5 Black Hat 2022 Takeaways (and One Bonus!)
Black Hat 2022 was unforgettable! The energy bursting out of customers, partners, journalists, panelists, vendors, and visitors was exhilarating. But the general enthusiasm was only the cherry on the cyber cake! The breadth and depth of the conversations with key stakeholders shed a bright light on today's most pressing concerns. I picked out the five most meaningful ones here:
1. The market is actively seeking validation
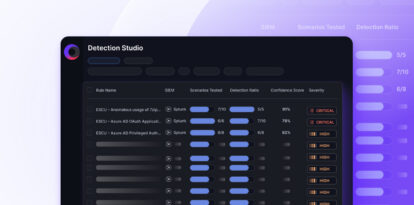
It seems that the awareness of the benefits of automated attack simulations to validate the efficacy of security controls is gaining traction.
The value of classic BAS (Breach & Attack Simulation) solutions to finetune security control configuration and optimize efficacy is far better understood today. This led to more in-depth questions regarding the capability of running end-to-end scenarios that mimic an attacker trying different options to overcome attack-routes obstacles.
Yet, while the value of classic BAS is far more accepted today than before as the category has gained traction in the last year, organizations understand that there is a broader context to consider is not limited to security controls efficacy validation. A comprehensive security validation process should also include other elements such as attack surface, IT policies, employee awareness, patch program validation, etc.
2. Simplicity rules!
The main concern of potential validation adopters is complexity. Even featured keynote speaker Chris Krebs, former director of the U.S. Cybersecurity and Infrastructure Security Agency, or CISA, drew attention to the increased risks stemming from increased complexity in tech stacks during his keynote speech.
The beauty of BAS technology, when integrated with the existing security stack, is that it very rapidly and easily shows where redundant capability unnecessarily bloats the data inflow with zero benefits, pinpoints where configuration finetuning would yield the highest efficiency return – which helps efficiently prioritize remediation efforts.
Reducing complexity is also facilitated by the ease of access to relevant data and the ability to visualize it in various formats at a click.
Cymulate’s BAS three-click installation process, coupled with the dynamic dashboards, customizable reports, and integrated ticketing, generated considerable interest ?.
3. Keeping the board informed
Technical concerns are not the only ones. Compelling, comprehensive, and timely communication is a growing concern as executives are becoming more aware of the criticality of cybersecurity and how it directly affects their bottom line.
Access to quantified data and security scores based on the actual ratio of attack scenarios detected and/or stopped by the defensive stack is far easier to understand than baselines established through estimates of abidance to best practices.
Similarly, the ability to continuously assess and reassess gives a progression of the security ratio, which facilitates communicating the value of cybersecurity investments and identifying security drift at its onset instead of far later.
Cymulate’s potent analytics system with dynamic default and customizable dashboards and reports covers the full array of security posture domains, reflects a comprehensive view of the investments made and their success rate, and monitors drift /regression over time.
4. Navigating the Blue Team Red Team divider
BAS users’ surprising feedback, aside from the expected benefits in security posture hardening, was how it improved the relationship between their in-house blue and red teams. How? When blue teams use automated validation and assessment capabilities, they can auto-validate the efficacy of their remediation efforts instead of risking being caught pants down by a smirking red team. On the other side of the divider, red teams have more time to focus on more challenging tasks and are happy giving pointers to blue teamers.
When also using the purple teaming framework, the collaboration between red and blue teams is further consolidated as they create advanced scenarios to increase the assessment depth for particularly sensitive segments.
5. Prioritization
In their “Calculating Risk in the Era of Obscurity: Reading Between the Lines of Security Advisories” presentation, Brian Gorenc, Senior Director, Trend Micro Zero Day Initiative, and Dustin Childs, Sr. Communications Manager, Trend Micro Zero Day Initiative, berated the misleading sense of security that might result from dutifully patching high CVSS scored vulnerability in priority.
Childs specifically warns against the dangers of falling back on CVSS-score-based prioritization, as it might - and does – lead to spending scarce resources on bugs with a very low likelihood of ever being exploited. He also warns against falling for the front-page title trends.
"An unauthenticated remote code execution (RCE) bug in an email server like Microsoft Exchange is going to generate a lot of interest from exploiting writers," he said. "An unauthenticated RCE bug in an email server like Squirrel Mail is probably not going to generate as much attention."
Though a healthy policy, relying on consistent and timely updated software versions might also induce a false sense of security. Childs criticizes the lack of comprehensiveness of many update releases that either fail to mention the exact CVE fixed and issue a blanket statement that the update fixes several security issues or mention ten fixed CVEs but 'forget' to mention the other 100 that are still to be patched, for example.
According to Childs and Golenc, overcoming the numerous patching issues boils down to in-context prioritization.
Attack Based Vulnerability Management (ABVM) prioritizes vulnerability management based on security flaws and actual exploitability evaluated through permeability to attack scenarios.
It takes into account not only the CVSS scores but also the efficacy of compensating security controls and the potential impact of an attacker taking advantage of the security flaw, including the odds that it could be leveraged to propagate within the network.

The Cymulate Team at Black Hat 2022
Bonus
These were our main takeaways from Black Hat, but, in addition, we saw significant interest from MSSPs (Managed Security Service Providers), as they look for ways to increase the value to their customers by proving that they continuously monitor the performance of their managed security services. The ability to easily access and share the data showing the risk reduction progress they achieved, document the improvements in detection and response, and meet the SLAs they are committed to. MSSPs using Cymulate enjoyed additional revenue streams while setting a competitive edge over other MSSPs, and all that with minimal effort.
Now that we are back from Black Hat and have collected invaluable feedback on our products, we will finetune the existing features and make sure to integrate the numerous insights we gathered into our stealth new product currently in development.