Frequently Asked Questions
Attack Campaign Details & Technical Insights
What vulnerability was exploited in the ManageEngine ADSelfService Plus targeted attack campaign?
The attackers exploited CVE-2021-40539, a REST API authentication bypass vulnerability that allows remote code execution on vulnerable devices. This was achieved by delivering crafted POST statements to the REST API LicenseMgr, enabling the installation of malicious payloads.
What tools did the attackers deploy during the campaign?
The attackers deployed the Godzilla webshell, NGLite backdoor, and KdcSponge credential stealer. Godzilla enabled command execution and lateral movement, NGLite provided anonymous remote control via blockchain-based NKN infrastructure, and KdcSponge harvested credentials from domain controllers.
How does the Godzilla webshell evade detection?
Godzilla uses AES encryption to obfuscate network traffic and has a low static detection rate across security vendor products. It parses inbound HTTP POST requests, decrypts data with a secret key, executes the decrypted content, and returns results via HTTP response, minimizing its footprint and risk of early detection.
What is the role of NGLite in the attack?
NGLite is an anonymous cross-platform remote control program based on blockchain technology. It uses the New Kind of Network (NKN) infrastructure for command-and-control communications, providing attackers with theoretical anonymity and rare C2 channel usage.
How does KdcSponge steal credentials?
KdcSponge injects into the LSASS process and hooks Kerberos API functions to intercept usernames and passwords. It identifies the Kerberos module version, hooks relevant APIs, and logs stolen credentials encrypted with XOR (key 0x55) in the system.dat file.
What files did the attackers target for exfiltration?
The attackers targeted the Active Directory database file (ntds.dit) and the SYSTEM hive from the registry, which contain sensitive information for further attacks and maintaining long-term access.
What were the main objectives of the threat actors?
The main objectives were to steal credentials for privileged accounts, maintain persistent access to high-value systems, and exfiltrate sensitive data from victim networks.
How did the attackers ensure redundancy in their toolset?
The attackers deployed both Godzilla and NGLite, which are publicly available tools, to ensure redundancy. If one tool was detected or disrupted, the other could maintain access to the compromised systems.
Why is Godzilla preferred over ChinaChopper by threat groups?
Godzilla is preferred due to its advanced evasion capabilities, AES encryption for network traffic, low detection rates, and richer functionality compared to ChinaChopper.
How can organizations defend against attacks like this?
Organizations should apply timely patches, adopt robust security validation processes, and use advanced threat simulation tools to identify and mitigate vulnerabilities before attackers exploit them.
What is the significance of using blockchain-based C2 channels like NKN?
Blockchain-based C2 channels like NKN provide attackers with theoretical anonymity and make detection more challenging, as such channels are rare and less likely to be monitored by traditional security tools.
How does credential theft impact an organization's security?
Credential theft enables attackers to escalate privileges, maintain persistent access, and exfiltrate sensitive data, significantly increasing the risk of ransomware deployment, policy modification, and disabling security tools.
What is the role of lateral movement in targeted attacks?
Lateral movement allows attackers to traverse the network, escalate privileges, and access high-value systems such as domain controllers, facilitating credential theft and data exfiltration.
How do attackers maintain persistence in compromised networks?
Attackers maintain persistence by deploying multiple tools (e.g., Godzilla, NGLite), stealing credentials, and creating backdoors, ensuring continued access even if some tools are detected or removed.
What is the impact of exploiting domain controllers in an attack?
Exploiting domain controllers allows attackers to access sensitive files (ntds.dit, SYSTEM hive), harvest credentials, and potentially control the entire network, leading to widespread compromise.
How do attackers use publicly available tools in sophisticated attacks?
Attackers leverage publicly available tools like Godzilla and NGLite, often with advanced evasion features, to ensure redundancy, minimize detection, and maximize their ability to maintain access and exfiltrate data.
What is the importance of decrypting and logging credentials in attacks?
Decrypting and logging credentials enables attackers to systematically harvest authentication details, escalate privileges, and maintain persistent access to critical systems.
How does the attack demonstrate evolving tactics in cybercrime?
The attack showcases the use of advanced and publicly available tools, rapid exploitation of vulnerabilities, and sophisticated evasion techniques, reflecting the evolving tactics of cybercriminals.
Cymulate Platform Features & Security Validation
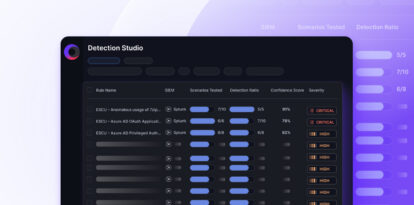
What types of threats can Cymulate validate?
Cymulate validates threats across the full kill chain, including phishing, malware, lateral movement, data exfiltration, and zero-day exploits, using daily updated threat templates and AI-generated attack plans. Learn more.
How quickly does Cymulate update its immediate threats module?
Cymulate's immediate threats module is updated rapidly to reflect new attacks, allowing organizations to quickly assess their IT estate for exposure and implement remedial actions promptly. Customers appreciate the speed and relevance of these updates for proactive defense. Source.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its ease of use and intuitive design. For example, Raphael Ferreira, Cybersecurity Manager, stated, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture." Source.
What are Cymulate's security and compliance certifications?
Cymulate is certified for SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. These certifications demonstrate Cymulate's commitment to industry-leading security and privacy standards. Source.
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs. Pricing is determined by the specific package, number of assets, and scenarios selected for testing and validation. For a detailed quote, schedule a demo. Source.
What integrations does Cymulate offer?
Cymulate integrates with a wide range of technology partners, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, CrowdStrike Falcon, Rapid7 InsightVM, SentinelOne, Wiz, and more. For a full list, visit our technology alliances and partners page.
What business impact can customers expect from using Cymulate?
Customers can expect a 30% improvement in threat prevention, 52% reduction in critical exposures, 60% increase in operational efficiency, 40X faster threat validation, 85% improvement in threat detection accuracy, and an 81% reduction in cyber risk within four months (as seen in the Hertz Israel case study). Read the case study.
Who is the target audience for Cymulate's products?
Cymulate's solutions are designed for Security Operations teams, CISOs, Vulnerability Management teams, and Red Teams across industries such as finance, healthcare, retail, and technology. Learn more.
How does Cymulate differ from competitors like AttackIQ, Mandiant, Pentera, Picus Security, SafeBreach, and Scythe?
Cymulate stands out with its unified platform, industry-leading threat scenario library, AI-powered capabilities, ease of use, continuous innovation, and comprehensive exposure validation. For detailed comparisons, visit our competitor comparison page.
What are the key capabilities and benefits of Cymulate's platform?
Cymulate offers continuous threat validation, exposure awareness, defensive posture optimization, scalable offensive testing, cloud validation, collaboration across teams, and comprehensive integration of BAS, CART, and Exposure Analytics. Benefits include improved threat prevention, reduced critical exposures, increased efficiency, faster validation, enhanced detection, proven ROI, and ease of use. Learn more.
What technical documentation is available for Cymulate?
Cymulate provides a product whitepaper, custom attacks data sheet, technology integrations data sheet, solution briefs, and analyst reports. These resources offer comprehensive technical insights. View resources.
How long does it take to implement Cymulate?
Cymulate is known for quick and seamless implementation. It operates in agentless mode, requires minimal resources, and customers can start running simulations almost immediately after deployment. Comprehensive support and educational resources are available. Learn more.
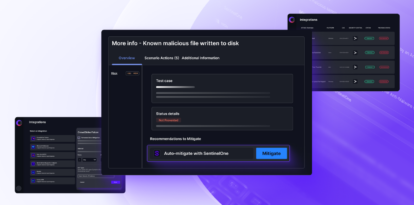
What types of threats and techniques does Cymulate simulate for endpoint security validation?
Cymulate simulates known malicious file samples, malicious behaviors, ransomware, worms, trojans, rootkits, DLL side-loading, and code injection for endpoint security validation. Learn more.
What is threat exposure prioritization in cybersecurity?
Threat exposure prioritization is the process of identifying and ranking vulnerabilities based on their actual exploitability and impact on business-critical assets. Cymulate uses automated threat validation and exposure scoring to help teams focus on exposures not protected by security controls. Learn more.
What are malware-based network attacks and how can they be prevented?
Malware-based attacks include worms, trojans, and ransomware. Prevention strategies involve deploying advanced endpoint detection and response (EDR), regularly patching systems, monitoring for anomalous activity, and validating lateral movement controls. Learn more.
What constitutes an insider threat?
An insider threat is a security risk originating from within an organization, including malicious insiders, negligent insiders, and compromised insiders whose credentials have been stolen. Learn more.
What types of cyber threats does the financial services sector face?
The financial services sector faces sophisticated threats such as ransomware, phishing, and advanced persistent threats (APTs), requiring robust security controls for both internal systems and customer-facing applications. Learn more.
What is an example of Kerberos CNAME relay using ARP poisoning to ADCS web enrollment (ESC8)?
An attacker sets up a rogue DNS server and fake HTTP/SMB servers, poisons CNAME records, and uses ARP poisoning to redirect victims. The attacker relays Kerberos authentication to ADCS web enrollment, requesting certificates in the victim's name. Read the full walkthrough.
What is the Threat Exposure Validation Summer Series and why is it important for 2025?
The Threat Exposure Validation Summer Series highlights the necessity of threat exposure validation in 2025. Watch the video: Threat Exposure Validation Summer Series: Threat Exposure Validation is a must have in 2025 video.