Adversary Emulation
Adversary Emulation with the MITRE ATT&CK® Framework: Your Guide to Proactive Defense Adversary Emulation
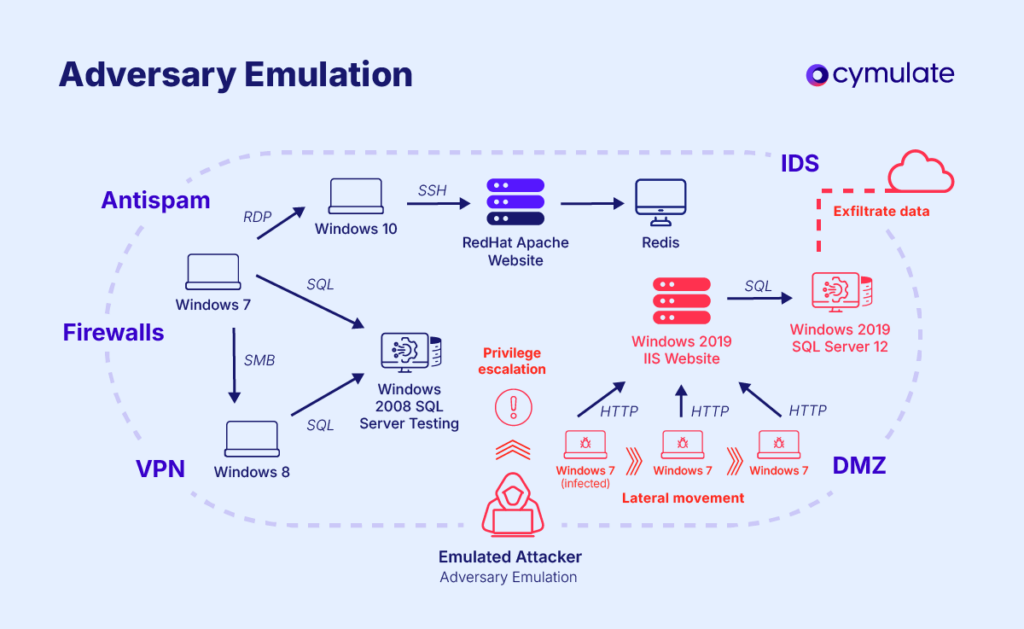
Adversary emulation is a proactive cybersecurity practice that replicates the tactics, techniques and procedures (TTPs) used by real-world threat actors. It plays a considerable role in identifying vulnerabilities, validating response capabilities and improving overall security posture.
What is Adversary Emulation in Cybersecurity?
Adversary emulation is a cybersecurity methodology that simulates the behavior of real-world attackers to test and evaluate an organization’s security controls and response capabilities. Adversary emulation doesn’t just test security measures in isolation—it challenges organizations to think like attackers, assessing every layer of their particular defense.
This methodology is especially useful in the current environment, where exploiters employ increasingly advanced techniques to breach systems. By mirroring these methods, organizations can patch hidden vulnerabilities and improve their defenses before actual malicious threat actors can exploit them.
Leveraging Frameworks Like MITRE ATT&CK for Adversary Emulation
Adversary emulation uses frameworks like MITRE ATT&CK to model adversary behaviors, ensuring that the simulations are aligned with the most up-to-date threat intelligence.
By mimicking authentic attack scenarios, adversary emulation bridges the gap between theoretical security measures and practical threat management, offering insights that generic penetration tests or vulnerability scans cannot provide.
If an organization faces threats from ransomware groups, adversary emulation might involve simulating encryption techniques or phishing strategies commonly used by those groups. This targeted approach ensures preparedness for specific, high-risk scenarios.
This enables organizations to not only identify gaps but also understand the implications of these gaps in real-world scenarios.
How Does MITRE Define Adversary Emulation?
The MITRE ATT&CK framework serves as a foundational reference for adversary emulation. It categorizes and documents the known behaviors of cyber adversaries, offering a comprehensive library of TTPs.
This framework empowers security professionals to create realistic emulation scenarios tailored to their specific environment.
Key features of the MITRE ATT&CK framework in emulation
- Comprehensive threat documentation: Includes a library of known adversary behaviors.
- Customizable scenarios: Allows adaptation of simulations to specific organizational risks.
- Actionable intelligence: Aligns security measures with current threat trends.
Organizations benefit from increased accuracy in identifying potential attack vectors and prioritizing the remediation of critical vulnerabilities.
Additionally, adversary emulation exercises provide security teams with hands-on experience in handling realistic attack scenarios, boosting their confidence and preparedness. By finding hidden weaknesses in processes and technologies, organizations can adopt a more strategic approach to improve their overall security posture.
Another key advantage is the ability to validate and improve incident response protocols. When organizations simulate sophisticated attacks, they test not just their tools but also their people and processes, ensuring a cohesive and timely response to actual threats.
This approach leads to reduced response times, minimized impact from breaches, and a stronger organizational resilience in the face of evolving cyber threats.
Adversary Emulation vs Other Testing Methods
Traditional methods, such as vulnerability scanning and penetration testing, primarily focus on identifying potential weaknesses within systems or specific applications. While valuable, these approaches often operate in isolation, analyzing static configurations or individual components rather than providing a holistic view of organizational resilience.
Adversary emulation takes a more dynamic and comprehensive approach. It simulates real-world attacks by replicating the tactics, techniques, and procedures (TTPs) employed by actual threat actors. This methodology not only identifies vulnerabilities but also evaluates how effectively systems, processes, and personnel can detect, respond to, and mitigate these threats under realistic conditions.
Unlike traditional methods that often provide theoretical insights, adversary emulation delivers actionable intelligence by exposing gaps in detection and response strategies. It reveals weaknesses in how security tools are configured, highlights areas where teams need additional training, and uncovers potential delays or failures in incident response workflows.
| Aspect | Adversary Emulation | Penetration Testing | Vulnerability Scanning |
| Scope | Focused on replicating specific adversary behaviors. | Broad assessment of vulnerabilities across systems. | Scan of systems and networks to identify potential vulnerabilities. |
| Intent | Validates detection and response capabilities. | Identifies exploitable vulnerabilities to determine potential attack paths. | Detects and catalogs known vulnerabilities for remediation or further investigation. |
| Methodology | Uses frameworks like MITRE ATT&CK for realistic simulations. | Relies on manual and automated tools to uncover weaknesses. | Relies on automated tools to scan for misconfigurations, outdated software, and weak spots. |
| Outcome | Provides a deep, scenario-based analysis of end-to-end attack scenarios. | Offers targeted insights into specific exploitable vulnerabilities. | Broad but shallow coverage, identifying low-hanging fruit and common weaknesses. |
| Frequency | Periodically or continuously as part of a proactive security program. | Typically performed annually or biannually for compliance or security assessments. | Performed regularly (e.g., weekly, monthly) as part of routine security hygiene. |
Why Should You Perform an Adversary Emulation?
Adversary emulation offers numerous benefits for organizations looking to strengthen their cybersecurity posture:
1. Identifying gaps in security controls
By simulating real-world attack scenarios, adversary emulation reveals vulnerabilities and areas where security measures may fail. These insights are crucial for prioritizing investments in tools and training.
An emulation might expose insufficient monitoring on critical systems, enabling organizations to prioritize improved logging and alerting capabilities.
2. Validating detection and response capabilities
It tests the effectiveness of security tools and teams, ensuring that they can detect and mitigate threats promptly. This validation builds confidence in an organization’s ability to respond to incidents effectively.
For example, simulating a credential-stuffing attack can highlight gaps in multi-factor authentication implementation.
3. Enhancing readiness against real-world threats
Organizations gain a deeper understanding of their risk exposure and develop strategies to counteract potential attacks. This readiness translates into faster response times and reduced impact during actual incidents.
3. Proactive threat management
Adversary emulation shifts organizations from reactive to proactive defense, reducing the impact of future attacks.
Proactively simulating a supply chain attack can prepare teams to detect and respond to threats like those faced in the SolarWinds breach.
4. Building organizational confidence
Beyond technical improvements, adversary emulation fosters a culture of preparedness. Teams become more confident in their capabilities, and leadership gains a clearer understanding of the organization’s cybersecurity posture.
Step-by-Step Guide to performing an Adversary Emulation
Adversary emulation involves a structured process to ensure that simulations are realistic, relevant, and effective.
- Planning and defining objectives : Clearly outline the goals of the emulation exercise, whether it’s testing specific controls, evaluating incident response, or identifying vulnerabilities. Success depends on a clear understanding of what the organization seeks to achieve.
- Gathering threat intelligence: Collect and analyze information about potential threat actors and their TTPs. This data informs the scenarios to be emulated, ensuring they align with current risks.
A global manufacturing firm might focus on espionage tactics employed by nation-state actors targeting intellectual property. - Selecting scenarios based on relevant TTPs: Choose attack scenarios that align with organizational risks and the TTPs documented in frameworks like MITRE ATT&CK. Tailored scenarios yield the most actionable insights. For example, a healthcare provider might select scenarios involving phishing campaigns targeting electronic health records (EHR).
- Executing the emulation and monitoring responses: Simulate the selected attack scenarios, observing how security controls and teams respond. Use advanced monitoring tools to capture every detail of the exercise.
- Analyzing results and implementing recommendations: Evaluate the findings to identify gaps, strengths, and areas for improvement. Use these insights to refine security measures and processes. Comprehensive analysis ensures that lessons from the exercise translate into actionable improvements.
How Different Sectors Leverage Adversary Emulation
Adversary emulation has become a game-changer for organizations looking to stay ahead of today’s ever-evolving threats. By simulating the same tactics and techniques used by attackers, industries like finance, healthcare, and critical infrastructure can pinpoint vulnerabilities that matter most, sharpen their defenses, and build resilience where it counts"
Finance Sector
In the finance sector, adversary emulation is essential for protecting sensitive data against sophisticated cyber threats.
- A financial institution conducted an internal adversary simulation that revealed vulnerabilities stemming from human factors, such as weak password policies and misconfigurations in Active Directory. The simulation demonstrated a complete compromise path without exploiting traditional vulnerabilities, highlighting the importance of addressing human error and organizational policies to prevent future attacks.
- The use of ransomware emulation allows banks to test their incident response plans. For instance, a bank might simulate a ransomware attack on its backup systems to evaluate the effectiveness of its data recovery processes, ensuring that they can restore operations quickly in the event of an actual attack.
Healthcare sector
The healthcare industry faces constant threats to patient data integrity, making adversary emulation crucial for testing defenses against targeted attacks.
- A hospital performed a spear-phishing simulation targeting its staff to assess their awareness and response capabilities. This exercise involved sending simulated phishing emails to employees and measuring the rate at which they recognized and reported the threats. The results helped improve training programs and incident response protocols.
- Healthcare organizations often emulate attacks on electronic health record (EHR) systems. By simulating unauthorized access attempts, hospitals can evaluate their detection capabilities and refine their access controls, ensuring patient data remains secure against cyber threats.
Critical infrastructure
Adversary emulation plays a vital role in protecting essential services from cyber threats that could disrupt operations or compromise safety.
- A utility provider simulated a denial-of-service (DoS) attack on its SCADA systems to evaluate resilience. This exercise tested how well the control systems could maintain operations under stress and how quickly they could recover from an attack. The results informed improvements in their incident response plans and system redundancies.
- In another case, critical infrastructure organizations have used adversary emulation to simulate physical attacks on power grid systems. By mimicking scenarios where attackers gain physical access to control rooms, these organizations can identify weaknesses in their physical security measures and enhance their overall security posture.
Adversary emulation not only helps organizations identify vulnerabilities but also ensures compliance with industry regulations that mandate regular security assessments. With these simulations, organizations can easily strengthen their defenses against upcoming and new cyber threats.
Specific scenarios
- Ransomware Simulation: Testing preparedness against ransomware threats by mimicking their delivery, encryption, and ransom demand methods.
- APT Attacks: Simulating advanced, multi-stage attacks to evaluate how well detection and response tools can mitigate sophisticated threats.
- Data Exfiltration: Testing how sensitive data might be accessed, exfiltrated, and how quickly such actions are identified and mitigated by security teams.
How Cymulate Can Help with Adversary Emulation
Cymulate offers an advanced platform that simplifies and enhances adversary emulation for organizations.
Key Features of the Cymulate platform
- Real-Time Emulation Capabilities: Conduct realistic simulations aligned with the latest threat intelligence.
- Actionable Insights: Receive detailed recommendations to address identified gaps and strengthen defenses.
- User-Friendly Interface: Streamline the emulation process with an intuitive platform designed for both Red Team and Blue Team use.
- Continuous Validation: Regularly test and optimize security controls to ensure ongoing protection.
Cymulate not only supports adversary emulation but also complements other security validation practices. Its seamless integration with existing tools makes it a versatile addition to any cybersecurity program.
Key Takeaways
Adversary emulation offers a significant advantage in today’s evolving and threat-laden security landscape.. By replicating the behaviors of real-world attackers, this approach allows organizations to move beyond reactive defenses and adopt a proactive security posture.
It provides a reality check for existing security measures, exposing vulnerabilities and ensuring teams are battle-ready for genuine cyber threats.
Incorporating adversary emulation is not just about testing—it’s about building confidence in your organization’s ability to withstand the onslaught of increasingly sophisticated attacks. Advanced platforms like Cymulate can help organizations to transition from merely hoping their defenses will hold to knowing they are completely prepared for any threats.