How to Give Red Teams the Freedom to Focus on High Value Tasks
“Automation” has become one of those words that I hear everywhere.
Most industries now understand that implementing some form of the automated process has many benefits, including improving operational efficiency, and as a result, employee morale. But what does this mean for cybersecurity, and more specifically, offensive security?
Before we can understand how automation can help improve red team processes, let’s look at the day-to-day challenges that red teams face.
The Daily Challenges of Red Teams
We are all very aware of how the cyber professional shortage and budget cuts are impacting cybersecurity, but a red team’s daily responsibilities create several challenges specific to them.
1. Repetitive and Time-Consuming Tasks
The red team’s responsibilities are time-consuming and labor-intensive, which leaves them less time for high-value tasks if they don’t automate the simple stuff. Internal red teams need to keep up with the latest indicators of compromise (IoCs) and tactics, techniques, and procedures (TTPs) by coding new attack simulations every day. These new simulations are difficult to develop and not easily incorporated without heavy coding and QA skills. Additionally, following each assessment, they may need to write up their results for two different audiences – technical results for the blue team, so they know what they need to remediate, and executive results for the leadership team so they understand how their security gaps impact the business.
2. Limited Scope and Resources
Attackers are unlimited in time and resources when they try and infiltrate an organization; they will do anything to gain an initial foothold and reach the crown jewels. Pen testers do their best to emulate an attacker, but they are limited by the scope of the engagement and minimizing the impact on the availability of systems. Attackers don’t care about knocking over that business-critical server if it gets them to their ultimate goal. Offensive security assessments often cannot mimic attacker techniques in breadth and depth.
For example, they may be unable to test all the different steps of the entire kill-chain due to client restrictions, or they do not have opportunistic capabilities when they reach a dead end to try and find other ways in.
As mentioned above, new IoCs and TTPs come out daily, and it can be difficult to keep up and create proof of concept exploits to test for these weaknesses while in an engagement.
3. Short-Lived Testing Results
To make sure your organization is protected, your red team needs to run assessments on a continual basis. Your annual pen test reports give you a point-in-time snapshot of your security, but cybersecurity is fast moving.
Dynamic IT environments and the continuously changing threat landscape lead to security drift; things change so quickly that if you aren’t testing repeatedly, you won’t know if you are actually protected against any new (or old) threat. Manually running these assessments is labor-intensive and time-consuming.
A new trend called red team automation is an easy way to solve these three challenges and scale adversarial activities.
Solving Red Team Challenges with Automation
Red team automation tools provide a platform to increase red teams’ operational efficiency and optimize their adversarial activities in a production-safe environment. Red team automation enables red teams to:
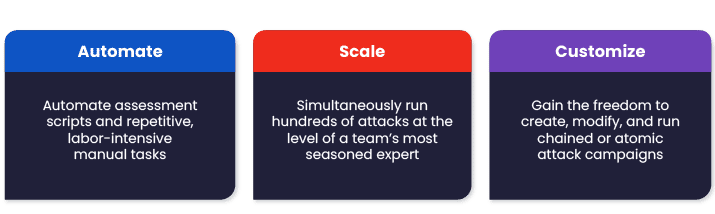
Automate, Scale, and Customize
Red team automation platforms reduce manual labor for red teamers by automating assessment scripts, repetitive tasks, and reporting in a centralized location. Red teamers can simply choose which out-of-the-box assessments they want to run based on their expertise, or easily create new templates which are made available to the entire team. This capability enables teams with junior members, who are still learning on the job, to scale and run hundreds of attacks at the level of their most seasoned team members. Think of trying to hike a new trail having a map to guide you versus just stumbling through on your own.
To watch me explain this capability in further detail, check out this episode of “Better Ask Jes”:
Red teams also have the option to continuously run their assessments on a scheduled cadence – daily, weekly, or monthly – to prevent drift and lower risk. Following each assessment, technical and executive reports with easy-to-digest remediation guidance are automatically created based on the data generated during the assessment, relieving red teams of that responsibility.
The assessment templates also promote continuous improvement and purple team capabilities which should be used to increase collaboration with blue teams. Training blue teamers to recognize the behaviors and signatures of an attacker through simulated assessments run by the red teamers is kind of like practicing before the big game.
Additionally, these platforms update their assessments 24/7 based on newly discovered threats so that red teamers with limited resources can hit the ground running sooner. Production-safe assessments are available for testing quickly after a new threat is discovered.
Red team automation platforms enable red teams to create complex customized scenarios from pre-built resources and custom binaries and executions, without any limits or restrictions. Each step in the scenario is connected, so a previous assessment output can be used as part of the upcoming assessment input. Custom scenarios can be used for pro-active threat hunting and health checks. It is also an effective way for blue teams to continuously test mitigation efforts following a pen test; by automating pen test assessments to see if the blue team’s remediation reduced risk, red teams don’t need to spend their time manually running the same assessments.
Once an assessment is run and blue teamers receive remediation guidance, they can re-run the same assessment as often as they want, independent of the red team, to see if their mitigation efforts are effective. Additionally, the framework launches attacks and correlates them to security control findings through API integrations to provide actionable detection and mitigation guidance for security analysts.
Advanced Capabilities of Red Team Automation Platforms
1. External Attack Surface Management (EASM)
The reconnaissance phase entails a comprehensive analysis of an organization which can mean days or weeks before red teamers even begin an attack depending on the scope of the engagement. External Attack Surface Management (EASM) technology emulates real attackers to continuously discover and enumerate externally accessible digital assets (such as domains and IP addresses). Taking it a step further to give important business context, EASM can identify vulnerabilities and exploit them to truly map out the organization’s external attack surface.
2. Phishing Awareness Campaigns Simulations
Testing phishing awareness is an important aspect of assessing an organization’s security posture but manually running phishing campaigns is labor intensive and time-consuming. Pen testing often doesn’t include social engineering in scope, but a large percentage of the hacks you read about on the news start with a phish. The Phishing Awareness capability provides the resources to create an automated internal phishing campaign.
3. Lateral Movement
Continuously assessing network configuration and segmentation policies through escalating privileges and exploiting misconfigurations on multiple machines can be time-consuming for red teams when done manually. The Lateral Movement capability emulates a real-life hacker that has gained an initial foothold in a company’s network and shows how the hacker can move laterally from the originating workstation in search of valuable assets. It runs automatically and applies “living off the land” non-destructive hacking tactics and techniques to continuously uncover infrastructure misconfigurations and weaknesses. This allows you to verify your environments are properly isolated with evidence.
Conclusion
A potential way to help your red team optimize their resources and skills, as well as encourage collaboration, is to introduce an automated red teaming tool. You will not only see an increase in your red team’s productivity but also in their morale because they will no longer have to focus on time-intensive manual tasks and reporting.


