Frequently Asked Questions
Product Overview & Purpose
What is Cymulate and what does it do?
Cymulate is a cybersecurity platform that enables organizations to proactively validate their defenses, identify vulnerabilities, and optimize their security posture. It provides continuous threat validation, exposure prioritization, and operational efficiency through automated attack simulations and actionable insights. Source
What is the primary purpose of Cymulate's platform?
The primary purpose of Cymulate's platform is to help organizations proactively validate their cybersecurity defenses, identify vulnerabilities, and improve their overall resilience against emerging threats. Source
How does Cymulate address specific cybersecurity needs?
Cymulate addresses cybersecurity needs by continuously simulating real-world threats, validating exploitability, prioritizing exposures, automating mitigation, and enabling collaboration across security teams. Source
What is Cymulate's vision and mission?
Cymulate's vision is to create a collaborative environment for lasting improvements in cybersecurity. Its mission is to transform cybersecurity practices by enabling organizations to proactively validate defenses, identify vulnerabilities, and optimize their security posture. Source
Features & Capabilities
What are the key features of Cymulate?
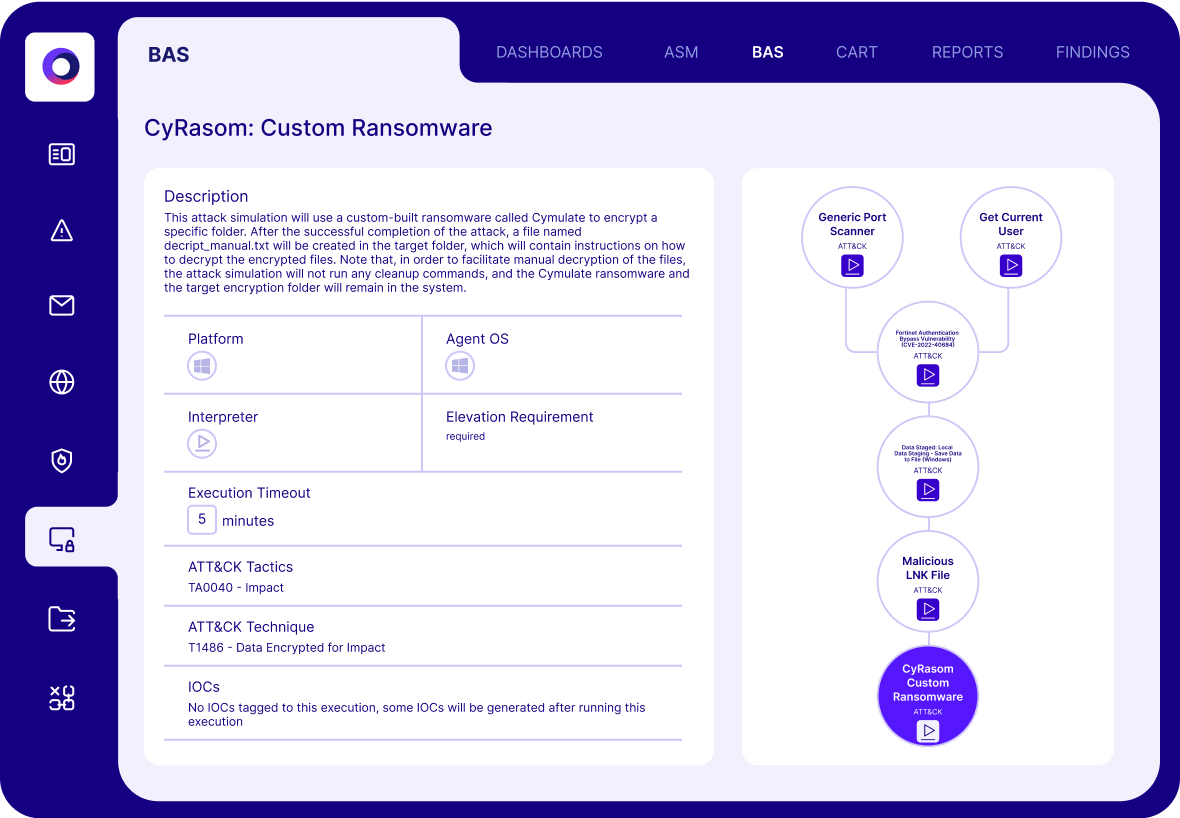
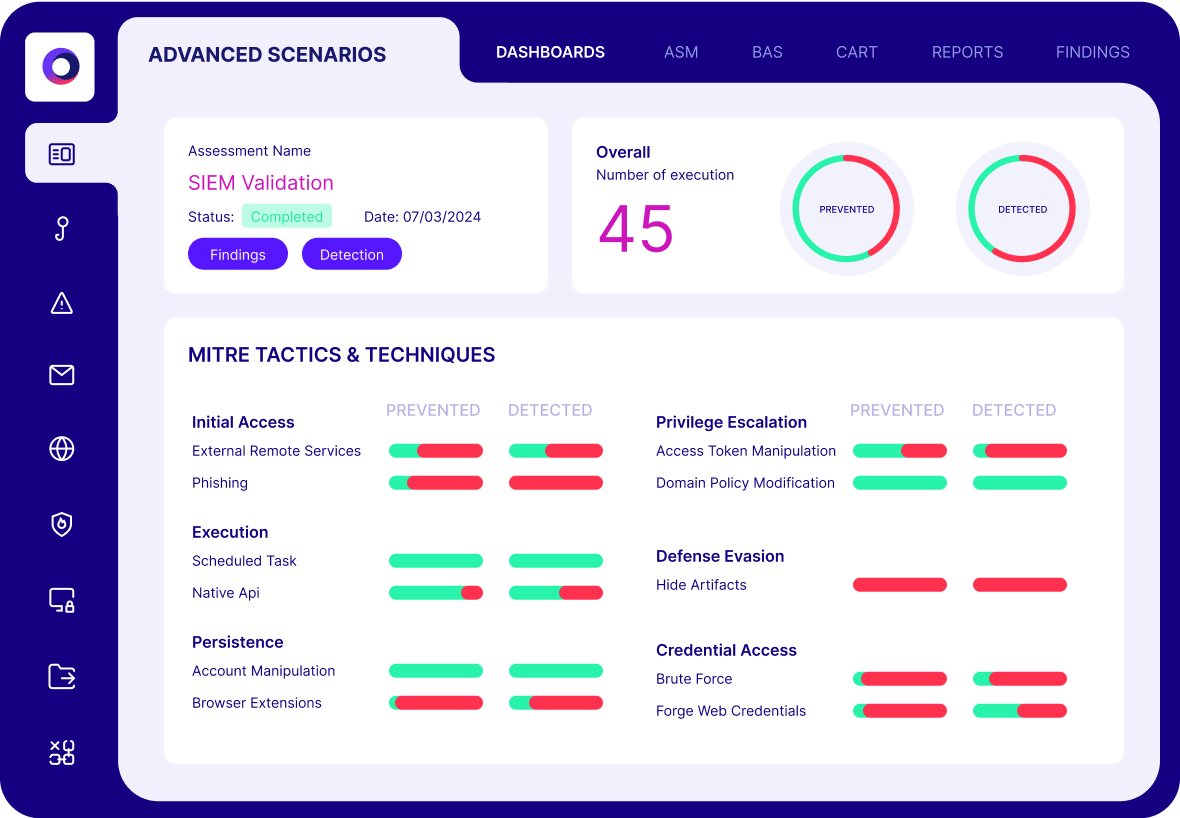
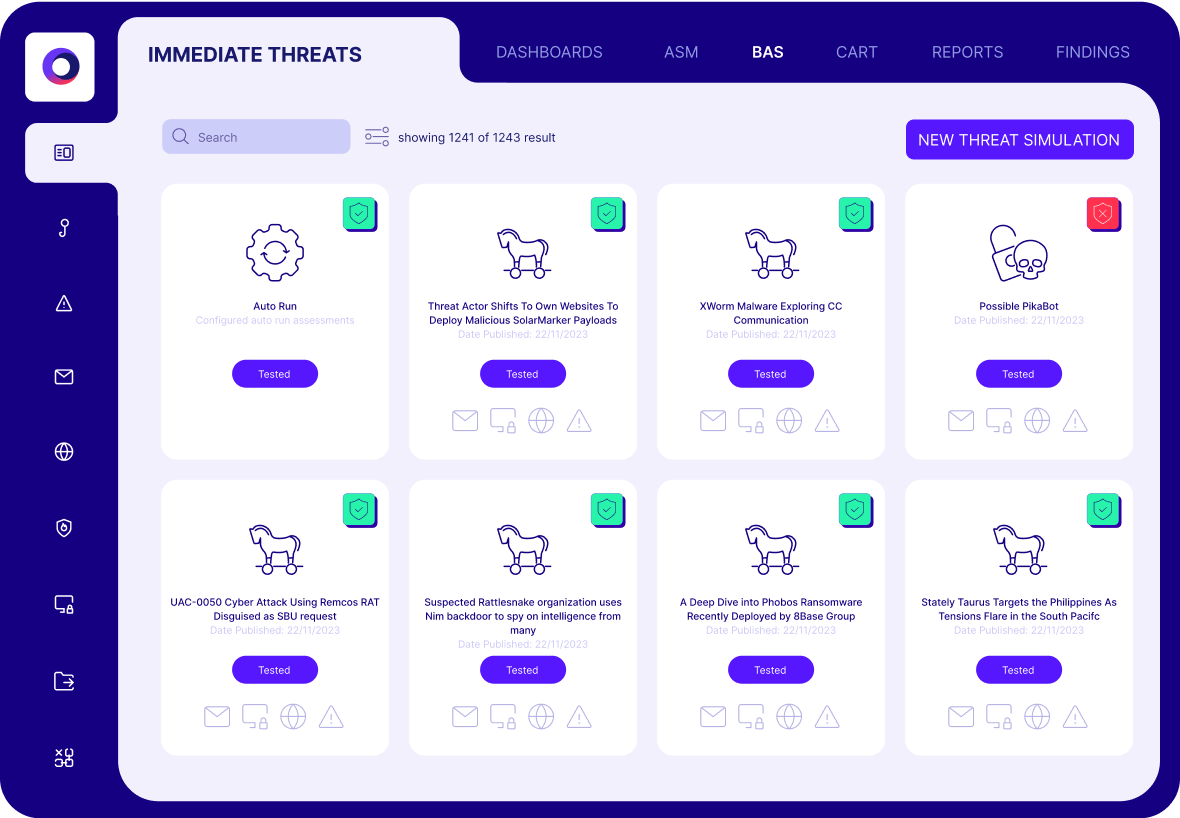
Cymulate offers continuous threat validation, a unified platform combining BAS, CART, and Exposure Analytics, attack path discovery, automated mitigation, AI-powered optimization, complete kill chain coverage, ease of use, and an extensive threat library with over 100,000 attack actions updated daily. Source
Does Cymulate support integrations with other security tools?
Yes, Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a full list, visit the Partnerships and Integrations page.
What is Cymulate's threat library and how is it updated?
Cymulate provides an advanced library of over 100,000 attack actions aligned to MITRE ATT&CK, with daily updates to ensure coverage of the latest threats. Source
How does Cymulate automate mitigation and remediation?
Cymulate integrates with security controls to push updates for immediate threat prevention and uses AI-powered optimization to prioritize remediation efforts. Source
What are the benefits of using Cymulate's unified platform?
The unified platform reduces complexity, improves efficiency, and enables collaboration across SecOps, Red Teams, and Vulnerability Management teams by combining multiple security validation tools into one solution. Source
How does Cymulate's AI-powered optimization work?
Cymulate uses machine learning to deliver actionable insights for prioritizing remediation efforts, helping organizations focus on high-risk vulnerabilities and optimize security controls. Source
What is Cymulate's approach to attack path discovery?
Cymulate identifies potential attack paths, privilege escalation, and lateral movement risks through automated testing, providing a holistic view of vulnerabilities across the attack lifecycle. Source
How does Cymulate support detection engineering?
Cymulate enables organizations to build, tune, and test SIEM, EDR, and XDR solutions to improve mean time to detect and respond to threats. Source
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, Red Teams, and Vulnerability Management teams in organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. Source
What business impact can customers expect from Cymulate?
Customers can achieve up to a 52% reduction in critical exposures, a 60% increase in team efficiency, an 81% reduction in cyber risk within four months, and save up to 60 hours per month in testing new threats. Source
What are some real-world case studies demonstrating Cymulate's value?
Hertz Israel reduced cyber risk by 81% in four months, a sustainable energy company scaled penetration testing cost-effectively, and Nemours Children's Health improved detection in hybrid and cloud environments. See more at the Cymulate Case Studies page.
How does Cymulate help with fragmented security tools?
Cymulate integrates exposure data and automates validation, providing a unified view of the security posture and addressing gaps caused by disconnected tools. Source
How does Cymulate address resource constraints in security teams?
Cymulate automates processes, improving efficiency and operational effectiveness, allowing security teams to focus on strategic initiatives rather than manual tasks. Source
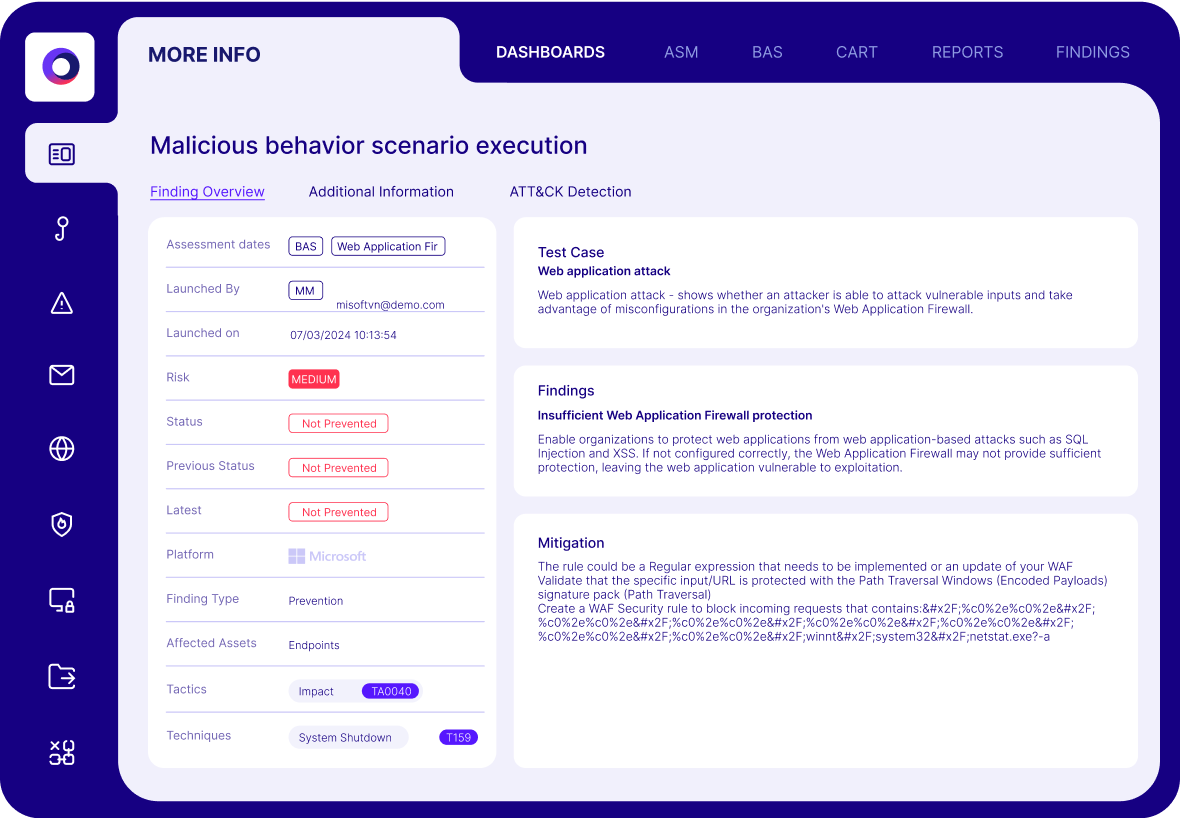
How does Cymulate improve risk prioritization?
Cymulate validates exploitability and ranks exposures based on prevention and detection capabilities, business context, and threat intelligence, helping organizations focus on the most critical vulnerabilities. Source
How does Cymulate help with cloud security validation?
Cymulate secures hybrid and cloud infrastructures through automated compliance and regulatory testing, increasing visibility and improving detection and response capabilities. Source
Competition & Comparison
How does Cymulate compare to Pentera?
Pentera is suitable for organizations seeking an on-premise BAS vendor. Cymulate offers a more complete exposure validation platform covering the full kill chain and cloud control validation. Source
How do Cymulate and Pentera approach attack path validation?
Both validate attack paths but use different methodologies: Cymulate's automated red teaming provides white box and grey box testing, while Pentera's automated pen testing provides white box and black box testing. Source
How does Cymulate's Attack Scenario creation workbench compare to Pentera's?
Cymulate offers a flexible workbench for building custom attack chains from over 100,000 actions and an AI attack planner. Pentera is a 'black box' with limited customization and does not allow users to build custom scenarios. Source
Who are Cymulate's main competitors?
Cymulate's main competitors include Pentera, AttackIQ, Mandiant Security Validation, Picus, and SafeBreach. Each has different strengths and approaches to security validation. Source
How does Cymulate compare to AttackIQ?
AttackIQ delivers automated security validation but does not match Cymulate's innovation, threat coverage, and ease of use. Cymulate offers the industry's leading threat scenario library and AI-powered capabilities. Source
How does Cymulate compare to Mandiant Security Validation?
Mandiant Security Validation is one of the original BAS platforms but has seen little innovation in recent years. Cymulate continually innovates, powers its platform with AI and automation, and has expanded into exposure management. Source
How does Cymulate compare to Picus?
Picus is suitable for organizations seeking an on-premise BAS vendor. Cymulate provides a more complete exposure validation platform with full kill chain and cloud control validation. Source
How does Cymulate compare to SafeBreach?
Cymulate outpaces SafeBreach with unmatched innovation, precision, and automation. It offers the industry's largest attack library, a full CTEM solution, and comprehensive exposure validation. Source
Pricing & Plans
What is Cymulate's pricing model?
Cymulate uses a subscription-based pricing model tailored to each organization's requirements. Pricing depends on the chosen package, number of assets, and scenarios selected. For a quote, schedule a demo.
Implementation & Ease of Use
How easy is it to implement Cymulate?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment. Source
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive interface, user-friendly dashboard, and actionable insights. Testimonials highlight its simplicity, quick implementation, and effective support. Source
What support resources are available for Cymulate users?
Cymulate offers email and chat support, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers and best practices. Source
Security & Compliance
What security and compliance certifications does Cymulate have?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating adherence to industry-leading security and privacy standards. Source
How does Cymulate ensure data security?
Cymulate ensures data security through encryption in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, and a tested disaster recovery plan. Source
Is Cymulate GDPR compliant?
Yes, Cymulate incorporates data protection by design and has a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO), to ensure GDPR compliance. Source
What application security measures does Cymulate use?
Cymulate follows a strict Secure Development Lifecycle (SDLC), conducts continuous vulnerability scanning, annual third-party penetration tests, and provides secure code training for developers. Source
What HR security policies does Cymulate enforce?
Cymulate enforces ongoing security awareness training, phishing tests, and comprehensive security policies for all employees. Source