September 2022 Cyberattacks Wrap-up
Below is a non-exhaustive summary of the main attacks addressed by the Cymulate research team during September 2022. All the attacks mentioned are included in Cymulate’s Immediate Threat module.
Nation-state attacks
September saw high activity from nation states, including Iran’s apparent APT42 surge in targeted attacks against personal and corporate email accounts of government officials, former Iranian policymakers or political figures, members of the Iranian diaspora and opposition groups, journalists, and academics who are involved in research on Iran, attacks designed to deploy mobile malware capable of tracking victim locations, recording phone conversations, accessing videos and images, and extracting entire SMS inboxes.
A US-CERT alert warns about IRGC-affiliated actors actively targeting a broad range of entities, including entities across multiple U.S. critical infrastructure sectors as well as Australian, Canadian, and United Kingdom organizations.
In addition, Iran-based threat actor MuddyWater, AKA Mercury, presumed to be a subordinate element within the Iranian Ministry of Intelligence and Security, leveraged the exploitation of Log4j 2 vulnerabilities in SysAid applications against a number of organizations located in Israel. The recent spike of attacks exploits Log4j 2 unpatched vulnerabilities.
North Korea also seems to have increased its activity with a Lazarus orchestrated campaign leveraging a new Magic Rat new remote access trojan to target energy providers, including in the US, Canada, and Japan, by infiltrating organizations and attempting to maintain long-term access and exfiltrate data.
Asia in the Line of Fire
The cyber-espionage group WOROK, a group claiming to be a cyberespionage collective that is currently not attributed to any specific nation-state, deployed multiple, publicly available tools for reconnaissance, including Mimikatz, EarthWorm, ReGeorg, and NBTscan, and then deployed their custom implants: a first-stage loader, followed by a second stage .NET loader (PNGLoad). EOROK targeted high-profile companies and local governments, mostly in Asia, though also in the Middle East and Africa.
Active since 2016, another threat actor launched an attack against a telecommunications agency in South Asia began. They used Chinoxy and PivNoxy in their attack that started with a simple email that initially appeared to be a standard malicious spam email message. However, it contained a weaponized attached Word that carried the Royal Road malicious tool and carried with the CVE-2018-0798 exploit targeting an Equation Editor vulnerability.
While a payload was unavailable at the time of the investigation, OSINT research points to the Poison Ivy RAT, which FortiGuard Labs has previously highlighted.
Asian organizations, and potentially some in Mexico, are believed to be a reconnaissance target of a threat actor that we believe was also involved in Operation NightScout in 2021.
CVE-2018-0798 is a Remote Code Execution (RCE) vulnerability in Microsoft's Equation Editor (EQNEDT32), for which Microsoft released a fix on January 9, 2018.
The fact that attackers are still targeting this vulnerability highlights that not all organizations deploy critical patches or upgrade to the latest software.
The truth is that older vulnerabilities are still commonly and successfully being exploited.
Grandoreiro Banking Trojan and Chile Locker Ransomware
A recent Grandoreiro campaign targeted organizations in the Spanish-speaking nations of Mexico and Spain that work across a variety of different industry verticals such as Automotive, Chemicals Manufacturing and others.
The attack consists of threat actors impersonating government officials from the Attorney General's Office of Mexico City and from the Public Ministry in spear-phishing emails designed to lure victims to download and execute "Grandoreiro", a prolific banking trojan that has been active since at least 2016, and that specifically targets users in Latin America.
Grandoreiro is written in Delphi and utilizes techniques like binary padding to inflate binaries, Captcha implementation for sandbox evasion, and command-and-control (CnC) communication using patterns that are identical to LatentBot.
ChileLocker Ransomware targeted a Mexican Bank:
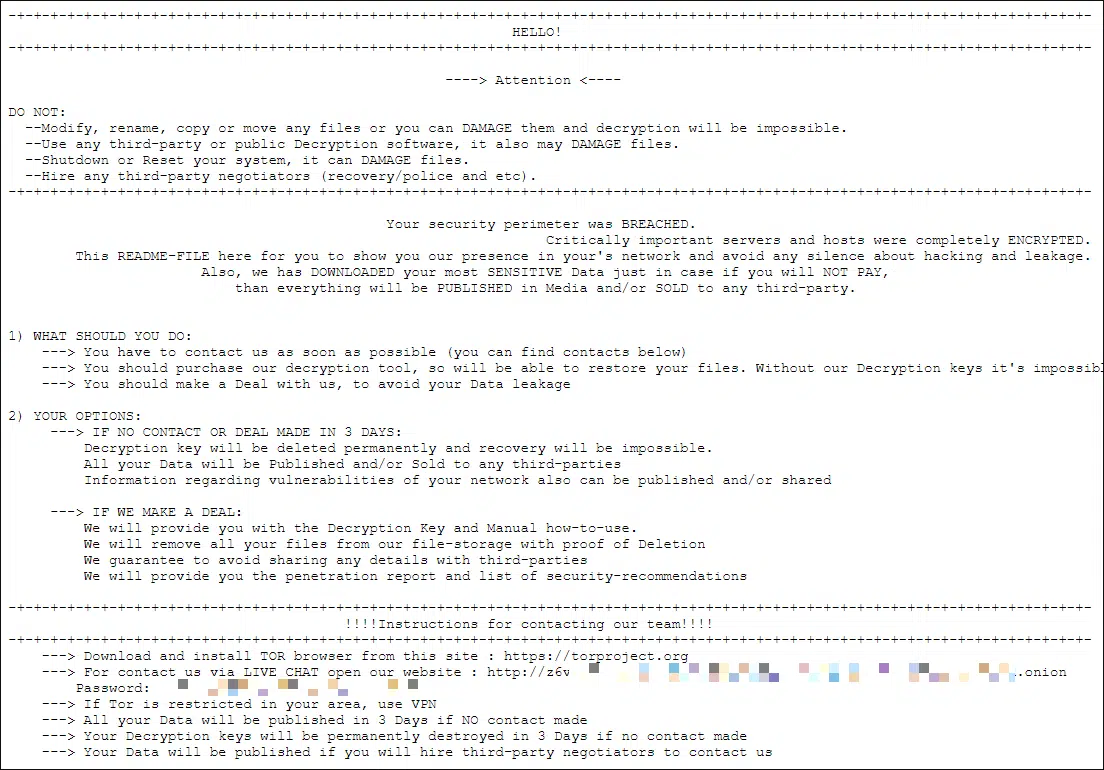
This crypto-ransomware encrypts the data of Windows and Linux VMWare ESXi servers using the NTRU (NTRUEncrypt Public Key Cryptosystem) algorithm and then demands a ransom in BTC to get the files back.
ChileLocker can be distributed by hacking through an insecure RDP configuration, email spam and malicious attachments, fake downloads, botnets, exploits, malicious ads, web injections, fake updates, repackaged and infected installers. It has the ability to gain access to executable files, can terminate processes, and spread over the local network.
It adds itself to the system startup, using the name SecurityUpdate in the Run section to execute at system startup.
Ongoing Linux Targeting
Continuing this year’s meteoric rise in malware and ransomware targeting Linux, this month saw the apparition of Shikitega, a new Linux-specific malware that delivers a multistage infection chain in multiple layers. The first layer contains only a few hundred bytes, with each module responsible for a specific task ranging from downloading and executing Metasploit meterpreter to exploiting Linux vulnerabilities, setting persistence in the infected machine, downloading and executing a cryptominer, or abusing legitimate cloud services to store some of its Command & Control servers.
Beware of Using Available Malware
Derived from AsyncRAT and StormKitty and written in .NET, Prynt Stealer is an information stealer with the ability to capture credentials stored on a compromised system, including web browsers, VPN/FTP clients, and messaging and gaming applications.
Prynt Stealer uses Telegram to exfiltrate data that is stolen from victims, and its author secretively added a backdoor Telegram channel to collect the information stolen by other criminals using that malware by exfiltrated data gathered by other threat actors and sending it to a private Telegram chat monitored by the builder's developers.
Academia Under Vice Society Attack
The Federal Bureau of Investigation (FBI), the Cybersecurity and Infrastructure Security Agency (CISA), and the Multi-State Information Sharing and Analysis Center (MS-ISAC) are releasing this joint CSA to disseminate IOCs and TTPs associated with Vice Society actors identified through FBI investigations.
Vice Society is an intrusion, exfiltration, and extortion hacking group that first appeared in summer 2021. As of writing date, Vice Society actors deployed versions of Hello Kitty/Five Hands and Zeppelin ransomware, but they may deploy other variants in the future. Their presumed favored attack method is to obtain initial network access through compromised credentials by exploiting internet-facing applications [T1190 after spending time exploring the network, identifying opportunities to increase accesses, and exfiltrating data [TA0010]. They then use a double extortion tactic, threatening to publicly release sensitive data unless a victim pays a ransom. Vice Society actors have been observed using a variety of tools, including SystemBC, PowerShell Empire, and Cobalt Strike to move laterally, as well as "living off the land" techniques targeting the legitimate Windows Management Instrumentation (WMI) service [T1047] and tainting shared content [T1080].
Other tactics used by Vice Society actors include
- the PrintNightmare vulnerability (CVE-2021-1675 and CVE-2021-34527) to escalate privileges [T1068].
- scheduled tasks [T1053], creating undocumented autostart Registry keys [T1547.001], and pointing legitimate services to their custom malicious dynamic link libraries (DLLs) through a tactic known as DLL side-loading [T1574.002] to maintain persistence.
- masquerading their malware and tools as legitimate files [T1036], using process injection [T1055], and likely use evasion techniques to defeat automated dynamic analysis [T1497] to evade detection
- running scripts to change the passwords of victims' network accounts to prevent the victim from remediating.
————–
Think your defenses are ready for today’s threats? Put them to the test. Run an automated simulation of active malware attacks to uncover exposures and harden resilience with actionable mitigation.