Compliance Solution Validation Overview
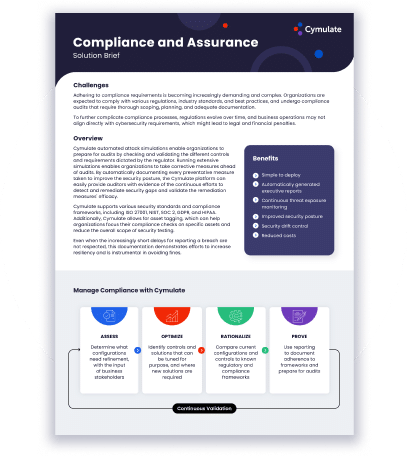
Compliance requirements constantly become more stringent and complex. Businesses are expected to adhere to a myriad of regulations, industry standards, and best practices. Keeping up with these compliance requirements is a daunting challenge for organizations of all sizes and industries. Failure to comply can lead to legal and financial consequences; as well as damage to the organization’s reputation with shareholders, customers, regulators, and the general public.
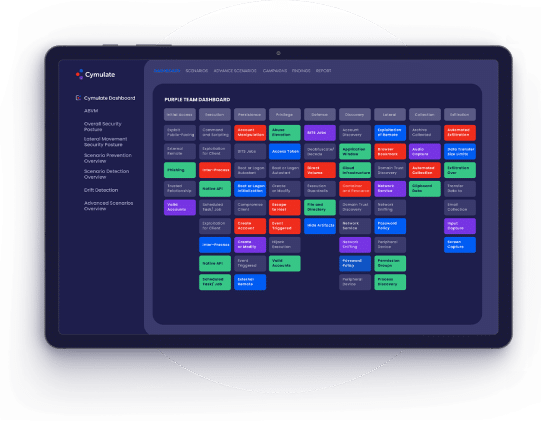
The Cymulate platform provides visibility on cybersecurity compliance to both technical and non-technical stake-holders. Many customers use information derived from Cymulate reporting to substantiate adherence to compliance, risk profiles, and frameworks like NIST and MITRE.
How Cymulate Streamlines
Compliance Processes
With the ongoing regulatory shift from periodic audits toward
cyber-resilience; cybersecurity compliance management can
benefit from continuous validation and comprehensive reporting.
Attack surface management paired with continuous attack
simulations and immediate threat validation facilitate
compliance with updated regulatory and industry standards.
Cymulate reports show the efficacy of preventative measures
taken to improve security posture and to demonstrate
continuous efforts for detecting and remediating security gaps.
This automated documentation facilitates communication with
compliance officers, auditors, and other stakeholders.
Continuous improvement to security not only facilitates
compliance, but also enhances and proves cybersecurity resilience.
Compliance Management with Cymulate
Compliance Solution Validation Benefits

Discover
Identify assets which may come
under audit and unmanaged
applications and systems
Test
Validate discoveries against MITRE, NIST, and other frameworks safely and frequently

Document
Leverage automated technical and executive reporting for stakeholders and auditors
Learn More About Cymulate
Compliance Solution Validation
Read more about Cymulate Compliance and Assurance solution.
Backed By the Industry
“I showed our board of directors the comprehensive visibility that Cymulate provides, and they told me that we needed it before I even had the budget to purchase it.”
Liad Pichon, Director of Cybersecurity, BlueSnap







“Cymulate has been helping me to evaluate my security posture against behavior based as well zero day threats.”
– IT Security & Risk Management Associate

“Technical capabilities provided are outstanding, customer service is highly responsive and product mgmt. is flexible in supporting us with our requests.”
– Security Operations Analyst

“The Cymulate BAS is delivering excellent outcomes, contributing significantly to enhancing my security effectiveness.”
– IT Security & Risk Management Associate

“My experience with the platform was exceptional. It delivers on its promises with easy navigation, effective mitigation steps, and top-notch after sales support.”
– Chief Risk Manager

“Always willing to help offering training sessions and encourage use of the product’s additional available features.”
– Senior Software Engineer

“I believe that Cymulate brings a vision of risks, vulnerabilities and actions that we are unable to pay attention to in our work day.”
– Security Operations Specialist

“The range and breadth of attack scenarios, potential targets and how well each tool integrates is really excellent.”
– Penetration Tester

“We had an excellent experience with Cymulate, from product deployment to while using the platform.”
– Senior Cybersecurity Engineer

“Awesome customer support and techniques used by Cymulate to identify security gaps.”
– IT Security & Risk Management