Red Team vs Blue Team vs Purple Team in Cybersecurity

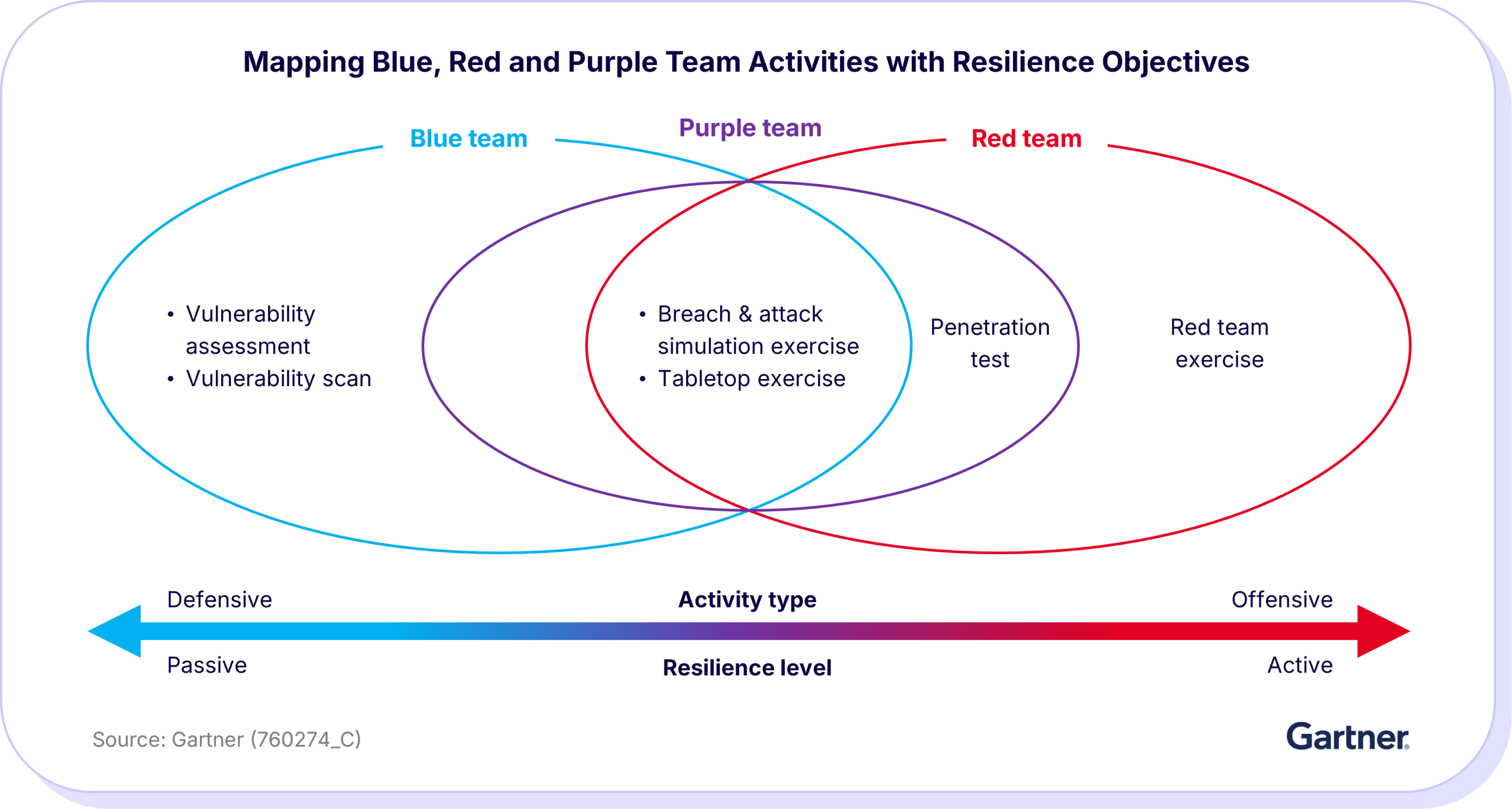
The cyber industry has adopted red, blue and purple to distinguish between the different responsibilities that contribute to an organization’s cyber resilience. Cybersecurity departments rely on their red, blue and purple teams to work in unison to identify vulnerabilities and security gaps, defend against attacks and optimize security measures.
Key takeaways:
- Red, blue and purple teams each play unique but complementary roles in strengthening an organization’s cyber resilience: offense, defense and collaboration.
- Shared challenges such as limited resources, rapidly evolving threats and communication gaps can hinder the effectiveness of all three teams.
- Breach and attack simulation (BAS) empowers all teams by automating testing, validating defenses and providing actionable remediation insights.
- The Cymulate platform helps understaffed teams keep pace with attackers while improving detection and response.
What is a red team in cybersecurity?
Red teams are composed of offensive security experts, such as ethical hackers, penetration testers and security researchers, who simulate real-world cyberattacks to identify vulnerabilities before malicious actors can exploit them.
The red team’s main objective is to:
- Uncover security weaknesses
- Test incident response
- Provide the blue team with actionable insights for improvements
To test an organization’s defenses comprehensively, a red team member adopts the mindset of attackers, using similar tactics such as social engineering, phishing, network infiltration and exploitation of known vulnerabilities.
What is a blue team in cybersecurity?
Blue teams are composed of defensive security professionals, such as security analysts, incident responders and network defenders, dedicated to protecting the organization from cyber threats.
The blue team exercises focus on defensive strategies and real-time threat mitigation by monitoring threats and detecting anomalies. Blue team’s objectives are:
- Protect data and internal systems
- Detect and respond to incidents
- Strengthen an organization’s security posture
Blue teams implement, validate and fine-tune their organizations’ security controls and security information and event management (SIEM) and improve their detection and response capabilities.
What is a purple team in cybersecurity?
Purple teams bridge the gap between red and blue teams, facilitating opportunities for collaboration to optimize security efforts. This team is not formal but more of an integration of blue and red teams during exercises to combine offensive and defensive strategies.
For this reason, it’s been said that blue and red teams are nouns while purple team is verb, as in purple teaming is what blue and red teams do when they collaborate on purple team exercises.
Purple team’s objectives are to:
- Improve overall cybersecurity posture
- Enhance collaboration
- Ensure continuous improvement
They are an excellent way for organizations to take a more proactive approach to security and bulk up defenses before an attack occurs.
What skills should red, blue and purple teams have?
Each team has specialized skills that enable it to excel in its role. Understanding these skill sets is key to building an effective cybersecurity strategy.
Red team skills
Red teams simulate attacks and think like adversaries. Key skills include:
- Penetration testing: Exploit vulnerabilities in networks, applications and systems.
- Social engineering: Craft phishing attacks, pretexting and other human-targeted attacks.
- Exploit development: Create custom scripts or tools to test security weaknesses.
- Threat modeling and attack planning: Analyze attack paths and simulate real-world scenarios.
- Advanced knowledge of IT and security: Deep understanding of operating systems, networks, cloud environments and applications.
- Creativity and problem-solving: Ability to anticipate defender actions and bypass security controls.
Blue team skills
Blue teams defend the organization and respond to threats. Key skills include:
- Monitoring and detection: Use SIEM, IDS/IPS and EDR tools to identify anomalies.
- Incident response: Investigate, contain and remediate security incidents quickly.
- Threat hunting: Proactively search for hidden threats in networks and systems.
- Vulnerability assessment and management: Identify and remediate security weaknesses.
- Knowledge of security frameworks: Familiarity with NIST, ISO, MITRE ATT&CK and compliance standards.
- Analytical thinking: Interpret logs, alerts and security data to make informed decisions.
Purple team skills
Purple teams bridge the gap between red and blue teams, requiring hybrid skills:
- Offensive and defensive knowledge: Understand both attack strategies and defense mechanisms.
- Collaboration and communication: Facilitate knowledge sharing between red and blue teams.
- Data analysis and reporting: Translate attack results into actionable insights for defenders.
- Process improvement: Identify gaps in security workflows and optimize testing processes.
- Strategic thinking: Focus on continuous improvement of the organization’s overall security posture.
- Tool integration: Manage platforms that unify testing, monitoring and reporting for maximum efficiency.
Differences among the red team, blue team and purple team
Each team has its own area of responsibility and main tasks to accomplish. Here’s how purple team vs. red team vs. blue team in cybersecurity compares:
| Difference | Red team | Blue team | Purple team |
| Primary goal | Test security by simulating attacks, find vulnerabilities | Protect the organization, detect and respond to attacks | Integrate offensive and defensive activities to improve security posture |
| Mindset and approach | Offensive, proactive, attacker mindset | Defensive, reactive, risk-averse | Collaborative, continuous improvement, hybrid mindset |
| Key responsibilities | Ethical hacking, penetration testing, exploit discovery, social engineering | Monitor systems, respond to incidents, hunt threats, maintain security | Coordinate Red & Blue activities, analyze results, recommend improvements |
| Typical activities | Pen testing, phishing campaigns, malware simulation, breach exercises | Log monitoring, alert analysis, incident response, vulnerability assessment | Run joint exercises, analyze attack simulations, optimize detection and mitigation |
| Tools and techniques | Metasploit, Burp Suite, exploit frameworks, social engineering toolkits | SIEM, IDS/IPS, EDR, firewalls, threat intelligence feeds | Combination of Red and Blue tools, dashboards, collaboration platforms |
| Metrics of success | Number of vulnerabilities found, time to breach, attack surface coverage, success rate of attacks | Mean Time to Detect (MTTD), Mean Time to Respond (MTTR), incidents contained, reduced false positives | Improvement in Blue team detection, reduction in recurring vulnerabilities, faster patching, security process maturity |
| Reporting focus | Attack findings, vulnerabilities discovered | Incident reports, mitigation measures | Lessons learned, joint insights, actionable recommendations |
| Frequency of operations | Periodic / scheduled exercises | Continuous | Continuous + post-exercise integration |
| Skill focus | Offensive security, exploitation, creativity | Defensive security, monitoring, analysis | Hybrid: understands both offense and defense, facilitates knowledge sharing |
| Outcome and value | Exposure of weaknesses, test of defenses | Minimized risk and damage from attacks | Strengthened overall security posture through collaboration and feedback |
Shared challenges of red teams, blue teams and purple teams
While each team has its own responsibilities, some of their challenges overlap.
1. Limited resources
According to a US Government Accountability Office (GAO) report, security teams are often understaffed and struggle to keep up with their specific responsibilities:
- Blue teams that are insufficiently staffed struggle to keep up with the volume of alerts and incidents.
- Red teams that don’t have enough manpower will be limited in the scope and depth of their testing.
- If blue and red teams are understaffed, their limitations will also impact how much time they can invest in purple team activities.
2. Rapidly evolving threat landscape
Many organizations use threat feeds so that red, blue and purple teams can stay on top of emergent threats to fulfill their different responsibilities. However, due to information overload, security teams often can’t determine the most dangerous threats to their organization, putting them at risk.
3. Communication gaps
Blue and red teams need effective communication to improve defenses, but because each team has different objectives, this can lead to conflicting priorities. For example, red teams may create extensive reports detailing security weaknesses, while blue teams require clear, actionable items to reduce risk. Typically, purple teams would bridge this communication gap by aligning both teams' goals.
How red, blue and purple teams can solve their problems
Because the blue, red and purple teams share challenges, they can also find value in the same solution, such as a breach and attack simulation (BAS) platform. BAS continuously tests the effectiveness of an organization's security posture by simulating real-world cyberattacks. It helps organizations take the attacker’s perspective by identifying vulnerabilities and gaps, validating security controls and ensuring their defenses can withstand real threats.
1. Limited resources → Automation
BAS provides automation that significantly benefits understaffed red, blue and purple teams by enhancing their productivity, efficiency and effectiveness in testing and validating security measures. Here’s how it impacts all three teams:
Red teams can:
- Automate creation and execution of tests
- Scale testing across IT environments
- Reduce manual effort in threat simulations
Blue teams can:
- Run risk assessments independently to validate controls
- Get immediate feedback on vulnerabilities
- Receive practical remediation guidance
- Prepare for audits without relying on red team reruns
Purple teams can:
- Unify red and blue team activity
- Enable collaborative simulations and analysis
- Share insights to strengthen the overall security posture
2. Rapidly evolving threat landscape → Immediate threats assessments
BAS platforms provide up-to-date simulations and insights on emerging threats:
- Daily updates with the latest attack simulations.
- Each assessment uses the exact IOCs of that threat. Threat and simulation updates include insights into threat actors, attack vectors, techniques mapped to MITRE ATT&CK and indicators of compromise.
- Red teams can automate simulations for new threats, saving time and effort.
- Blue teams can easily digest results, focus remediation efforts and rerun assessments to ensure protection.
- Purple teams can enhance collaboration by bridging blue and red activities, fostering continuous improvement.
3. Communication gaps → Reporting and remediation guidance
BAS enhances clarity, collaboration and actionable insights by:
- Providing clear reports with practical remediation guidance.
- Facilitating fact-based discussions about vulnerabilities and security improvements.
- Aligning all teams on priorities and next steps, reducing miscommunication.
- Enabling teams to act faster and coordinate more effectively.
Take a proactive approach to cybersecurity with Cymulate
The Cymulate Exposure Management Platform provides the automation, immediate threat intelligence and reporting:
- It’s simple to deploy and use
- It offers comprehensive coverage
- It’s highly customizable
Cymulate enables red teams and blue teams to work together and integrate offensive and defensive security measures, creating a purple team function. Continuous security validation encourages organizations to take a more proactive approach to security to provide better resilience.
If you’re interested in seeing how Cymulate can help your red, blue and purple teams increase collaboration, schedule a demo here.