CVE-2021-42287 & CVE-2021-42278: Active Directory Vulnerabilities That Demand Immediate Action
Beyond the far-reaching Apache Log4j vulnerability and the Log4Shell exploits, cybersecurity professionals must address another critical pair of vulnerabilities that pose a severe risk to enterprise security—CVE-2021-42287 & CVE-2021-42278.
These Microsoft vulnerabilities affect every Windows Server release and, when exploited together, allow unprivileged users to escalate privileges and gain Active Directory domain administrator rights through SAMAccountName spoofing. Given the potential for widespread exploitation, organizations must take immediate action to patch these vulnerabilities and secure their Active Directory environments.
How the Exploit Works
The attack chain is alarmingly simple:
- An unenhanced user in the domain sends a Kerberos service ticket request to a vulnerable Active Directory server.
- The server replies with a standard Kerberos service ticket for the user.
- The attacker then spoofs a domain administrator account and requests a second Kerberos service ticket.
- Due to the lack of verification mechanisms in CVE-2021-42287 & CVE-2021-42278, the vulnerable server grants the attacker admin-level privileges.
- The attacker now has full control over the Active Directory domain, enabling them to:
- Modify user permissions
- Deploy malware or ransomware
- Exfiltrate sensitive data
- Create persistent backdoors for future access
This attack vector presents a critical risk to enterprises that rely on Active Directory for identity and access management.
Urgent Patch Guidance
Microsoft has released security patches to mitigate these vulnerabilities, and organizations must apply them immediately to prevent exploitation.
Vulnerability Details:
- CVE-2021-42287
- MITRE Link: CVE-2021-42287
- Microsoft Security Response Center (MSRC): Patch Details
- CVE-2021-42278
- MITRE Link: CVE-2021-42278
- Microsoft Security Response Center (MSRC): Patch Details
Patching Resources:
- KB5008380 – Authentication Updates (CVE-2021-42287):
How Cymulate Can Help
Organizations must proactively validate their security posture to determine whether their Active Directory servers remain vulnerable to these exploits.
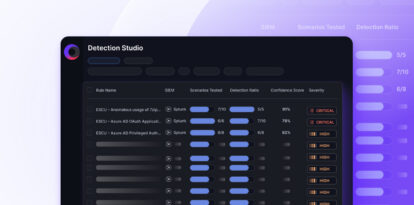
Cymulate's Extended Security Management Platform now includes a Purple Team scenario specifically designed to test Active Directory controllers against CVE-2021-42287 & CVE-2021-42278 exploits. Security teams can access this under the Purple Team Scenario resources within the Cymulate interface.
By running automated security validation tests, organizations can identify gaps in their defenses and take preemptive measures to secure their networks before attackers strike.