Frequently Asked Questions
Technical Details: OLE, CBF, and CVE-2022-30190
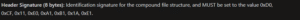
What is CVE-2022-30190 (Follina) and why is it significant?
CVE-2022-30190, also known as Follina, is a Microsoft Support Diagnostic Tool (MSDT) vulnerability that allows attackers to execute arbitrary code via maliciously crafted files, such as RTF or DOCX. Its significance lies in its ability to trigger code execution simply by previewing a file in Windows Explorer, making it highly exploitable and dangerous for organizations using Microsoft Office products.
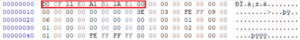
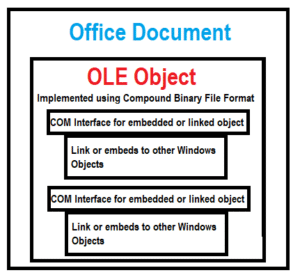
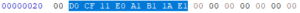
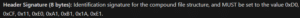
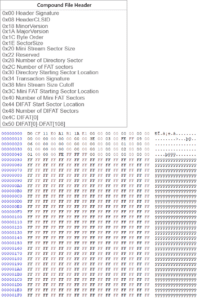
How does the Compound File Binary Format (CBF) relate to OLE objects in Microsoft Office files?
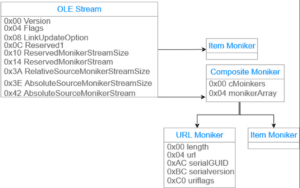
The Compound File Binary Format (CBF) is a Microsoft-developed container format used to store multiple files and streams within a single file. OLE objects, which enable embedding and linking of documents and data, are stored within CBF files in Office formats like DOC, XLS, and PPT. This structure allows complex objects, such as embedded Excel sheets in Word documents, to function seamlessly across applications using the Component Object Model (COM).
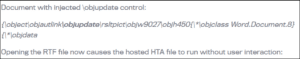
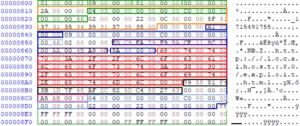
What role do OLE objects play in exploiting CVE-2022-30190?
OLE objects are used to embed or link external content within Office documents. In the context of CVE-2022-30190, attackers craft OLE objects within RTF files to include malicious hyperlinks or payloads. When the file is previewed or opened, the OLE object triggers the exploit, leading to code execution via the MSDT vulnerability.
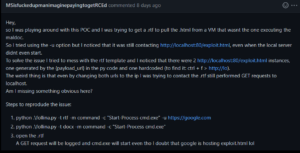
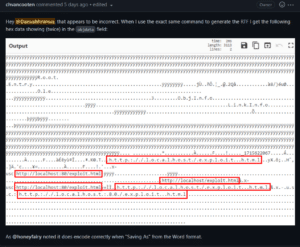
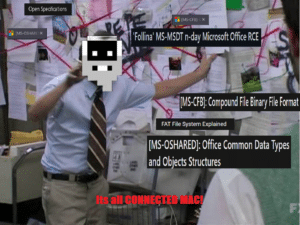
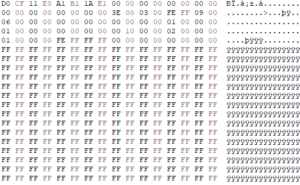
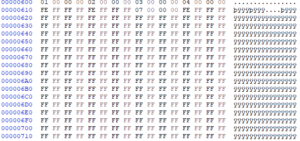
Why is automating the creation of weaponized RTF files challenging?
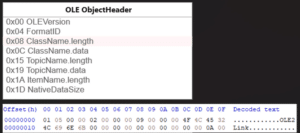
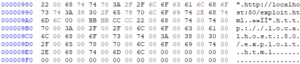
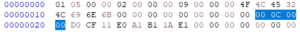
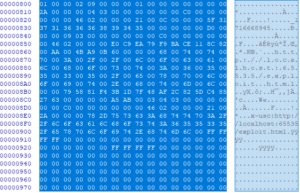
Automating weaponized RTF file creation is challenging because OLE objects within RTF files require precise binary formatting, including correct stream sizes, sector alignment, and proper handling of embedded hyperlinks. Manual generation often leads to errors unless all CBF and OLE specifications are followed, making automation non-trivial without deep technical understanding.
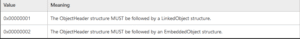
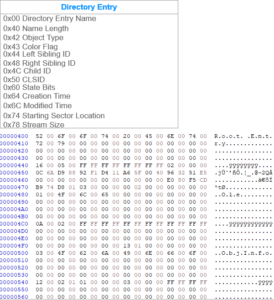
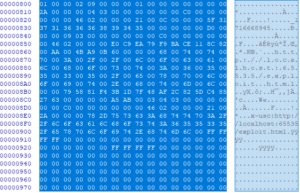
What are monikers in the context of OLE and CBF files?
Monikers are objects in Microsoft's Component Object Model (COM) that refer to specific instances of other objects. In OLE and CBF files, moniker streams contain information about hyperlinks or embedded objects, instructing the COM interface on how to load or execute the referenced content. They are critical for linking and embedding functionalities in Office documents.
How does understanding OLE and CBF structures help in security research?
Understanding OLE and CBF structures enables security researchers to analyze, craft, and detect malicious payloads embedded in Office documents. This knowledge is essential for automating exploit generation, developing detection tools, and creating effective mitigations against document-based attacks like CVE-2022-30190.
What tools are useful for analyzing OLE objects in RTF files?
Tools such as oletools and hex editors like HxD are valuable for analyzing OLE objects in RTF files. These tools allow researchers to inspect the binary structure, extract embedded objects, and verify stream sizes and alignments as specified in Microsoft documentation.
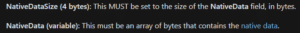
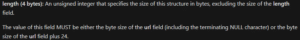
How can modifying stream sizes in CBF files affect exploit delivery?
Modifying stream sizes in CBF files is crucial for successful exploit delivery because incorrect sizes can prevent the Office application from reading the entire OLE object, causing the exploit to fail. Properly adjusting these values ensures the payload is processed as intended, enabling reliable exploitation or testing scenarios.
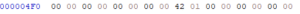
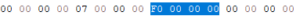
What is the significance of the MiniFAT chain in CBF files?
The MiniFAT chain in CBF files manages the allocation of small streams within the compound file. It links sectors together, allowing the storage of OLE objects and other embedded data. Understanding and correctly configuring the MiniFAT chain is essential for ensuring the integrity and functionality of embedded objects in Office documents.
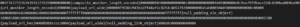
Where can I find the proof-of-concept code for automating RTF exploit generation?
The proof-of-concept code for automating RTF exploit generation related to CVE-2022-30190 can be found on GitHub. This code demonstrates how to generate DOCX and RTF files weaponized with the Follina exploit.
How does Cymulate Exposure Validation help with advanced security testing?
Cymulate Exposure Validation makes advanced security testing fast and easy by providing a unified platform for building custom attack chains and simulating real-world threats. It enables organizations to assess their defenses against vulnerabilities like CVE-2022-30190 and validate their security posture with actionable insights. Learn more.
What is the practical impact of understanding OLE and CBF for defenders?
For defenders, understanding OLE and CBF structures allows for better detection of malicious documents, development of custom detection rules, and more effective incident response. It also aids in validating security controls against sophisticated document-based attacks, improving overall organizational resilience.
How does Cymulate empower organizations to stay ahead of threats like Follina?
Cymulate empowers organizations by continuously assessing and validating their security posture against the latest threats, including vulnerabilities like Follina. The platform provides actionable insights, automated attack simulations, and comprehensive reporting to help teams proactively address exposures before they are exploited.
What are the main features of Cymulate's Exposure Management Platform?
Cymulate's Exposure Management Platform offers continuous threat validation, unified Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), exposure analytics, attack path discovery, automated mitigation, AI-powered optimization, and an extensive threat library with over 100,000 attack actions updated daily. Learn more.
How does Cymulate integrate with other security tools?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, and SentinelOne. These integrations enhance network, cloud, endpoint, and vulnerability management capabilities. See the full list.
What security and compliance certifications does Cymulate hold?
Cymulate holds several industry-leading certifications, including SOC2 Type II (covering security, availability, confidentiality, and privacy), ISO 27001:2013 (Information Security Management), ISO 27701 (Privacy Information Management), ISO 27017 (Cloud Services Security Controls), and CSA STAR Level 1. These certifications demonstrate Cymulate's commitment to robust security and compliance. Learn more.
How easy is it to implement Cymulate in my organization?
Cymulate is designed for rapid, agentless deployment with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately, and the platform offers comprehensive support, including email, chat, and a knowledge base. Schedule a demo to learn more.
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and selected scenarios. For a personalized quote, schedule a demo with the Cymulate team.
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams in organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. The platform addresses the unique needs of each role with tailored solutions. Learn more.
What business impact can customers expect from Cymulate?
Customers using Cymulate report up to a 52% reduction in critical exposures, a 60% increase in team efficiency, and an 81% reduction in cyber risk within four months. The platform also enables faster threat validation (up to 40x faster than manual methods) and cost savings by consolidating tools. See case studies.
How does Cymulate compare to other security validation platforms?
Cymulate stands out by offering a unified platform that combines Breach and Attack Simulation, Continuous Automated Red Teaming, and Exposure Analytics. It provides continuous, automated testing, AI-powered optimization, and the most advanced attack simulation library, with proven results in reducing risk and improving efficiency. See comparisons.
What pain points does Cymulate address for security teams?
Cymulate addresses fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation, operational inefficiencies in vulnerability management, and post-breach recovery challenges. The platform automates validation, prioritizes exposures, and provides actionable insights. Read customer stories.
How does Cymulate support different security personas?
Cymulate tailors its solutions for CISOs (providing metrics and insights), SecOps teams (automating processes and improving efficiency), red teams (offensive testing with a large attack library), and vulnerability management teams (automated validation and prioritization). Learn more by role.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive, user-friendly interface and ease of implementation. Testimonials highlight the platform's accessibility for users of all skill levels and the effectiveness of its support team. Read testimonials.
Where can I find Cymulate's blog, newsroom, and resource hub?
You can stay updated on the latest threats, research, and company news through Cymulate's blog, newsroom, and Resource Hub.
What is Cymulate's mission and vision?
Cymulate's mission is to transform cybersecurity practices by enabling organizations to proactively validate their defenses, identify vulnerabilities, and optimize their security posture. The vision is to create a collaborative environment for lasting improvements in cybersecurity strategies. Learn more.
How does Cymulate ensure data security and privacy?
Cymulate ensures data security through encryption in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and compliance with GDPR. The platform also features mandatory 2FA, RBAC, IP restrictions, and continuous vulnerability scanning. Read more.
Where can I find Cymulate's webinars, events, and glossary?
Cymulate offers webinars, live events, and a cybersecurity glossary. Visit the Events & Webinars page and Cybersecurity Glossary for more information.
How does Cymulate help with lateral movement attack prevention?
Cymulate provides attack path discovery and automated testing for lateral movement, helping organizations identify and mitigate risks of attackers moving within their network. For more details, see the blog post Stopping Attackers in Their Tracks.