Automated Penetration Testing
When organizations face security threats daily, they continually seek innovative ways to protect their data, networks and systems. One protective approach is automated penetration (aka pen) testing. By applying an automated pen test, organizations are able to save valuable resources in all forms, gain vital operational efficiencies and most importantly identify vulnerabilities quickly and securely. There is no question that this automated approach far outpaces its manual predecessor.
What is Automated Penetration Testing?
Originally, automating penetration testing entailed replacing most of the repetitive tasks performed by a human pen tester with automation. Yet, as complexity grew beyond the ability of any human to keep an overarching view of the entire cyber-criminal capabilities, the generic field of automated pen testing had to evolve and become what is now known as Continuous Security Validation.
Automated pen tests simulate cyber attacks against an organization’s network, applications and systems to identify security weaknesses, unlike manual pen testing, which relies on human expertise and effort. Automated penetration testing leverages software to execute repetitive and complex tasks quickly and efficiently, whereas manual pen testing introduces opportunity for errors and is a great deal more time consuming.
What are the Key Differences Between Automated and Manual Penetration Testing?
Both approaches have their place, and many organizations use them together to get the best of both worlds: automated tests for wide coverage and quick checks, and manual testing for thoroughness and discovery of sophisticated vulnerabilities.
- Automated Penetration Testing is ideal for quick assessments, large-scale environments, and repetitive checks of common vulnerabilities. It's faster, more cost-effective, and can handle high-volume scanning.
- Manual Penetration Testing is best suited for deep, thorough testing, especially in complex environments. It's highly adaptable, accurate, and capable of uncovering hidden vulnerabilities, but it takes more time and expertise.
| Aspect | Automated Pen Testing | Manual Pen Testing |
| Speed | Fast; Scans can be completed quickly for known vulnerabilities | Slower; Requires time to explore and test various attack vectors |
| Scope | Limited by pre-configured tools; mainly focuses on common vulnerabilities | Broad; testers can explore new and complex attack vectors, using creativity |
| Cost | Generally, less expensive due to automation | More costly due to human expertise and time |
| Accuracy | Can miss complex vulnerabilities or ones that require context or manual inspection | High accuracy, especially for complex or unique vulnerabilities |
| Scalability | Easily scalable to test large networks or applications | Less scalable due to manual effort required |
Automated Penetration Testing has Challenges too
Even significant technological advancements can come with imperfections and automated penetration testing is no exception. Here are some key challenges organizations face when relying on automated pen testing:
- False Positives and Negatives: Automated penetration testing tools can sometimes produce inaccurate results. These tools are designed to scan for known vulnerabilities and issues, but their automated nature can lead to:
- False Positives: Automated tools may flag harmless or non-critical issues as vulnerabilities. For example, a tool might identify a misconfigured setting or a missing header as a serious security flaw when it actually poses little to no risk in the given context.
- False Negatives: On the flip side, automated tools might miss more sophisticated or subtle vulnerabilities, especially those that require an understanding of the system’s business logic or more advanced techniques. For example, a zero-day vulnerability, a complex chain of attacks, or an issue that depends on user roles might not be detected by basic automation.
- Limited Customization: Automated pen testing tools work well for detecting known vulnerabilities but lack flexibility when it comes to simulating advanced or highly targeted attacks. Tools often operate based on predefined rules or attack patterns, which means they may not easily adjust to unique or customized environments. Specific systems or business logic may require more tailored attacks, which automated tools might not replicate effectively.
- Over-reliance on Tools: Just as tools can be a major operational relief, there is still risk in overuse and does not replace the need for nuanced human skills that come with experience and judgment.
- Integration Challenges: Integrating automated penetration testing tools into an organization’s existing security processes, workflows and environments can require individual sets of tools or configurations for platforms, applications or infrastructures.
- Tool compatibility: not all automated testing tools are compatible with each type of environment or system.
- Workflow integration: Continuous integration/continuous deployment (CI/CD) pipelines and vulnerability management processes are automated tests that must align with existing security operations, which can be complicated and time-consuming.
- Skills gap: Ongoing training for internal employees is a critical component of ensuring new technology is maintained. Lack of familiarity with automated testing tools can result in underutilization and improper configuration.
Automated Penetration Testing and Software
The right tools can make a hard job easy and a time-consuming job quick. With automated penetration testing tools organizations can quickly identify vulnerabilities, misconfigurations, and weaknesses in their systems. The right tool can enhance security posture, accelerate vulnerability detection, and ensure that defenses are continuously tested.
With so many tools in the market it’s critical to narrow down the most favorable ones with key features like compatibility, reporting capabilities, executing regular updates and scalability. These widely popular tools include:
- Burp Suite: Excellent for web application testing, offering features like proxy interception, spidering, intruder, and repeater for manual manipulation of requests and payloads.
- Nessus: A well-known vulnerability scanner that can scan various systems and networks for potential vulnerabilities.
- Metasploit: A powerful penetration testing framework with a large library of exploits and modules for various vulnerabilities.
- Qualys: Offers broad scanning capabilities across different environments including cloud and internal networks.
- Acunetix: Focused on website vulnerability scanning, providing detailed reports on identified vulnerabilities.
Key features to look for in an automated penetration testing tool include:
- Compatibility with various environments: Ensure the tool supports multiple deployment options, including cloud, on-premises, and hybrid environments, to align with your organization's infrastructure.
- Actionable reporting and recommendations: Look for tools that offer detailed, clear and actionable reports with prioritized recommendations for remediation. This helps security teams focus on critical vulnerabilities first.
- Regular updates for evolving threats: An effective automated testing tool should continuously update its vulnerability database and attack simulations to reflect the latest security trends, exploits, and threat intelligence.
- Scalability and flexibility: The tool should scale to meet the needs of your organization, whether you're testing a few systems or a large, complex IT environment.
What Makes Cymulate a Leading Security Validation Provider?
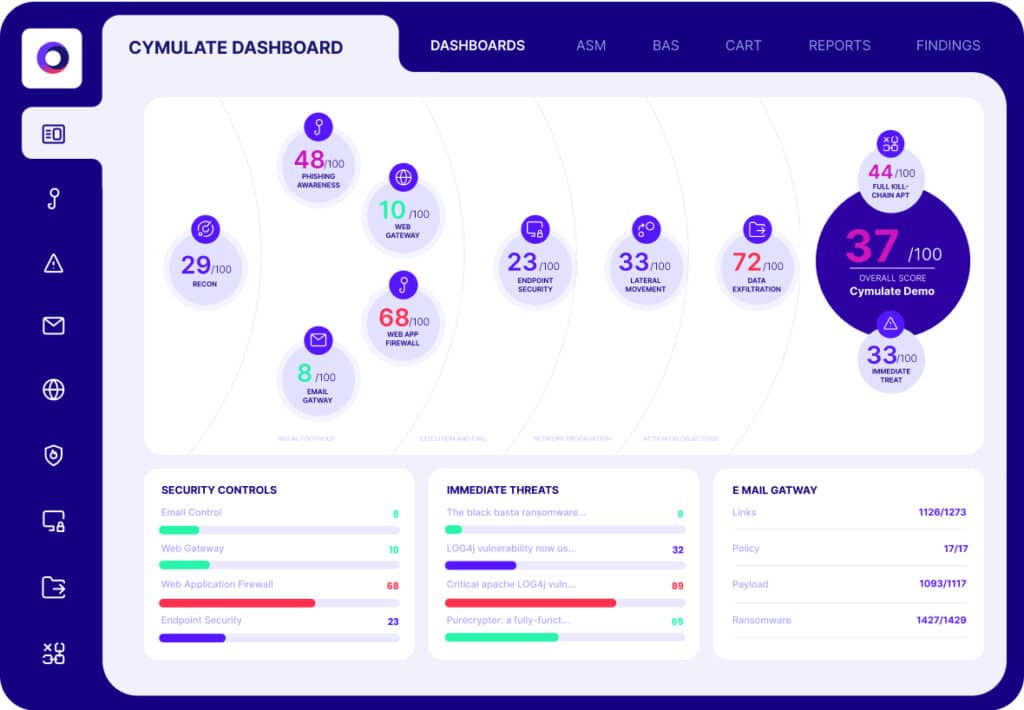
As a leading automated penetration testing and security validation platform provider, Cymulate focuses on continuous security testing and validation across a wide variety of environments. By validating the effectiveness of an organization’s existing defenses, the leading platform can not only proactively assess an organization’s security posture in real-time by simulating real-world attacks but also strengthen its security posture.
With real-time testing of security controls Cymulate provides a constant stream of real-time security feedback to help teams ensure their security controls are functioning as expected. Cymulate performs continuous exposure validation, allowing organizations to identify vulnerabilities across networks, endpoints and security tools on an ongoing basis. This is a crucial feature for identifying gaps in security before attackers can exploit them.
Through simulating real-world attacks, including multi-stage and sophisticated attack paths, organizations can test how well their security controls can handle real-world attack chains. Every organization and leader needs to know about their results and next steps. The Cymulate platform provides detailed reports with actionable recommendations, enabling organizations to prioritize security fixes based on severity, risk level and potential impact to business operations.
Key Takeaways
It’s become clear that automated penetration testing is an essential part of modern cybersecurity efforts and strategy. By leveraging automation, organizations can identify vulnerabilities more efficiently, scale their testing across multiple systems, and continuously monitor their security posture.
However, organizations must approach automated penetration testing as a complement to, rather than a replacement for, human expertise, as every technological advancement comes with challenges and will always need skilled human experts by its side to pave the way.