Collect and Analyze Data from Across the IT and Security Infrastructure
Cymulate Exposure Analytics collects and analyzes data from across the IT and security infrastructure to
measure and communicate cyber resilience as part of exposure management programs.
Identify and prioritize risk exposure with business context, attack surface assessment, and control validation for breach feasibility
Forecast mitigation outcomes with simulation modeling
Mobilize teams to action with clearer understanding of a vulnerability’s operational and business impact
Guide teams to action with actionable guidance and integrations with SecOps and service management
Measure, track, and visualize risk posture of business systems and security tools
Build risk metrics and performance tracking for CTEM program scoping and mobilization
Measure Cyber Resilience as Part of Threat Exposure Management
Correlated Analysis
Full view of attack surface, assets, vulnerabilities, and business impact
Risk Quantification
Measure risk based on business impact, control efficacy, and breach feasibility
Prioritization
Identify mitigations that address biggest risk and drive cyber resilience improvements
Simulation Modeling
Forecast mitigation outcomes and impact on cyber resilience and risk
How it Works

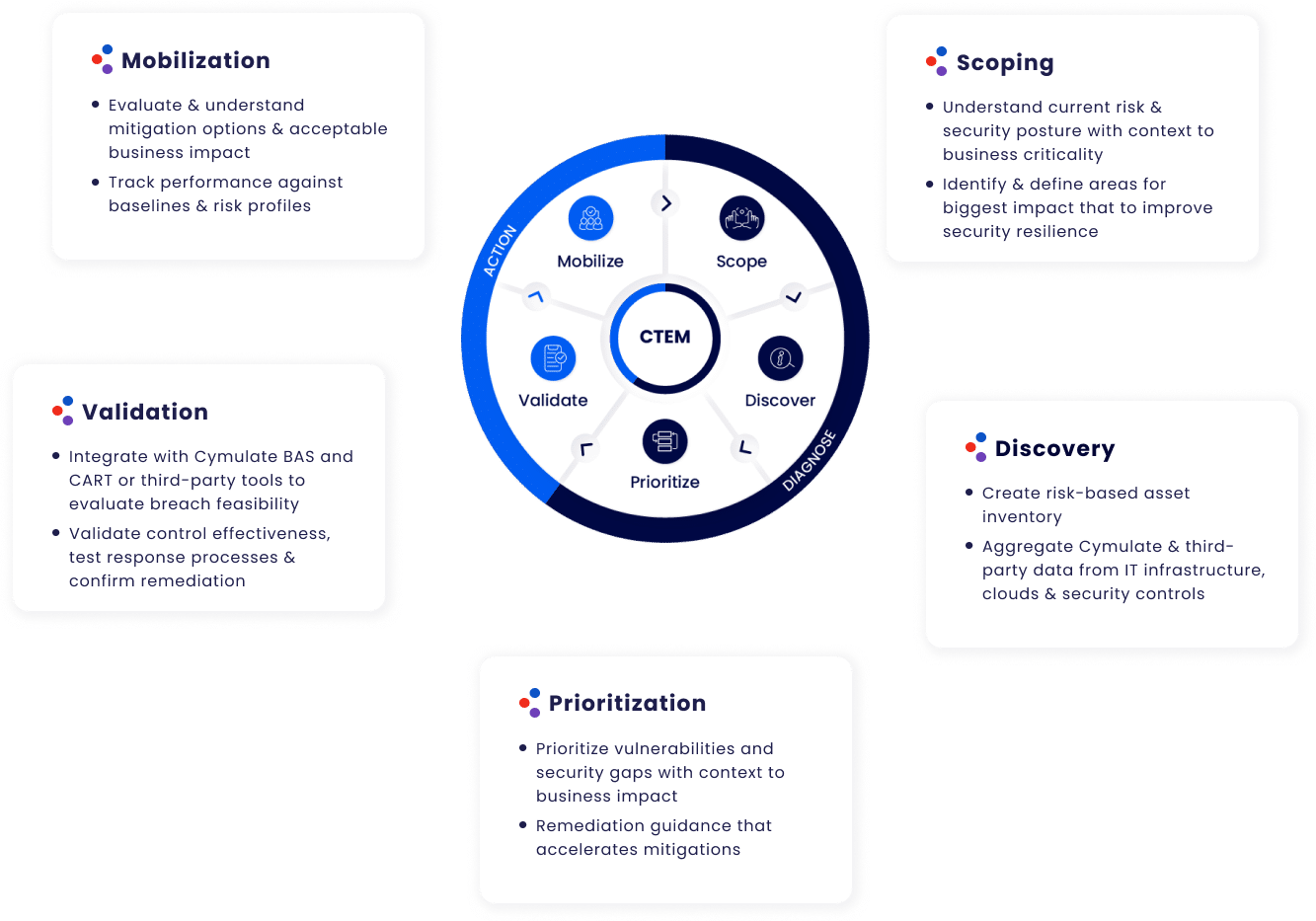
Continuous Threat Exposure Management
Centralize intelligence and visibility to security posture with business
context essential to an exposure management program

Measure & Baseline
Cyber Resilience
Quantify risk based on attack surface, business impact,
control efficacy, and breach feasibility – as well as
external data such as CVSS scores and threat intel
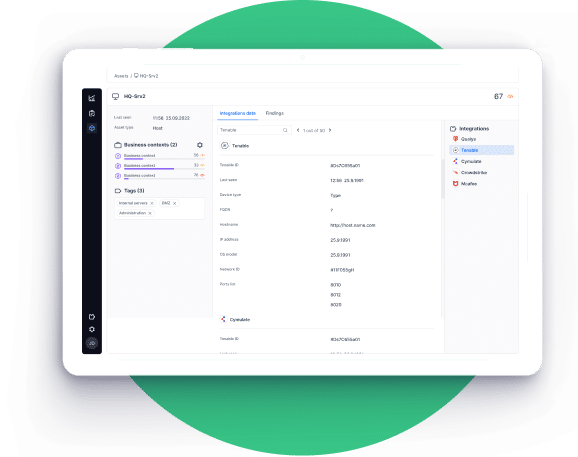
Profile Assets for Risk and Business Context
Ingest and contextualize data from disparate data sources
to create a consolidated view of assets with context to their
risk with per asset inventory of:
- Existing security controls
- Current enforced policies
- Known vulnerabilities
- Un-patchable vulnerabilities or security gaps
- Mitigation status

Focus on Greatest Risk
And Mobilize Mitigations
With Clear View of Impact
Prioritize mitigations that deliver the biggest reduction in
risk and improvement in cyber resilience
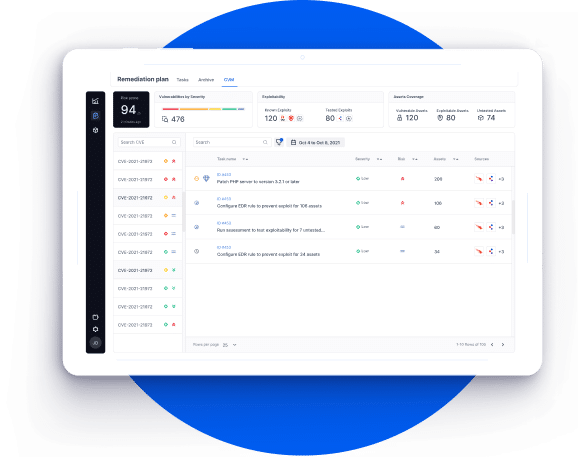
Accelerate Mitigation with
Remediation Planning
Mobilize teams to action with full understanding of a
vulnerability’s operational and business impact.
Integrations
Cymulate Exposure Analytics aggregates information from across the IT and security stack to create a security
data fabric that combines an internal view of controls with an external attacker view of viable targets.

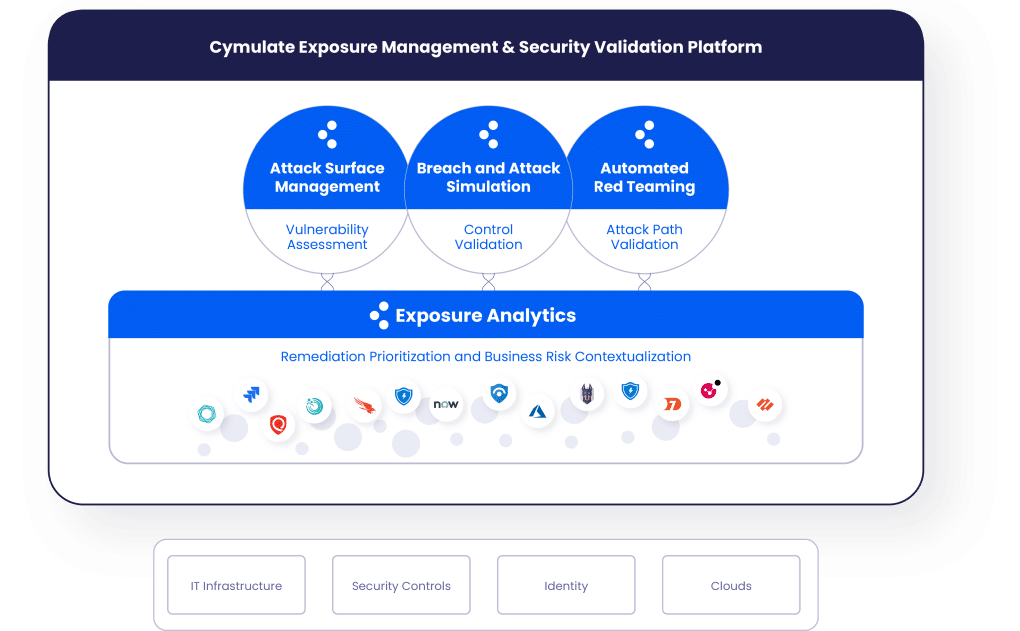
The Cymulate Exposure Management and Security Validation Platform
Cymulate Exposure Analytics is available both as a standalone SaaS offering and as an integrated offering within the Cymulate Exposure Management and Security Validation Platform.
Backed By the Industry


Cymulate Recognized as Top Innovation Leader
F&S recognized in their Frost Radar™️ Global BAS, 2022 report