Frequently Asked Questions
Product Information & Vulnerability Validation
What is CVE-2022-30190 (Follina) and how does it impact Microsoft Office users?
CVE-2022-30190, also known as Follina, is a high-severity remote code execution (RCE) vulnerability affecting Microsoft Office. It exploits the Microsoft Support Diagnostic Tool (MSDT) via the ms-msdt:// protocol, allowing attackers to execute malicious PowerShell code through macro-less Word documents, even in protected view. This vulnerability enables attackers to install programs, modify or delete data, or create new accounts within the user's rights. It impacts Office 2013, 2016, 2019, 2021, Office Pro Plus, and Office 365. Microsoft guidance recommends disabling the MSDT URL protocol to mitigate risk.
How can Cymulate help organizations validate their exposure to CVE-2022-30190?
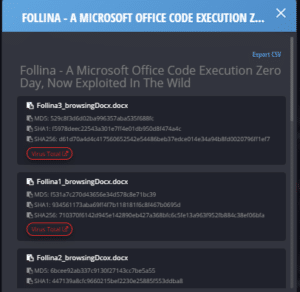
Cymulate provides a purple team scenario with a production-safe payload for validating resilience to CVE-2022-30190. Since June 2, 2022, Cymulate users can access this scenario, and since June 1, a dedicated Immediate Threat Intelligence kit for Follina is available. Cymulate enables organizations to test their defenses against this vulnerability and update their SIEM signature bank with multiple Indicators of Compromise (IoCs). Learn more about SIEM validation.
What is the recommended mitigation for CVE-2022-30190?
Microsoft recommends disabling the MSDT URL protocol to prevent attackers from exploiting CVE-2022-30190. Applying the published workarounds and validating their effectiveness is crucial for protection. See Microsoft guidance.
How does CVE-2022-30190 exploit macro-less Word documents?
The Follina vulnerability allows attackers to activate MSDT from regular .docx or .rtf documents without macros, and even when opened in protected view. It also works on shared .docs files, enabling malicious code execution via the ms-msdt protocol.
Which versions of Microsoft Office are affected by CVE-2022-30190?
CVE-2022-30190 affects Office 2013, 2016, 2019, 2021, Office Pro Plus, and Office 365. Any network user is a potential victim until mitigations are applied and validated.
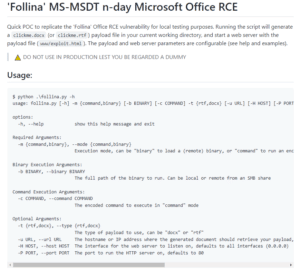
How can I locally test for the Follina Office RCE vulnerability?
A proof-of-concept (PoC) for locally testing CVE-2022-30190 is available on GitHub. This tool helps organizations verify their exposure to the vulnerability.
What resources does Cymulate offer for validating against CVE-2022-30190?
Cymulate offers a purple team scenario, Immediate Threat Intelligence kit, and SIEM signature updates for validating against CVE-2022-30190. These resources are accessible to all Cymulate users and help organizations stay ahead of emerging threats.
How quickly did Cymulate release validation scenarios for CVE-2022-30190?
Cymulate published a dedicated Immediate Threat Intelligence kit for Follina on June 1, 2022, and by June 2, users could access a purple team scenario with a production-safe payload for validation.
Can Cymulate help update SIEM signature banks with IoCs for CVE-2022-30190?
Yes, Cymulate users can update their SIEM signature banks with multiple Indicators of Compromise (IoCs) related to CVE-2022-30190, enhancing detection and response capabilities. Learn more.
What is the role of the ms-msdt protocol in CVE-2022-30190 exploitation?
The ms-msdt protocol enables remote execution of diagnostic tools via Microsoft Support. In CVE-2022-30190, attackers use this protocol to execute arbitrary PowerShell code through malicious documents, bypassing macro restrictions.
How does Cymulate Exposure Validation make advanced security testing easier?
Cymulate Exposure Validation centralizes custom attack chain building and advanced security testing in one platform, making it fast and easy for security teams to validate their defenses. Learn more.
What customer feedback has Cymulate received regarding ease of use?
Cymulate is consistently praised for its user-friendly and intuitive platform. Security professionals highlight its ease of implementation, actionable insights, and accessible support. For example, Raphael Ferreira, Cybersecurity Manager at Banco PAN, stated, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture." Read more testimonials.
How quickly can Cymulate be implemented in an organization?
Cymulate is designed for rapid implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment. Support is available via email and chat, and educational resources help optimize usage. Explore webinars.
What are the key capabilities of Cymulate's platform?
Cymulate offers continuous threat validation, attack path discovery, automated mitigation, detection engineering, complete kill chain coverage, and an extensive threat library with daily updates. These capabilities help organizations stay ahead of emerging risks and improve operational efficiency. Learn more.
What business impact can customers expect from using Cymulate?
Customers report an 81% reduction in cyber risk within four months, a 60% increase in operational efficiency, 40X faster threat validation, 30% improvement in threat prevention, and a 52% reduction in critical exposures. Cymulate delivers measurable ROI and improved detection accuracy. Read the Hertz Israel case study.
What pain points does Cymulate address for security teams?
Cymulate addresses overwhelming threat volumes, lack of visibility, unclear prioritization, operational inefficiencies, fragmented tools, cloud complexity, and communication barriers. It provides continuous threat validation, prioritization, improved resilience, collaboration, automation, and validated exposure scoring. Learn more.
How does Cymulate's exposure prioritization differ from CVSS scoring?
CVSS scores indicate severity but not exploitability. Cymulate validates which exposures are actively exploitable, enabling more effective and efficient remediation. Learn more.
Features & Capabilities
What integrations does Cymulate support?
Cymulate integrates with a wide range of technology partners, including Akamai Guardicore (Network Security Validation), AWS GuardDuty (Cloud Security Validation), BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, CrowdStrike Falcon, Cybereason, and more. For a complete list, visit our Partnerships and Integrations page.
How does Cymulate differ from similar products in the market?
Cymulate offers a unified, AI-driven platform integrating breach and attack simulation (BAS), continuous automated red teaming (CART), and exposure prioritization. It provides continuous threat validation, complete kill chain coverage, ease of use, and proven results. Competitors often focus on specific areas or lack Cymulate's innovation and threat coverage. See comparisons.
What certifications does Cymulate hold for security and compliance?
Cymulate is certified for SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. It is GDPR compliant and hosted in secure AWS data centers with strong encryption and high availability. Learn more about security at Cymulate.
How often does Cymulate update its threat simulation library?
Cymulate provides daily updates to its threat simulation library, ensuring customers stay ahead of emerging threats with the most advanced attack scenarios.
What educational resources does Cymulate provide?
Cymulate offers a Resource Hub, blog, glossary, webinars, and e-books covering cybersecurity best practices, threat validation, and product information. Visit the Resource Hub.
Pricing & Plans
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and scenarios selected. The subscription fee is non-refundable. For a quote, schedule a demo.
Competition & Comparison
How does Cymulate compare to AttackIQ?
AttackIQ delivers automated security validation but lacks Cymulate's innovation, threat coverage, and ease of use. Cymulate offers the industry's leading threat scenario library and AI-powered capabilities to streamline workflows. Read more.
How does Cymulate compare to Mandiant Security Validation?
Mandiant is an original BAS platform but has seen little innovation in recent years. Cymulate continually innovates with AI and automation, expanding into exposure management as a grid leader. Read more.
How does Cymulate compare to Pentera?
Pentera focuses on attack path validation but lacks Cymulate's depth for full defense assessment. Cymulate offers comprehensive exposure validation, covering the full kill chain and providing cloud control validation. Read more.
How does Cymulate compare to Picus Security?
Picus is suitable for on-premise BAS needs but lacks Cymulate's complete exposure validation platform. Cymulate covers the full kill chain and includes cloud control validation, making it a more comprehensive solution. Read more.
How does Cymulate compare to SafeBreach?
SafeBreach offers breach and attack simulation but lacks Cymulate's innovation, precision, and automation. Cymulate leads with AI-powered BAS, the largest attack library, and a full Continuous Threat Exposure Management (CTEM) solution. Read more.
How does Cymulate compare to Scythe?
Scythe is suitable for advanced red teams but lacks Cymulate's focus on actionable remediation and automated mitigation. Cymulate provides a more complete exposure validation platform with daily threat updates, no-code workflows, and vendor-specific remediation guidance. Read more.
Use Cases & Benefits
Who is the target audience for Cymulate's platform?
Cymulate serves CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams across industries such as finance, healthcare, retail, media, transportation, and manufacturing. Learn more about CISOs.
How does Cymulate address pain points for different personas?
Cymulate tailors solutions for CISOs (communication barriers, metrics), SecOps (operational inefficiencies, visibility), red teams (threat simulation scale), and vulnerability management (risk prioritization). Each persona benefits from quantifiable metrics, automation, and actionable insights. Learn more.
Technical Requirements & Support
What technical requirements are needed to deploy Cymulate?
Cymulate operates in agentless mode, requiring minimal infrastructure. Customers must provide necessary equipment and third-party software as per Cymulate’s prerequisites. The platform integrates seamlessly into existing workflows.
What support options does Cymulate provide?
Cymulate offers email support ([email protected]), real-time chat support, and access to a knowledge base with technical articles and videos. Educational resources include webinars and e-books. Explore webinars.
Resources & Thought Leadership
Where can I find Cymulate's blog and newsroom?
For the latest threats, research, and company news, visit our blog and our newsroom.
Where can I find resources like whitepapers, product info, and thought leadership articles?
All resources, including whitepapers, product information, and thought leadership articles, are available in our Resource Hub.
Where can I find a central hub for Cymulate's insights, thought leadership, and product information?
Visit our Resource Hub for all Cymulate insights, thought leadership, and product information.
Where can I find information on the Improper Attestation Validation vulnerability in Windows Admin Center?
Cymulate has published a detailed analysis of the Improper Attestation Validation vulnerability in Windows Admin Center. Read the blog post at this link.