How to Expand IoCs for Immediate Threat Simulations
Why Expanding IoCs Enhances Threat Detection
With the acceleration of new cyber immediate threats emergence rhythm, it is always a good idea to add new threat hunting skills and techniques.
Typically, the trigger to create a new threat simulation campaign is the more or less strident public reporting of the appearance of a new threat. As cyber-attackers are also quick to capitalize on these new attacks, finding ways to procure the attack technology and weaponize it before the defensive arrays have been updated.
This is an ongoing race and staying ahead of potential attackers can be enhanced by enriching your internal threat intelligence feed with tools such as Virus Total and other tools – utilizing their IOC bank.
Before getting into the nitty-gritty detail of how to use any of those tools, let’s put things into a defensive context, that presupposes an effective SIEM and SOAR array.
Closing the Gap Between IOC Detection and Defense
SIEM and SOAR tools are regularly updated by their vendors to reflect the emergence of new threats and IOCs, but there is a time gap between the time IOCs are available, the time the vendors update their database, and the time these updates are reflected within the defensive infrastructure. These time gaps are a golden opportunity for attackers to strike.
In order to rapidly check if a specific IOC is detected by the existing defensive array or if it needs to be manually added. anyone can use Virus Total, copy-paste the IOC, and check if the tools in your SIEM/SOAR array are detecting it. If not, it might be a good idea to add it manually.
But to really expand on enriching your Threat Intelligence feed, you might want to emulate Cymulate's R&D team and consider Virus Total Enterprise.
Yet, as Virus Total Enterprise is quite costly, it might help to get a better idea of what you might gain from it if you adopt it. Alternatively, you can use the other freemium tools mentioned in this blog post.
This guide aims at giving you a better idea of some of its capabilities and of tricks that could help you maximize its use.
Leveraging VirusTotal to Improve Threat Intelligence
Among other capabilities, acquiring Virus Total Enterprise premium access opens the gates to Virus Total full file database, allows you to perform unique queries within it, and creates hunting rulesets that utilize YARA rules to hunt for malware campaigns.

As the purpose of this post is to give an idea of the richness of VirusTotal’s database and of how to maximize its use, we will focus on locating IOCs generated by a specific threat actor, more specifically, following a mention of that threat actor in a publication.
Discovering Hidden IoCs in Lazarus Phishing Campaigns
To keep it simple, we will look at the expanded IOC list that can be unearthed based on a random recent blog post referring to a recent phishing campaign launched by the threat actor “Lazarus”.
This blog post helpfully provides Lazarus’ raw IOC from that attack. VirusTotal Enterprise includes a nifty auto-formatting feature. We can use that feature to obtain a detailed list of all Lazarus passed IOC simply by copy-pasting the raw IOC from the blog in the VirusTotal search bar.
The copied IOCs are:
Hashes
e87b575b2ddfb9d4d692e3b8627e3921
a27a9324d282d920e495832933d486ee
3f326da2affb0f7f2a4c5c95ffc660cc
490c885dc7ba0f32c07ddfe02a04bbb9
712a8e4d3ce36d72ff74b785aaf18cb0
a27a9324d282d920e495832933d486ee
f2a0e9034d67f8200993c4fa8e4f5d15
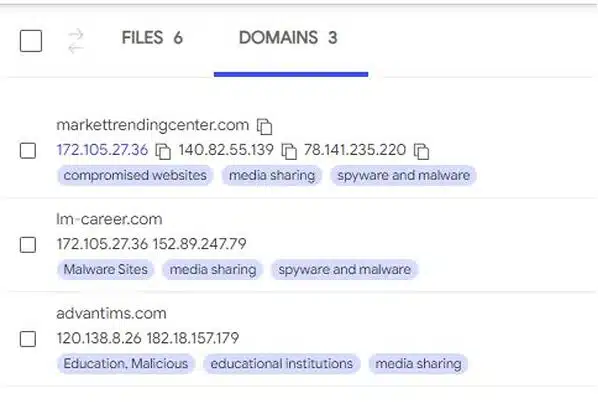
Domains
markettrendingcenter.com
lm-career.com
advantims.com
This yields the results displayed below, listed as either files or domains.
First, let’s consider interesting commonalities between the word documents mentioned in the blog post as part of the phishing campaign.
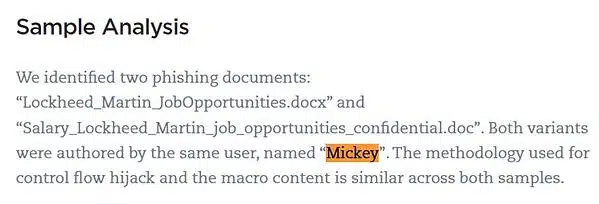
The post draws attention to the fact that both are authored by a user named “Mickey”. We can confirm this by reviewing the sample’s hashes “a27a9324d282d920e495832933d486ee” and “3f326da2affb0f7f2a4c5c95ffc660cc”
VirusTotal returns the following data:
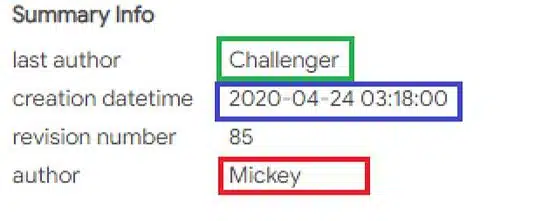
You can see that reviewing these hashes with VirusTotal provided additional information. We now know that the last author of these files is named “Challenger” and that both files were created on the same date. This information enables us to dig down further by querying additional files matching this metadata! All we have to do is click the “Mickey” field and VirusTotal will create the query for us.
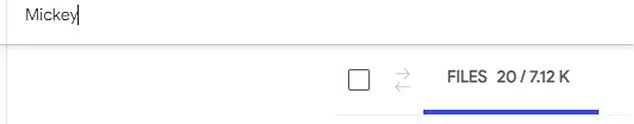
Yuck, 7k results! It appears that lazily just clicking that field returns all files within VirusTotal that contain the sequence “Mickey” within their content or metadata. That is unmanageable and, therefore, not useful. But we can easily solve that!
Let’s refine the query by looking exclusively at metadata and further restrict the search by limiting it to document files containing both “Mickey” and “Challenger”.
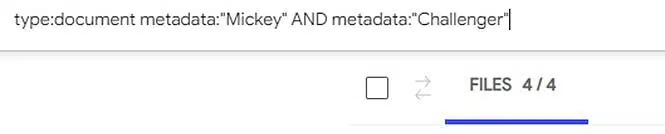
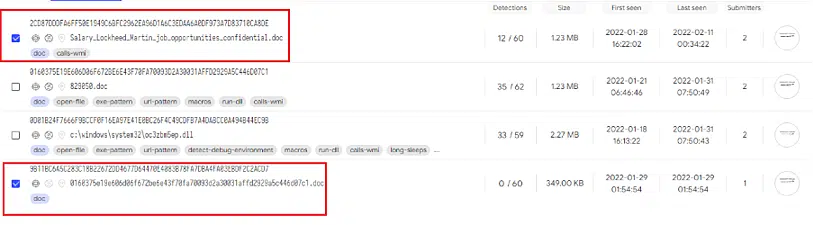
That worked! Only 4 files! When reviewing the file list, we see that we have uncovered 2 additional files that, though they are part of the malicious Lazarus campaign, were not listed in the blog post.
Using VirusTotal to Uncover Malicious URLs
Another technique we can use is combining Shodan, Virus Total, and URLScan to locate malicious URLs. For this example, we will follow APT27 tracks, with this Trend Micro article about the Iron tiger APT update. The article contains a particularly interesting observation:
If we query all the scanned URLs in VirusTotal that contain this URI sequence, we can potentially find new IoC’s, and if not, we can create a rule which tracks this kind of events using the YARA module integrated into VirusTotal. That second option will be explored in detail in a future post, but, for now, we will first go to VirusTotal’s “advanced” tab search and click the URL tab.
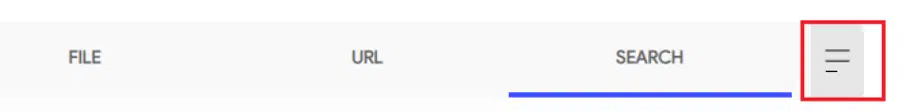
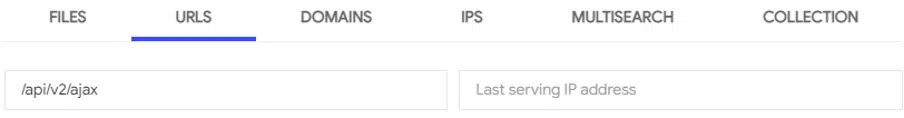
There, we insert the /api/v2/ajax string sequence in the “URL Contains” field and click search.
And we find 10 URLS! Including one that is not referenced within the blog post!
This is an actual C2 that belongs to APT27 and should be added to your own IoC list.
Using Shodan to Locate Malicious Infrastructure
Now, let’s see how we can leverage shodan.io to expand on these findings. Shodan is an online service that scans the internet. Shodan lists and indexes its findings in its ever-expanding database that contains data of various kinds returned from the performed scans. Even better, unless you are planning to perform API queries on the raw data returned from the scans, most of the premium features are free.
This data can be filtered by returned responses from services on the scanned servers, SSL certificates, ASN names, IP Blocks, and so on. As we will see, it will prove very useful to extracting additional IoC’s and signing malicious infrastructure for future hunting.
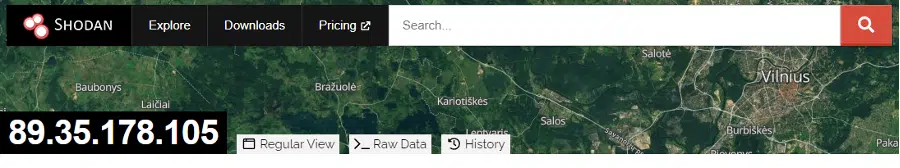
For this example, I decided to use Shodan to query the confirmed malicious IPs I extracted from the blog. Let’s look at the response that is returned.

Here we can see that a February 9th scan performed on the C2 on TCP port 443 returned a 500 Internal Server Error response with zero content. This is actually quite common for HyberBro (APT 27 malware) C2s. As 500 internal HTTP errors should return body content – this can be confirmed by looking at additional HyperBro C2 servers.
As you can see, I marked a number sequence in a red square. This is actually the hash returned from the scan body and it can be queried against shodan.io to find more servers returning this hash from their responses – let's click the hash.
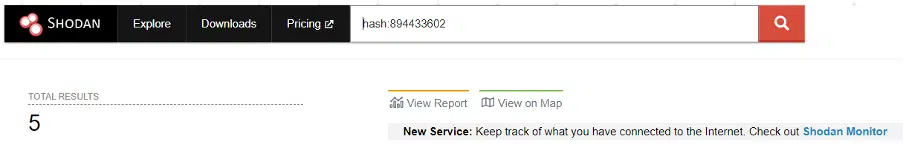
This yields additional HyperBro C2 servers that can be added to your IoC list!
Using URLScan to Locate Malicious Infrastructure
Finally, another service that can be used to find additional infrastructure is URLScan.IO –

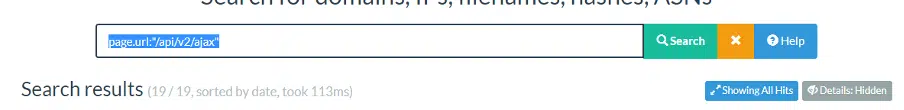
URLScan is a web sandbox, it scans URLs and returns their behavior in a detailed report. We can perform the same query VirusTotal against URLScan by clicking the search tab and typing page.url:"/api/v2/ajax" to return all the scans which contained this URI:
We found 19 results that can be filtered on your current IoC list to see if any new C2 can be added to it.
Automating IoC Updates for Faster Threat Response
This concludes my first Threat Intelligence guide,I hope this provides you with quick and easy ways to expand on your own IoC list and will write more tips in the near future.
If you're looking to further streamline and automate the validation of immediate threats, Cymulate’s Immediate Threats Validation module offers continuous, automated assessments using real-time threat simulations. By proactively validating your defenses against newly emerging threats, Cymulate ensures you're always ahead of attackers—without the manual effort!