Frequently Asked Questions
Cybersecurity Effectiveness Report & Key Findings
What is the Cymulate Cybersecurity Effectiveness Report and what makes it unique?
The Cymulate Cybersecurity Effectiveness Report is an annual analysis that summarizes findings from all Cymulate customers' security assessments. It is unique because it outlines security gaps and events not detected by security controls, covering attack surface exposures, vulnerabilities, and attack paths in a single study. In 2022, the report was based on the equivalent of over 197 years of offensive cybersecurity testing within production environments, providing a comprehensive view of global cybersecurity resilience across industries and company sizes. Read the full report.
What are the most significant findings from the 2022 Cymulate Cybersecurity Effectiveness Report?
Key findings include: 40% of organizations have vulnerabilities with available patches for over two years; organizations often prioritize remediation based on media headlines rather than actual risk; data protection effectiveness is declining, with cloud service-related assessments scoring a high-risk average of 70; and 92% of the top 10 exposures are related to domain and email security. The report also shows that continuous Breach and Attack Simulation significantly improves cyber resiliency, lowering EDR risk scores from high to low in less than a year when recommended mitigations are implemented.
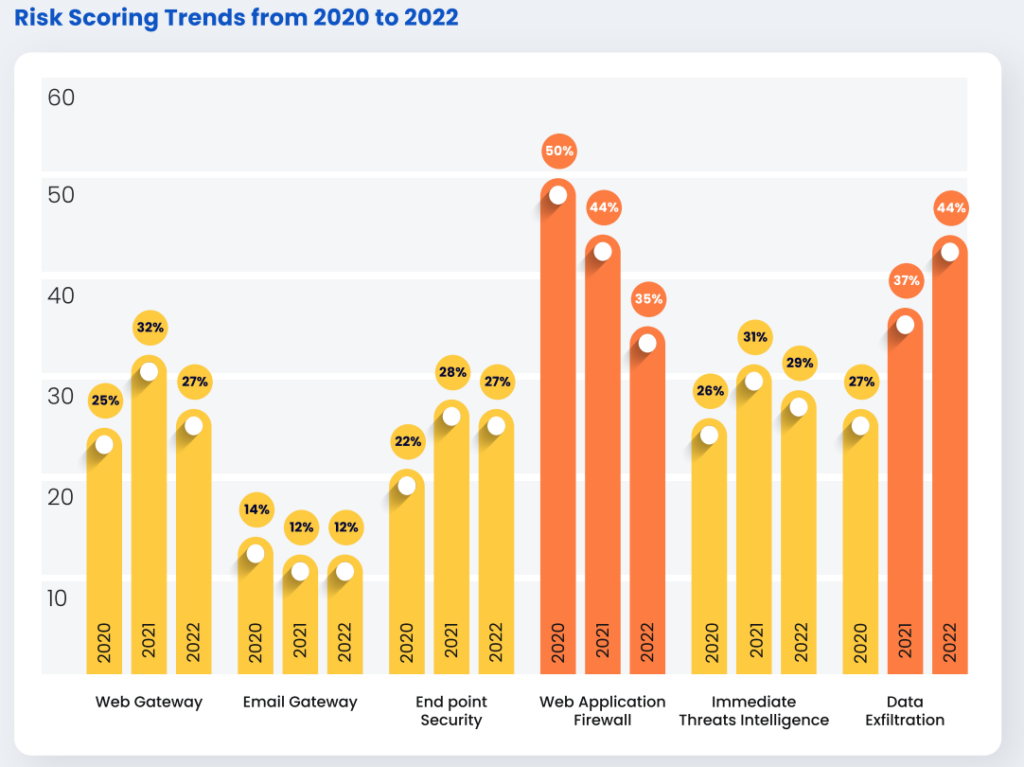
How does Cymulate measure the effectiveness of security controls?
Cymulate measures security control effectiveness by running continuous, automated attack simulations across customer environments. The platform identifies which threats and vulnerabilities are not detected by existing controls, providing actionable insights into where defenses are failing and how to improve them. The 2022 report highlights that Data Leakage Prevention (DLP) controls scored the lowest, especially against exfiltration methods like email and cloud storage uploads.
What types of exposures and vulnerabilities are most commonly detected by Cymulate?
The most common exposures detected are related to domain security (59.3%) and email security (32.8%). Other frequent issues include unpatched CVEs, misconfigured Identity and Access Management (IAM) and Privilege Access Management (PAM), and exposed digital assets identified by the External Attack Surface Management (EASM) module.
How does headline-driven remediation impact cybersecurity risk?
Organizations often prioritize remediation based on threats that receive media attention rather than those that pose the greatest actual risk. This can lead to misallocation of resources and neglect of more pressing vulnerabilities, as highlighted in the 2022 Cymulate report.
What are the main challenges with Data Leakage Prevention (DLP) controls according to Cymulate's research?
The main challenges with DLP controls are their complexity, the expense of implementation, and reliance on cloud storage platforms like AWS S3 and Azure Websites for business operations. These factors make it difficult to prevent data exfiltration via email and cloud uploads, resulting in DLP scoring the lowest among tested controls in 2022.
What types of Business Email Compromise (BEC) attacks are most common?
Common BEC attacks include CEO fraud (impersonating executives to request fund transfers), account compromise (using hijacked employee accounts to request payments), false invoice schemes (impersonating suppliers), attorney impersonation, and PII misappropriation (targeting HR or other departments for sensitive data).
How does Cymulate help organizations address emerging threats?
Cymulate's research team operationalizes safe testing of new threats as they emerge daily, allowing organizations to test their resilience immediately without needing to research, code, or prepare for the threats themselves. This proactive approach ensures that defenses are validated against the latest attack techniques.
What are the primary methods of compromise used by attackers in 2022?
The primary methods of compromise observed include phishing, water hole attacks, and supply-chain attacks. Attackers often use known tools such as Cobalt Strike, Sliver framework, APT41, Nmap, SQLmap, and Acunetix, with motives typically centered on financial gain or espionage.
How does Cymulate's External Attack Surface Management (EASM) module help organizations?
The EASM module discovers exposed digital assets that adversaries could exploit, providing organizations with visibility into their external attack surface and helping them prioritize remediation of the most critical exposures.
Where can I read the full Cymulate Cybersecurity Effectiveness Report?
You can access the full report at Cymulate’s report page for detailed findings, top vulnerabilities, and business implications.
How does Cymulate empower organizations to improve their security posture?
Cymulate empowers organizations by providing continuous assessment and validation of their security posture through threat simulation and comprehensive security assessments. This enables organizations to identify gaps, validate controls, and stay ahead of cyber threats with actionable insights and innovative tools.
What is the impact of continuous Breach and Attack Simulation on cyber resiliency?
Continuous Breach and Attack Simulation, as highlighted in the 2022 report, significantly improves cyber resiliency. Organizations that implement recommended mitigations based on simulation results can lower their EDR risk scores from high to low in less than a year, demonstrating measurable improvements in defense effectiveness.
What are the most common digital assets exposed according to Cymulate's EASM findings?
The EASM module frequently discovers exposed assets such as misconfigured domains, open ports, outdated software, and publicly accessible sensitive data, all of which can be exploited by attackers if not properly secured.
How does Cymulate help organizations prioritize remediation efforts?
Cymulate provides actionable insights by identifying which vulnerabilities and exposures are most critical based on exploitability, business context, and threat intelligence, enabling organizations to focus remediation efforts where they will have the greatest impact.
What are the business implications of the findings in the Cymulate Effectiveness Report?
The report’s findings highlight the need for organizations to move beyond reactive, headline-driven security and adopt continuous validation and remediation strategies. This approach reduces risk, improves compliance, and ensures resources are allocated to address the most significant threats and exposures.
How can organizations use Cymulate to test their resilience against new threats?
Organizations can leverage Cymulate’s continuously updated threat library and automated simulations to safely test their defenses against the latest attack techniques, ensuring they are prepared for emerging threats without manual research or preparation.
What resources are available for learning more about Cymulate's research and findings?
You can explore Cymulate’s blog, webinars, and resource hub for the latest research, expert insights, and practical guidance. Featured resources include the full Cybersecurity Effectiveness Report, webinars like 'What Your Controls Aren’t Telling You', and the Threat Exposure Validation Impact Report 2025.
How does Cymulate support organizations of different sizes and industries?
Cymulate’s platform is designed to provide value to organizations of all sizes and across various industries, offering scalable solutions that address unique security challenges and compliance requirements. The 2022 report includes data from a diverse range of sectors and company sizes.
What is the role of Cymulate's research team in enhancing security validation?
The Cymulate research team continuously monitors the threat landscape and operationalizes safe testing of new threats, ensuring that customers can validate their defenses against the latest attack techniques as soon as they emerge.
Features & Capabilities
What are the core features of the Cymulate platform?
Cymulate offers a unified platform that combines Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics. Key features include continuous threat validation, attack path discovery, automated mitigation, AI-powered optimization, complete kill chain coverage, and an extensive threat library with over 100,000 attack actions updated daily. Learn more.
Does Cymulate integrate with other security technologies?
Yes, Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a complete list, visit our Partnerships and Integrations page.
How does Cymulate help with exposure prioritization and remediation?
Cymulate validates the exploitability of exposures and ranks them based on prevention and detection capabilities, business context, and threat intelligence. This enables organizations to focus on the most critical vulnerabilities and optimize remediation efforts. Learn more.
What are the benefits of using Cymulate for continuous threat validation?
Benefits include up to a 52% reduction in critical exposures, a 20-point improvement in threat prevention, a 60% increase in team efficiency, and an 81% reduction in cyber risk within four months, as reported by customers. Continuous validation ensures organizations stay ahead of emerging risks and make data-driven security decisions.
How easy is it to implement Cymulate and start using it?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately, and comprehensive support is available via email, chat, and a knowledge base. Schedule a demo to learn more.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive, user-friendly interface and actionable insights. Testimonials highlight the platform's simplicity, quick implementation, and accessible support. For example, Raphael Ferreira, Cybersecurity Manager, said, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture." Read more customer stories.
What security and compliance certifications does Cymulate hold?
Cymulate holds several industry-leading certifications, including SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. These certifications demonstrate Cymulate's commitment to robust security, privacy, and compliance standards. Learn more.
How does Cymulate ensure data security and privacy?
Cymulate ensures data security through encryption in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and a strict Secure Development Lifecycle (SDLC). The platform also includes mandatory 2-Factor Authentication (2FA), Role-Based Access Controls (RBAC), and GDPR compliance with a dedicated privacy and security team. More details.
What is Cymulate's pricing model?
Cymulate uses a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and scenarios selected for testing. For a personalized quote, schedule a demo with the Cymulate team.
Who is the target audience for Cymulate's platform?
Cymulate is designed for CISOs and security leaders, SecOps teams, Red Teams, and Vulnerability Management teams in organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. Learn more about roles.
How does Cymulate compare to other security validation platforms?
Cymulate stands out with its unified platform that integrates BAS, CART, and Exposure Analytics, continuous 24/7 threat validation, AI-powered optimization, and an extensive threat library. It is recognized for ease of use, measurable outcomes, and continuous innovation, updating its SaaS platform every two weeks. See comparisons.
What pain points does Cymulate address for security teams?
Cymulate addresses fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation, operational inefficiencies in vulnerability management, and post-breach recovery challenges. See case studies.
Are there case studies showing Cymulate's impact?
Yes, for example, Hertz Israel reduced cyber risk by 81% in four months, and a sustainable energy company scaled penetration testing cost-effectively with Cymulate. More case studies are available at Cymulate’s customer stories.
How does Cymulate tailor solutions for different security roles?
Cymulate provides quantifiable metrics and insights for CISOs, automates processes for SecOps teams, offers automated offensive testing for Red Teams, and enables efficient vulnerability prioritization for Vulnerability Management teams. Learn more about tailored solutions.
Where can I find Cymulate's blog, newsroom, and resource hub?
You can find the latest threats, research, and company news on our blog, newsroom, and resource hub.
How can I stay updated with Cymulate's latest news and research?
Stay informed by visiting the company blog for the latest threats and research, and the newsroom for media mentions and press releases.
Where can I find information about Cymulate's events and webinars?
Information about live events and webinars is available on our Events & Webinars page.
What is Cymulate's mission and vision?
Cymulate’s mission is to transform cybersecurity practices by enabling organizations to proactively validate defenses, identify vulnerabilities, and optimize their security posture. The vision is to create a collaborative environment for lasting improvements in cybersecurity strategies. Learn more.