Take an Attacker's View to Exposure Management
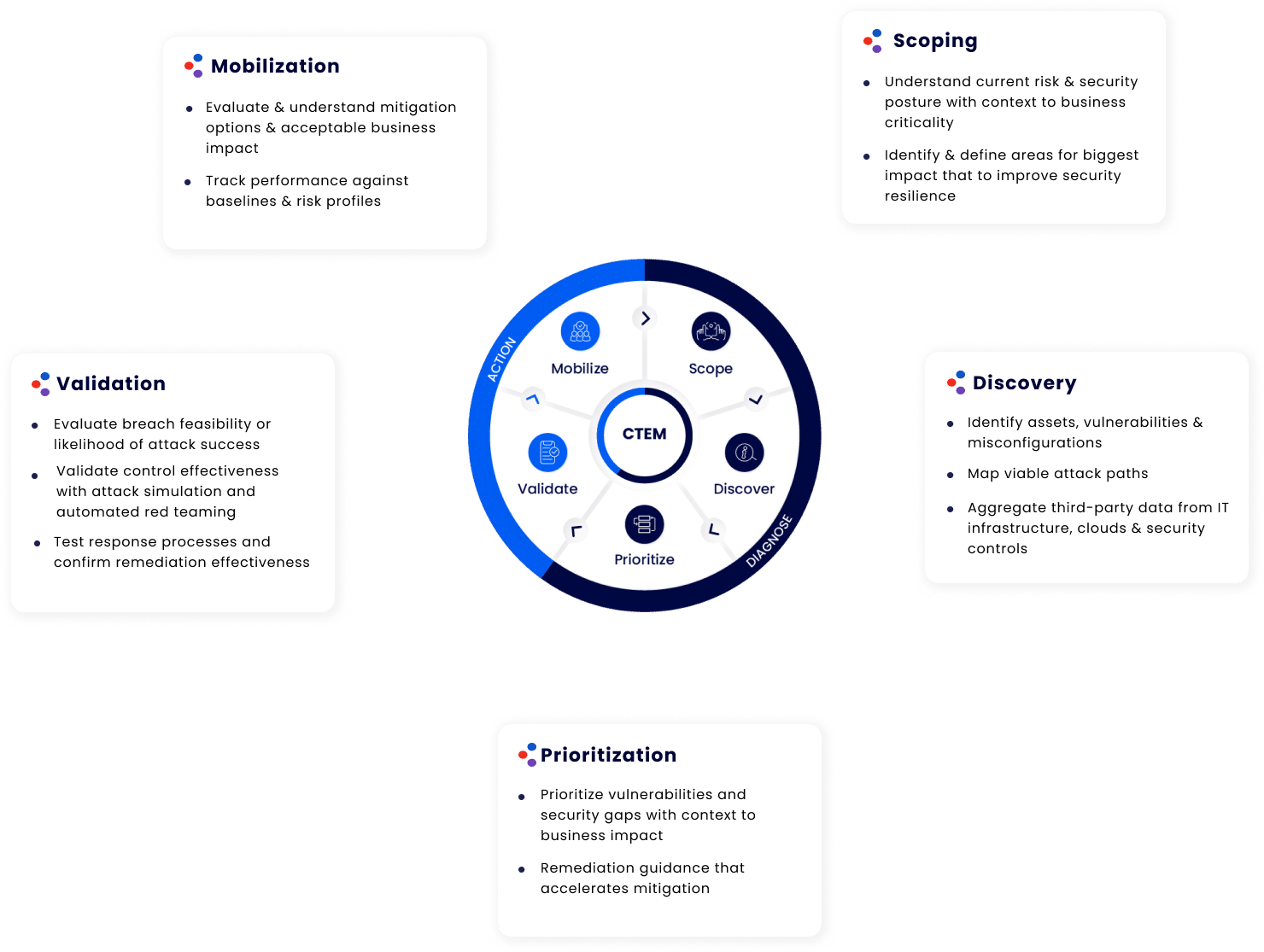
The Cymulate platform drives continuous threat exposure management programs and supports both the technical and business requirements of scoping, discovery, prioritization, validation, and mobilization.
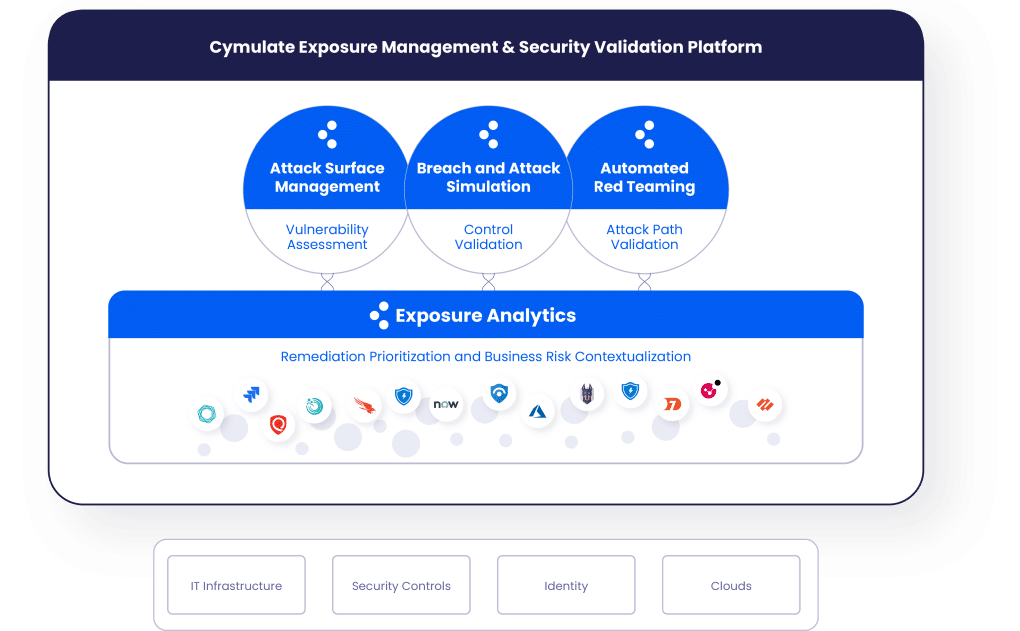
The Cymulate Platform Drives Continuous Threat Exposure Management Programs

Cymulate Attack
Surface Management
- Discover attack surfaces, identify misconfigurations,
and scan for vulnerabilities for more effective and
efficient remediation programs - Create risk-based asset profiles and determine
attack path viability

Cymulate Breach and
Attack Simulation
- Validate security controls with realistic testing
of security controls and architecture - Test for immediate threats and see if the security
controls have the necessary capabilities to stop them - Optimize SecOps and incident response with
continuous, automated validation of security
operations processes, efficiency, and efficacy
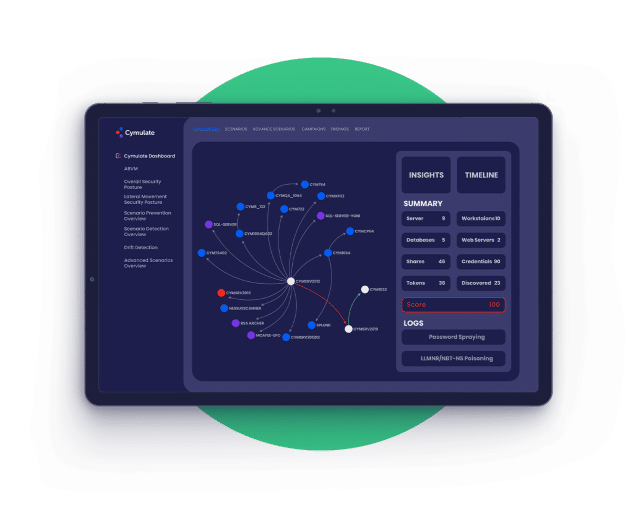
Cymulate Continuous
Automated Red Teaming
- Automated testing for vulnerability validation,
what-if scenarios, and custom-testing for
repeatable and scalable testing.
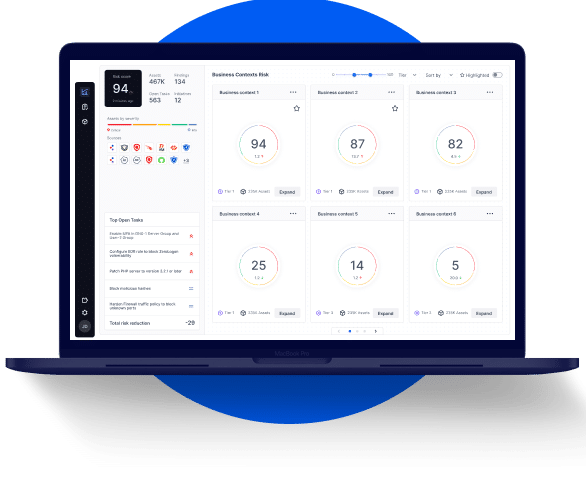
Cymulate Exposure Analytics
- Aggregate disparate data from Cymulate and third-party data sources
- Measure & baseline cyber resilience
- Profile assets for risk and business context
- Focus mitigation on the greatest risk with remediation planning
Backed By the Industry

Cymulate Recognized as Top Innovation Leader
F&S recognized in their Frost Radar™️ Global BAS, 2022 report
Related Resources
Cymulate Platform FAQs
Cymulate ASM automates the identification of internal and external assets, listing all external and internal assets and identifying exploitable attack surface.
Cymulate BAS offers wide-ranging capabilities, including immediate threat intelligence, full kill-chain scenarios, and custom attack simulations. It validates cybersecurity controls and provides continuous assessment and remediation guidance.
Cymulate CART provides a flexible framework for automated red teaming, including full kill-chain campaigns and network penetration testing.
Cymulate Exposure Analytics aggregates data from ASM, BAS, CART, and third-party sources, providing correlated analysis and contextualized vulnerability management. It is a core component that enhances the platform’s exposure management capabilities.
Having all four products in a single platform ensures seamless integration, provides a comprehensive view of the exposure, facilitates security validation, and optimizes vulnerability remediation by correlating exposure and business risks.
The Cymulate platform embodies Gartner’s concept of CTEM by providing a systematic approach to exposure management. It offers technology for exposure discovery, validation, prioritization, and connects to business risks, aligning with Gartner’s principles of CTEM.
By providing insights into attack surfaces, vulnerabilities, and security efficacy, the Cymulate platform identifies security gaps and correlates their risk levels to business priorities. This enables defining risk tolerance levels, accelerates impactful remediation and promotes secure business flexibility.
The combination of ASM (Attack Surface Management), BAS (Breach and Attack Simulation), CART (Continuous Automated Red Teaming), and Exposure Analytics in a single platform the Cymulate platform offers a complete view of the security posture. It profiles the risk of each asset, validates control effectiveness, contextualizes vulnerability prioritization, and correlates risk scores with business priorities to minimize business risks.