How Continuous Security Validation Prevents Undetected Security Drift
American visionary computer scientist, Alan Curtis Kay, once said, "The best way to predict the future is to invent it."
This statement holds today as enterprise IT infrastructures continue to expand and evolve rapidly and now routinely span across various data centers, workforces, and multiple clouds, and interacts with numerous third-party software suppliers.
This complexity requires continuous security validation to ensure that security measures remain effective. Otherwise, ad-hoc updates, system failures, or misconfigurations can introduce security gaps—many of which go unnoticed until exploited by attackers.
How Security Drift Goes Unnoticed
One way a security drift goes undetected is when it hides behind the misplaced sense of security relying on last quarter's penetration test result, which leads to complacency. Another main security drift avenue is the creation of a new type of attack that might be undetected by EDR (Endpoint Detection and Response), gateways, and firewalls until it is identified and their database is updated, leaving infrastructures unprotected in the interim time.
But the main source of emerging security drift is some minor oversight by the IT or security team during routine tasks or configuration changes due to modifying ongoing projects or launching new ones.
The Need for Continuous Security Validation
To mitigate these hidden risks, organizations should shift from protecting against known threats to identifying exposure. Gartner now recommends this proactive approach under Continuous Threat Exposure Management (CTEM).
How Continuous Security Validation Works
At Cymulate Customer Success, we see firsthand how organizations spot and mitigate new exposures in real time by applying continuous security validation methods such as:
- Breach and Attack Simulation (BAS): Regularly testing security defenses against realistic attack scenarios.
- Security Control Validation: Ensuring security configurations remain effective over time.
- Automated Threat Assessments: Continuously challenging security controls for weaknesses before attackers do.
Unlike traditional security assessments that identify one-time security gaps, continuous security validation (CSV) ensures ongoing evaluation of an organization’s resilience in live environments.
The goal? Preventing security drift by continuously verifying that detection and response mechanisms remain effective.
Examples of Security Drift
Web Gateway Security Oversight
For our first example, we will look at an investment company located in EMEA and employing 1,200 people.
The organization initially used Cymulate BAS to establish a baseline that blocked all file downloads. Once that phase was completed, the organization switched to weekly assessments that continuously validated that their security controls remain effective.
One of these weekly assessments registered an unexplained spike in the web gateway’s risk score, from 0 to 100.
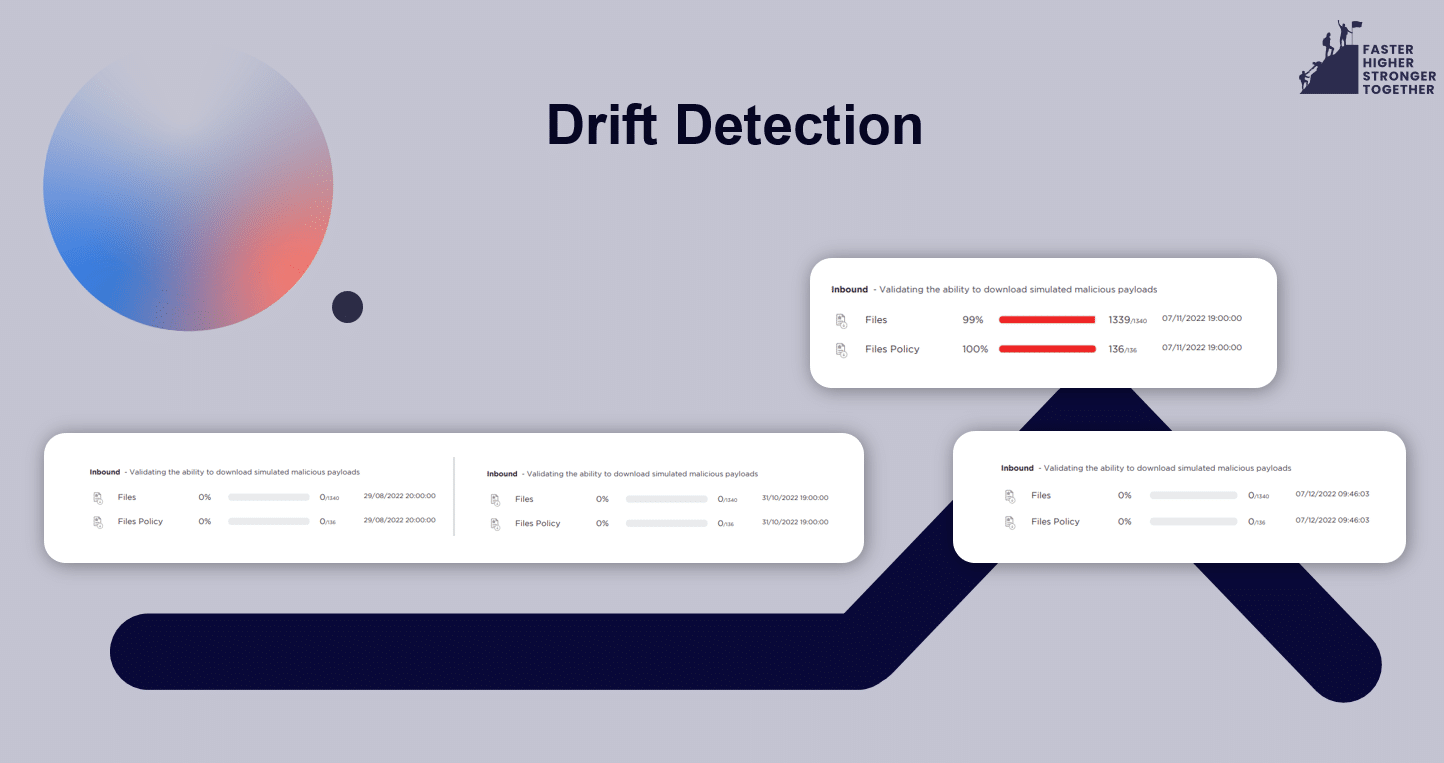
The subsequent investigation uncovered that a separate project run by the IT department was at the root of this sudden risk score spike. In order to run one of their projects, the IT team had modified the files download policy on the web gateway, allowing all the users in the organization to openly download files, causing a significant risk to the organization.
SIEM Blind Spot in OT Network
The second example is taken from a manufacturing EMEA company with 7,000 employees.
This manufacturer runs two network environments – IT and OT.
In both environments, a local endpoint security management server forwards all the logs and events to the organizational SIEM (Security Information and Event Management) solution, where detection logic—such as Sigma rules—is applied to identify potential threats in real time
To validate both endpoint security posture and detection rate, the organization has set a weekly endpoint security assessment with SIEM integration enabled that worked seamlessly for months.
Then, suddenly, the SIEM events/alerts stopped appearing on the OT environment’s assessments.
The security analysts investigated the reasons behind this unintended silence. They discovered that the IT security team had upgraded the endpoint security server in the OT environment to a new one. Though this upgrade was planned and approved, the IT security team had forgotten to configure the new server to send SYSLOG events into the SIEM, effectively blinding the SIEM to any event, intrusion, or other, in the entire OT environment.
Why Continuous Security Validation is Essential
Both examples highlight how normal, well-intentioned IT activities can unknowingly create security gaps.
Without continuous security validation, these risks would have remained unnoticed until exploited by attackers.
At Cymulate Customer Success, we see cases like these daily—customers reaching out to thank us or requesting guidance in identifying risk spikes.
By implementing continuous security validation, organizations can:
- Detect and mitigate security drift in real time
- Ensure security configurations remain effective over time
- Prevent undetected exposure before attackers exploit its.



