SOC Automation: Optimize Your SOC Workflow
SOC Automation: Optimize Your SOC Workflow
Security operations centers (SOCs) are the nerve centers of modern cybersecurity, where potential threats are identified, assessed and neutralized around the clock. But as threat volumes surge and attack sophistication grows, many SOCs find themselves stuck in a reactive loop — overwhelmed by alert fatigue, resource bottlenecks and inconsistent response efforts.
Automation offers a way out, not by replacing human analysts, but by augmenting their capabilities, accelerating detection and ensuring that actions are rooted in validated security outcomes.
Let’s explore the ins and outs of SOC automation, why it’s relevant to your organization and how to integrate security validation in workflows with Cymulate.
Key highlights:
- Security operation center (SOC) automation is the use of technology to standardize and enhance core security workflows across detection, triage and response.
- Reducing alert noise improves incident response speed and analyst effectiveness, helping your team manage rising threat volumes without sacrificing accuracy.
- Automation should scale across hybrid and cloud environments to maintain consistency and control as infrastructure and attack surfaces evolve.
- Cymulate strengthens your automated security operations by validating workflows and responses against real-world attack scenarios, ensuring actions deliver measurable risk reduction rather than false confidence.
What is SOC automation?
SOC automation refers to the use of tools and workflows to automate repetitive, time-consuming tasks within the SOC, such as alert triage, data enrichment, threat intelligence ingestion and initial response actions.
This doesn’t mean handing over the SOC to machines. It means enhancing analysts’ ability to focus on high-value activities while reducing cognitive overload and burnout.
Contrary to what you might think, SOC automation does not eliminate jobs. There remains a critical need for human management and intervention when it comes to operating the SOC.
Instead, SOC automation empowers human analysts by taking over routine functions and enabling a faster, more consistent response. From auto-triaging a flood of low-level alerts to launching playbooks for common threats, automation helps streamline and scale SOC operations without compromising security rigor.
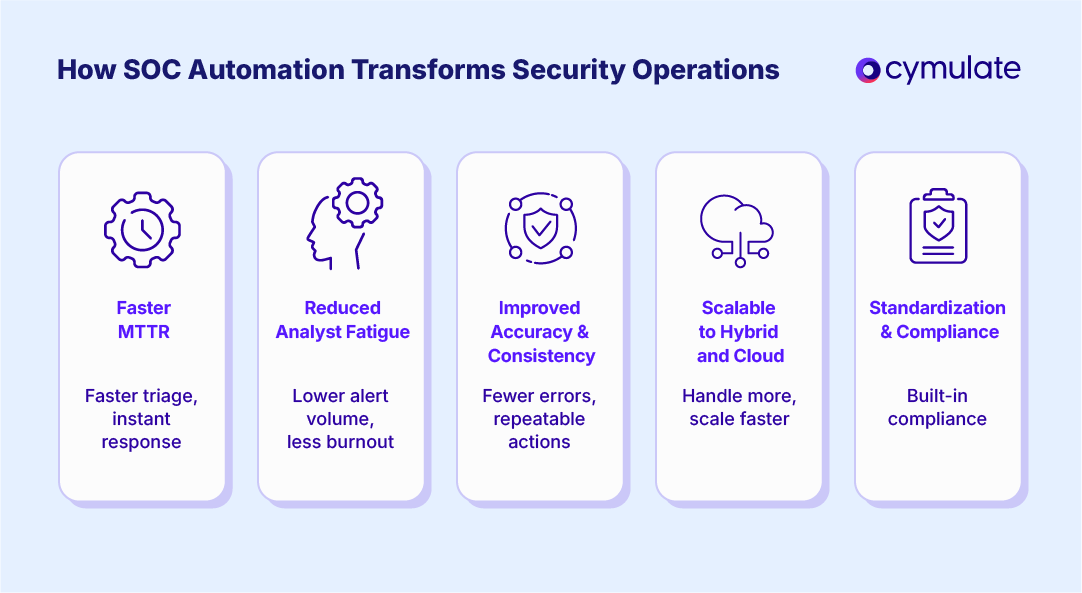
Key Benefits of SOC workflow automation
Implementing a strategy around SOC workflow automation can create tangible, lasting benefits for both your security environment and the people responsible for managing it, including:
Faster mean time to remediate (MTTR)
Automated SOC enables near-instant triage and response, allowing teams to reduce MTTR drastically and contain threats before they escalate. Automated workflows correlate alerts, prioritize severity and trigger predefined actions, shaving hours or even days off traditional manual efforts.
Reduced security analyst fatigue
With thousands of alerts per day, even the most experienced analysts face cognitive overload. Automating repetitive manual tasks and filtering false positives significantly reduces alert fatigue and lowers the risk of burnout. This workflow can translate to better morale, retention and performance across the SOC at a time when turnover and business continuity can often be issues.
Improved accuracy and consistency
Manual processes introduce variability and human error, especially as alert volumes increase and decisions are made under pressure. Automation enforces standardized workflows, ensuring responses are consistent, auditable and aligned with predefined logic across security incidents, analysts and environments.
Scalable to Hybrid and Cloud Environments
Modern SOC managers must monitor complex hybrid infrastructures. Automation provides the scalability and agility needed to keep up, enabling security teams to manage larger environments without linearly increasing headcount.
Selecting the best automation tools for enhancing security operations
Evaluating the best workflow automation tools for SOC teams via automation requires more than checking feature lists. Security teams need to assess whether tools will improve decision-making, response quality and resilience across real-world workflows. Key capabilities to look for include:
- Native integration with SIEM tools to ensure automation operates within existing workflows rather than relying on fragile connectors or custom scripts.
- Workflow visibility and decision transparency so analysts understand why automated actions are triggered and can maintain trust, accountability and security control.
- Flexibility to adapt workflows as threats, environments and priorities change, without constant reconfiguration or manual workarounds.
- Support for hybrid and cloud environments to ensure automation scales across modern infrastructure without introducing blind spots.
- Validation and continuous testing capabilities to confirm automated actions actually reduce risk and perform as expected under real-world attack conditions.
Understanding AI's role in SOC workflow automation
In SOC operations, AI is increasingly embedded in automation workflows to support the analysis, prioritization and actioning of alerts at scale. In practice, this shows up in several core areas:
- Generative AI for alert summarization: Providing high-level context, summaries and recommendations in human-readable form.
- Predictive threat modeling: Using historical and environmental data to predict where attacks are likely to occur.
- Decision support systems: Recommending the most effective containment or mitigation steps based on real-time threat intelligence.
As generative models improve, they will support analysts not just in detection but in communicating risk to stakeholders and automating decision-making at scale.
AI and ML are no longer experimental technologies in cybersecurity — they’re foundational to modern SIEM architectures, and deliver scalable, intelligent threat detection, enabling SOCs to operate efficiently in high-volume, high-stakes environments.
Use cases: Where SOC automation tools add the most value
For enterprises, automated SOC solutions deliver the most value when applied to repeatable, high-volume workflows where speed and consistency matter. The following use cases highlight where automation can meaningfully reduce MTTR and analyst load — and where validation is critical to ensure responses work as intended.
Streamlining detection
Detection automation focuses on correlating signals across SIEMs, EDRs and network telemetry to surface early-stage threats faster than manual analysis allows. By automatically identifying suspicious patterns across disparate data sources, SOC teams can reduce dwell time and detect attacks before they escalate into full incidents.
Cymulate Advantage:
By continuously validating detection logic, Cymulate ensures telemetry signals align with the most current threat behaviors so automation doesn’t miss evolving attack patterns.
Enhancing triage
Automated triage classifies, enriches and prioritizes alerts at scale, helping SOC teams separate genuine threats from background noise. This use case is critical for reducing alert fatigue, ensuring analysts focus their time on incidents that present real risk rather than chasing low-value or duplicate alerts.
Cymulate Advantage:
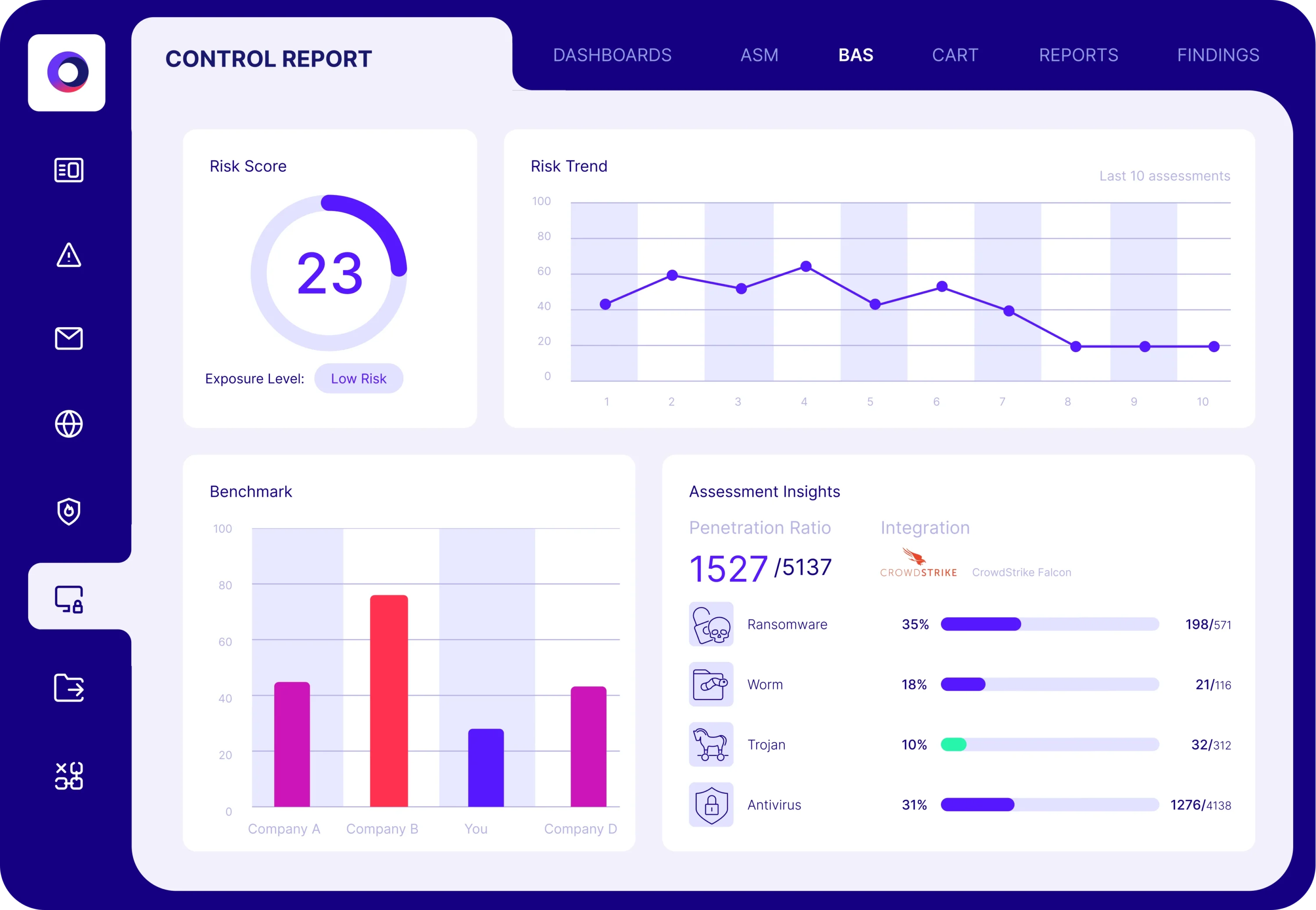
Test your triage workflows with Cymulate Breach and Attack Simulation (BAS) capabilities. Inject simulated threats and confirm your system triages and classifies them correctly.
Improving response
Response automation enables predefined actions — such as isolating endpoints, revoking credentials or blocking malicious traffic — to execute immediately once a threat is confirmed. When done correctly, this use case dramatically reduces mean time to respond and limits attacker movement during the most time-sensitive stages of an incident.
Cymulate Advantage:
Cymulate validates that automated responses are effective, not just triggered. This feedback loop ensures SOAR and SIEM playbooks result in actual threat mitigation, not just procedural execution.
Maintaining compliance
In compliance-driven environments, automation supports consistent execution and documentation of security controls across detection and response workflows. While not a substitute for governance, this use case helps SOC teams produce repeatable evidence, demonstrate control effectiveness and reduce the manual burden of audit preparation.
Cymulate Advantage:
The Cymulate continuous validation engine supports these efforts by providing auditors with concrete proof that detection and response workflows operate as designed.
How Cymulate helps optimize SOC workflows
Relying on cybersecurity automation tools for enterprise SOCs without validation is risky. Misconfigured rules, untested playbooks or blind reliance on machine-triggered actions can introduce new vulnerabilities or fail to stop real threats.
Cymulate bridges this gap by ensuring that every automated workflow, rule and playbook is stress-tested against real-world scenarios using these tactics:
- Security control validation: Test if automated actions — like endpoint isolation or credential resets — actually reduce risk across your specific environment.
- SIEM/SOAR optimization: Use Cymulate to simulate attacks and measure if your platforms detect and respond effectively.
- Continuous exposure validation: Map automation coverage to your actual risk exposure. If automated playbooks don’t align with real threat vectors, Cymulate flags the gaps.
Cymulate transforms automated SOC from a set-it-and-forget-it toolset into a living, validated system that adapts to emerging threats and shifting environments.
Validate security operations center automation with Cymulate
Security operations center automation is not about doing more — it’s about doing better. The most effective SOCs use automation not only to speed up response but to ensure every step in the process is validated, resilient and aligned with actual risk reduction.
Cymulate complements SOC automation tools efforts by validating whether detection and response mechanisms work as intended. The platform provides a continuous threat exposure management (CTEM) offering that puts proven threat validation at the forefront of your efforts.
Through continuous validation, Cymulate ensures that automation doesn’t just happen — it works. With our platform, SOC teams can:
- Simulate attacks
- Test playbooks
- Visualize responses to real-world threats
Book a demo today and explore how Cymulate can elevate your SOC automation strategy by ensuring that every alert triage, response playbook and detection rule is battle-tested and outcome-driven.
Frequently asked questions
No. SOC automation is designed to work alongside existing SIEM and SOAR platforms, not replace them. Effective automation enhances current workflows by orchestrating actions, enriching alerts and accelerating response while allowing teams to continue using the tools and processes they already rely on.
Automated SOC strategies execute predefined actions, while validation confirms that those actions actually reduce risk. Without validation, workflows may run successfully but fail to stop real attacks. Validation ensures detection logic, playbooks and automated responses perform as intended under real-world threat conditions.
Security operations center automation ROI is often reflected in reduced response times, fewer low-value alerts and more effective use of enterprise resources. Validation strengthens these gains by revealing where automated workflows fall short, allowing teams to focus effort on controls and processes that meaningfully reduce risk.



