Endpoint Protection Platform
Endpoint Protection Platform
Endpoint protection platforms (EPP) consolidate cyber prevention and detection into a single system that stops threats before they cause damage while catching anything that gets through.
In this guide, we'll explain how EPP works, what separates them from traditional security tools, and how to measure whether your defenses are effective.
Key highlights:
- An endpoint protection platform (EPP) is a cybersecurity solution that delivers comprehensive protection across all managed devices.
- EPPs leverage advanced AI, machine learning and behavioral analytics to proactively detect and block both known and zero-day threats, surpassing traditional antivirus capabilities.
- Endpoint platforms integrate with security strategies such as zero-trust and EDR, serving as a critical first line of defense against cyberattacks.
- Cymulate Endpoint Security Validation solution continuously assesses and validates EPP effectiveness through simulated attacks, identifying vulnerabilities and optimizing an organization's endpoint security posture.
What is an endpoint protection platform (EPP)?
An endpoint protection platform is a unified, cloud-native security solution designed to protect managed devices, including laptops, servers and mobile endpoints, from sophisticated security threats. By consolidating multiple defensive functions into a single agent, an EPP prevents fileless malware, ransomware and zero-day exploits from compromising the network perimeter.
These are the core functions and objectives of EPP solutions:
- Advanced threat prevention: Blocks malware, ransomware and phishing attacks, while aiding in intrusion prevention before they cause harm
- Real-time monitoring: Continuously scans devices for unusual behavior
- AI and machine learning: Identifies emerging threats without relying solely on known malware signatures
- Endpoint detection and response (EDR): Investigates and neutralizes advanced attacks
- Data protection: Prevents unauthorized access and data leaks
- Cloud integration: Ensures security across remote and hybrid work environments
Best endpoint protection platform features
Advanced EPP solutions go beyond traditional antivirus, employing a multi-layered approach to stop threats and proactively protect managed devices. The following sophisticated mechanisms help organizations achieve this approach:
Behavioral analytics
Instead of just looking for known malware signatures, EPPs continuously monitor endpoint activity — including processes, file access and network connections. The security platform analyzes behavior patterns to detect anomalies and suspicious sequences, effectively identifying fileless malware and other evasive attacks that don't rely on traditional executables.
Machine learning and artificial intelligence
EPPs leverage advanced AI and machine learning algorithms to analyze vast datasets of both malicious and benign code and activity. The endpoint platform identifies and blocks new, unknown (zero-day) threats, evolving ransomware variants and sophisticated phishing attempts before they can execute or cause harm, without requiring prior signature updates.
Cloud-based threat intelligence
Endpoint protection platforms connect to extensive, real-time cloud threat intelligence databases, continuously collecting and sharing information about emerging threats, vulnerabilities and attack vectors. Endpoints receive instantaneous updates, ensuring all devices are protected against the very latest cyber threats as soon as they are identified anywhere in the world.
How to evaluate endpoint protection platforms
Choosing the right EPP from endpoint protection platform examples is critical for securing devices against cyber threats. Here are key features to consider:
- Threat detection capabilities: A strong EPP should use machine learning, behavioral analytics and real-time scanning to detect threats before they cause harm. It must identify known malware, zero-day attacks and suspicious activities without slowing down endpoint devices.
- Ease of deployment and management: Look for a cloud-based solution for easier updates and scalability. On-premise options work for organizations needing full control. The platform should integrate smoothly with existing IT infrastructure and support remote management.
- Integration with other security tools: Your EPP should work with SIEM, SOAR and EDR solutions. Seamless integration ensures better visibility, faster threat response and a more cohesive security strategy.
- Automation & AI: Automation reduces manual workload and improves response times. AI-powered tools help prioritize real threats, cutting down on alert fatigue. The EPP should automate threat investigation and remediation.
- Compliance & Regulatory standards: A good EPP helps businesses meet General Data Protection Regulation (GDPR), The Health Insurance Portability and Accountability Act (HIPAA), PCI-DSS and other regulations. It should offer auditing, reporting and data protection features to ensure compliance.
By focusing on these features, organizations can enhance security, streamline operations and stay ahead of cyber threats.
Endpoint protection vs. endpoint detection and response: A comparison
Both EPP and endpoint detection and response (EDR) protect endpoints, but they serve different purposes. Understanding their differences helps organizations build a stronger security strategy.
| Protection feature | Endpoint protection platform | Endpoint detection and response |
| Primary focus | Prevent attacks before they cause damage. | Detect, investigate and respond to advanced attacks after they bypass initial prevention. |
| Core function | Block known and unknown malware, ransomware and phishing attempts at the entry point. | Monitor activity, identify suspicious behavior and provide security teams with tools to analyze and respond to threats. |
| Detection methods | Antivirus, machine learning and behavioral analysis to detect threats early. | Continuously monitor endpoint activity to identify anomalous or suspicious behavior. |
| Scope of action | First line of defense to stop threats from gaining a foothold. | Deep analysis and active response to advanced, persistent threats. |
| Role in security strategy | Reduce overall risk by stopping most threats at the entry point. | Add critical visibility and capabilities to detect and investigate advanced attacks that bypass EPP. |
Why do you need both EPP and EDR for comprehensive security?
A strong security strategy requires both an endpoint protection platform for prevention and an endpoint detection and response for deeper threat detection and response. EPP reduces risk by stopping most threats at the entry point, and EDR adds security visibility by detecting and investigating advanced attacks.
Together, they close security gaps: EPP prevents, while EDR detects and mitigates anything that slips through.
By combining EPP and EDR, organizations improve threat protection, reduce downtime and strengthen their cybersecurity posture. Prevention alone isn’t enough and detection without prevention leads to unnecessary risk. A layered approach ensures maximum security.
What is the difference between antivirus and endpoint protection?
Endpoint protection platforms and traditional antivirus both aim to protect devices from cyber threats. However, EPP offers a more advanced, proactive approach compared to traditional antivirus software.
Here’s a detailed comparison between traditional antivirus and endpoint platforms:
| Key differences | Traditional antivirus | Endpoint protection platform |
| Threat detection | Traditional antivirus relies on signature-based detection. It blocks known threats but struggles with new, unknown malware. | EPP uses machine learning, behavioral analysis and AI to detect both known and unknown threats in real-time. |
| Protection scope | Antivirus mainly focuses on individual devices, scanning files and programs for malware. | EPP secures entire networks, covering multiple endpoints, including laptops, mobile devices and cloud workloads. |
| Prevention vs. Response | Antivirus only blocks threats when they are detected. | EPP goes further by preventing, detecting and automatically responding to cyber threats. |
| Cloud integration and management | Antivirus requires manual updates and local installations. | EPP often operates from the cloud, providing centralized management and automatic updates across all endpoints. |
| Zero-day threat protection | Antivirus is ineffective against new, unknown threats until a signature update is available. | EPP proactively identifies and stops zero-day attacks using AI and behavioural analysis, even before security patches exist. |
| Insider threat detection | Antivirus focuses on external threats like malware and viruses. | EPP detects suspicious behavior from insiders, such as unauthorized access, unusual file transfers or credential misuse. |
Traditional antivirus alone is not enough against today’s evolving cyber threats. Organizations need EPP’s advanced detection, automation and cloud-based management to stay secure. It reduces risk, simplifies security management and provides better protection against modern attacks.
Optimize your EPP with Cymulate
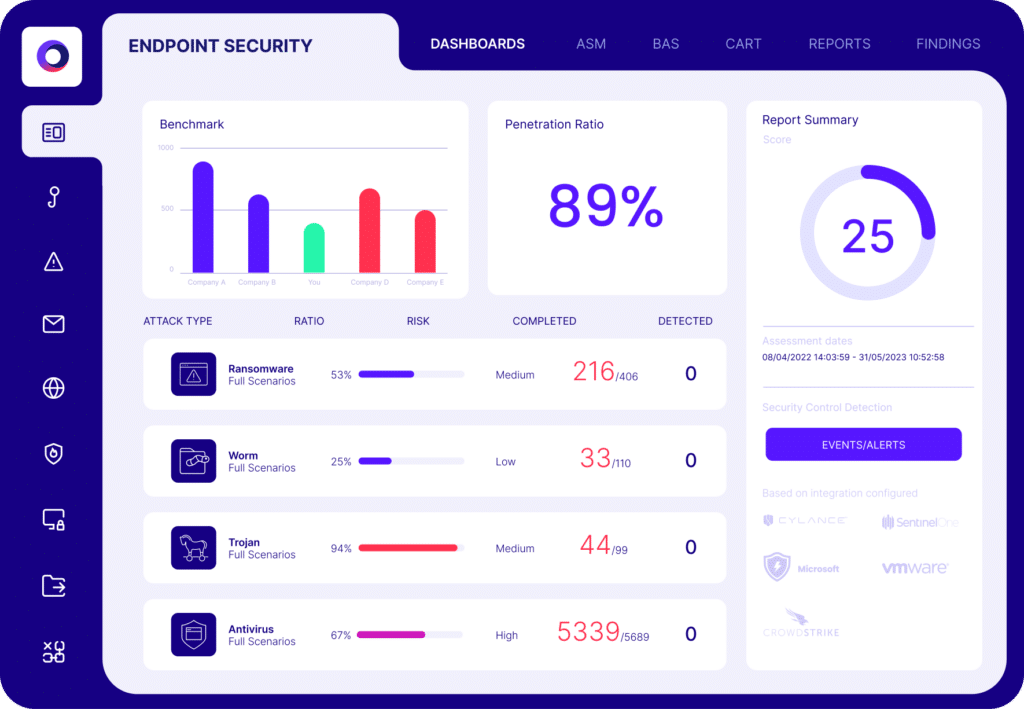
As an endpoint security validation solution, Cymulate:
- Validates the effectiveness of EPP solutions: Cymulate Endpoint Security Validation allows businesses to test whether their EPP blocks threats effectively. It simulates real-world attacks to check if security controls are detecting and preventing threats as they should.
- Simulates real-world threats: Cybercriminals constantly evolve their tactics. With Cymulate Breach and Attack Simulation (BAS), organizations can test their EPP against ransomware, advanced malware and phishing attacks in a controlled environment.
- Closes security gaps: Even next-generation endpoint protection platforms are not foolproof. When vulnerabilities appear, Cymulate provides actionable insights and clear remediation steps. Instead of guessing where security weaknesses are, organizations get detailed reports on how to strengthen their defenses. This proactive approach helps businesses stay ahead of attackers.
- Supports both EPP and EDR assessments: A strong security strategy includes both prevention (EPP) and detection/response (EDR). Cymulate enables organizations to test both to ensure they are working together effectively.
Security isn’t about hoping your tools work — it’s about proving they do. Cymulate gives organizations the confidence that their EPP is effective, identifies weaknesses and helps continuously improve endpoint protection.
By testing, validating and optimizing security measures, businesses can stay one step ahead of cyber threats. Request a demo and ensure your EPP is truly effective against modern threats
Frequently asked questions
EPP tools are the advanced functionalities and integrated technologies within an endpoint protection platform (EPP) that employ a multi-layered approach to secure endpoints. These security tools go beyond traditional antivirus by leveraging mechanisms such as behavioral analytics, machine learning, artificial intelligence and cloud-based threat intelligence to proactively prevent fileless malware, ransomware and zero-day exploits.
EPPs are effective for small to medium-sized businesses (SMBs) and are not exclusively for large enterprises. SMBs face the same sophisticated cyber threats, and EPPs provide advanced, multi-layered protection. Cloud-based management and automation features in modern EPPs simplify deployment and reduce the IT resources required, making robust security accessible and manageable for businesses of all sizes.