Frequently Asked Questions
Ransomware Attack Simulation: Product Features & Capabilities
What is Cymulate's Ransomware Attack Simulation?
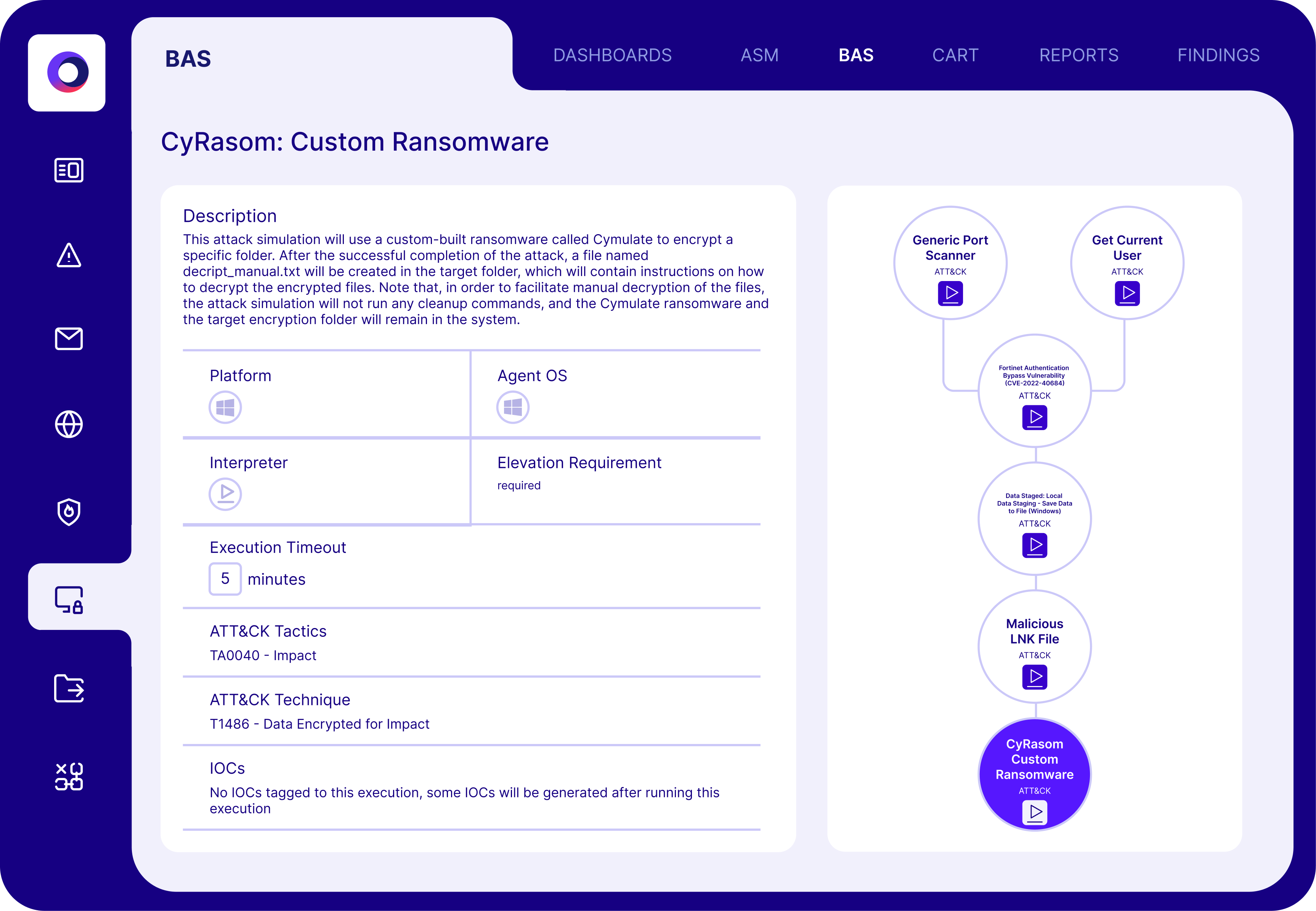
Cymulate's Ransomware Attack Simulation is a solution that safely emulates the stages of a real ransomware attack, from initial access to encryption, to test your organization's prevention, detection, and response capabilities without impacting production systems. This enables organizations to validate their resilience against real-world ransomware threats. Source
How does Cymulate simulate ransomware attacks safely?
Cymulate runs non-destructive ransomware behaviors in a controlled environment, ensuring that simulations do not impact production systems, data, or operations. All ransomware behaviors are emulated safely, allowing organizations to test defenses without risk. Source
What are the main benefits of using Cymulate for ransomware simulation?
Benefits include proactively identifying and fixing weaknesses, validating un-patchable exposures, improving SOC detection and response, and reducing breach risk and downtime by continuously testing defenses across endpoints, cloud, network, and identity systems. Source
How does Cymulate help uncover ransomware weaknesses?
Cymulate provides continuous, repeatable, and safe simulations that reveal new control gaps as they emerge, allowing organizations to uncover ransomware weaknesses before attackers can exploit them. Source
What types of attack paths does Cymulate simulate?
Cymulate recreates real attacker routes using current ransomware TTPs (Tactics, Techniques, and Procedures) to pinpoint misconfigurations and exposure points, providing realistic attack path validation. Source
How quickly can organizations start using Cymulate's ransomware simulation?
Organizations can start running ransomware simulations in minutes without complex deployments, thanks to Cymulate's fast setup and agentless mode. Source
What security controls can Cymulate's ransomware simulation validate?
Cymulate can validate controls across endpoint security (AV/EDR), cloud security (CWPP), containers/Kubernetes, secure email and web gateways, web application firewalls, network security (IPS/IDS), data loss prevention, and SIEM/SOAR detections. Source
How does Cymulate help validate un-patchable exposures?
Cymulate allows organizations to test legacy systems, unsupported OS versions, and architectural limitations safely, confirming that compensating controls are effective. Source
How does Cymulate improve SOC detection and response?
Cymulate ensures that alerts trigger at the right time and that security teams can contain threats quickly, minimizing potential impact and improving overall SOC readiness. Source
What is the process for running a ransomware simulation with Cymulate?
The process includes choosing a ransomware scenario, executing safe simulations, analyzing exposure and control gaps, receiving guided remediation, and retesting continuously to ensure improvements are effective. Source
Use Cases & Customer Success
How do organizations use Cymulate to reduce ransomware risk?
Organizations use Cymulate's attack simulations to reduce ransomware risk and improve security posture by continuously testing defenses, identifying weaknesses, and validating controls across their environments. Source
What feedback have customers given about Cymulate's ransomware simulation?
Customers have praised Cymulate for its ease of use, comprehensive validation, and ability to demonstrate risk. For example, a Chief Security Officer at a global hedge fund said, "With Cymulate, I can validate controls against emerging threats faster than I could before." Source
How often should ransomware simulations be run?
Simulations should be run continuously to maintain up-to-date visibility of ransomware readiness. Regular testing ensures that new systems, configurations, or security gaps are assessed before attackers can exploit them. Source
Can Cymulate demonstrate risk to stakeholders?
Yes, Cymulate provides an easy and elegant method to demonstrate the risk associated with security controls or policies, making it easier to communicate with stakeholders. Source
How does Cymulate help with legacy systems and unsupported OS versions?
Cymulate enables organizations to test legacy systems and unsupported OS versions safely, ensuring that compensating controls are effective and exposures are validated. Source
What is the lifecycle of a ransomware attack as simulated by Cymulate?
The lifecycle includes initial access, establishing persistence, privilege escalation, lateral movement, data exfiltration, payload deployment, and encryption/impact. Cymulate simulates these stages to test organizational defenses. Source
Does Cymulate support continuous testing for ransomware resilience?
Yes, Cymulate supports continuous testing, allowing organizations to uncover new control gaps as they emerge and maintain up-to-date ransomware resilience. Source
How does Cymulate help reduce breach risk and downtime?
Cymulate lowers the chance of ransomware crippling operations by continuously testing defenses and validating controls across all critical systems, reducing breach risk and downtime. Source
Technical Requirements & Implementation
Is Cymulate's ransomware simulation agentless?
Yes, Cymulate operates in an agentless mode, requiring no additional hardware or complex configurations, which simplifies deployment and reduces setup time. Source
What is required to implement Cymulate's ransomware simulation?
Implementation requires minimal resources. The customer provides necessary infrastructure and third-party software as per Cymulate’s prerequisites, but the platform is designed for seamless integration into existing workflows. Source
Security & Compliance
What security and compliance certifications does Cymulate hold?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating adherence to industry-leading security and privacy standards. Source
How does Cymulate ensure data security?
Cymulate ensures data security through encryption in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, and a tested disaster recovery plan. Source
Is Cymulate GDPR compliant?
Yes, Cymulate incorporates data protection by design and has a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO), ensuring GDPR compliance. Source
Integrations & Partnerships
What integrations does Cymulate support for ransomware simulation?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. Source
Where can I find a complete list of Cymulate's integrations?
You can find a complete and up-to-date list of Cymulate's technology integrations on the Partnerships and Integrations page.
Competition & Differentiation
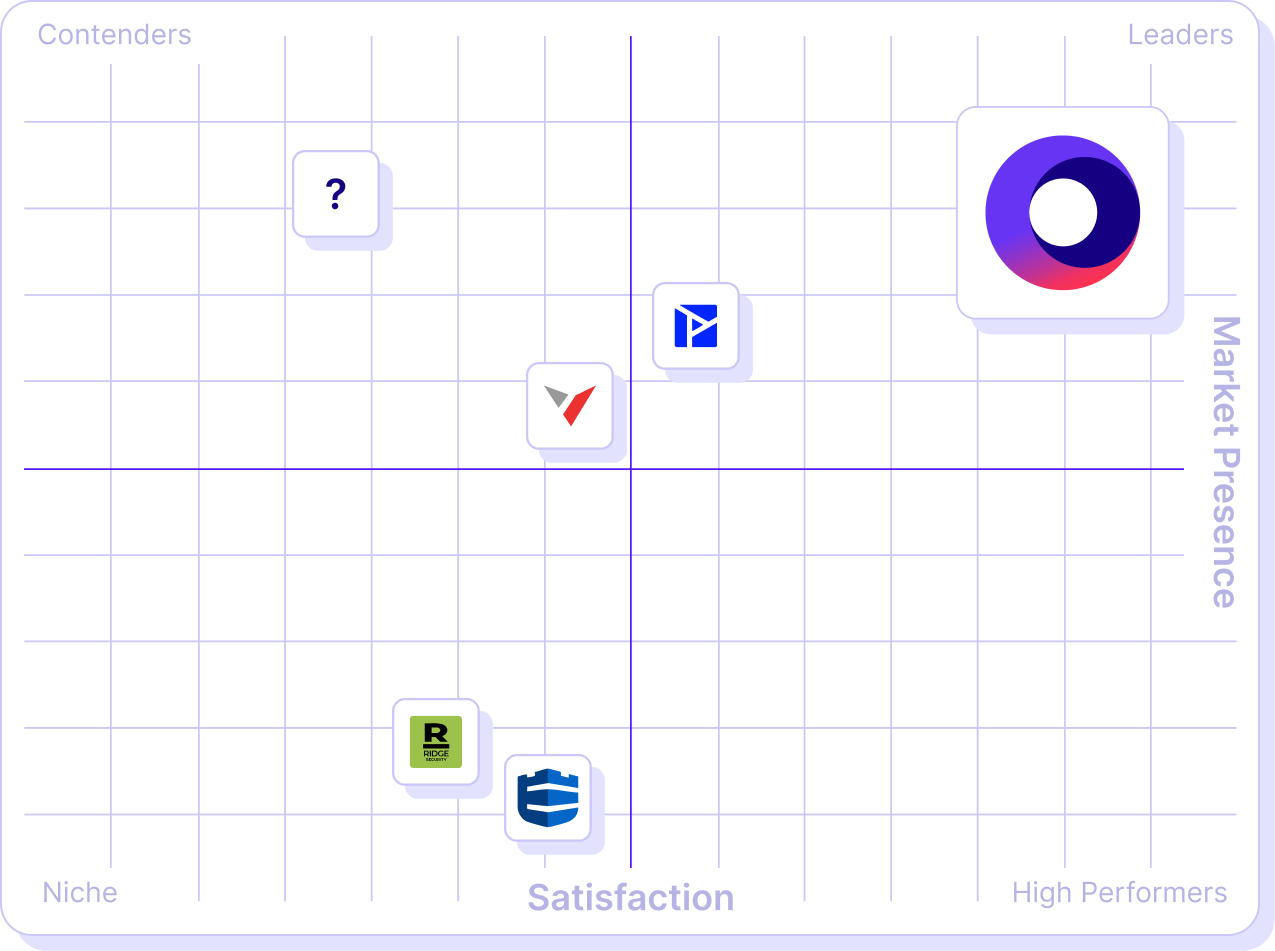
How does Cymulate compare to other ransomware simulation solutions?
Cymulate stands out with its unified platform, continuous threat validation, AI-powered optimization, and extensive attack simulation library. It is recognized for ease of use, rapid deployment, and comprehensive coverage across the attack lifecycle. Source
What are Cymulate's main competitors in ransomware simulation?
Main competitors include AttackIQ, Mandiant Security Validation, Pentera, Picus Security, SafeBreach, and Scythe. Each has different strengths, but Cymulate is noted for innovation, automation, and comprehensive exposure validation. Source
Why choose Cymulate over other ransomware simulation platforms?
Cymulate offers a unified platform with continuous validation, actionable insights, rapid deployment, and proven results such as a 52% reduction in critical exposures and an 81% reduction in cyber risk within four months. Source
Pricing & Plans
What is Cymulate's pricing model for ransomware simulation?
Cymulate uses a subscription-based pricing model tailored to each organization's requirements, including chosen package, number of assets, and scenarios. For a detailed quote, schedule a demo with the Cymulate team.
Documentation & Resources
What technical documentation is available for Cymulate's ransomware simulation?
Cymulate provides guides, whitepapers, solution briefs, and data sheets covering exposure validation, attack path discovery, automated mitigation, and more. Access these resources at the Resource Hub.
Where can I find best practices for ransomware resilience?
Best practices for ransomware resilience are available in Cymulate's blogs, webinars, and e-books, such as "7 Essential Steps to Becoming Ransomware Resilient" and "How to Keep Ransomware at Bay." Visit the Resource Hub for more.