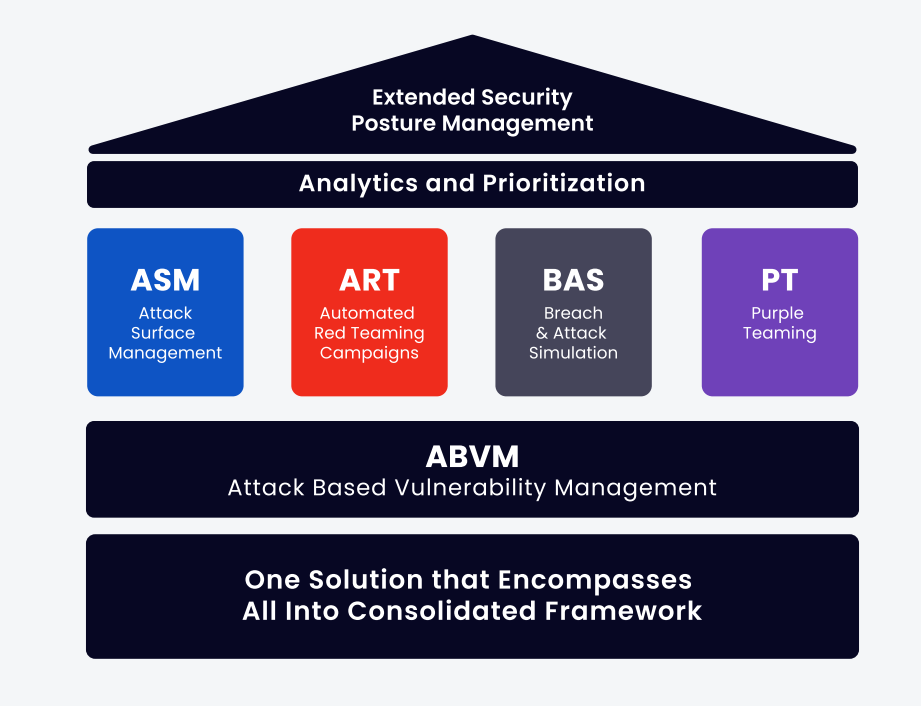
Extended Security Posture Management (XSPM) for Comprehensive Validation Coverage
Extended Security Posture Management (XSPM) provides a comprehensive set of validation tools an organization needs to provide ongoing management of its cybersecurity posture. It is the only platform to automate and combine purple teaming and red teaming methodologies that answer customer concerns: Are my security technologies and processes effectively protecting the organization? and How can my organization be breached?

Delivering Comprehensive Security and Business Validation with XSPM
The cybersecurity industry is based on the principle that hackers are usually one step ahead and defenders are a step behind. To try and flip it around, businesses took steps to understand where their security posture is weak and vulnerable. For instance, automated testing in the application development lifecycle (continuous but not comprehensive) or penetration testing services (comprehensive but not continuous).
With its XSPM platform, Cymulate helps companies stay one step ahead of cyber attackers. It mimics the same myriad of attack strategies and tools that malicious hackers and cybercriminals use, allowing businesses to assess their true preparedness to handle cybersecurity threats effectively. Once discovered, it provides specific recommendations for remediation and both technical and executive reporting.
Since it’s an on-demand SaaS-based platform, it lets users run simulations 24/7 from anywhere, significantly shortening the testing cycles and speeding up the time to remediation.
The capabilities and functions of the Cymulate XSPM platform include:
- The ability to test all phases of an attack: pre-exploitation, exploitation, and post-exploitation
- Full coverage of the MITRE ATT&CK framework
- On-demand testing in addition to automation for continued testing and monitoring
- Effective but safe testing that avoids disrupting production systems
- Test individual controls, as well as how those controls work together
- Continuous, automatic updates, including pinpoint simulations of emerging threats
- Full technical reporting, native SOAR and GRC integration, CSV output for ingestion in other tools, and executive reporting for non-technical professionals
Offensive Testing Methods Used in XSPM
To truly understand how an adversary might breach a system, organizations need to adopt a range of offensive testing techniques. These methods emulate different stages of real-world cyberattacks and help assess whether security defenses can withstand them. Each approach plays a unique role, and when combined within the XSPM platform, they offer a comprehensive and continuous view of an organization’s security posture.
- Attack Surface Management (ASM) looks for exposed and accessible digital assets or company information. Essentially, this technology emulates an adversary's reconnaissance stage.
- Continuous Automated Red Teaming (CART) – end-to-end penetration campaigns that point to the attack paths through which an organization might be breached.
- Breach and Attack Simulation (BAS) – simulates attacks against each and every security control in order to validate its efficacy.
- Purple Teaming - collaborative exercises between red and blue teams to simulate real-world attack scenarios and improve detection and response capabilities
Time and time again we hear from security professionals and executives that different teams utilize different approaches and a full-stack solution combining those approaches is really what they need to get a holistic view of the current state of the security posture.
Red Teams focus on automating penetration campaigns end to end and Purple Teams on customizing attacks and complex attack scenarios. Many vendors focus on one or two of the above and provide their customers only with a partial picture.
Exposure Management: The Future of Extended Security Posture Management
Comprehensive, end-to-end validation is essential, but validation alone often results in another long list of unresolved action items. This is where exposure management takes center stage. By correlating data from security validation with vulnerability insights, exposure management provides context-driven prioritization, turning raw findings into actionable remediation steps. Modern exposure management platforms go beyond traditional BAS and Continuous Security Validation tools, offering analytics, intuitive dashboards, automation, and integration to ensure that security teams can act effectively.
Cymulate’s exposure management approach unifies continuous testing, contextual risk scoring, and prioritization. By connecting to vulnerability scanners and mapping results against real-world attack paths, the platform highlights which exposures matter most to the business. This enables security leaders to have fact-based discussions, allocate resources efficiently, and strengthen resilience.
When adopting exposure management, make sure that your solution empowers you to:
- Assess your current exposure to establish a clear baseline
- Prioritize and remediate based on business impact
- Optimize investments across technology, people, and processes
- Prevent drift and continuously validate improvements
- Eliminate assumptions by proving security effectiveness end-to-end