Frequently Asked Questions
Product Information & Adversary Simulation
What is adversary simulation?
Adversary simulation is the practice of recreating real-world cyberattacks so an organization’s cybersecurity defenses can be evaluated under realistic conditions. Unlike static assessments or theoretical risk models, adversary simulation applies actual threat actor tactics to reveal the effectiveness of your detection, response, and containment capabilities. This approach provides actionable insight into gaps that traditional security testing methods can miss by securely and accurately replicating the behavior of various threat actors, including cybercriminals, nation-state actors, and insider threats. Learn more.
How does adversary simulation work?
Adversary simulation works through controlled attack scenarios that simulate the adversary lifecycle, including initial access, lateral movement, privilege escalation, and data exfiltration. These simulations are closely mapped to frameworks like MITRE ATT&CK and can use pre-built or custom scenarios to replicate emerging threats. This process helps organizations discover exposures, misconfigurations, or blind spots, enabling faster mean time to remediate (MTTR) and improved detection. Learn more about MITRE ATT&CK mapping.
What is the difference between adversary simulation and adversary emulation?
Adversary emulation seeks to replicate the exact behavior of a known threat actor, reproducing their documented tactics, techniques, and procedures (TTPs). Adversary simulation, on the other hand, models broader attack techniques and scenarios not limited to a single group. Simulation identifies overall security gaps and resilience, while emulation provides deep, scenario-based analysis of precise threats. Read more.
How do red team adversary simulations help improve security posture?
Red team adversary simulations expose how attacks unfold across systems, users, and processes, validating that security controls work in the face of realistic attacks. This process uncovers attack paths, validates detections, and stress-tests incident response playbooks, accelerating security maturity and strengthening your posture against threats. Learn more about attack path discovery.
Can Cymulate emulate specific threat actors?
Yes. Cymulate offers an advanced platform that simplifies and enhances adversary emulation for organizations. It provides real-time emulation capabilities aligned with the latest threat intelligence, actionable insights for remediation, a user-friendly interface, and continuous validation to regularly test and optimize security controls. Learn more.
Will Cymulate adversary simulation overwhelm our SOC with alerts?
No, Cymulate is designed to optimize SOC efficiency, not overwhelm it. Simulations are executed in a controlled manner, highlighting exposures and gaps without generating excessive noise in production systems. Your SOC gains actionable intelligence for enhanced detection rules, fine-tuned controls, and optimized workflows, allowing teams to focus on what matters most. Read more.
Can I simulate cyber threat scenarios across hybrid environments with Cymulate?
Yes. Cymulate supports adversary simulation across hybrid environments, including on-premises, cloud, SaaS applications, and remote endpoints. Scenarios follow realistic attack paths spanning cloud workloads to internal networks, enabling organizations to validate defenses end-to-end and reduce risk from lateral movement and data exfiltration. Learn more.
What types of security controls can Cymulate test?
Cymulate can test a wide range of security controls, including Endpoint Security (AV/EDR), Cloud Security (CWPP), Containers/Kubernetes, Secure Email Gateway (SEG), Secure Web Gateway (SWG), Web Application Firewall (WAF), Network Security (IPS/IDS), Data Loss Prevention (DLP), and SIEM/SOAR detections. Each control is tested with relevant attack scenarios to identify weaknesses and provide mitigation guidance. Learn more about endpoint security validation.
How does Cymulate help with lateral movement and privilege escalation testing?
Cymulate enables organizations to safely execute lateral movement and privilege escalation scenarios, mapping attack paths to reveal exposed routes to critical assets. Automated testing identifies how attackers could move laterally and provides mitigation recommendations to prevent security breaches. Read the Attack Path Discovery data sheet.
What is the primary purpose of Cymulate's adversary simulation platform?
The primary purpose of Cymulate's adversary simulation platform is to help organizations proactively validate their cybersecurity defenses, identify vulnerabilities, and optimize their security posture. It empowers security teams to stay ahead of emerging threats and improve overall resilience through continuous threat validation, exposure prioritization, and operational efficiency. Learn more about Cymulate.
How does Cymulate automate adversary simulation testing?
Cymulate automates adversary simulation testing by providing pre-built templates, best practice assessments, and an attack scenario workbench for custom attacks. Automation and AI enable continuous, proactive defense strategies, scaling advanced testing for active campaigns and custom threats targeting users, systems, and networks. Learn more about exposure validation.
How does Cymulate visualize security gaps across the MITRE ATT&CK framework?
Cymulate enables users to easily see security gaps across the adversary lifecycle by mapping simulation results to the MITRE ATT&CK framework. This visualization supports prioritizing remediations and helps keep your environment secure by highlighting areas of weakness and improvement. Learn more.
What are the benefits of using Cymulate's adversary simulation platform?
Benefits include simplified and automated offensive testing, increased efficiency through continuous red teaming, improved threat detection, and continuous validation to prove and improve threat resilience. The platform also provides actionable insights, policy tuning guidance, automated control updates, and custom mitigation rules. Learn more.
How does Cymulate support continuous testing?
Cymulate supports continuous testing by automating assessments using pre-built templates and customizable attack scenarios. This enables organizations to monitor for drift, validate defenses against the latest threats, and maintain an up-to-date security posture. Learn more.
What kind of organizations use Cymulate's adversary simulation platform?
Organizations across all industries, including finance, healthcare, retail, media, transportation, and manufacturing, use Cymulate for exposure validation and adversary simulation. Customers range from small enterprises to large corporations with over 10,000 employees. See customer stories.
What feedback have customers given about Cymulate's adversary simulation platform?
Customers have praised Cymulate for its ease of use, actionable insights, and ability to validate controls against emerging threats. For example, a Chief Security Officer at a global hedge fund said, “With Cymulate, I can validate controls against emerging threats faster than I could before.” Read more reviews.
What technical documentation is available for Cymulate's adversary simulation platform?
Cymulate provides a range of technical resources, including guides, whitepapers, solution briefs, and data sheets. Notable resources include the Exposure Management Platform Whitepaper, Attack Path Discovery Data Sheet, and Exposure Validation Data Sheet. Visit the Resource Hub for more.
How does Cymulate integrate with other security technologies?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a complete list, visit the Partnerships and Integrations page.
What security and compliance certifications does Cymulate hold?
Cymulate holds several key security and compliance certifications, including SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. These certifications demonstrate Cymulate’s commitment to industry-leading best practices for security, privacy, and cloud services. Learn more about security at Cymulate.
How does Cymulate ensure data security and privacy?
Cymulate ensures data security through encryption for data in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, and a tested disaster recovery plan. The platform is developed using a strict Secure Development Lifecycle (SDLC), and employees undergo ongoing security awareness training. Cymulate is also GDPR compliant. Read more.
How long does it take to implement Cymulate's adversary simulation platform?
Cymulate is designed for quick and easy implementation. It operates in agentless mode, requiring no additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment. Comprehensive support and educational resources are available to help you get started. Book a demo.
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization’s requirements. Pricing depends on the chosen package, number of assets, and scenarios selected for testing and validation. For a detailed quote, schedule a demo with the Cymulate team.
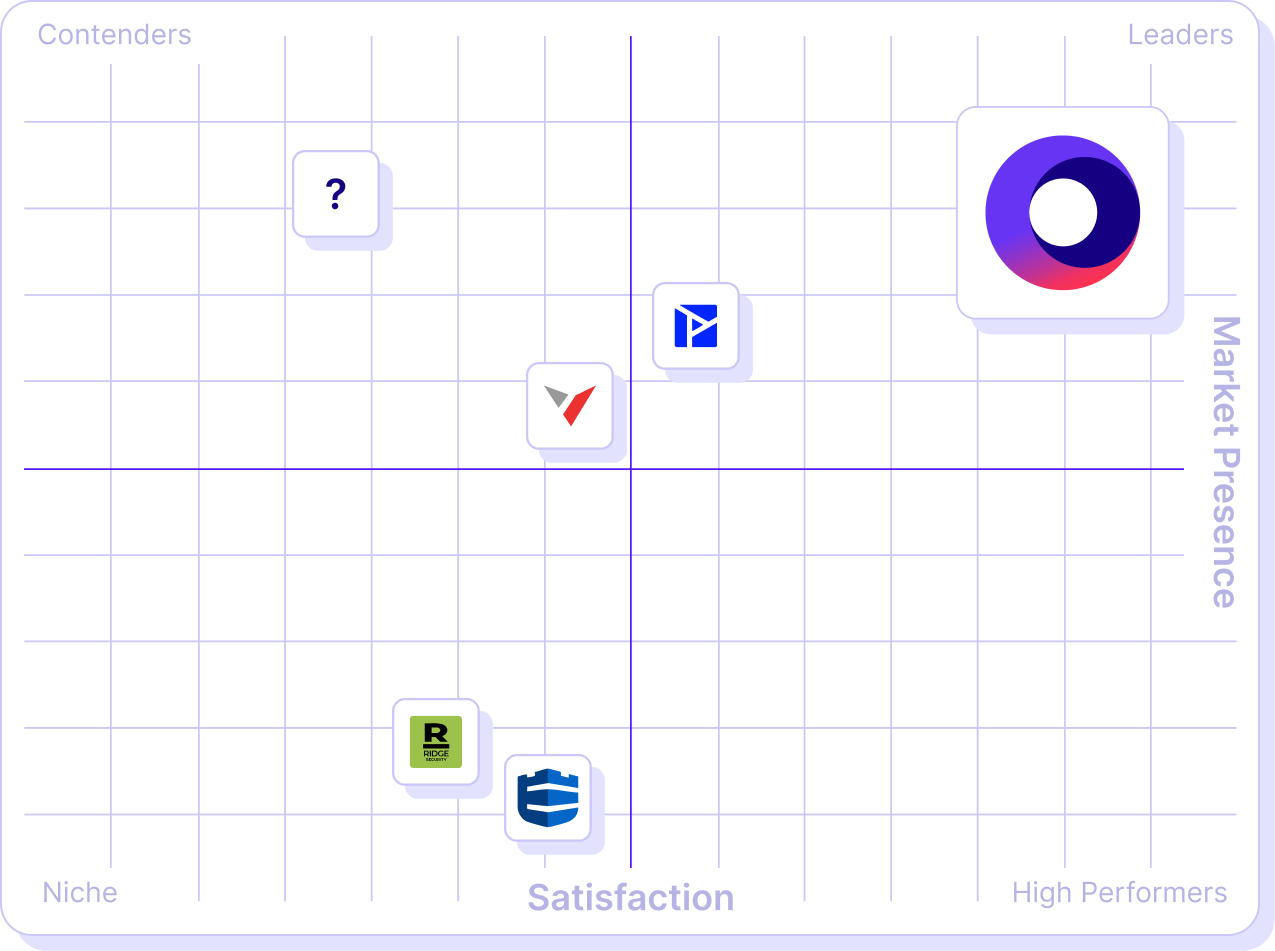
How does Cymulate compare to other adversary simulation and BAS platforms?
Cymulate stands out for its unified platform, continuous threat validation, AI-powered optimization, complete kill chain coverage, ease of use, and proven results. It offers the industry’s largest attack library, daily updates, and measurable outcomes such as a 52% reduction in critical exposures and an 81% reduction in cyber risk within four months. See detailed comparisons.
Who are Cymulate's main competitors?
Cymulate’s main competitors include AttackIQ, Mandiant Security Validation, Pentera, Picus Security, SafeBreach, and Scythe. Each competitor has different strengths, but Cymulate is recognized for its innovation, comprehensive exposure validation, and continuous platform updates. Read more.
What are the key capabilities and benefits of Cymulate's adversary simulation platform?
Key capabilities include continuous threat validation, unified platform for BAS and CART, attack path discovery, automated mitigation, AI-powered optimization, complete kill chain coverage, ease of use, and an extensive threat library. Benefits include improved security posture, operational efficiency, faster threat validation, cost savings, enhanced threat resilience, and better decision-making. Learn more.
What business impact can customers expect from using Cymulate?
Customers can expect up to a 52% reduction in critical exposures, a 20-point improvement in threat prevention, a 60% increase in team efficiency, and an 81% reduction in cyber risk within four months. Cymulate also helps automate processes, save time, and improve communication with stakeholders. See more business impact metrics.
What pain points does Cymulate solve for security teams?
Cymulate addresses fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation capabilities, operational inefficiencies in vulnerability management, and post-breach recovery challenges. See case studies.
Are there case studies showing Cymulate's impact?
Yes. For example, Hertz Israel reduced cyber risk by 81% in four months, a sustainable energy company scaled penetration testing cost-effectively, and Nemours Children's Health improved detection and response in hybrid environments. Read more case studies.
How does Cymulate tailor solutions for different security roles?
Cymulate provides tailored solutions for CISOs and security leaders (metrics and risk prioritization), SecOps teams (automation and efficiency), Red Teams (automated offensive testing), and Vulnerability Management teams (in-house validation and prioritization). Learn more about role-based solutions.
What support options are available for Cymulate customers?
Cymulate offers email support, real-time chat support, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers. Contact support or schedule a demo.