Automate Advanced Testing for
Blue & Red Team Efficiency & Scale
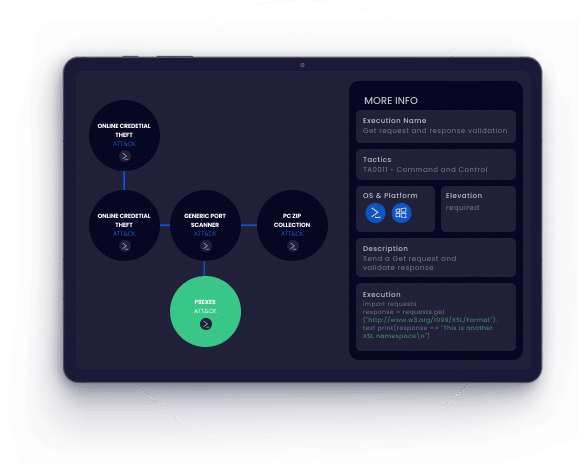
Cymulate BAS Advanced Scenarios provides an open framework for customizing chained
cybersecurity assessments and automating testing.
- Out-of-the-box resources and templates for applications, environments &
infrastructure testing - Modify templates or create new tests from simple executions to testing
entire protocols
- Automate security control validation, confirm remediation, or prepare for
audits & penetration tests - On-demand and schedules assessments for easy, repeatable testing and
validation
Benefits of BAS Advanced Scenarios

Realistic
Testing
Offensive chained attack simulations based on threat actor tactics and techniques

Extensive
Customization
The ability to create, modify & run chained or atomic attack campaigns

Automated
Assessments
Automated testing for SecOps to independently repeat assessments, validate mitigations & identify drift

Cyber Framework
Mapping
Assessments mapped to the MITRE ATT&CK® and NIST 800-53 frameworks
Capabilities
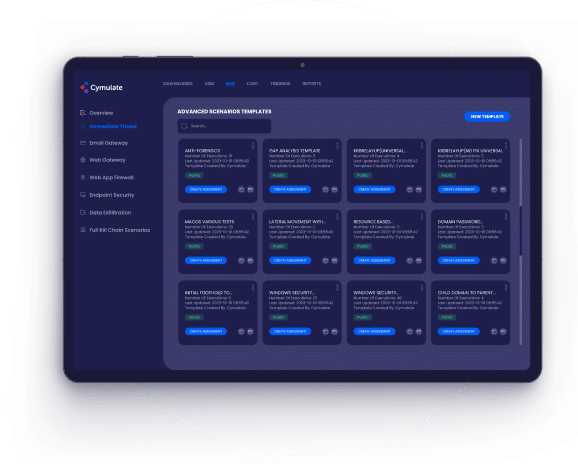
Advanced Template Editor
- Utilize thousands of resources and templates designed by
Cymulate Threat Research Group based on actual threat
actor behavior and techniques - Modify built-in resources or create new assets from
executions to entire testing protocols - Create a single execution or a series of chained scenarios
tailored to meet specific assessment requirements, data
systems, applications, and infrastructure
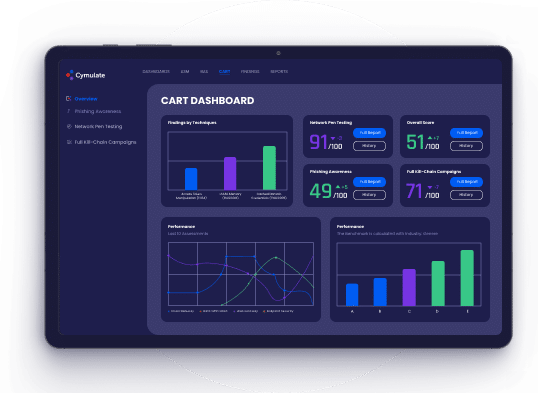
On-demand and Scheduled
Assessments
- Schedule assessments to run once or on recurring
schedule - Customize simulations for blue teams to easily re-
run following remediation - Automate assessments to monitor security drift and
regression testing
Mitigation Guidance
- Understand mitigation methodologies for each
discovered gap and multiple pathways for remediation - Correlate data with SIEM, SOAR, GRC, EDR, and other
tools to facilitate more targeted remediation actions - Gain information on attack indicators and Sigma rules
to improve SIEM detection
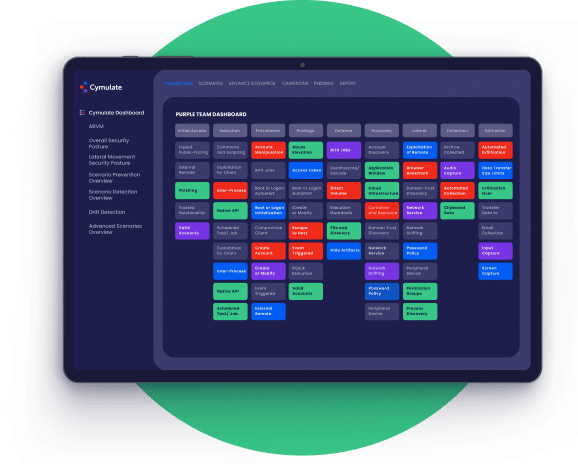
MITRE ATT&CK and NIST Support
- Simulate real-world behavior of malware and APT groups that
imitate the specific tactics and techniques mapped to MITRE
ATT&CK® and NIST 800-53 frameworks - View all attack simulation results on the Cymulate MITRE
ATT&CK® Heatmap dashboard for a summarized view of security
resilience
Environments
The attack surface constantly changes, requiring organizations to plan for an react to these changes.
Cymulate provides extensive attack simulation and immediate threat testing across on-premises, cloud,
and hybrid infrastructure and supports a wide variety of operating systems.

On-premises
- Internal Systems
- Legacy Applications
- User Networks

Cloud
- IaaS
- Containers
- Serverless/APIs

Hybrid
- Remote Workers
- Shared Services
- Cloud Storage
Windows
- Desktop
- Servers
- Virtual

Linux
- RedHat
- Debian
- Forked Distributions

MacOS
- Intel
- Apple Silicon
- 10.13 and higher
Cymulate BAS Advanced Scenarios
Scalable
Scalable
Automated testing to reduce repetitive, labor-intensive manual tasks and increase productivity
Extensive
Extensive
Assess multiple layers of security controls with regularly updated TTPs targeted to each area of defense
Comprehensive
Comprehensive
Covers security control validation and exposure risk assessment for on-premises, Cloud, and hybrid environments
Easy
Easy
Deploys with ease, customizable, and runs ongoing non-disruptive assessments
The Cymulate Exposure Management and Security Validation Platform
Cymulate BAS Advanced Scenarios is available both as a standalone SaaS offering and as an
integrated offering within the Cymulate Exposure Management and Security Validation Platform.
Backed By the Industry

Cymulate Recognized as Top Innovation Leader
F&S recognized in their Frost Radar™️ Global BAS, 2022 report