Frequently Asked Questions
Product Overview & Adversarial Exposure Validation
What is adversarial exposure validation (AEV)?
Adversarial exposure validation (AEV) is a unified approach to continuously testing and improving your organization's cyber resilience. AEV tools simulate real-world adversaries across your network, cloud, endpoints, and applications, validate both offensive and defensive capabilities, prioritize exploitable vulnerabilities, and provide actionable mitigation guidance, including automated control updates and custom detection rules.
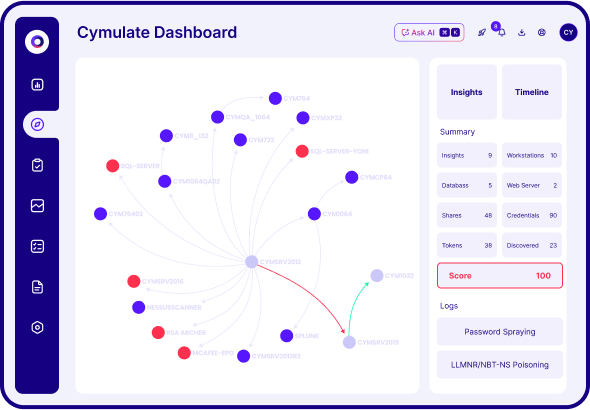
How does Cymulate's adversarial exposure validation work?
Cymulate's adversarial exposure validation continuously evaluates your security posture by simulating attacker campaigns across networks, endpoints, and cloud environments. It validates controls in real time, maps exploitable attack paths, and provides actionable insights to help you uncover and remediate security gaps before attackers can exploit them.
What are the main benefits of using adversarial exposure validation tools?
Implementing adversarial exposure validation tools provides actionable insights and continuous assurance that security controls are effective against real-world threats. Key benefits include maximized threat prevention, optimized detection and response, scaled offensive testing, improved exposure awareness, and enhanced collaboration between red, blue, and purple teams.
How does Cymulate simulate attacker campaigns?
Cymulate allows you to run full attack simulations across networks, endpoints, and cloud environments, emulating how an adversary would move and exploit weaknesses. This helps organizations see how vulnerabilities and misconfigurations could be combined to reach critical assets, providing a clear view of risk exposure.
What environments and security controls can Cymulate validate?
Cymulate validates a wide range of security controls and environments, including endpoint security (AV/EDR), cloud security (CWPP), containers/Kubernetes, secure email gateways, secure web gateways, web application firewalls, network security (IPS/IDS), data loss prevention, and SIEM/SOAR detections. This comprehensive coverage ensures your entire security stack is tested against real threats.
How does Cymulate validate controls in real time?
Cymulate measures whether existing security tools, monitoring, and detection controls actually stop or detect attacks as expected. This real-time validation provides actionable insights for remediation and helps prioritize exposures that matter most to your organization.
What is the advanced attack scenario workbench in Cymulate?
The advanced attack scenario workbench in Cymulate lets you build or customize attack chains and campaigns from a library of over 100,000 actions. This enables you to match your environment and threat model, ensuring realistic and relevant testing.
How does Cymulate support purple teaming collaboration?
Cymulate maps attacks to security logs, alerts, and response playbooks, allowing red and blue teams to work together and improve overall cyber resilience. Shared dashboards, scorecards, and heatmaps help align efforts and drive measurable improvements.
What is automated mitigation in Cymulate?
Automated mitigation in Cymulate enables you to push immediate remediation or custom detection rules to endpoints, SIEM, and XDR systems for validated threats. This reduces exposure faster and more safely, ensuring critical assets are protected even against un-patchable vulnerabilities.
How does Cymulate help with validating un-patchable exposures?
Cymulate confirms that security controls effectively mitigate risks for vulnerabilities that cannot be patched, providing proof of protection for critical assets and supporting compliance and audit requirements.
Features & Capabilities
What features does Cymulate offer for exposure validation?
Cymulate offers continuous threat validation, unified platform capabilities (BAS, CART, Exposure Analytics), attack path discovery, automated mitigation, AI-powered optimization, complete kill chain coverage, ease of use, and an extensive threat library with over 100,000 attack actions updated daily.
How does Cymulate optimize threat detection?
Cymulate continuously tests detection mechanisms to ensure alerts, logs, and monitoring accurately capture attack activity. This helps organizations fine-tune their detection systems and improve mean time to detect threats.
What integrations does Cymulate support?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a complete list, visit the Partnerships and Integrations page.
How does Cymulate's AI-powered optimization work?
Cymulate uses machine learning to deliver actionable insights for prioritizing remediation efforts, helping organizations focus on high-risk vulnerabilities and optimize security controls for maximum impact.
How does Cymulate support continuous innovation?
Cymulate updates its SaaS platform every two weeks with new features, such as AI-powered SIEM rule mapping and advanced exposure prioritization, ensuring customers always have access to the latest capabilities.
How does Cymulate compare to traditional penetration testing?
Unlike point-in-time penetration testing, Cymulate provides automated, continuous exposure validation, offering a more realistic and effective defense by validating controls against the latest adversarial techniques and providing ongoing assurance of security posture. Learn more in our guide.
How does exposure validation improve vulnerability management?
Exposure validation helps security teams cut through the noise of countless vulnerabilities by validating which risks are truly exploitable. This enables teams to prioritize their efforts and focus on mitigating real threats to the organization. Read more in our guide.
What are the key benefits of implementing threat exposure validation?
The key benefits identified in Cymulate's report include: 47% of organizations experienced improved mean time to detection, 40% saw increased threat resilience against the latest threats, and 37% achieved continuous validation and tuning of security controls. Source: Threat Exposure Validation Impact Report.
Use Cases & Customer Success
Who can benefit from Cymulate's adversarial exposure validation?
Cymulate's solutions are designed for CISOs and security leaders, SecOps teams, red teams, and vulnerability management teams in organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. The platform delivers measurable improvements in threat resilience and operational efficiency for each persona.
What problems does Cymulate solve for security teams?
Cymulate addresses challenges such as fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation capabilities, operational inefficiencies in vulnerability management, and post-breach recovery challenges. The platform unifies exposure data, automates validation, and provides actionable insights to improve security posture.
Are there real-world examples of Cymulate's impact?
Yes. For example, Hertz Israel reduced cyber risk by 81% in four months using Cymulate. Other case studies include a sustainable energy company scaling penetration testing, a credit union optimizing SecOps, and Nemours Children's Health improving detection in hybrid and cloud environments. See more at Cymulate Customers.
How does Cymulate help different security personas?
Cymulate tailors its solutions for CISOs (providing metrics and insights for investment justification), SecOps teams (automating processes and improving efficiency), red teams (offensive testing with a vast attack library), and vulnerability management teams (automating validation and prioritization). Each persona receives targeted capabilities to address their unique challenges.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive, user-friendly interface and ease of implementation. Testimonials highlight the platform's simplicity, actionable insights, and accessible support, making it effective for users of all skill levels. See more reviews at Cymulate Reviews.
How quickly can Cymulate be implemented?
Cymulate is designed for rapid deployment, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately, with comprehensive support and educational resources available to ensure a smooth onboarding process.
How does Cymulate help with post-breach recovery?
Cymulate enhances visibility and detection capabilities after a breach, enabling organizations to recover faster by identifying and closing security gaps that may have been exploited during an incident.
How does Cymulate support regulatory and compliance requirements?
Cymulate helps organizations demonstrate measurable, proactive cyber resilience for standards like NIS2, DORA, and industry best practices by providing continuous validation, evidence-based reporting, and proof of control effectiveness.
Security, Compliance & Trust
What security and compliance certifications does Cymulate hold?
Cymulate holds several key certifications, including SOC2 Type II (covering security, availability, confidentiality, and privacy), ISO 27001:2013 (Information Security Management), ISO 27701 (Privacy Information Management), ISO 27017 (Cloud Services Security Controls), and CSA STAR Level 1. These certifications demonstrate Cymulate's commitment to industry-leading best practices. See details at Security at Cymulate.
How does Cymulate ensure data security?
Cymulate ensures data security through encryption for data in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and a robust security program that includes secure development lifecycle, vulnerability scanning, and third-party penetration testing.
Is Cymulate GDPR compliant?
Yes, Cymulate incorporates data protection by design and has a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO), ensuring GDPR compliance and robust privacy practices.
What product security features does Cymulate offer?
Cymulate's platform includes mandatory 2-Factor Authentication (2FA), Role-Based Access Controls (RBAC), IP address restrictions, and TLS encryption for its Help Center, ensuring strong access control and data protection.
Pricing & Plans
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's requirements. The subscription fee is determined by the chosen package, number of assets, and scenarios selected for testing and validation. For a detailed quote, you can schedule a demo with the Cymulate team.
Competition & Market Position
How does Cymulate differ from other adversarial exposure validation solutions?
Cymulate stands out by unifying Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics into a single platform. It offers continuous, evidence-based insights, automated mitigation, actionable prioritization, and supports collaboration across red, blue, and purple teams. Customers have reported measurable outcomes, such as a 52% reduction in critical exposures and an 81% reduction in cyber risk within four months.
What industry recognition has Cymulate received?
Cymulate has been named a Market Leader for Automated Security Validation by Frost & Sullivan and a Customers' Choice in the 2025 Gartner Peer Insights for Adversarial Exposure Validation. These recognitions reflect Cymulate's leadership and customer satisfaction in the security validation space.
Implementation & Support
What support resources are available for Cymulate customers?
Cymulate provides comprehensive support, including email support, real-time chat, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers and security insights. These resources help customers maximize the value of the platform.
How does Cymulate ensure ease of use for new users?
Cymulate is designed to be intuitive and easy to use, with an agentless deployment model, minimal setup requirements, and a user-friendly dashboard. Customers can quickly start running simulations and receive actionable insights with just a few clicks.