APAC Cybersecurity Wake-Up Call: Reinforcing Resilience is Key
The recent Latitude Financial breach’s fame is only due to its preeminence in APAC. It is consistent with the 2022 spate of data breaches in APAC, starring Medibanks, Optus, MyDeal Retail, Telstra, and even the New Zealand government, that highlighted the urgent need for businesses to prioritize cybersecurity measures. Many smaller, less famous, organizations are also taking hits, and, though their relative lack of fame protects them from making headlines, the damage they experience can be crippling.
This growing cyber insecurity might be what underlines the trend to increase cybersecurity budget and spending, a trend reported by 64% of organizations, as reported by Kroll’s latest APAC State of Incident Response report.
Cybersecurity Legal Frameworks Evolution in Australia and New Zealand
Last year’s Medibank and Optus data breaches triggered the steep increase of financial penalty from AU$ 2.2 million to AU $ 50 million or 30% of the infringing company turnover, whichever is greater. It also increased the scope of the Office of the Australian Information Commissioner’s (OAIC) involvement in the privacy breach resolution and scope determination process and led to the creation of Australia’s Home Affairs Cyber Security Strategic Expert Advisory Board, headed by the former Telstra CEO Andy Penn.
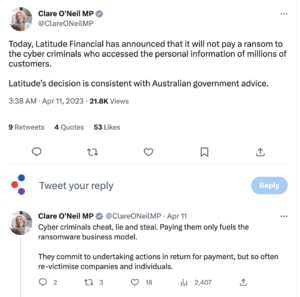
On April 11th, 2023, Latitude Financial announced that they would refuse to pay the ransom, as advised by the Australian Cyber Security Centre (ACSC). In line with Andy Penn’s recommendation, Australia Cyber Security Minister Clare O’Neil is now weighing outlawing the payment of ransom.
Last February, Penn underlined the potential national security impact of reliance on digital connectivity, especially in view of the growing number of interdependencies and the multiplication of actors involved in supply chains. “There are certain systems within our country”, he said, “that may or may not be in private hands, but that, if disrupted, could lead to an issue of national security.”
This, according to Penn, is at the core of the need for Australia to put in place minimum standards of cybersecurity, especially as the evolution of the threat landscape has outpaced the level of cybersecurity preparedness and that much more needs to be done.
As the ACSC estimates that the downside of the often proudly reported Australian highest median wealth per adult in the world is that it makes Australia particularly attractive for cybercriminals.
In New Zealand, last December, the government suffered a breach resulting from a supply chain attack, that affected the Ministry of Justice, among other governmental agencies, granting access to thousands of autopsy reports.
APAC-Specific Cybersecurity Weak Points
Data collected to create the Cymulate 2022 Cybersecurity Effectiveness Report indicated that APAC region organizations fared poorly in protecting against data exfiltration, web application firewall (WAF), and web gateway-based breaches compared to their global counterparts. The scores in the table below are the risk scores for each attack vector.
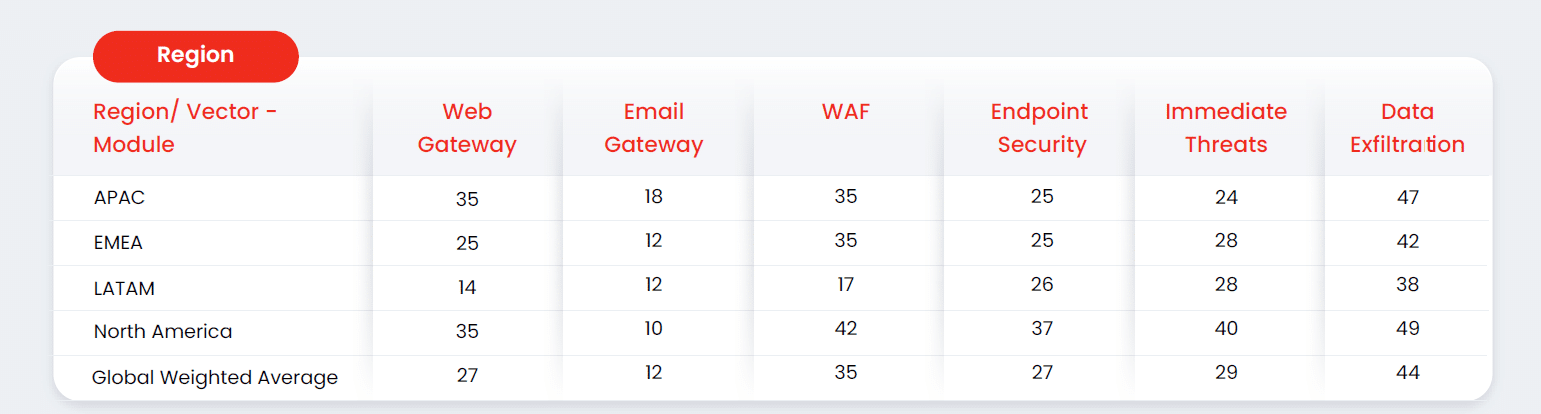
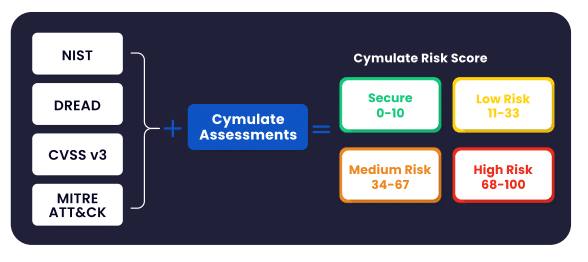
Note: The risk score is based on an algorithm that analyzes attack simulation’s ability to evade detection and how far their attack path can progress unimpeded. The results are then correlated with NIST, DREAD, CVSS and MITRE ATT*CK severity scoring system. The risk score reflects the contextual risk score within an organization’s infrastructure, factoring in security controls’ ability to protect assets despite the presence of vulnerabilities or other security gaps.
In New Zealand, the 2022 Director Sentiment Survey report shows that a significant proportion of boards was insufficiently prepared yet adopted an “it won’t happen to us” approach.
According to Forrester, 68% of Asia Pacific (APAC) organizations were breached in 2021, highlighting how the overall APAC region lacks preparation against cybersecurity breaches.
This combination of inadequate preparedness, tightening regulations, increased penalties, and expanded threat landscape are likely behind the predicted 16.7% increase in security spending for the region in 2023, forecasted to reach US$55 billion by 2026.
How to Assess the Value of Cyber Investments
The first step to identify where to invest additional money to shore up a cybersecurity system is to measure the efficacy of the existing one.
Although the cost of a cybersecurity defense system can be calculated by adding the cost of cybersecurity solutions and the wages of security and IT teams, determining the actual value of defensive solutions is much more complex.
It requires validating the efficacy of solution stacks and SIEM and SOAR arrays, that all depend heavily on selecting and enforcing adequate security control policies for each solution. Validating exclusively through penetration testing lacks the granularity required to identify which solution stopped a particular attack and the continuity required to continuously evaluate resilience.
Sometimes, this shows that there is no need to invest in yet more solutions, just fine-tuning the existing ones to get the desired results.
Pinpointing underperforming security solutions and quantifying risk exposure calls for a robust, continuous security validation strategy, preferably driven by a unified platform. An effective exposure validation platform spans the full cyber kill chain, identifying gaps from initial access and lateral movement to data exfiltration. It enables organizations to validate their defenses comprehensively across exposed assets, escalation paths, command and control channels, and beyond - providing clear, actionable insights to strengthen cyber resilience.


