Frequently Asked Questions
Data Exfiltration & DLP Challenges
What is data exfiltration and why is it a growing concern for organizations?
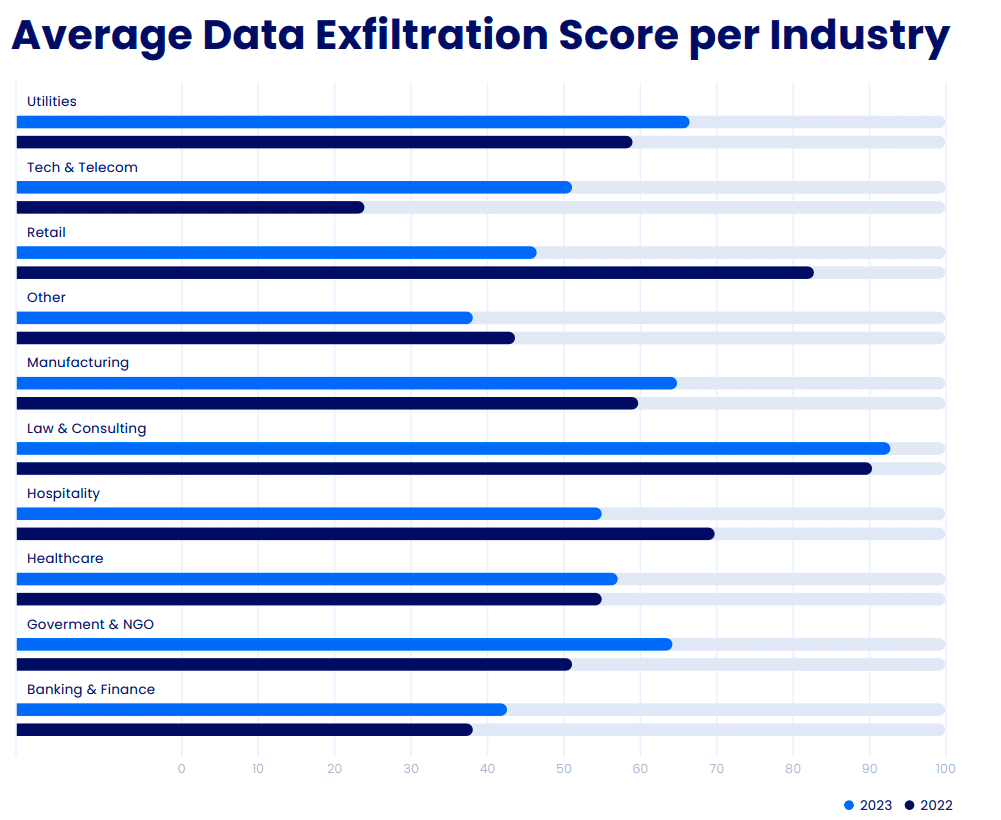
Data exfiltration refers to the unauthorized transfer of sensitive data from an organization. According to the Cymulate 2024 State of Exposure Management & Security Validation report, the average data exfiltration risk score has increased since 2021, highlighting the growing threat and the need for organizations to reassess their data loss prevention (DLP) strategies.
How does Cymulate measure data exfiltration risk?
Cymulate uses a proprietary 0 to 100 scoring method based on industry standards such as the MITRE ATT&CK® Framework and NIST Special Publication 800-50 to measure control effectiveness and baseline security posture, including data exfiltration risk.
Why are traditional DLP tools not providing adequate protection?
Traditional DLP tools often rely on predefined rules and patterns, which are increasingly ineffective against modern, sophisticated attack techniques. Attackers continuously evolve their methods to evade these defenses, and traditional DLP solutions struggle to keep up with encrypted traffic, data volume growth, and integration with new technologies.
What are the main challenges organizations face with DLP solutions today?
Key challenges include the evolving threat landscape, the encryption paradox (where attackers use encryption to hide malicious activity), the exponential growth of data (data deluge dilemma), and integration and compatibility issues with modern cloud and SaaS environments. These factors make it difficult for traditional DLP systems to provide comprehensive protection.
How does encryption impact data exfiltration detection?
While encryption enhances privacy and security for legitimate data, attackers now use encryption to mask illicit activities, making it harder for traditional DLP tools to distinguish between benign and malicious traffic. This increases the need for advanced solutions capable of analyzing encrypted data flows.
What role do insider threats play in data exfiltration risks?
Insider threats, whether accidental or intentional, constitute a significant percentage of data breaches. Organizations must focus on both external and internal risks, as insiders can bypass traditional controls and contribute to data exfiltration incidents.
How can organizations proactively address data exfiltration risks?
Organizations should adopt a proactive stance by regularly updating security policies, conducting thorough risk assessments, ensuring continuous monitoring, and fostering a culture of security awareness among employees. Continuous validation and real-time analysis are also critical for effective DLP strategies.
Why is continuous assessment important for data loss prevention?
Continuous assessment ensures that security controls remain effective against evolving threats and compliance requirements. Regular validation exercises help identify vulnerabilities and provide actionable insights for strengthening defenses before attackers can exploit them.
How does detection engineering enhance data exfiltration defense?
Detection engineering extends beyond prevention by enabling organizations to detect and respond to data exfiltration attempts in real-time. It involves building, tuning, and testing detection rules to swiftly identify and mitigate threats, minimizing potential damages.
What is the benefit of validating DLP controls with Cymulate?
Validating DLP controls with Cymulate helps organizations rigorously test their defenses against evolving threats, identify potential gaps, and receive actionable insights for improvement. This proactive approach ensures that security measures perform as expected and remain effective over time.
Features & Capabilities
What are the key capabilities of Cymulate's platform?
Cymulate offers continuous threat validation, unified exposure management, attack path discovery, automated mitigation, AI-powered optimization, complete kill chain coverage, ease of use, and an extensive threat library with over 100,000 attack actions aligned to MITRE ATT&CK and updated daily.
How does Cymulate support detection engineering?
Cymulate enables organizations to build, tune, and test SIEM, EDR, and XDR detection rules, improving mean time to detect and respond to threats, including data exfiltration attempts.
Does Cymulate integrate with other security technologies?
Yes, Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a complete list, visit the Partnerships and Integrations page.
How does Cymulate help organizations prioritize exposures?
Cymulate validates exploitability and ranks exposures based on prevention and detection capabilities, business context, and threat intelligence, enabling organizations to focus on the most critical vulnerabilities.
What is Cymulate's approach to continuous threat validation?
Cymulate provides 24/7 automated attack simulations to validate security defenses in real-time, ensuring organizations stay ahead of emerging threats and maintain a strong security posture.
How does Cymulate's platform support operational efficiency?
By automating security validation processes, Cymulate allows security teams to focus on strategic initiatives, leading to a 60% increase in team efficiency and saving up to 60 hours per month in testing new threats (source: customer success metrics).
What is the benefit of Cymulate's extensive threat library?
Cymulate's threat library includes over 100,000 attack actions aligned to MITRE ATT&CK and is updated daily, ensuring organizations can test their defenses against the latest tactics, techniques, and procedures used by attackers.
How easy is it to implement Cymulate?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive interface and ease of use. For example, Raphael Ferreira, Cybersecurity Manager, stated, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture."
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams in organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing.
What measurable outcomes have customers achieved with Cymulate?
Customers have reported outcomes such as a 52% reduction in critical exposures, a 60% increase in team efficiency, and an 81% reduction in cyber risk within four months (source: Hertz Israel case study).
How does Cymulate help organizations comply with regulatory requirements?
Cymulate supports compliance by continuously validating security controls, providing quantifiable metrics, and aligning with industry standards such as MITRE ATT&CK, NIST, and ISO certifications. This helps organizations demonstrate due diligence and meet regulatory obligations.
Are there case studies showing Cymulate's impact on data exfiltration risk?
Yes, for example, Hertz Israel reduced cyber risk by 81% in four months by addressing gaps in visibility and control with Cymulate. More case studies are available on the Cymulate Customers page.
How does Cymulate address the needs of different security roles?
Cymulate tailors its solutions for CISOs (providing metrics and insights), SecOps teams (automating validation and improving efficiency), red teams (offensive testing with a large attack library), and vulnerability management teams (prioritizing and validating exposures). Each role benefits from features aligned to their specific challenges.
What are some common pain points Cymulate helps solve?
Cymulate addresses fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation, operational inefficiencies in vulnerability management, and post-breach recovery challenges.
How does Cymulate help with cloud security validation?
Cymulate integrates with cloud security solutions such as AWS GuardDuty, Check Point CloudGuard, and Wiz to validate cloud security controls, ensuring comprehensive protection across hybrid and cloud environments.
What is the primary purpose of Cymulate's platform?
The primary purpose of Cymulate is to help organizations proactively validate their cybersecurity defenses, identify vulnerabilities, and optimize their security posture to stay ahead of emerging threats and improve overall resilience.
Security, Compliance & Company Information
What security and compliance certifications does Cymulate hold?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating adherence to industry-leading security and privacy standards. More details are available on the Security at Cymulate page.
How does Cymulate ensure data security and privacy?
Cymulate ensures data security through encryption in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and a strict Secure Development Lifecycle (SDLC) with continuous vulnerability scanning and third-party penetration tests.
Is Cymulate GDPR compliant?
Yes, Cymulate incorporates data protection by design and has a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO), ensuring GDPR compliance.
What is Cymulate's mission and vision?
Cymulate's mission is to transform cybersecurity practices by enabling organizations to proactively validate their defenses, identify vulnerabilities, and optimize their security posture. The vision is to create a collaborative environment for lasting improvements in cybersecurity strategies. Learn more on the About Us page.
Where can I find Cymulate's latest news, research, and resources?
You can stay updated through the Cymulate blog, newsroom, and Resource Hub, which offer insights, thought leadership, and product information.
Does Cymulate provide educational resources like a glossary or webinars?
Yes, Cymulate offers a cybersecurity glossary, webinars, e-books, and a knowledge base with technical articles and videos to help users stay informed and optimize their security practices.
Pricing & Implementation
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's requirements. Pricing depends on the chosen package, number of assets, and scenarios selected. For a detailed quote, you can schedule a demo with the Cymulate team.
How long does it take to implement Cymulate?
Cymulate is designed for rapid deployment, with most customers able to start running simulations almost immediately after setup due to its agentless architecture and minimal configuration requirements.
What support options are available for Cymulate customers?
Cymulate provides comprehensive support, including email support ([email protected]), real-time chat support, a knowledge base, webinars, e-books, and an AI chatbot for quick answers and guidance.