsing), SMTP/IMAP (email), FTP or DNS so that it blends in with normal network traffic. Commands and responses are embedded within what looks like ordinary protocol communication.
T1095 – Non-Application Layer Protocol
Using lower-level network protocols for C2 that operate below the application layer (attack.mitre.org). This includes things like ICMP (Internet Control Message Protocol), which is normally used for pings and network diagnostics, or raw TCP/UDP sockets without a higher-level protocol.
Many organizations don’t closely monitor ICMP or unusual IP packet types, so malware can hide communications there.
T1219 – Remote Access Software
Abuse of legitimate remote access or administration tools to carry out C2. Instead of using custom malware protocols, the attacker leverages off-the-shelf remote desktop software (e.g. TeamViewer, AnyDesk, LogMeIn, VNC, etc.) as their C2 channel.
These tools are often allowed in environments or may appear as normal IT support activity. An adversary may install and secretly run such software on a victim host to get a graphical or command-line remote session as if they were an IT admin.
Because the software is legitimate (just used maliciously), it may not trigger antivirus and its traffic (often encrypted and to vendor cloud servers) may not be blocked. This technique is sometimes called “Living off the Land,” since it uses existing software to avoid deploying obvious malware.
T1105 – Ingress Tool Transfer
Transferring files or tools from outside into the compromised environment. Once inside, attackers often need to bring in additional tools, such as password dumpers, network scanners, or second-stage malware. Ingress Tool Transfer is the technique of using the C2 channel or another method to download/upload tools onto the victim system.
For instance, using the backdoor connection, the attacker might issue a command to download a script or executable from an external server (or directly transfer it through the C2 connection). Malware frequently does this to update itself or install supplementary components. This technique is essentially how an attack can pull in new payloads on demand.
Detecting it might involve catching an unknown binary being dropped on a host from an external source. On Windows, a common example is a malware using powershell.exe to download a file from the internet (a PowerShell one-liner invoking Invoke-WebRequest to fetch a malicious DLL, for example). On Linux, an example might be using curl or wget to fetch a tool from an attacker server. By transferring tools in, attackers increase their capabilities on the victim machine.
(MITRE ATT&CK includes many other C2 techniques as well, such as Encrypted Channels (T1573), Domain Fronting, Fallback Channels (T1008), Protocol Tunneling (T1572), and more. The ones above are some of the most frequently observed in real-world attacks.)
Each of these techniques highlights a different way that threat actors can maintain command and control over compromised systems. Defenders should be familiar with them because effective C2 detection requires knowing what “normal” vs “abnormal” looks like for each of these communication types.
C2 Malware and Tooling Examples
To better understand C2 attacks, let’s look at a few notable malware families and tools that heavily utilize command-and-control:
Cobalt Strike
Originally developed as a legitimate penetration testing suite, Cobalt Strike has a full-fledged C2 framework known as “Beacon” that has unfortunately become a favorite of threat actors. Cobalt Strike’s Beacon payload provides a robust, customizable C2 channel that attackers use to remotely control compromised systems.
Its traffic can be tailored with malleable C2 profiles to closely mimic normal activity (e.g. making Beacon communications look like innocuous HTTP traffic or using an encoded protocol over DNS). Attackers ranging from nation-state APT groups to ransomware gangs have leveraged Cobalt Strike because it’s stealthy and feature-rich.
Once they drop a Beacon on an infected machine, they can execute commands, move laterally, escalate privileges, and more, all through encrypted communications with a C2 team server.
Emotet
Initially a banking Trojan, Emotet evolved into a modular botnet known for robust C2 infrastructure. It connects infected PCs to numerous globally distributed C2 servers, retrieving commands via HTTP/HTTPS. Emotet continuously updates payloads, dynamically downloading new modules like credential stealers or spam tools.
It uses infected machines to launch mass spam campaigns and download additional malware (e.g., TrickBot or ransomware). Frequent C2 server changes help Emotet evade disruptions, even recovering after takedowns by law enforcement. Defenders typically detect Emotet by identifying characteristic network beacons and HTTP patterns.
TrickBot
TrickBot, a Trojan-turned-botnet, extensively employs C2 for modular delivery. It utilizes proxy layers, compromised IoT devices (e.g., routers), and non-standard ports for obfuscation. TrickBot also employs Domain Generation Algorithms (DGA), frequently changing domain names to evade detection.
Through its C2 channels, TrickBot downloads additional payloads like Ryuk or Conti ransomware, coordinating lateral movements and credential dumping. Its infrastructure takedowns in 2020 and 2021 highlighted C2’s critical role, as the malware cannot function without its C2 servers.
These examples demonstrate how essential C2 infrastructure is to malware operations. Tools like Cobalt Strike or botnets like Emotet and TrickBot rely heavily on C2 to maintain persistence, scale attacks, and adapt to defenses. Defenders can detect C2 activity through distinctive network behaviors and indicators like Beacon artifacts or unusual outbound traffic.
(Another prevalent example is remote access trojans (RATs) like PlugX, Remcos, or AgentTesla, which are basically malware that give attackers backdoor control and all rely on C2 channels. Even many ransomware attacks today involve an earlier C2 stage where the attackers had backdoor access to the network prior to deploying the ransomware payload. The C2 stage is often the linchpin that connects initial compromise to final impact.)
Detection and Prevention of C2 Activity
Detecting command-and-control activity is challenging but absolutely essential for cyber defense. Since C2 traffic is meant to hide among legitimate traffic, security teams need to use a combination of techniques and tools to spot the signals of beaconing or covert channels.

Here are some key tactics for C2 detection and prevention:
- Monitor network traffic and beaconing behavior: Establish a baseline of normal outbound traffic. C2 malware often shows regular beaconing intervals, unusual timing, or abnormal protocols and ports. Advanced Network Detection and Response (NDR) tools can identify these patterns, even in encrypted traffic.
- Analyze DNS for C2 indicators: Monitor DNS queries closely for anomalies like excessively long domains, frequent subdomain lookups or queries resolving to unusual external IP addresses. Implement DNS logging and firewalling to detect and block suspicious activity, including DNS tunneling and pseudo-random domain names.
- Use threat intelligence and signature-based detection: Regularly update threat intelligence feeds containing known malicious C2 indicators (blacklisted IPs, domains, file signatures). Intrusion detection/prevention systems (IDS/IPS) and Endpoint Detection and Response (EDR) solutions can alert on recognized signatures, unusual host behaviors, or misuse of legitimate tools like PowerShell. Although not infallible alone, combining signatures with behavioral analysis significantly improves detection.
- Network segmentation and egress controls: Implement strict network segmentation and egress filtering to limit potential C2 channels. Allow only necessary outbound connections; block all others by default. Use next-generation firewalls (NGFW) and web proxies to detect and prevent anomalies, forcing attackers into fewer, easily monitored channels. Proper segmentation reduces attackers’ lateral movement and restricts C2 establishment.
- Detect host indicators of C2 agents: Analyze hosts for suspicious behaviors, like unexpected command shells, registry modifications, scheduled tasks, or unusual network connections. Employ host-based intrusion detection, antivirus solutions, and memory analysis to identify C2 malware artifacts early, ideally at initial beaconing.
- User awareness and security hygiene: Educate users about phishing and social engineering to reduce initial compromise. Encourage timely reporting of suspicious activity. Keep systems patched, enforce multi-factor authentication, and maintain good credential hygiene to minimize C2 footholds.
- Regular testing of detection capabilities: Organizations should continuously validate their C2 detection methods using breach-and-attack simulations and purple-team exercises. Controlled simulations of outbound C2 traffic identify gaps in defenses, such as permissive firewall rules or inadequate DNS monitoring.
According to the Cymulate 2025 Threat Exposure Validation Impact Report, 95% of security leaders emphasize the importance of regularly testing threat detection to maintain a strong security posture.
Cymulate’s Role in Validating C2 Defense
Cymulate offers Breach & Attack Simulation and Purple Teaming capabilities within their Exposure Management Platform, allowing security teams to emulate real-world command-and-control (C2) attack scenarios safely.
Using controlled simulations mapped to the MITRE ATT&CK framework, Cymulate tests how effectively security controls (such as firewalls, IDS, and SIEM tools) detect various C2 techniques like HTTP-based channels, DNS exfiltration, or ICMP backdoors.
Continuous updates ensure scenarios reflect current threat actor behaviors, identifying security gaps early and clearly highlighting strengths and weaknesses through detailed MITRE-based reporting.
Continuous Testing and Purple Team Collaboration
Cymulate facilitates regular, automated testing rather than infrequent red team exercises, helping organizations keep pace with evolving attacker tactics. Security teams can schedule ongoing simulations to proactively identify and remediate detection gaps as new C2 methods emerge.
Additionally, Cymulate promotes effective collaboration between defensive (blue teams) and offensive testers (red teams or automated capabilities from Cymulate). This collaborative environment allows real-time practice detecting subtle C2 signals, significantly enhancing team preparedness.
Post-simulation reports provide actionable insights and recommendations, enabling swift improvements to defenses, ultimately strengthening resilience against real-world C2 attacks.
Continuous Validation
Another advantage of Cymulate is continuous validation. Rather than doing a one-off red team test once a year, Cymulate allows you to run automated tests on an ongoing basis. C2 defenses especially benefit from this, because threat actor behaviors evolve rapidly.
You can schedule periodic C2 simulations (daily, weekly, etc.) to continually challenge your SOC with benign “attacks.” If a new C2 technique emerges in the wild, (i.e., attackers start using a particular cloud storage service for secret communications) Cymulate can likely emulate that so you can test if your controls hold up.
This helps implement a proactive, continuous exposure management strategy to keep your organization resilient against C2 attacks.
Why C2 Matters in Today’s Cybersecurity World
Command and Control attacks remain one of the most significant threats to organizations because they allow threat actors to maintain hidden access and control over compromised systems. Once a C2 channel is established, attackers can operate almost as if they are an insider, issuing commands, stealing data, and spreading to other systems, all while blending in with normal traffic. This makes early detection and prevention of C2 activity paramount.
Security teams must be active in monitoring for the faint indicators of C2, from beaconing network patterns and odd protocol use to suspicious use of admin tools on endpoints.
Implementing strong network egress controls, up-to-date threat intelligence, and advanced behavior analytics are all key defenses against C2 attacks. And just as importantly, these defenses should be continuously validated.