Cymulate Discovers Hidden Malware Defense Evasion Technique
Cymulate discovers hidden malware defense evasion technique using Microsoft Terminal Services Client (MSTSC). Read more about the malware.
Featured Resources
View More Resources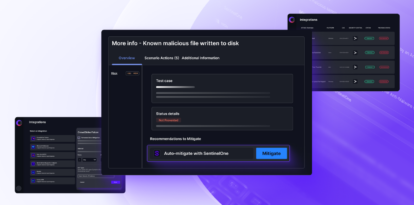
blog
Mitigation Hub Turns Findings into Fixes
Shiraz Arush Brinder, Senior Product ManagerAvigayil Stein, Senior Product Marketing Manager Security teams don’t need more dashboards or disconnected findings. They need a faster
Read More
blog
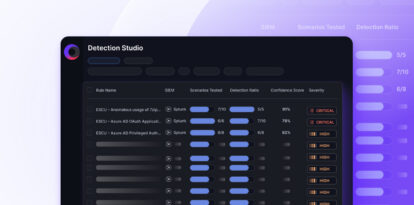
Detection Drift: Why Continuous Validation Matters
Detection drift breaks SIEM rules over time. Learn how continuous validation uncovers gaps before attackers do.
Read More

blog
The Truth About Your Security: Why We Built Cymulate Vero AI
Meet Cymulate Vero AI: the agentic AI system that validates threats, proves defenses and drives action.
Read More