As many businesses and organizations transition to the cloud, cloud security has become a critical concern. What does this new threat landscape look like, and how can companies mitigate risk without freezing operations or having their business destroyed by an undetected attack? Answering these questions involves a thorough analysis of the current state of cloud security, identification of key challenges, and an understanding of the proactive measures available to mitigate risks.
What is Cloud Security Validation?
Cloud security validation is the process of assessing and verifying that the security measures and protocols implemented in a cloud and hybrid environment are working efficiently. This involves evaluating the effectiveness of security controls, identifying vulnerabilities, and ensuring compliance with relevant security standards and regulations. The goal is to make sure that data and applications hosted in the cloud are protected against unauthorized access, data breaches, and other cyber threats.
The Current State of Cloud Security
The IBM 2023 Cost of a Data Breach Report paints a vivid picture of the current state of cloud security. According to the report:
- 82% of breaches that involved data were stored in cloud environments. This includes 39% on multiple environments, 27% on public cloud, 16% on private cloud, with the remaining 18% on-premises.
- The cost of data breaches across multiple environments reached a staggering USD 4.75 million, the highest cost of the environments analyzed. This figure is 17.6% higher than the USD 3.98 million cost of data breaches in a private cloud environment, which was the lowest cost of the environments analyzed. The cost of data breaches across multiple environments also exceeded the average cost of a data breach of USD 4.45 million by a margin of 6.5%.
82% of breaches that involved data were stored in cloud environments
These numbers are not just statistics; they represent real-world challenges that organizations face every day. The longest time to identify and contain a breach involved data stored across multiple environments, taking 291 days. This interval exceeded the shortest time to identify and contain a breach—which was 235 days in a private cloud environment—by 56 days or 21.3%. It’s also worth noting that the use of multiple environments is the only model that exceeds the 2023 reported average time to identify and contain a data breach of 277 days by a margin of 14 days or 4.9%.
On the slightly more positive side, organizations using threat intelligence identified breaches 28 days faster.
The 2022 Snyk State of Cloud Security Report found that misconfigurations are the number one threat to cloud security. The report found that 80% of organizations have experienced a cloud security incident caused by misconfigurations. This alarming figure underscores the need for proactively identify and correct these misconfigurations before a malevolent actor exploits them.
Furthermore, the CSA State of SaaS Security: 2023 Survey Report indicates that 55% of organizations reported that they experienced an incident in the past two years, up 12% from the previous year. About a third (32%) of respondents stated that they hadn’t encountered a SaaS security incident within the same period, while 12% were unsure. These findings provide a snapshot of the ongoing battle against cyber threats and the need for continuous improvement in security practices.
Common Cloud Security Challenge
Navigating the cloud security landscape requires understanding the common challenges and their origins. Security teams responsible for validating cloud security and managing risk exposure often struggle to:
- Determine and measure risk: With a lack of centralized visibility to cloud deployments, VMs, EC2s, containers, shadow IT infrastructure, and more, security teams find it difficult to understand security posture and proactively manage risk. Exposure data is too often spread across siloed solutions and systems without business correlation.
- Manage misconfigurations and security controls: While vulnerabilities and exploits remain a concern, human mistakes and misconfigurations introduce gaps and weaknesses. These oversights create security gaps, allow improper access, spin up unmanaged assets, deviate from standard policies and take dangerous security control shortcuts.
- Manage identity and access: Identity and access management in the cloud is designed for flexibility and rapid change. This leads to over-privileged users and the potential for abuse and privilege escalation. This includes obfuscation techniques such as disabling cloud logging tools like AWS Cloudtrail, Azure Sentinel, and GCP Cloud Audit Logs.
- Keep up with a constantly evolving field: Cloud security is a rapidly evolving field, lacking an equivalent to the well-established on-prem security best practice. In many cases, this lack of established playbook requires security professionals to create untested ad-hoc practices and hope that they are secure.
The Need for Proactive Cloud Security Measures – Adopting a new approach
The first step to address the challenges above is to identify the underlying reasons. Those typically derive from these three main branches:
- Lack of Visibility and Control: Unlike traditional IT environments that provide complete visibility and control over the infrastructure, cloud environments imply sharing infrastructure with other tenants. This reduces visibility and control and requires shared responsibility in implementing security, which complexifies the process.
- New Attack Vectors: The cloud introduces new ways for attackers to move laterally within a network. Additionally, cloud providers often have access to customer data, adding another layer of complexity.
- Complexity: Cloud environments are inherently complex. Managing security across multiple cloud providers, each with its own security model, is a daunting task. Keeping up with the ever-changing threat landscape adds to the challenge.
Taking the Attacker’s View of Cloud
The dynamic nature of cloud environments, designed for flexibility and rapid change, necessitates proactive security to identify and mitigate potential threats before they pose a risk to the organization.
This proactive approach to cloud security enhances effectiveness by detecting and addressing security gaps before they can be exploited, rather than reacting to breaches after they occur, which can be difficult and costly to manage. Additionally, proactive measures support compliance with regulatory requirements, which increasingly emphasize resilience. Implementing such security validations also strengthens trust by demonstrating a commitment to safeguarding data, thereby enhancing an organization’s reputation.
Introducing the Cymulate Solution for Cloud Security Validation
The Cymulate exposure management and security validation platform offers a modular suite of cloud security solutions designed to meet the unique challenges of validating cloud security and improving cyber resilience.
- Cymulate ASM (Attack Surface Management)
- Discover Cloud Assets: Inventory VMs, storage objects, VPCs, entitlements, Kubernetes containers, and more across AWS, Azure, and GCP.
- Identify Misconfigurations: Both internal and external assets and deployments are covered, ensuring a comprehensive view of potential vulnerabilities.
- Cymulate BAS (Breach and Attack Simulation)
- Validate Core Controls: Test cloud assets against malicious behaviors, including those specific to cloud threats.
- Immediate Threats Validation: Stay ahead of emergent threat activity against cloud assets.
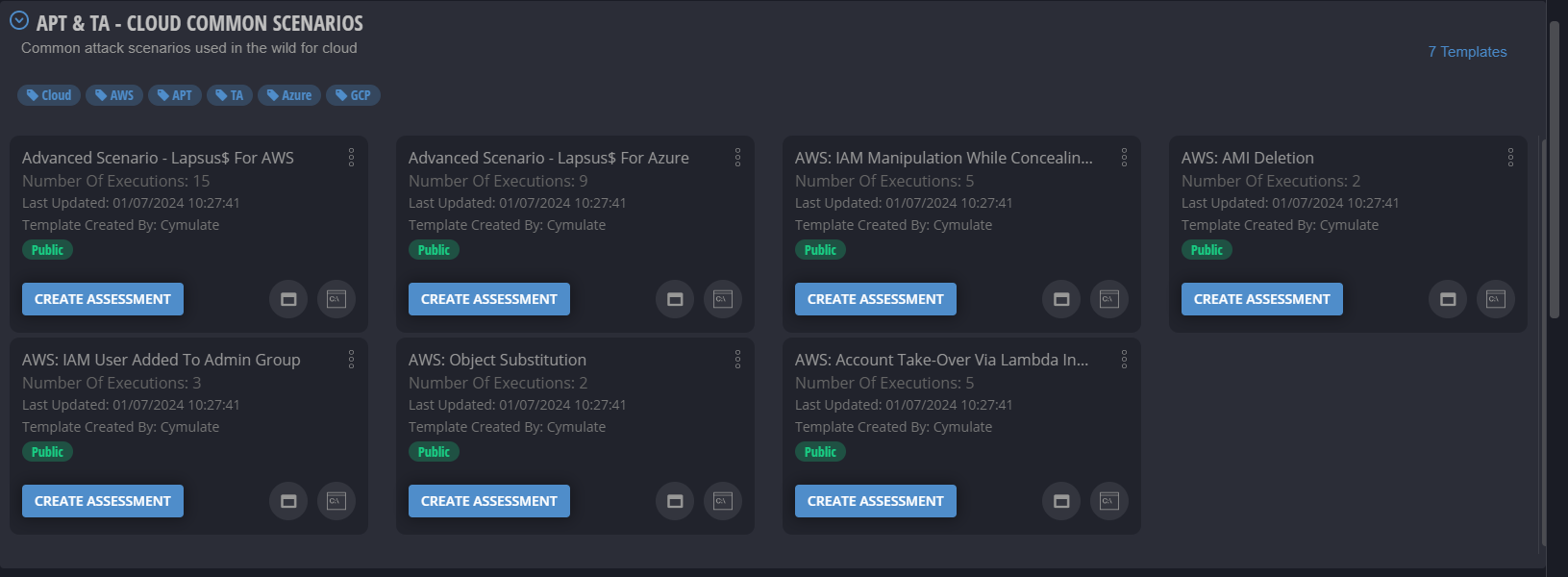
- Cymulate BAS – Advanced Scenarios
- Validate Best Practices: Ensure that cloud and Kubernetes policy configurations are aligned with industry standards.
- Open Framework: Create, store, modify, and execute both simple and sophisticated assessments using custom or out-of-the-box resources.
- Cymulate CART (Continuous Automated Red Teaming)
- Automated Network Penetration Testing: Validate potential propagation within the cloud and from cloud to on-prem and back.
- Cymulate Exposure Analytics (Exposure Analytics)
- Collect and Align Data: Integrate with cloud deployments, tools and controls to correlate third-party data with the findings from Cymulate ASM, BAS and CART
- Create risk-profiled asset inventory: Add business context by grouping cloud assets and environments to critical business functions and then measuring risk for each asset and business function.
- Prioritize Remediation: Focus on contextualized exposure risk correlating validated security gaps with business priorities.
- Measure and Baseline Security Resilience: Understand and track the security resilience for cloud deployments.
For a deeper understanding of cloud security and the solution for cloud security validation, book a demo with Cymulate today